I developed my first crypter in pure C using the standard process hollowing: create a new process thread in suspended state, put the PE inside it and execute the thread.
I use these winapi: CreateProcess GetThreadContext VirtualAllocEx WriteProcessMemory SetThreadContext ResumeThread. And I use a simple XOR encryption with a long random key.
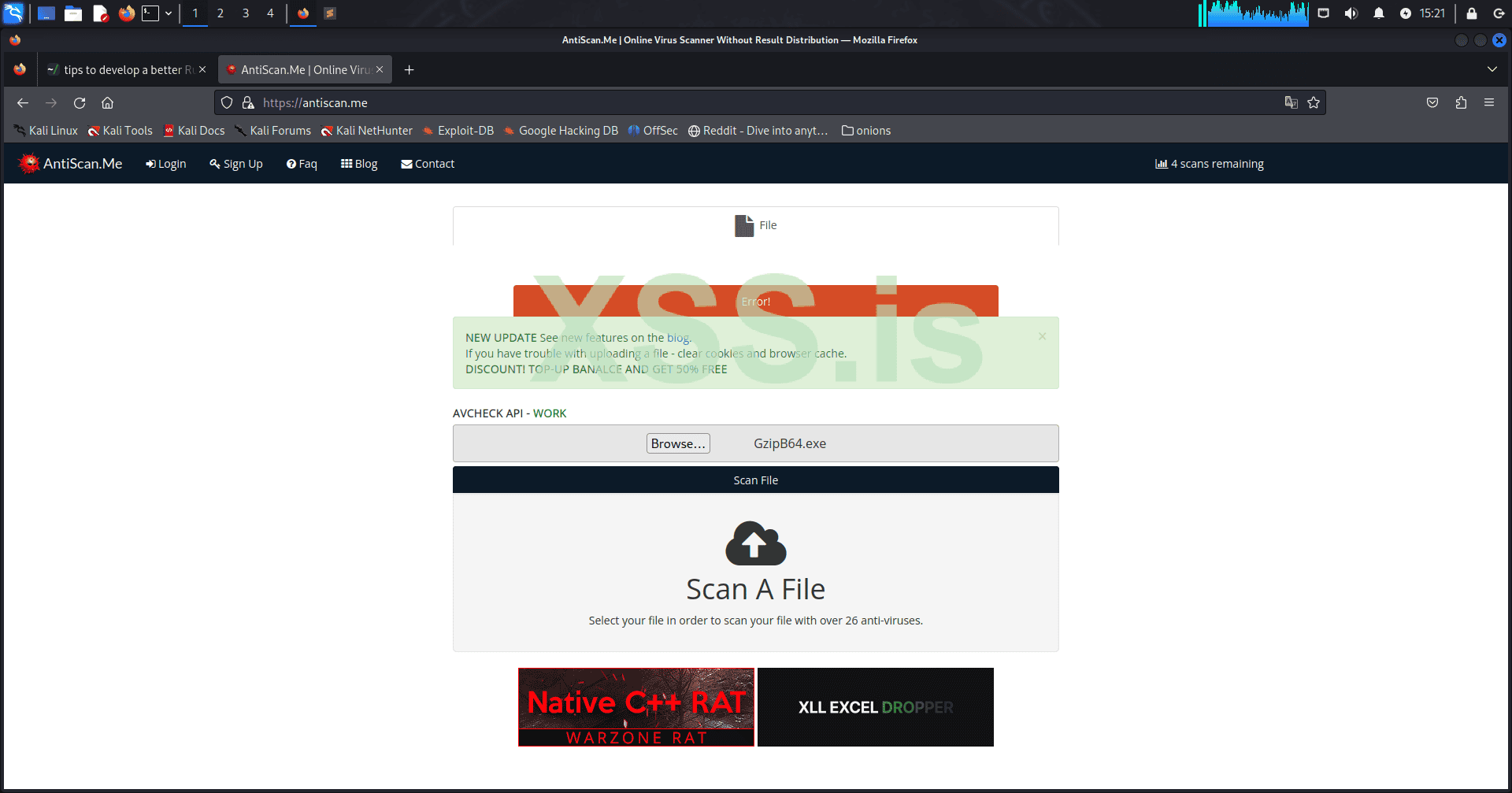
The problem is that it's not undetected, there are around 10 of the most popular AVs that detects it in scantime (I suppose in runtime too). I think the problem is that I use the same winapi everyone use and in a very common way.
I read some blogs about other methods such as injection in other trusted processes, reflective injection or other process hollowing techniques.
Studying and implementing some of them will require a lot of time, so I need some advice, what direction sould be the best for my research? I just want to implement a simple runpe that is undetected, should I try to make my RunPE FUD (if yes, how? maybe I need to obfuscate the api call.. I'm not sure they are the main problem) or it's better to try another more stealth method?
I use these winapi: CreateProcess GetThreadContext VirtualAllocEx WriteProcessMemory SetThreadContext ResumeThread. And I use a simple XOR encryption with a long random key.
The problem is that it's not undetected, there are around 10 of the most popular AVs that detects it in scantime (I suppose in runtime too). I think the problem is that I use the same winapi everyone use and in a very common way.
I read some blogs about other methods such as injection in other trusted processes, reflective injection or other process hollowing techniques.
Studying and implementing some of them will require a lot of time, so I need some advice, what direction sould be the best for my research? I just want to implement a simple runpe that is undetected, should I try to make my RunPE FUD (if yes, how? maybe I need to obfuscate the api call.. I'm not sure they are the main problem) or it's better to try another more stealth method?