Пожалуйста, обратите внимание, что пользователь заблокирован
Hola!
For cracked teamserver (Lifetime) offer:
++ ONLY $4999 + FREE WD + SmartScreen Killer - OR - 3 CRYPT FUD BUILDS -> COBALTSTRIKE 4.8 + LATEST KIT 3/2023 ++ Trusted Trade only in xss.pro ++
-- Discount 20% on CURRENT client's.
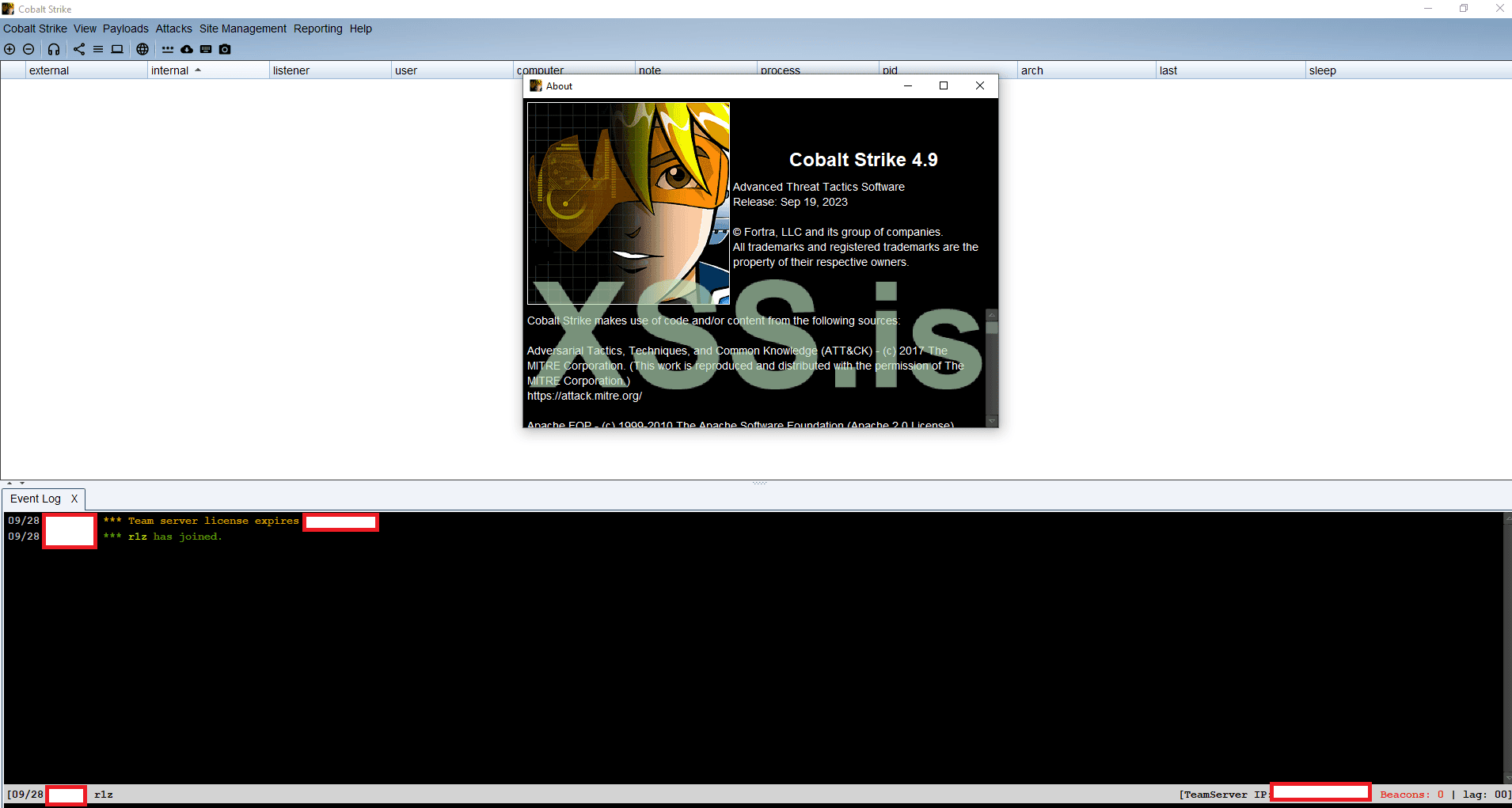
CS Client :
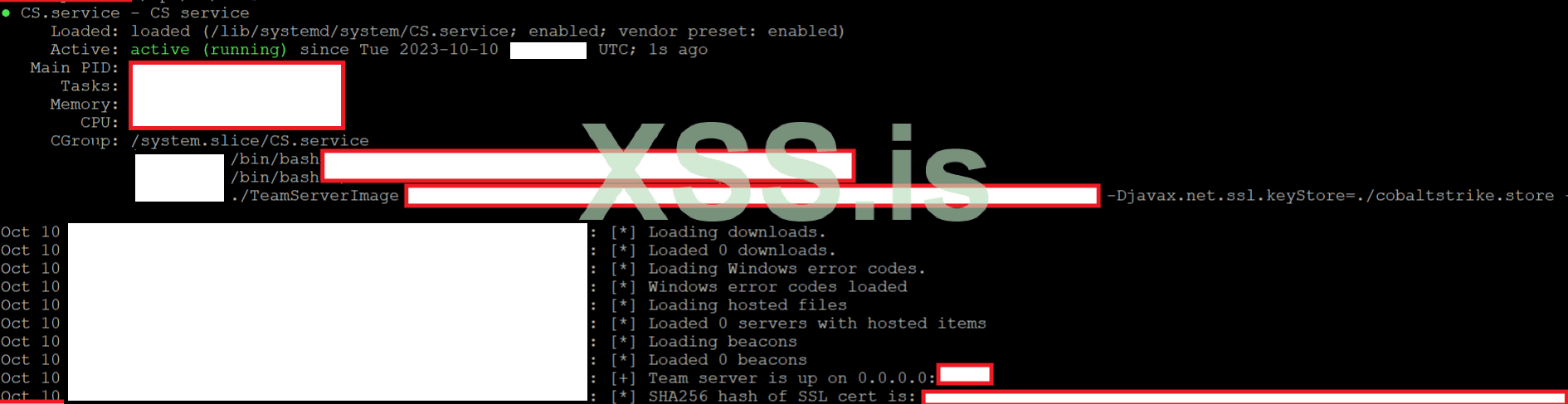
Teamserver debug (No license check):
For Teamserver Licensed offer:
++ ONLY $1999 + FREE WD + SmartScreen Killer - OR - 3 CRYPT FUD BUILDS -> COBALTSTRIKE 4.8 + LATEST KIT 3/2023 ++ Trusted Trade only in xss.pro ++
# Cobalt Strike 4.8 (February 28, 2023)
043dfa038873462039c28cdc3e0e3356de814157e5e851cc0931bfe2d96d7e8e Cobalt Strike 4.8 Licensed (cobaltstrike.jar)
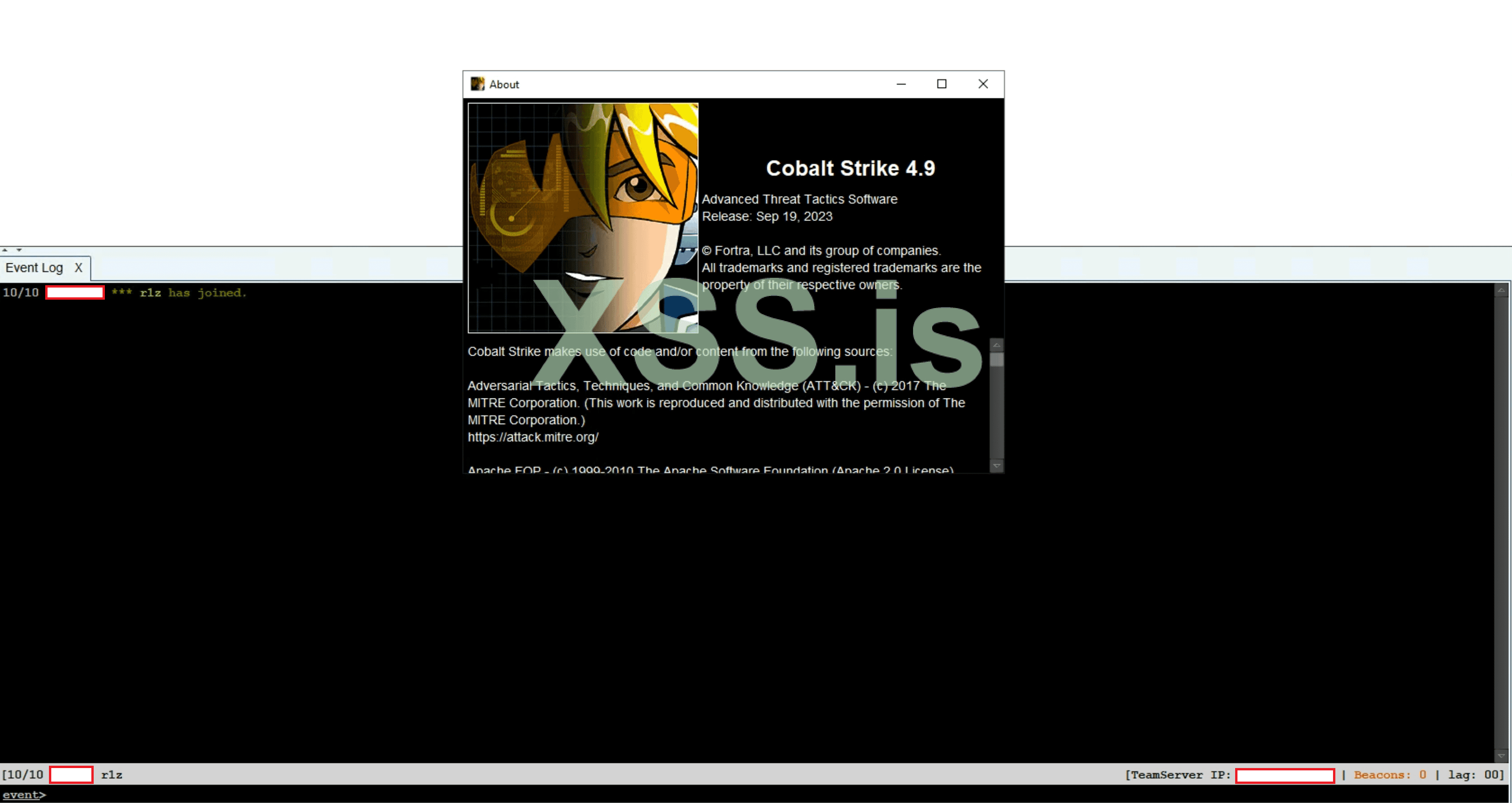
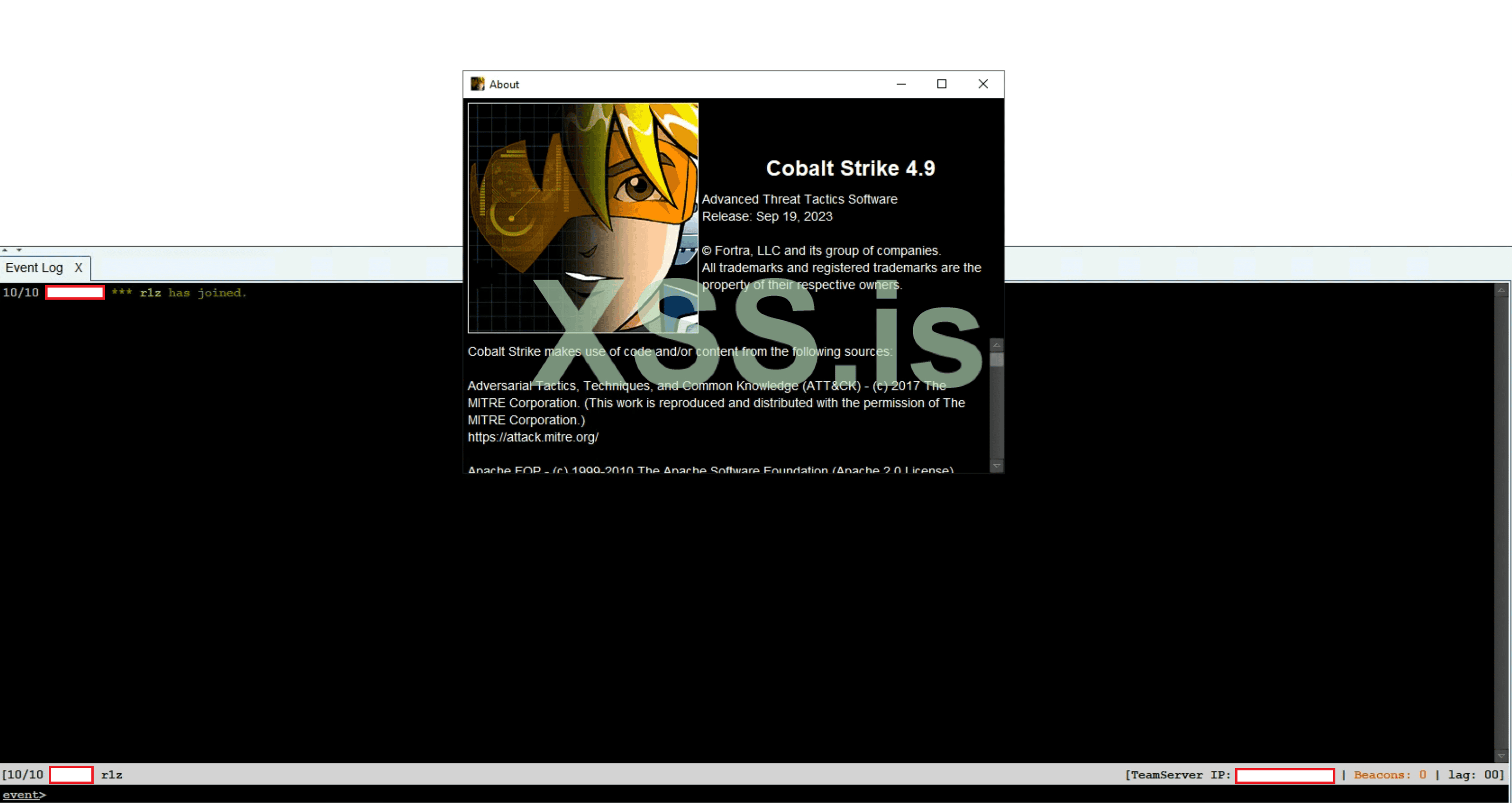
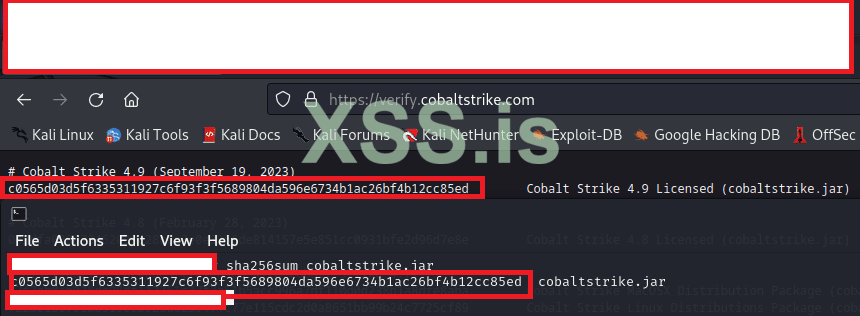
Licensed CobaltStrike 4.9
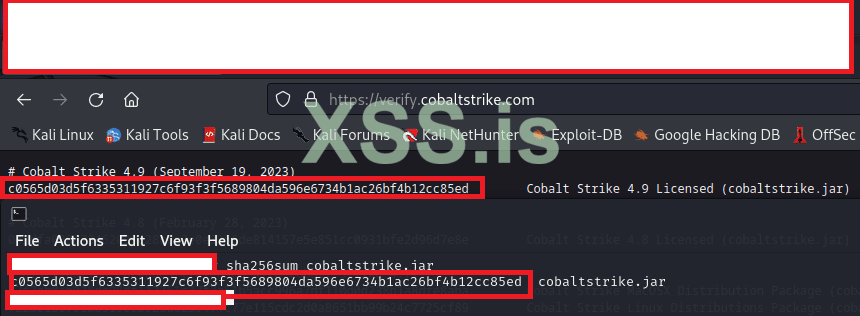
Verify hash:
Release notes:
-------------
September 19th, 2023 - Cobalt Strike 4.9
-------------
+ Authorization files are no longer backwards compatible.
