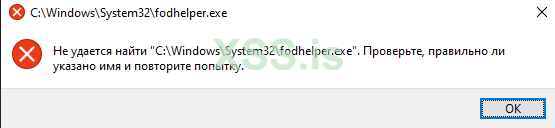
Собственно всем привет, уважаемые! Реализую самый заезженный способ байпасса юак через fodhelper.exe на сишечке, но проблема заключается в том, что как бы я не пытался запустить fodhelper из под x32, софтина не видит его, хоть убей. Пробовал через CreateProcess, ShellExecuteEx, даже через гребанный system(*путь до fodhelper*), ничего не помогло. В х64 все прекрасно работает. Не понимаю в какую сторону копать, чтобы понять почему такая проблема возникает именно на x32. Если запущу таким же образом условный calc.exe, то все отработает на ура.
C:
SHELLEXECUTEINFOW shellinfo;
shellinfo.lpVerb = L"open";
shellinfo.lpFile = L"C:\\Windows\\System32\\fodhelper.exe";
shellinfo.nShow = 0;
shellinfo.fMask = SEE_MASK_NOCLOSEPROCESS;
shellinfo.cbSize = sizeof(SHELLEXECUTEINFOW);
shellinfo.hwnd = 0;
shellinfo.lpParameters = 0;
shellinfo.lpDirectory = 0;
shellinfo.hInstApp = 0;
if (API(SHELL32, ShellExecuteExW)(&shellinfo))
{
wprintf(L"Created process sucessfully through shellexecute\n");
API(KERNEL32, ExitProcess)(0);
}
else
Exit(L"error while creating process");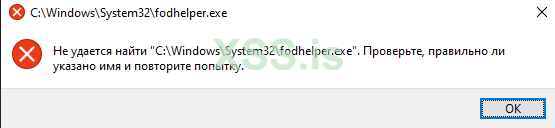
Последнее редактирование:
