Hi, recently I ran into a problem not much discussed on the internet.
One of my partners shared a password-protected PKCS12 certificate (.p12) he needed to bruteforce.
Searching the Internet I didn't find many tools capable of doing it, other than one created by "aestu" called "crackpkcs12" (https://crackpkcs12.sourceforge.net/) that I couldn't compile on my instances.
For this reason I decided to write this little script; it's not the best, but it does what it was meant for.
I hope someone will find this usefull.
A few notes:
1) The script uses the deprecated OpenSSL library, for convenience I decided to use this and suppress the deprecation error
2) There are bash solutions similar to this one(I've included one in this thread), if you can't use Python use those instead.
Feel free to do anything you want with this code, you got a better solution? Share it here!
One of my partners shared a password-protected PKCS12 certificate (.p12) he needed to bruteforce.
Searching the Internet I didn't find many tools capable of doing it, other than one created by "aestu" called "crackpkcs12" (https://crackpkcs12.sourceforge.net/) that I couldn't compile on my instances.
For this reason I decided to write this little script; it's not the best, but it does what it was meant for.
I hope someone will find this usefull.
A few notes:
1) The script uses the deprecated OpenSSL library, for convenience I decided to use this and suppress the deprecation error
2) There are bash solutions similar to this one(I've included one in this thread), if you can't use Python use those instead.
Bash:
cat passwords-file.txt|
while read p; do
echo trying $p;
openssl pkcs12 -in "cert-to-crack.p12" -passin "pass:$p";
RC=$?; if [ $RC -eq 0 ]; then
break; fi ; done
Python:
import sys
import os
import OpenSSL
from OpenSSL import crypto
# Here I decided to suppress the OpenSSL deprecation warning
import warnings
warnings.filterwarnings("ignore", category=DeprecationWarning)
## Be sure that the user submits the required parameters
if(len(sys.argv) < 3):
print("\nExample: python3 pkcs-cracker.py filetocrack.p12 wordlist.txt\n")
sys.exit()
## Take the input, and check if both the files do exist or not
file_to_crack = sys.argv[1]
passwords = sys.argv[2]
try:
if(os.path.isfile(file_to_crack)==True and os.path.isfile(passwords)==True):
pass
else:
sys.exit()
except:
print("\n Files not available, please check the supplied arguments \n")
sys.exit()
## Push the wordlist supplied into a list
with open(passwords, 'r') as f:
passwords_list = [line.strip() for line in f]
## Try to crack the .p12 file using the passwords provided by the user
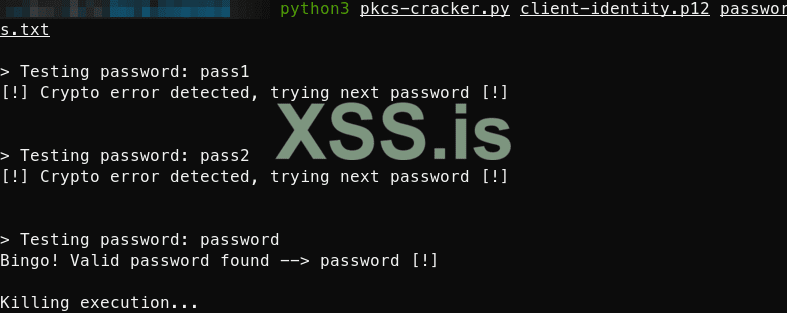
for pass_temp in passwords_list:
print("\n> Testing password: "+pass_temp)
try:
crack_p12 = crypto.load_pkcs12(open(file_to_crack, 'rb').read(), pass_temp.encode())
k = crypto.dump_privatekey(crypto.FILETYPE_PEM, crack_p12.get_privatekey())
if(b"PRIVATE KEY" in k):
print("Bingo! Valid password found --> "+pass_temp+" [!]\n")
print("Killing execution...")
sys.exit()
except OpenSSL.crypto.Error:
print('[!] Crypto error detected, trying next password [!]\n')
pass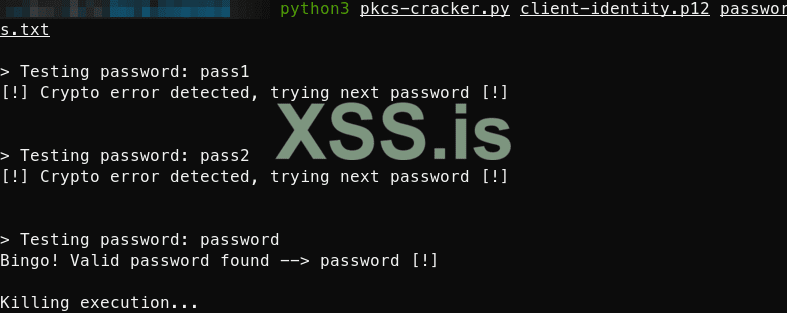
Feel free to do anything you want with this code, you got a better solution? Share it here!
Последнее редактирование:
