Пожалуйста, обратите внимание, что пользователь заблокирован
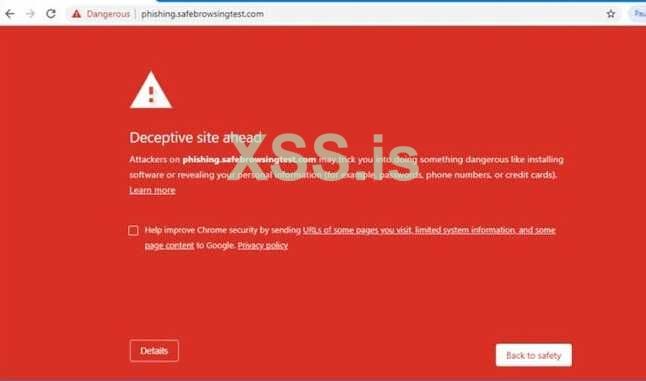
Most Phishing Campaigns encounter the problem of having their Phishing Pages / Websites /Letters backlisted (e.g RED PAGE)
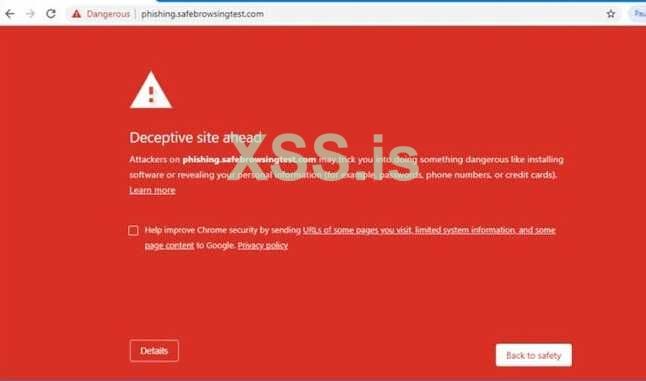
I offer my service to make your phishing pages or letters to LAST ALOT LONGER before it gets flagged as "deceptive site"
PM me or message on Telegram below
Official Telegram Profile: @ScalarNetwork
Official Telegram Channel: @ScalarNetworkOfficial
I offer my service to make your phishing pages or letters to LAST ALOT LONGER before it gets flagged as "deceptive site"
PM me or message on Telegram below
Official Telegram Profile: @ScalarNetwork
Official Telegram Channel: @ScalarNetworkOfficial