+ Changed Post-Ex DLL's to use prepended loaders (sRDI/Double Pulsar).
Implemented in browserpivot, hashdump, invokeassembly, keylogger, mimikatz, netview, portscan, powershell, screenshot, and sshagent.
Added Aggressor hooks for applying UDRLs to post-ex DLLs (POSTEX_RDLL_GENERATE).
Added support for transform.strrep to post-ex DLL Processing.
Added post-ex.cleanup malleable C2 profile property.
Added smart-inject pointers to the POSTEX_RDLL_GENERATE hook.
+ Added Beacon without the exported ReflectiveLoader function to support the prepended UDRLs (sRDI/Double Pulsar).
The BEACON_RDLL_SIZE function default changed from 0 to 5k.
When the BEACON_RDLL_SIZE returns 0, then a Beacon without the reflective loader is passed to BEACON_RDLL_GENERATE and BEACON_RDLL_GENERATE_LOCAL hooks.
+ Added Beacon User Data to pass user specified information via UDRL.
Added support for syscall functions addresses/numbers.
Added a user specified field to Beacon User Data.
Added BOF API function to get the pointer to the user data.
+ Added data-store command to store BOFs and .NET assemblies in the beacon Data Store.
Added the aggressor script functions for supporting the beacon Data Store.
Added BOF API functions to access and protect stored items in the beacon Data Store.
+ Support spawning processes under the impersonated user security context.
+ Added DuplicateHandle, ReadProcessMemory, and WriteProcessMemory system calls in beacon.
+ Added Malleable C2 Profile definition of Host Profiles to customize the uri, header, and parameter attributes of the HTTP(S) get/post to be host specific and dynamic.
+ Added callback support to aggressor script functions: bnet, beacon_inline_execute, binline_execute, bdllspawn, bexecute_assembly, bhashdump, bmimikatz, bmimikatz_small, bportscan, bpowerpick, bpowershell, and bpsinject
+ Added support for a HTTP(S) beacon based on the WinHTTP library.
Added .http-beacon.library Malleable C2 setting to specify the default beacon http library type (wininet|winhttp).
+ Added aggressor script support for sending/receiving data between clients.
+ Added BOF APIs to access the key/value store in beacon.
+ Added BOF API to retrieve the sleep mask information.
+ Added Malleable C2 sleep setting to match the sleep command syntax.
+ Fixed Malleable C2 strrep setting issues with sleep mask BOF.
+ Fixed Malleable C2 headers_remove setting.
+ Fixed Malleable C2 http-config.headers setting with Content-Type option adds "Content-Type: null" header.
+ Fixed c2lint syntax highlighting when data jitter and append are used.
+ Fixed steal_token command to open a process that is protected.
-- CRYPT PRICE OFFER UPDATE :
[+] Premuim Crypt:
-- ONE TIME CRYPT 1 build $500 ; Expired.
-- WEEKLY CRYPT 5 builds $1k ;
-- MONTHLY CRYPT Unlimited builds $5k ;
Bypass Guarantee ===> Sophos, McAfee, Trend Micro, WD, Kaspersky, ESET, SentinelOne.
[+] VIP CRYPT:
Bypass Guarantee ===> ESET, Crowdstrike, Carbon black monthly subscription Unlimited builds!
-- LAST BUILD:
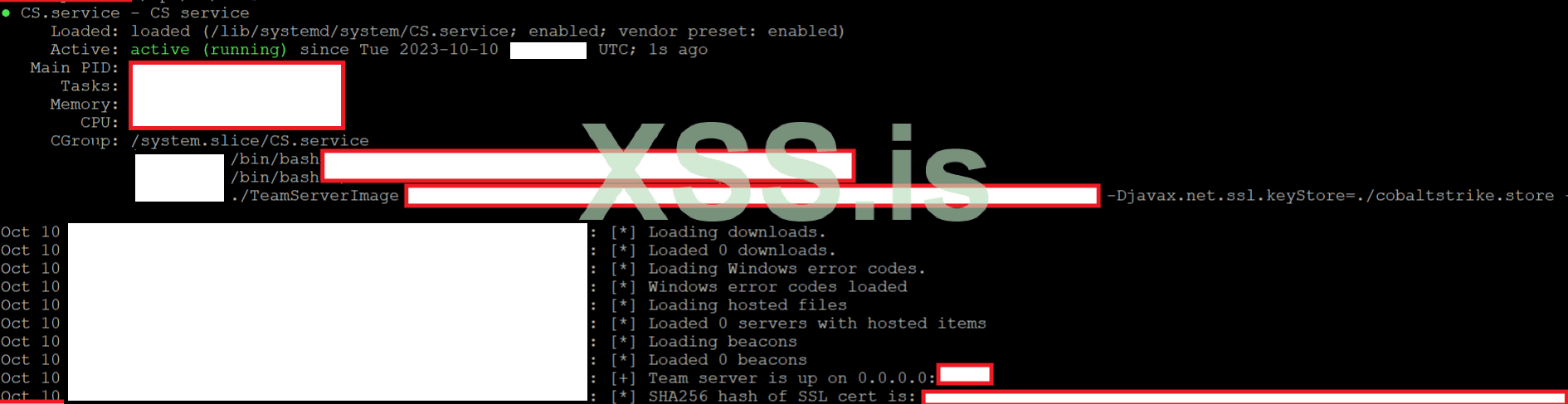
-- FULL COMPLETE INFRASTRUCTURE SETUP :
Total Setup price Latest CobaltStrike 4.9 ($1999)+ Anonymouse VPS ($1499) + Anonymouse Domain registration ($99) + OPSEC Installation service ($999): $8.500 NOW $4596 ( One time FEES, C2 Teamserver valid for 6 months ).
-------------------------------------------------- -------------------------------------------------- ------------------------------
There is an options to purchace anonymously domain for your teamserver or redirector(s) and/or order anonymously VPS with extra mount, discussed in PM.
The service will include one of comptabile features from the above list for all teamserver, plus redirectors from +1 to +4 redirectors, more redirectors will cost additional fees. ( FREE consultation+recommendation for c2 infrastructure ).
• Orders will be confirmed from XSS PM or TOX only.
• Once the order is confirmed, the buyer needs to deliver the VPS's access to start deliver the service.
• VPS must be in Ubuntu/Debian with " root ", otherwise the service will be hold. ( recommended OS: Ubuntu ).
• Consulting & Recommendation setup service is not more than 4-5 questions, otherwise your order will be dismissed .
• There is no documentation. (The service is not-documented at all, it as a one-time setup, or monthly subscribe).
• nmap (https://github.com/whickey-r7/grab_beacon_config/blob/main/grab_beacon_config.nse) scanner. ( blocked )
• BeaconEye (https://github.com/CCob/BeaconEye) scanner ( blocked )
• Cobalt parser (https://github.com/Sentinel-One/CobaltStrikeParser) . ( blocked )
• Hidden URI aka checksum8. (https://github.com/fox-it/dissect.cobaltstrike/blob/main/scripts/checksum8-accesslogs.py)( hidden )
• Hide your Teamserver under CloudFlared Tunnel (https://xss.pro/threads/54879/)
• Steal SSL for your target company. ( bypassed )
• Bypass most moderm EDR's. ( bypassed )
• and / or Install TOR over Teamserver.
• and / or Install OpenVPN with redirector.
• and / or Install DNSCrypt (DoH) via CloudFlare.
• and / or Install Domains Randomizor.
• and / or Install JARM randomizor aka JA3's obfuscator.
Who looking for crypt cobaltstrike beacon & bypass ( not CrowdStrike & Sential ), The most modern AV's, read this topic.
• Kleenscan report (https://kleenscan.com/scan_result/1f4bcf849243b39c54d139fe61c57799aecca0456d57858fad1a3a2e4becd2d0) 0/40 for today scan.
• CheckZilla report (https://checkzilla.io/scan/769c60c7-0390-47fe-8c24-59cbed29cb39)0 (https://checkzilla.io/scan/769c60c7-0390-47fe-8c24-59cbed29cb39)/19 for last scan.
• Powershell Obfuscation & clean.
*UPDATE NOTES (30.03.23) :
• The OPSEC i provide is restriected rules.. and the client need to follow my rules to get the highest security for his teamserver, hence any client refuse to follow the rules and request to not follow my recommendation the crypt server will be only for the current teamserver.. if he request new teamserver he need to pay new teamserver fees + new crypt fees.
• All crypt should be only for http/https/dns/smb cryption, anything else will not be included in my service, any new teamserver means you need to pay new fees for crypt the new teamserver.
Read this topic & check reviews (https://xss.pro/threads/72985/post-504742) before contact.
./r1z
A5852A300E402AD8AA973E1147D024FFE7DCF34BCC203C7B9DFB8560A3B10361000000000003.
( 20% Discount on CURRENT customers as promised )
Since some cracked version's appeared in the market, this is notified for new client's who looking for TRUSTED cracked resources with no backdoor's, get moneyback in case of any suspecion file you can see!For cracked teamserver (Lifetime) offer:
++ ONLY $4999 + FREE WD + SmartScreen Killer - OR - 3 CRYPT FUD BUILDS -> COBALTSTRIKE 4.8 + LATEST KIT 3/2023 ++ Trusted Trade only in xss.pro ++
-- Discount 20% on CURRENT client's.
CS Client :
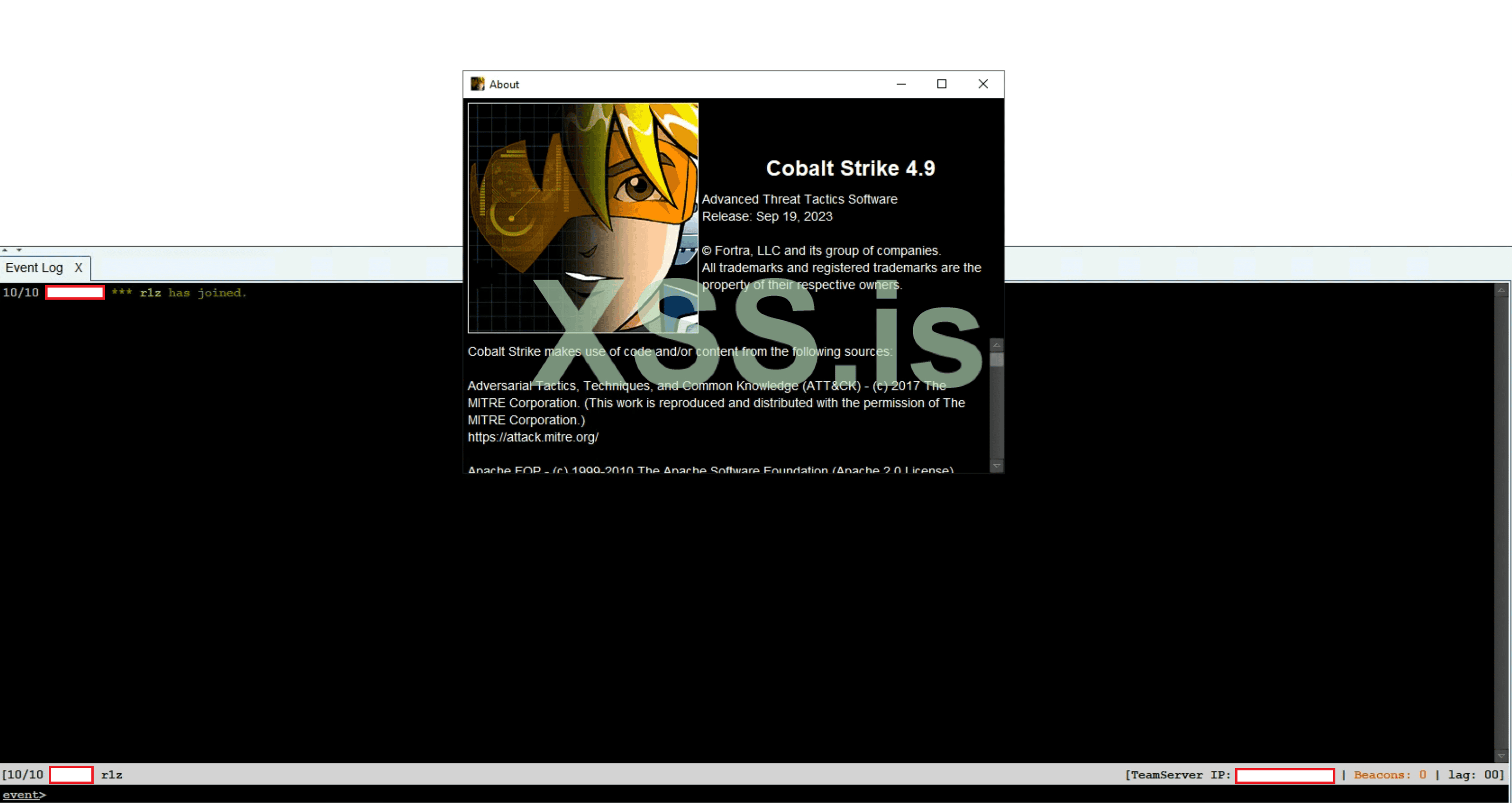
Teamserver debug (No license check):
For Teamserver Licensed offer:
++ ONLY $1999 + FREE WD + SmartScreen Killer - OR - 3 CRYPT FUD BUILDS -> COBALTSTRIKE 4.8 + LATEST KIT 3/2023 ++ Trusted Trade only in xss.pro ++
# Cobalt Strike 4.8 (February 28, 2023)
043dfa038873462039c28cdc3e0e3356de814157e5e851cc0931bfe2d96d7e8e Cobalt Strike 4.8 Licensed (cobaltstrike.jar)
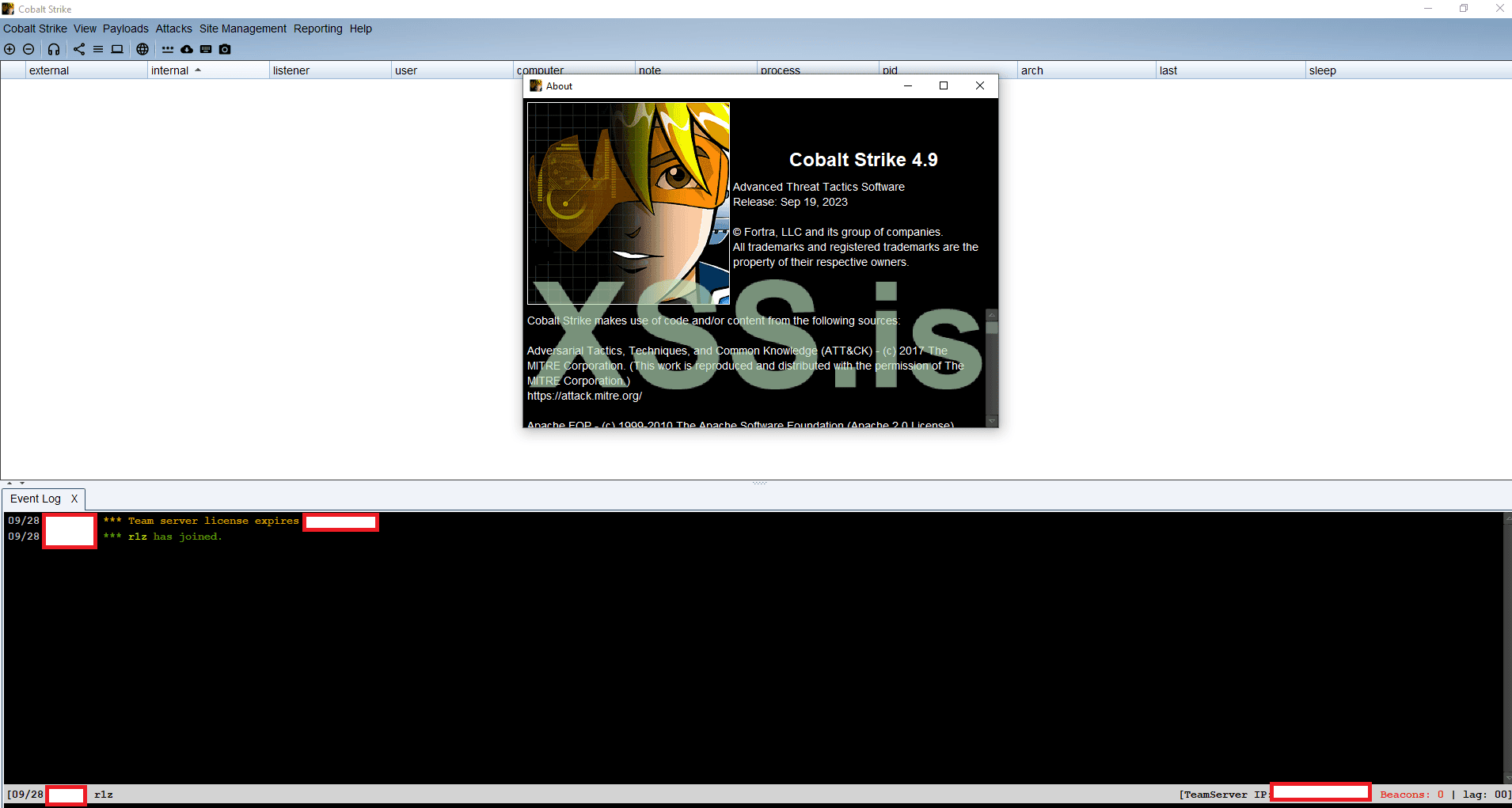
Licensed CobaltStrike 4.9
( 20% Discount on CURRENT customers as promised )
Verify hash:
Release notes:
-------------
September 19th, 2023 - Cobalt Strike 4.9
-------------
+ Authorization files are no longer backwards compatible.
+ Changed Post-Ex DLL's to use prepended loaders (sRDI/Double Pulsar).
Implemented in browserpivot, hashdump, invokeassembly, keylogger, mimikatz, netview, portscan, powershell, screenshot, and sshagent.
Added Aggressor hooks for applying UDRLs to post-ex DLLs (POSTEX_RDLL_GENERATE).
Added support for transform.strrep to post-ex DLL Processing.
Added post-ex.cleanup malleable C2 profile property.
Added smart-inject pointers to the POSTEX_RDLL_GENERATE hook.
+ Added Beacon without the exported ReflectiveLoader function to support the prepended UDRLs (sRDI/Double Pulsar).
The BEACON_RDLL_SIZE function default changed from 0 to 5k.
When the BEACON_RDLL_SIZE returns 0, then a Beacon without the reflective loader is passed to BEACON_RDLL_GENERATE and BEACON_RDLL_GENERATE_LOCAL hooks.
+ Added Beacon User Data to pass user specified information via UDRL.
Added support for syscall functions addresses/numbers.
Added a user specified field to Beacon User Data.
Added BOF API function to get the pointer to the user data.
+ Added data-store command to store BOFs and .NET assemblies in the beacon Data Store.
Added the aggressor script functions for supporting the beacon Data Store.
Added BOF API functions to access and protect stored items in the beacon Data Store.
+ Support spawning processes under the impersonated user security context.
+ Added DuplicateHandle, ReadProcessMemory, and WriteProcessMemory system calls in beacon.
+ Added Malleable C2 Profile definition of Host Profiles to customize the uri, header, and parameter attributes of the HTTP(S) get/post to be host specific and dynamic.
+ Added callback support to aggressor script functions: bnet, beacon_inline_execute, binline_execute, bdllspawn, bexecute_assembly, bhashdump, bmimikatz, bmimikatz_small, bportscan, bpowerpick, bpowershell, and bpsinject
+ Added support for a HTTP(S) beacon based on the WinHTTP library.
Added .http-beacon.library Malleable C2 setting to specify the default beacon http library type (wininet|winhttp).
+ Added aggressor script support for sending/receiving data between clients.
+ Added BOF APIs to access the key/value store in beacon.
+ Added BOF API to retrieve the sleep mask information.
+ Added Malleable C2 sleep setting to match the sleep command syntax.
+ Fixed Malleable C2 strrep setting issues with sleep mask BOF.
+ Fixed Malleable C2 headers_remove setting.
+ Fixed Malleable C2 http-config.headers setting with Content-Type option adds "Content-Type: null" header.
+ Fixed c2lint syntax highlighting when data jitter and append are used.
+ Fixed steal_token command to open a process that is protected.
-- CRYPT PRICE OFFER UPDATE :
[+] Premuim Crypt:
-- WEEKLY CRYPT 5 builds $1k ;
-- MONTHLY CRYPT Unlimited builds $5k ;
Bypass Guarantee ===> Sophos, McAfee, Trend Micro, WD, Kaspersky, ESET, SentinelOne.
[+] VIP CRYPT:
Bypass Guarantee ===> ESET, Crowdstrike, Carbon black monthly subscription Unlimited builds!
-- LAST BUILD:
-- FULL COMPLETE INFRASTRUCTURE SETUP :
- HIDDEN TEAMSERVER.
- ANONYMOUSE REDIRECTORS NO.4
- ANONYMOUSE RDP ( WINDOWS / LINUX ).
- ANONYMOUSE DOMAINS ( 1 YEAR VALID ).
..::: COMPLETE SETUP CLACULATION FEES :::..
-------------------------------------------------- -------------------------------------------------- ------------------------------Total Setup price Latest CobaltStrike 4.9 ($1999)+ Anonymouse VPS ($1499) + Anonymouse Domain registration ($99) + OPSEC Installation service ($999): $
-------------------------------------------------- -------------------------------------------------- ------------------------------
There is an options to purchace anonymously domain for your teamserver or redirector(s) and/or order anonymously VPS with extra mount, discussed in PM.
The service will include one of comptabile features from the above list for all teamserver, plus redirectors from +1 to +4 redirectors, more redirectors will cost additional fees. ( FREE consultation+recommendation for c2 infrastructure ).
• Orders will be confirmed from XSS PM or TOX only.
• Once the order is confirmed, the buyer needs to deliver the VPS's access to start deliver the service.
• VPS must be in Ubuntu/Debian with " root ", otherwise the service will be hold. ( recommended OS: Ubuntu ).
• Consulting & Recommendation setup service is not more than 4-5 questions, otherwise your order will be dismissed .
• There is no documentation. (The service is not-documented at all, it as a one-time setup, or monthly subscribe).
• nmap (https://github.com/whickey-r7/grab_beacon_config/blob/main/grab_beacon_config.nse) scanner. ( blocked )

• BeaconEye (https://github.com/CCob/BeaconEye) scanner ( blocked )

• Cobalt parser (https://github.com/Sentinel-One/CobaltStrikeParser) . ( blocked )

• Hidden URI aka checksum8. (https://github.com/fox-it/dissect.cobaltstrike/blob/main/scripts/checksum8-accesslogs.py)( hidden )

• Hide your Teamserver under CloudFlared Tunnel (https://xss.pro/threads/54879/)

• Steal SSL for your target company. ( bypassed )

• Bypass most moderm EDR's. ( bypassed )

• and / or Install TOR over Teamserver.
• and / or Install OpenVPN with redirector.
• and / or Install DNSCrypt (DoH) via CloudFlare.
• and / or Install Domains Randomizor.
• and / or Install JARM randomizor aka JA3's obfuscator.
Who looking for crypt cobaltstrike beacon & bypass ( not CrowdStrike & Sential ), The most modern AV's, read this topic.
• Kleenscan report (https://kleenscan.com/scan_result/1f4bcf849243b39c54d139fe61c57799aecca0456d57858fad1a3a2e4becd2d0) 0/40 for today scan.
• CheckZilla report (https://checkzilla.io/scan/769c60c7-0390-47fe-8c24-59cbed29cb39)0 (https://checkzilla.io/scan/769c60c7-0390-47fe-8c24-59cbed29cb39)/19 for last scan.
• Powershell Obfuscation & clean.
*UPDATE NOTES (30.03.23) :
• The OPSEC i provide is restriected rules.. and the client need to follow my rules to get the highest security for his teamserver, hence any client refuse to follow the rules and request to not follow my recommendation the crypt server will be only for the current teamserver.. if he request new teamserver he need to pay new teamserver fees + new crypt fees.
• All crypt should be only for http/https/dns/smb cryption, anything else will not be included in my service, any new teamserver means you need to pay new fees for crypt the new teamserver.
Read this topic & check reviews (https://xss.pro/threads/72985/post-504742) before contact.
./r1z
A5852A300E402AD8AA973E1147D024FFE7DCF34BCC203C7B9DFB8560A3B10361000000000003.
Последнее редактирование: