New features
- JAVA IAST AcuSensor can now be used on WebSphere
- HTTP requests can be copied as Curl command from the vulnerability data
New vulnerability checks
- New check for DotCMS unrestricted file upload (CVE-2022-26352)
- New check for .NET JSON.NET Deserialization RCE
- New check for Unauthenticated RCE in Confluence Server and Data Center (CVE-2022-26134)
- New check for Authentication bypass via MongoDB operator injection
- New check for MongoDB $where operator JavaScript injection
Updates
- Multiple DeepScan updates improving crawling of Single Page Applications (SPAs)
- Upgraded Chromium to v103.0.5060.114
- Improved handling of installed.json by PHP IAST AcuSensor
- SCA, AcuMonitor (OOB vulnerability checks) and URL malware checks now require the “Acunetix Online Services” to be enabled in the user profile
- Updated the MongoDB Injection checks
- Various UI updates and fixes
Fixes
- Multiple fixes in the JAVA and .NET IAST AcuSensors
- Fixed false negative in “Possible virtual host found”
- Fixed bug causing CSRF tokens to be retrieved using HTTP
- Fixed false positive in “Apache HTTP Server Source Code Disclosure”
Download
- Windows + Linux: https://mega.nz/file/OgcBkS7b#Ln3MPnOevxSvfVthjUOeHAsYJHVg7yxeL8TQqEuCTy0
- Mirror: https://anonfiles.com/36Bcq2zcyb/Acunetix-v14.9.220713150_zip
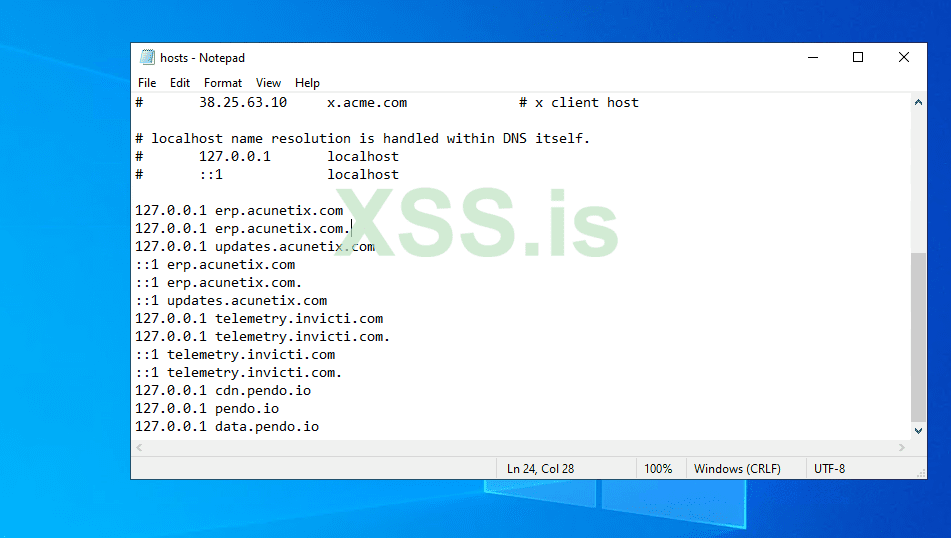
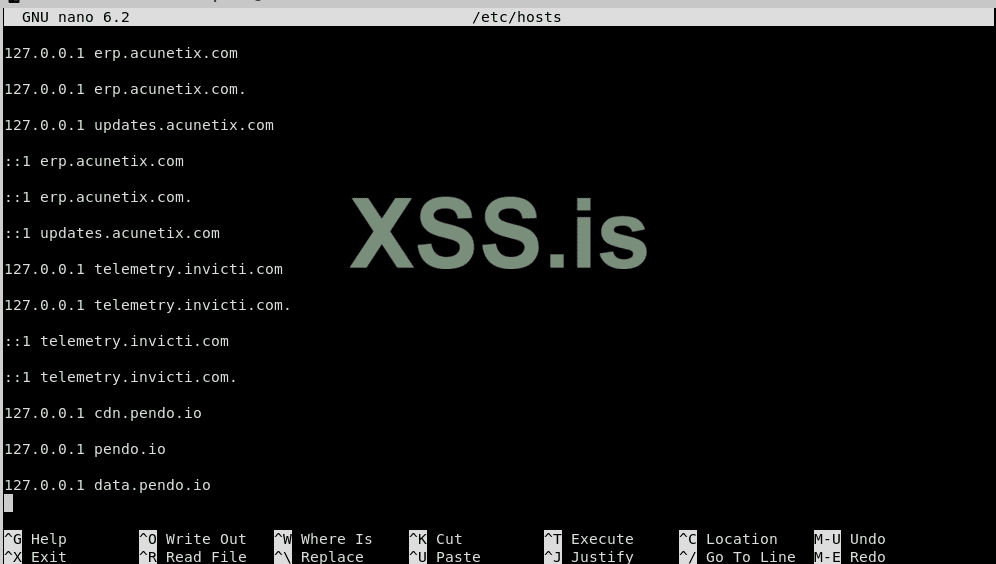
Guide
- Instructions are inside the zip archive.
Последнее редактирование: