Пожалуйста, обратите внимание, что пользователь заблокирован

Windows Privilege Escalation for Beginners
Learn how to escalate privileges on Windows machines with absolutely no filler.
 academy.tcm-sec.com
academy.tcm-sec.com

95% off Windows Privilege Escalation for Beginners - Udemy Coupon & Course Review
Udemy discount coupon: 95% off Windows Privilege Escalation for Beginners. (Course review & coupon.)
FuzzySecurity | Windows Privilege Escalation Fundamentals
Privilege Escalation - Windows · Total OSCP Guide

Online Course: Windows Privilege Escalation for Beginners from Udemy | Class Central
2020 launch! Learn how to escalate privileges on Windows machines with absolutely no filler.

Windows Privilege Escalation Fundamentals - HackerSploit Blog
Privilege Escalation consists of techniques that adversaries use to gain higher-level permissions on a system or network. Adversaries can often enter and explore a network with unprivileged access but require elevated permissions to follow through on their objectives.
 hackersploit.org
hackersploit.org

Windows-Privilege-Escalation-Resources/README.md at master · TCM-Course-Resources/Windows-Privilege-Escalation-Resources
Compilation of Resources from TCM's Windows Priv Esc Udemy Course - Windows-Privilege-Escalation-Resources/README.md at master · TCM-Course-Resources/Windows-Privilege-Escalation-Resources

WINDOWS PRIVILEGE ESCALATION FOR BEGINNERS
2020 launch! Learn how to escalate privileges on Windows machines with absolutely no filler.What you’ll learnEthical hacking and penetration testing skillsWindows privilege escalation techniquesCommon privilege escalation tools and methodologyPreparation for capture the flag style exams and
Amazon.com: How To Pass OSCP Series: Windows Privilege Escalation Step-by-Step Guide: 9798558514902: Wang, Alan: Books
Amazon.com: How To Pass OSCP Series: Windows Privilege Escalation Step-by-Step Guide: 9798558514902: Wang, Alan: Books
www.amazon.com
Privilege Escalation | Offensive Security
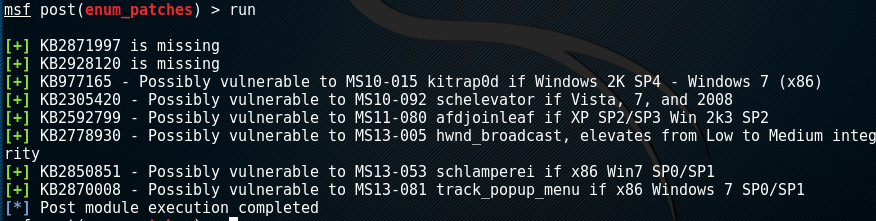
Metasploit has a Meterpreter "getsystem" script, that will use a number of different techniques in attempt to gain SYSTEM level privileges on the remote target.

Understanding Privilege Escalation and 5 Common Attack Techniques
Learn about privilege escalation, and discover windows privilege escalation techniques and see how to mitigate them. Also, see Linux privilege escalation.
Manh-Dung Nguyen - Windows Privilege Escalation
There is a ton of great resources of privilege escalation techniques on Windows. However, I still want to create my own cheat sheet of this difficult topic a...
strongcourage.github.io

Windows Privilege Escalation and Bypassing Win10 OS Hardening | Hacking & Cyber Security Briefing
c0c0n is a 14 years old platform that is aimed at providing opportunities to showcase, educate, understand and spread awareness on Information Security, data protection, and privacy. It also aims to provide a hand-shaking platform for various Corporate, Government organizations including the...

Windows Privilege Escalation for OSCP & Beyond
Finding and exploiting Windows vulnerabilities and misconfigurations to gain an administrator shell.
 hackersacademy.com
hackersacademy.com
Windows - Rowbot's PenTest Notes
 guide.offsecnewbie.com
guide.offsecnewbie.com

My 5 Top Ways to Escalate Privileges
During a penetration test, rarely will the tester get access to a system with the administrator privileges in the first attempt. You are almost always required to use privilege escalation techniques to achieve the penetration test goals. Several people have...

PayloadsAllTheThings/Methodology and Resources/Windows - Privilege Escalation.md at master · swisskyrepo/PayloadsAllTheThings
A list of useful payloads and bypass for Web Application Security and Pentest/CTF - swisskyrepo/PayloadsAllTheThings
GitHub - frizb/Windows-Privilege-Escalation: Windows Privilege Escalation Techniques and Scripts
Windows Privilege Escalation Techniques and Scripts - GitHub - frizb/Windows-Privilege-Escalation: Windows Privilege Escalation Techniques and Scripts
GitHub - itm4n/PrivescCheck: Privilege Escalation Enumeration Script for Windows
Privilege Escalation Enumeration Script for Windows - GitHub - itm4n/PrivescCheck: Privilege Escalation Enumeration Script for Windows

GitHub - carlospolop/winPE: Windows privilege escalation with cmd
Windows privilege escalation with cmd. Contribute to carlospolop/winPE development by creating an account on GitHub.
GitHub - ycdxsb/WindowsPrivilegeEscalation: Collection of Windows Privilege Escalation (Analyse/PoC/Exp...)
Collection of Windows Privilege Escalation (Analyse/PoC/Exp...) - GitHub - ycdxsb/WindowsPrivilegeEscalation: Collection of Windows Privilege Escalation (Analyse/PoC/Exp...)
GitHub - m0nad/awesome-privilege-escalation: A curated list of awesome privilege escalation
A curated list of awesome privilege escalation. Contribute to m0nad/awesome-privilege-escalation development by creating an account on GitHub.
GitHub - antonioCoco/RogueWinRM: Windows Local Privilege Escalation from Service Account to System
Windows Local Privilege Escalation from Service Account to System - GitHub - antonioCoco/RogueWinRM: Windows Local Privilege Escalation from Service Account to System
pentest/windows-privilege-escalation.md at master · lamontns/pentest
Contribute to lamontns/pentest development by creating an account on GitHub.
Pentest-Cheatsheets/windows.rst at master · Tib3rius/Pentest-Cheatsheets
Contribute to Tib3rius/Pentest-Cheatsheets development by creating an account on GitHub.
GitHub - Ignitetechnologies/Windows-Privilege-Escalation
Contribute to Ignitetechnologies/Windows-Privilege-Escalation development by creating an account on GitHub.

GitHub - Tib3rius/windowsprivchecker: Windows privilege escalation (enumeration) script designed with OSCP labs (legacy Windows) in mind
Windows privilege escalation (enumeration) script designed with OSCP labs (legacy Windows) in mind - GitHub - Tib3rius/windowsprivchecker: Windows privilege escalation (enumeration) script designed...
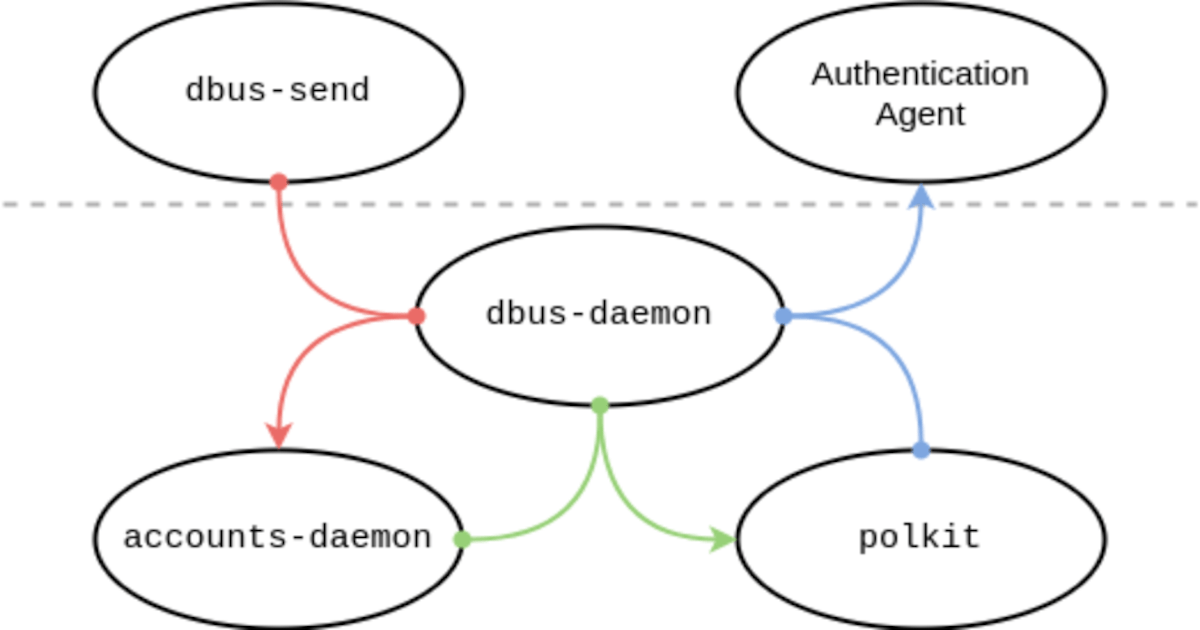
Privilege escalation with polkit: How to get root on Linux with a seven-year-old bug | The GitHub Blog
polkit is a system service installed by default on many Linux distributions. It’s used by systemd, so any Linux distribution that uses systemd also uses polkit.
Windows Privilege Escalation Scripts & Techniques
Privilege escalation is an important process part of post exploitation in a penetration test that allow an attacker to obtain a higher…
 rahmatnurfauzi.medium.com
rahmatnurfauzi.medium.com
GitHub - nickvourd/Windows_Privilege_Escalation_CheatSheet: Windows Privilege Escalation Methodology
Windows Privilege Escalation Methodology. Contribute to nickvourd/Windows_Privilege_Escalation_CheatSheet development by creating an account on GitHub.

Windows Privilege Escalation Guide
Privilege escalation always comes down to proper enumeration. But to accomplish proper enumeration you need to know what to check and look for. This takes familiarity with systems that normally comes along with experience. At first privilege escalation can seem like a daunting task, but after a...
www.absolomb.com

Windows Privilege Escalation Cheatsheet for OSCP
Hello Everyone, here is the windows privilege escalation cheatsheet which I used to pass my OSCP certification. I am not a professional, I tried to add as many commands as possible which might be useful in windows privilege escalation and enumeration of services, exploiting the services and the...

Windows Privilege Escalation — MacroSEC
Privilege escalation happens when a malicious user exploits a vulnerability in an application or operating system to gain elevated access to resources that should normally be unavailable to that user. The attacker can then use the newly gained privileges to steal confidential data, run...
Windows Privilege Escalation (AlwaysInstallElevated) - Hacking Articles
Hello Friends!! In this article, we are demonstrating the Windows privilege escalation method via the method of AlwaysInstallElevated policy. In penetration testing, when we spawn
www.hackingarticles.in

Newbie Step By Step Guide To Learn The Windows Privilege Escalation
Learn newbie step by step guide to learn the windows privilege escalation in corporate . Exploit the internal network environments with manual exploitation.
 blog.certcube.com
blog.certcube.com
Windows Privilege Escalation
Windows Privilege Escalation Cheatsheet Latest updated as of: 12 / June / 2022 So you got a shell, what now? This post will help you with local enumeration as well as escalate your privileges further. Usage of different enumeration scripts and tools is encouraged, my favourite is WinPEAS. If...

Windows Privilege Escalation - Credentials Harvesting - StefLan's Security Blog
Windows systems often stores clear text, encoded/hashed credentials in the system, this guide will show how to identify them.

Windows Privilege Escalation Best Practices
One of the most difficult aspects of security in a Windows environment is keeping visibility to and control over Windows privileges. This post analyzes Windows Server privilege escalation, why it is dangerous, and how your organization can effectively implement the tools and controls needed for...
Privilege escalation: Windows - Hacker's Grimoire
 vulp3cula.gitbook.io
vulp3cula.gitbook.io
Windows Privilege Escalation
Here is my Windows Privilege Escalation what i have created during my OSCP journey. These Techniques are also applicable in real world situations!
Privilege Escalation - Windows - OSCP
 oscp.infosecsanyam.in
oscp.infosecsanyam.in

Windows Privilege Escalation
Information Gathering + What system are we connected to? systeminfo | findstr /B /C:”OS Name” /C:”OS Version” + Get the hostname and username (if available) hostname echo %u…
GitHub - pentestmonkey/windows-privesc-check: Standalone Executable to Check for Simple Privilege Escalation Vectors on Windows Systems
Standalone Executable to Check for Simple Privilege Escalation Vectors on Windows Systems - pentestmonkey/windows-privesc-check

GDS - Blog - Introducing Windows Exploit Suggester
February 22, 2017 Update This post provides an update on two topics regarding Windows Exploit Su...

GitHub - PowerShellMafia/PowerSploit: PowerSploit - A PowerShell Post-Exploitation Framework
PowerSploit - A PowerShell Post-Exploitation Framework - GitHub - PowerShellMafia/PowerSploit: PowerSploit - A PowerShell Post-Exploitation Framework

HostRecon: A Situational Awareness Tool - Black Hills Information Security
Beau Bullock // Overview HostRecon is a tool I wrote in PowerShell to assist with quickly enumerating a number of items that I would typically check after gaining access to […]

GitHub - SecWiki/windows-kernel-exploits: windows-kernel-exploits Windows平台提权漏洞集合
windows-kernel-exploits Windows平台提权漏洞集合. Contribute to SecWiki/windows-kernel-exploits development by creating an account on GitHub.

GitHub - abatchy17/WindowsExploits: Windows exploits, mostly precompiled. Not being updated. Check https://github.com/SecWiki/windows-kernel-exploits instead.
Windows exploits, mostly precompiled. Not being updated. Check https://github.com/SecWiki/windows-kernel-exploits instead. - GitHub - abatchy17/WindowsExploits: Windows exploits, mostly precompiled...

oscp/windows-template.md at master · sheimo/oscp
Contribute to sheimo/oscp development by creating an account on GitHub.
