- Description
Hello everyone, today I present to you RoseBleed. An multi-purpose Dropper, Stealer and an Obfuscator. It's written in Python 3.10. Fast and efficient File/Browser credential Stealing along with high and configuration customization. Use of encryption is used, so no one except you can view the logs. Currently supports 18 Chromium based Browsers!
- Technical Information about the Stealer (~ you may not skip it):
1. As it was built in Python, using an good Obfuscator helps you reduce the Static Detections way faster and with great ease to FUD.
2. You can use use UPX Compress without any issues, it will help you reduce the size of the executable.
3. Choosing the File Extension for file grabbing has never been so easy, highly configurable.
4. The use of Glob library was utilized in a efficient way, has support for Recursive file searching. Don't worry about missing a file.
5. Has hard-coded folder Blacklist variable, so you can make it skip unwanted folders with ease.
6. After the collection is done, it compresses and uses an random AES key generated on the victim machine to encrypt it. ~ Don't worry about the key, we will get to it.
7. It uploads the encrypted zip to an given hard-coded file upload-er service. (Telegram can be used if needed but needs some coding) ~ for example ufile.io, anonfiles.. etc
8. Now it creates a text file, which holds various information about the Victim. For example: name of the computer, username, ram, cpu, guid, external IP Address, working path to the executable, encryption password(~ from the 6.) and finally the zip upload link. ~ the text is organized and can be read easily.
9. The text file is uploaded to our controlled Paste-bin Api. ~ can be customized.
- The second phase of the Stealer:
1. Might use a extra thread to speed up the process.
2. Starts searching for the respective browser locations. ~ local app-data.
3. Decryption starts on the victim machine as of now. ~ will be changed in the future for the web panel, so the decryption happens in our controlled machine rather than the victim's.
4. Collects the Cookies, Web History and Passwords. ~ no wallets and cryptocurrency as of now, maybe in the future.
5. Organizes the collected Information's in a Zip file and uploads to Discord Web-hook (Telegram can be used if needed but needs some coding.). ~ state to change in future when there is a web panel.
5. Cleans up the created zips/file's and then initiates self destruction.
- Technical Information about the Dropper (~ you may skip it):
1. Creates persistence using another executable which is written in Go Lang, reason? It's job is to decipher (~ rot13) an fixed hard-coded glued registry key every reboot to start our dropper. ~ source will be provided with the purchase of the dropper. Behind the hood there is more going on
2. Downloads and renames our Go Lang executable. (~ for persistence), using Living of the Land Bins. ~ BitsAdmin, if you wonder.
3. Silent download, zero windows are shown.
4. Frequent Intelligent Arbitrary Internet checks so nothing breaks down.
5. If all checks are green, proceeds to download our hard-coded Stealer from a given download link, using Living of the Land bin.
6. After completion, the downloaded file automatically gets added to Task Scheduler to run with a delay of given time seconds/minutes.
7. It proceeds to go in a infinite loop with a check happening every specified seconds/minutes, it monitors an given pastebin link for two hard-coded text.
8. For example if "KEYWORD1" is found, it initiates Self-Destruction and cleans up all the noise.
9. If "KEYWORD2" is found, it downloads and executes from an given link similar to step 5 and 6.
10. Keeps on monitoring the started process and waits for it to close or stop. If closed, it follows step 8.
11. How do we make sure the dropper doesn't run twice within a given time frame? We create an check:
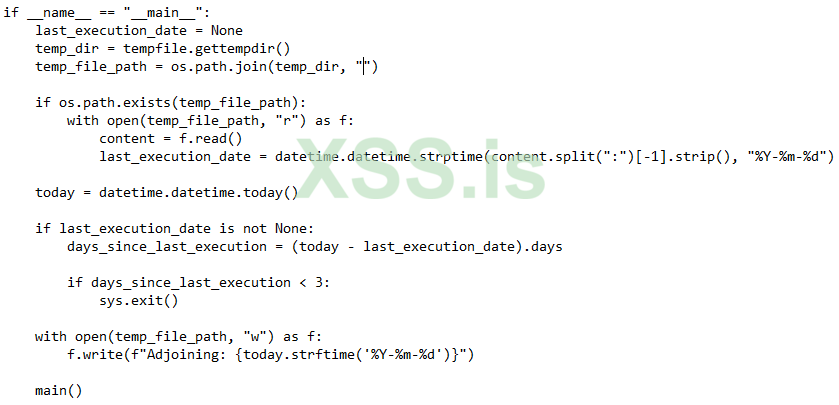
- What about Obfuscator?
It needs an separate thread to explain all of its technicalities in detail, just to save time. The pictures of Detection rates are given.
- Detection Information:
1. Dropper - Hit: 0 (~ no use of Obfuscation)
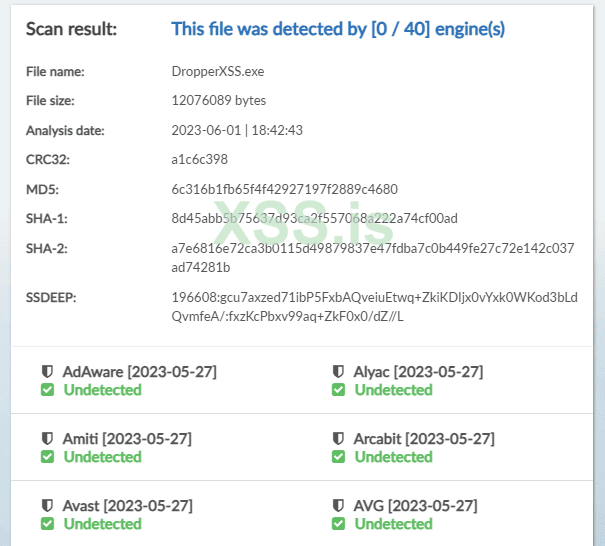
Scan Result Link for Dropper.
2. Stealer/File Grabber - Hit: 0 (~ with obfuscation):
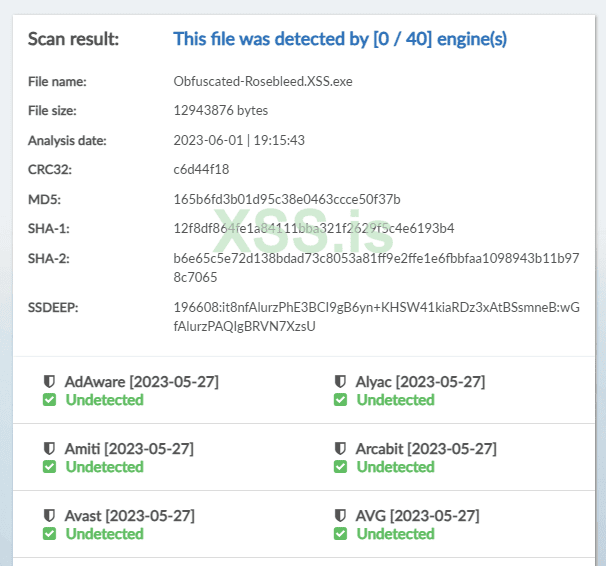
Static Scan link for Stealer/File Grabber with obfuscation
2.1 Stealer/File Grabber - Hit: 5 (~ zero obfuscation)
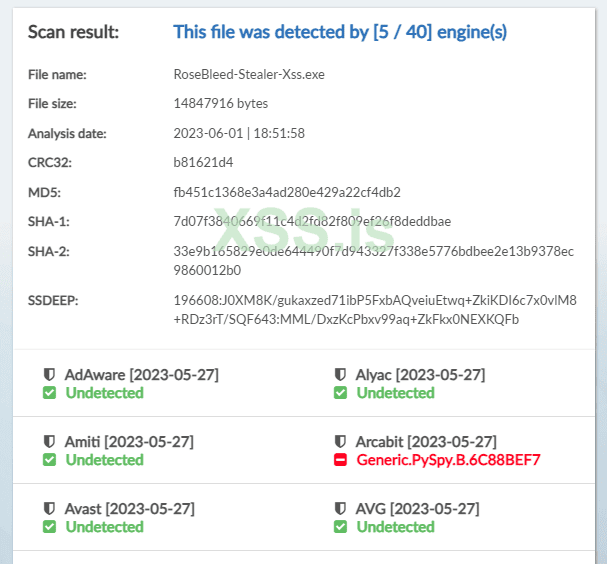
Static Scan link for Stealer/File Grabber with zero obfuscation.
- Note for Buyers:
The tool will be sold with limited quantity, only 3-5 pieces. Full source code will be given and after the purchase, you will get priority support for lifetime and with every problem, a solution will be given and the way to use the tools will be explained too. Keep in mind I don't speak russian yet as of now and will give support in English. May it be through live voice call or screen share. Any functionality can be added at the discretion of the client. Obfuscation is very much required for lower detection's and as to not leak source code in its true form.
- Rates:
Dropper: 22 USD ~ BTC/XMR
Stealer/File Grabber: 32 USD ~ BTC/XMR
Obfuscator: 26 USD ~ BTC/XMR
Full Package with 10% discount: 72 USD ~ BTC/XMR
- Terms of Service:
No refund after purchase, guarantor or reputable middleman in the phase of purchasing is mandatory. That's it, enjoy.
- Final Verdict:
It might look and feel very uneasy to customize without an builder or web panel but bear with me. I promise to make a modern web-panel that will take this to next level. For example, logs decryption happening on the C&C.
I feel like this needs a rewrite from another language and an C&C would've been best with extra features like taking screenshot, key logger and opening a shell. I'm transitioning to Go Lang and in future, the Stealer will be rewritten or maybe not depending on the sales. Feel free to suggest/criticize and provide better description of the problems. So, in future I can avoid it.
- Contact:
Jabber: RoseBleed@jabber.calyxinstitute.org (~ active)
XSS PM (~ highly available)
Always verify through PM from the forum of xss.pro
Hello everyone, today I present to you RoseBleed. An multi-purpose Dropper, Stealer and an Obfuscator. It's written in Python 3.10. Fast and efficient File/Browser credential Stealing along with high and configuration customization. Use of encryption is used, so no one except you can view the logs. Currently supports 18 Chromium based Browsers!
- Technical Information about the Stealer (~ you may not skip it):
1. As it was built in Python, using an good Obfuscator helps you reduce the Static Detections way faster and with great ease to FUD.
2. You can use use UPX Compress without any issues, it will help you reduce the size of the executable.
3. Choosing the File Extension for file grabbing has never been so easy, highly configurable.
4. The use of Glob library was utilized in a efficient way, has support for Recursive file searching. Don't worry about missing a file.
5. Has hard-coded folder Blacklist variable, so you can make it skip unwanted folders with ease.
6. After the collection is done, it compresses and uses an random AES key generated on the victim machine to encrypt it. ~ Don't worry about the key, we will get to it.
7. It uploads the encrypted zip to an given hard-coded file upload-er service. (Telegram can be used if needed but needs some coding) ~ for example ufile.io, anonfiles.. etc
8. Now it creates a text file, which holds various information about the Victim. For example: name of the computer, username, ram, cpu, guid, external IP Address, working path to the executable, encryption password(~ from the 6.) and finally the zip upload link. ~ the text is organized and can be read easily.
9. The text file is uploaded to our controlled Paste-bin Api. ~ can be customized.
- The second phase of the Stealer:
1. Might use a extra thread to speed up the process.
2. Starts searching for the respective browser locations. ~ local app-data.
3. Decryption starts on the victim machine as of now. ~ will be changed in the future for the web panel, so the decryption happens in our controlled machine rather than the victim's.
4. Collects the Cookies, Web History and Passwords. ~ no wallets and cryptocurrency as of now, maybe in the future.
5. Organizes the collected Information's in a Zip file and uploads to Discord Web-hook (Telegram can be used if needed but needs some coding.). ~ state to change in future when there is a web panel.
5. Cleans up the created zips/file's and then initiates self destruction.
- Technical Information about the Dropper (~ you may skip it):
1. Creates persistence using another executable which is written in Go Lang, reason? It's job is to decipher (~ rot13) an fixed hard-coded glued registry key every reboot to start our dropper. ~ source will be provided with the purchase of the dropper. Behind the hood there is more going on

2. Downloads and renames our Go Lang executable. (~ for persistence), using Living of the Land Bins. ~ BitsAdmin, if you wonder.
3. Silent download, zero windows are shown.
4. Frequent Intelligent Arbitrary Internet checks so nothing breaks down.
5. If all checks are green, proceeds to download our hard-coded Stealer from a given download link, using Living of the Land bin.
6. After completion, the downloaded file automatically gets added to Task Scheduler to run with a delay of given time seconds/minutes.
7. It proceeds to go in a infinite loop with a check happening every specified seconds/minutes, it monitors an given pastebin link for two hard-coded text.
8. For example if "KEYWORD1" is found, it initiates Self-Destruction and cleans up all the noise.
9. If "KEYWORD2" is found, it downloads and executes from an given link similar to step 5 and 6.
10. Keeps on monitoring the started process and waits for it to close or stop. If closed, it follows step 8.
11. How do we make sure the dropper doesn't run twice within a given time frame? We create an check:
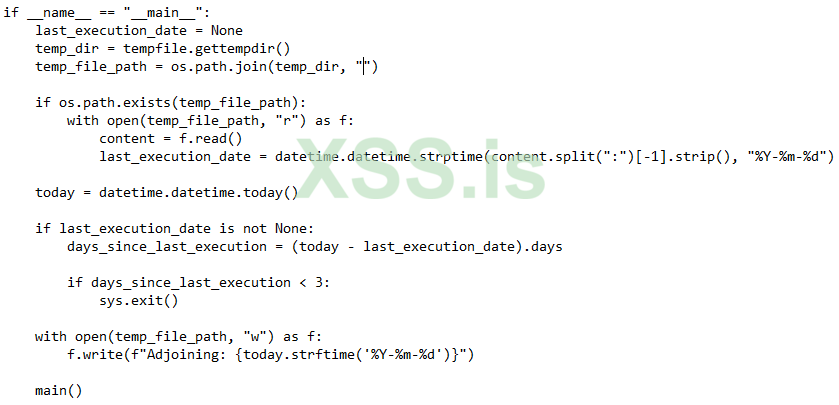
- What about Obfuscator?
It needs an separate thread to explain all of its technicalities in detail, just to save time. The pictures of Detection rates are given.
- Detection Information:
1. Dropper - Hit: 0 (~ no use of Obfuscation)
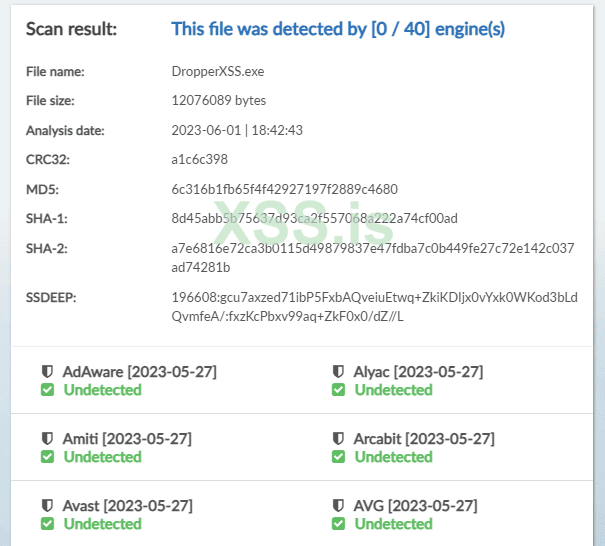
Scan Result Link for Dropper.
2. Stealer/File Grabber - Hit: 0 (~ with obfuscation):
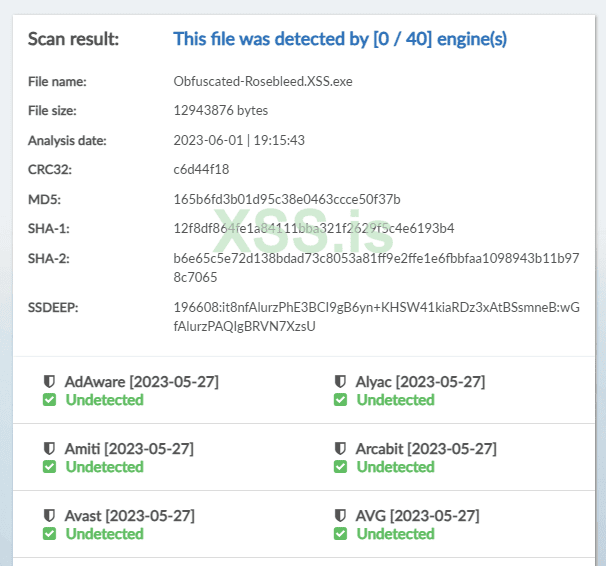
Static Scan link for Stealer/File Grabber with obfuscation
2.1 Stealer/File Grabber - Hit: 5 (~ zero obfuscation)
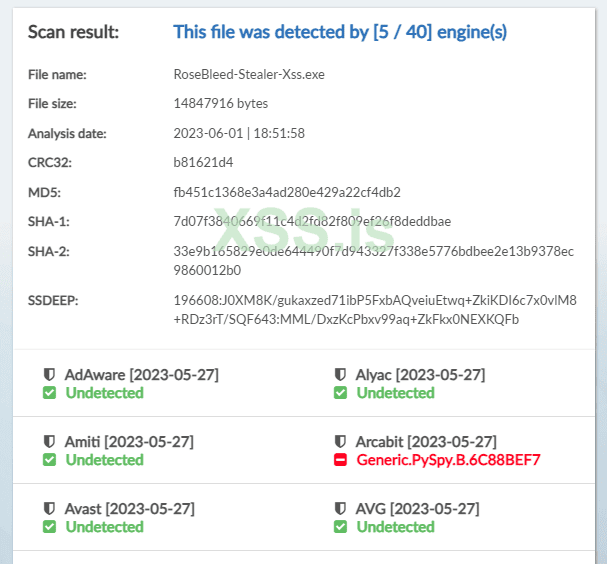
Static Scan link for Stealer/File Grabber with zero obfuscation.
- Note for Buyers:
The tool will be sold with limited quantity, only 3-5 pieces. Full source code will be given and after the purchase, you will get priority support for lifetime and with every problem, a solution will be given and the way to use the tools will be explained too. Keep in mind I don't speak russian yet as of now and will give support in English. May it be through live voice call or screen share. Any functionality can be added at the discretion of the client. Obfuscation is very much required for lower detection's and as to not leak source code in its true form.
- Rates:
Dropper: 22 USD ~ BTC/XMR
Stealer/File Grabber: 32 USD ~ BTC/XMR
Obfuscator: 26 USD ~ BTC/XMR
Full Package with 10% discount: 72 USD ~ BTC/XMR
- Terms of Service:
No refund after purchase, guarantor or reputable middleman in the phase of purchasing is mandatory. That's it, enjoy.
- Final Verdict:
It might look and feel very uneasy to customize without an builder or web panel but bear with me. I promise to make a modern web-panel that will take this to next level. For example, logs decryption happening on the C&C.
I feel like this needs a rewrite from another language and an C&C would've been best with extra features like taking screenshot, key logger and opening a shell. I'm transitioning to Go Lang and in future, the Stealer will be rewritten or maybe not depending on the sales. Feel free to suggest/criticize and provide better description of the problems. So, in future I can avoid it.
- Contact:
Jabber: RoseBleed@jabber.calyxinstitute.org (~ active)
XSS PM (~ highly available)
Always verify through PM from the forum of xss.pro