Пожалуйста, обратите внимание, что пользователь заблокирован
Welcome everyone,
we are very excited to bring this new revolutionary exploit to the market.
This tool is an extension to our older .lnk builder:
https://duckduckgo.com/?q=lnk+quantum+builder
https://xss.pro/threads/67100/
But its so game changing that we decided to create a new thread for it.
The new and improved QuantumBuilder will make your payload look like any file format (.png, .mp4, .doc, ...), just like our other project, but you will be also able to send the plain payload without using .Zips and even attach it to Gmail. Also any file can now be used as an icon.
Demo:
Attach to Gmail demo:
Features:
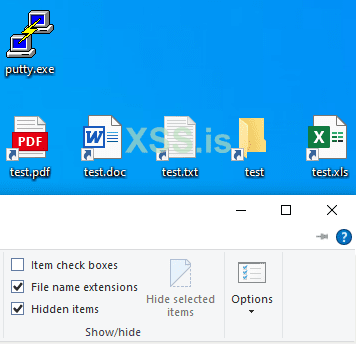
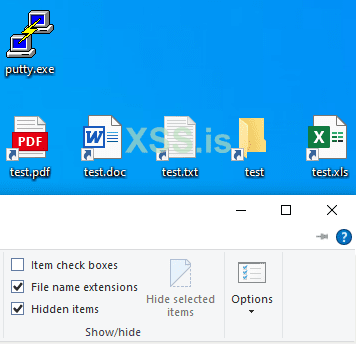
The actual .url extension is always hidden in windows:
Implementation of the dogwalk n-day exploit:
This exploit will allow you to send shortcuts over email without actually attaching any file.
Demo:
Prices:
1 month > 1900 EUR
2 months > 3400 EUR
Lifetime > 5000 EUR
Forum guarantor accepted
Contacts:
Telegram > @QuantumBuilderSupport (https://t.me/QuantumBuilderSupport)
This is the @ of a user, not a channel. Some scammers are trying to impersonate us so be careful.
Tox > FD378852532E37DB2DC7B945E581F2C5D49AB2E89F4715AC136E89F04F960A06EA08061D4DD4
TOS:
we are very excited to bring this new revolutionary exploit to the market.
This tool is an extension to our older .lnk builder:
https://duckduckgo.com/?q=lnk+quantum+builder
https://xss.pro/threads/67100/
But its so game changing that we decided to create a new thread for it.
The new and improved QuantumBuilder will make your payload look like any file format (.png, .mp4, .doc, ...), just like our other project, but you will be also able to send the plain payload without using .Zips and even attach it to Gmail. Also any file can now be used as an icon.
Demo:
Features:
- Premium support team and many video tutorials are available [NEW]
- Load any icon you want [NEW]
- Attach to gmail [NEW]
- Spoof ANY extension
- UAC Bypass
- Implementation of the dogwalk n-day exploit, more info below
- Bypass Windows Smartscreen, EV certs are a thing of the past
- 100% FUD, even if you spread your stub. Every build is unique (https://www.checkzilla.io/scan/a09553ac-fce9-4536-99a8-32f65275ee01)
- Decoy (upon opening your .url a file of your choosing will be displayed on your victim's pc)
- Multiple payloads per .url file. Even if one gets detected the rest will still run
- Supported payload formats: .exe/.js/.vbs/.bat/.ps1/.msi
- Dll payloads
- Choose the .url file size
- Execute your exes with admin privileges by prompting UAC with a Microsoft signed binary (powershell.exe)
- Run your payload at startup, with a delay or when the victim's computer is idle
- Hide your payloads after executing them
- Replace the .url with the decoy file once executed.
- Melt .url after execution
- WD exclusion wrapper
- Display a message when the .url gets run
- Choose where your payload is dropped on your victim's computer
- Compress your shortcut in a .iso/.img/.cab
The actual .url extension is always hidden in windows:
Implementation of the dogwalk n-day exploit:
This exploit will allow you to send shortcuts over email without actually attaching any file.
Demo:
Prices:
1 month > 1900 EUR
2 months > 3400 EUR
Lifetime > 5000 EUR
Forum guarantor accepted
Contacts:
Telegram > @QuantumBuilderSupport (https://t.me/QuantumBuilderSupport)
This is the @ of a user, not a channel. Some scammers are trying to impersonate us so be careful.
Tox > FD378852532E37DB2DC7B945E581F2C5D49AB2E89F4715AC136E89F04F960A06EA08061D4DD4
TOS:
- Uploading samples to virus total and similar scanners is prohibited.
- All support is provided via private chat, not in this thread. Asking for instructions here is prohibited (many people get pinged every time a message is sent).
- If you are given some instructions and you refuse to follow them, for example disabling windows defender's sample submission, your license might be banned.
- We do not offer any kind of compensation if your payload gets detected while the files produced by this builder are clean.
- All sales are final.
Последнее редактирование:
