Пожалуйста, обратите внимание, что пользователь заблокирован
I am still wondering if I am writing an on-topic thread or not,  lets's just simply dive into info.
lets's just simply dive into info. 
First of all, spreading work is very boring work.. and without proper guidance, it's almost a disaster. so, I include these three methods to make things easier.
1. spreading via traffic
2. spreading via PPI networks, also.
3. spreading via vulnerability
so let's start with the first method, on live traffic.
1. spreading via traffic
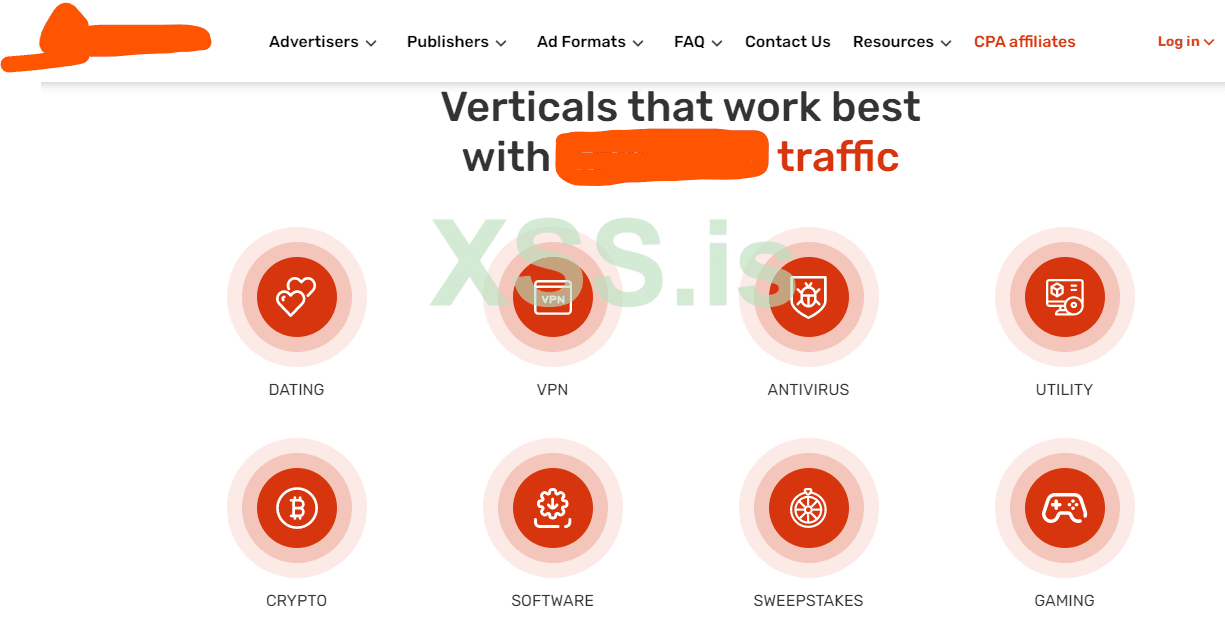
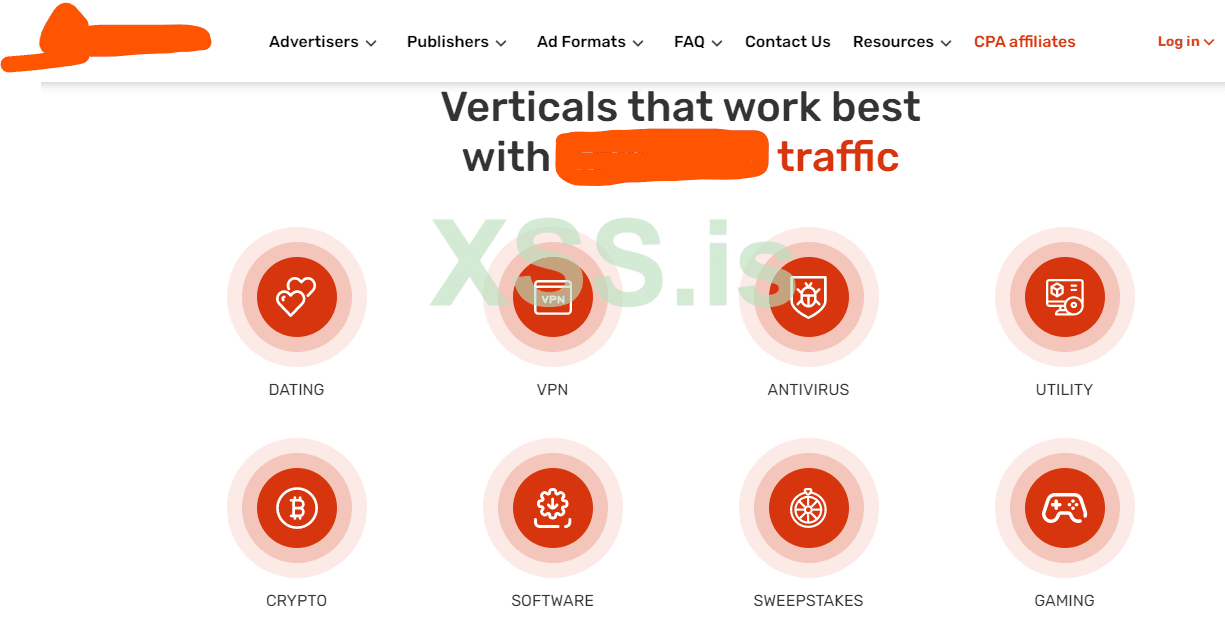
when you use an ad network to perform installs you first need a CPA-based ad network. CPA stands for cost per action or performance-based marketing as redefined part.
a CPA network is a part of the advertising industry that mainly focuses on actions or is called a complete task. let's assume we have opened the browser. the first thing the browser will do is give us an identity for eg: Unknown.
when we first open a search engine and search some text we are identified as a user
when we reach a certain website according to our search we become traffic
when we choose some from websites like a product or something and checkout. we become a customer.
the main focus of CPA network is making customers.
not only CPA ad networks but also landing pages are needed. the full list is:
a) CPA ads network or performance-based ad network
b) landing pages
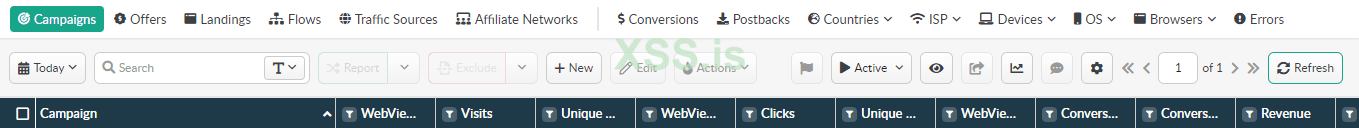
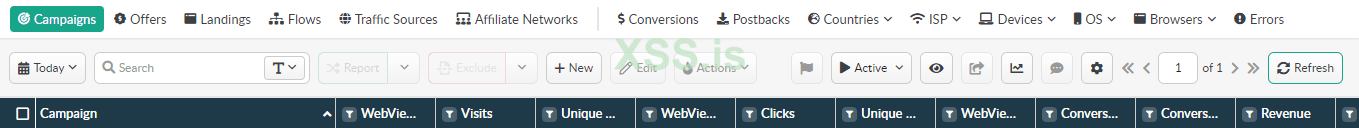
c) tracking
d) approval
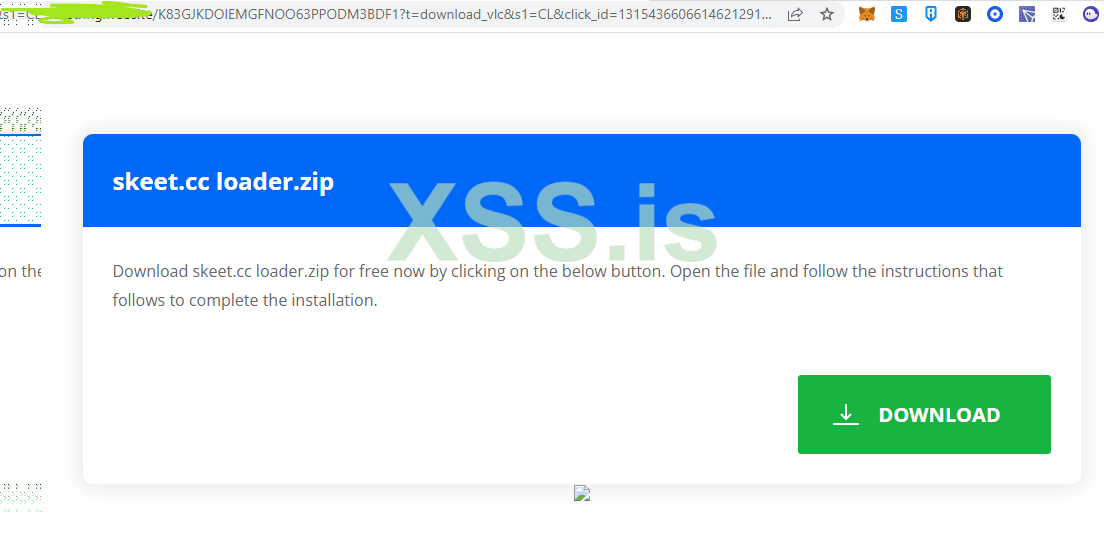
continuing about landing pages, you need to design your landing pages so it will not be downloading files by forcing but tricking. it isn't bad using a download button. also, it's the basic approval phenomenon you should be aware of. other than this, it'll be healthy if you use redirect between multiple landing pages.
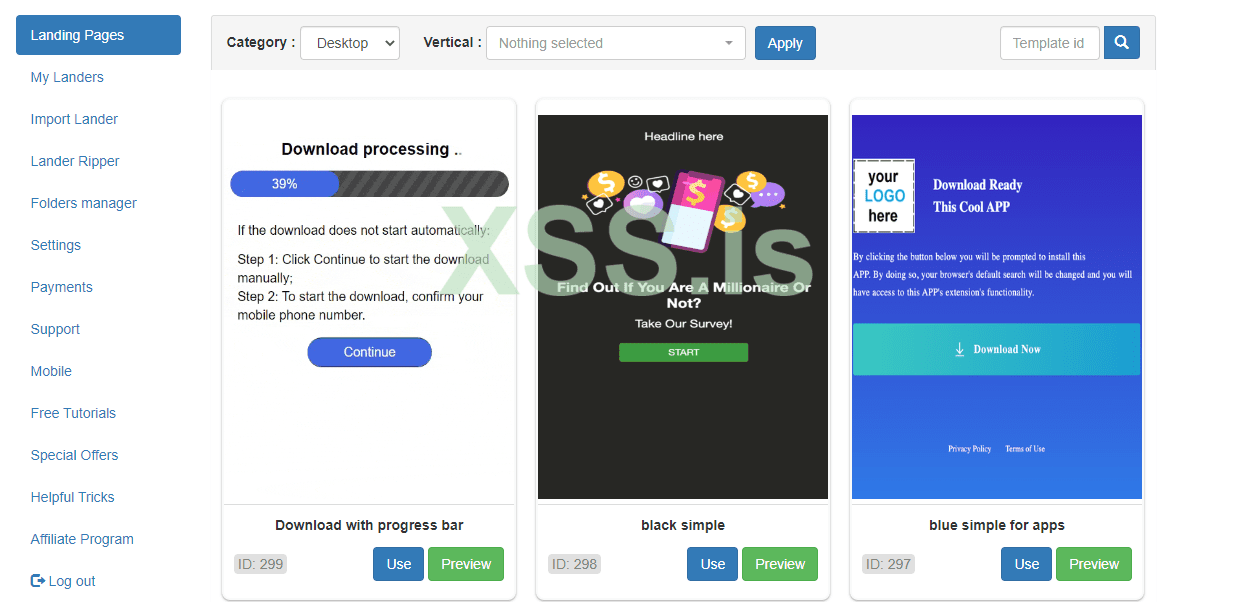
Redirect will help you to the direction of the traffic on the second landing page which is saying download file. you do redirect because putting a redirect download page on the ads network isn't allowed.. more you can learn with their blog section.
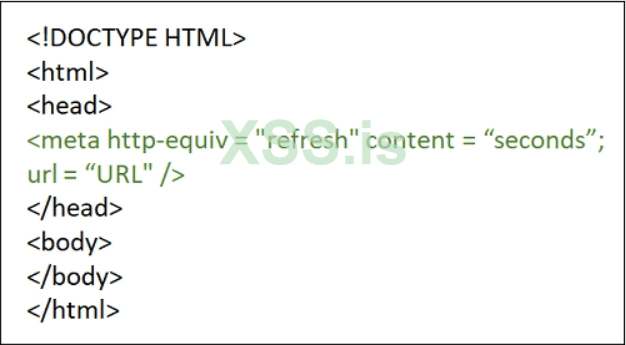
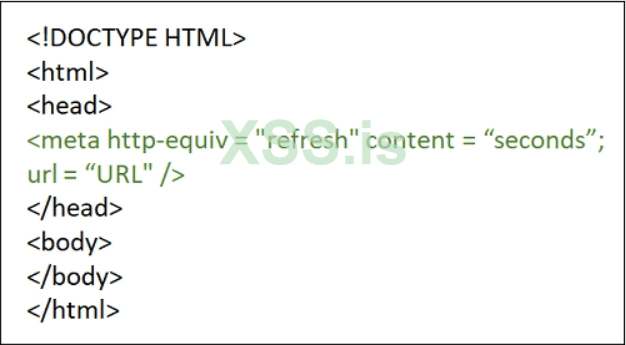
According to google search, when you have a redirect landing page, nothing is shown to the user when the landing page is being redirected to the final URL
you should avoid it in websites, only use it for setting up a redirect for landing to redirect page to offer page to avoid campaign disapproval policies
tracking is useful for making a campaign URL as well as the place where you'll set up your landing pages and offer URL. an offer is simply a task that will get performed. and tracking will let know exactly what task was performed or not it's different than ads network impression stats.
on approval, I already wrote in the landing pages section. also, the campaign design guidelines can be found in ads network setup campaign guides.
The next part is pay per install.
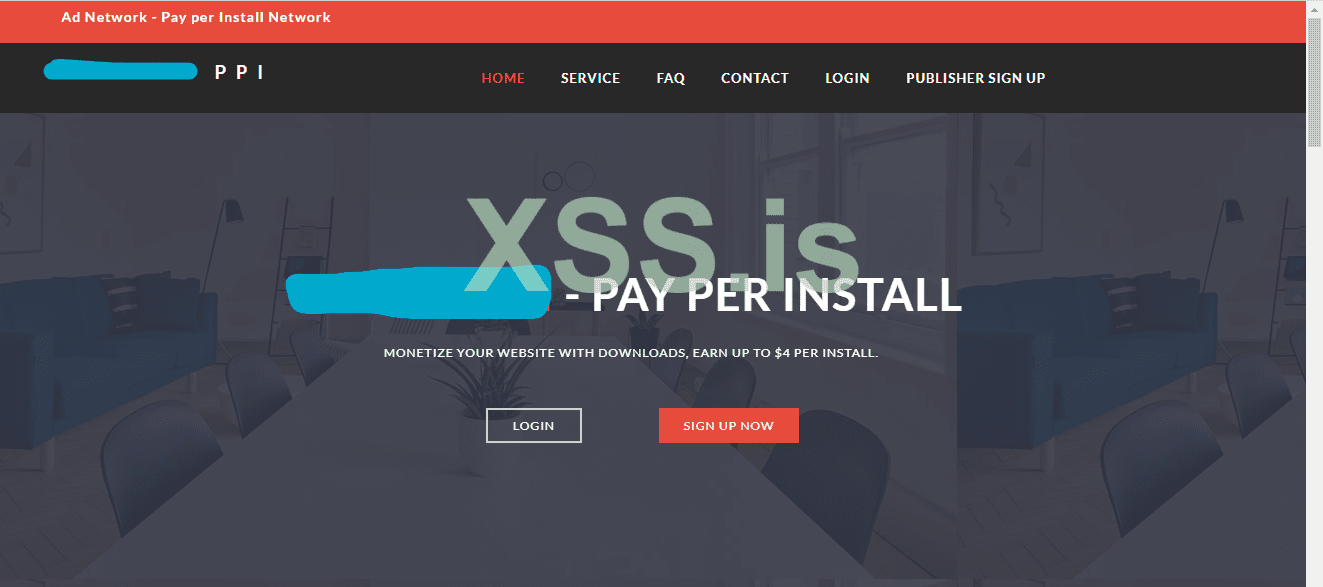
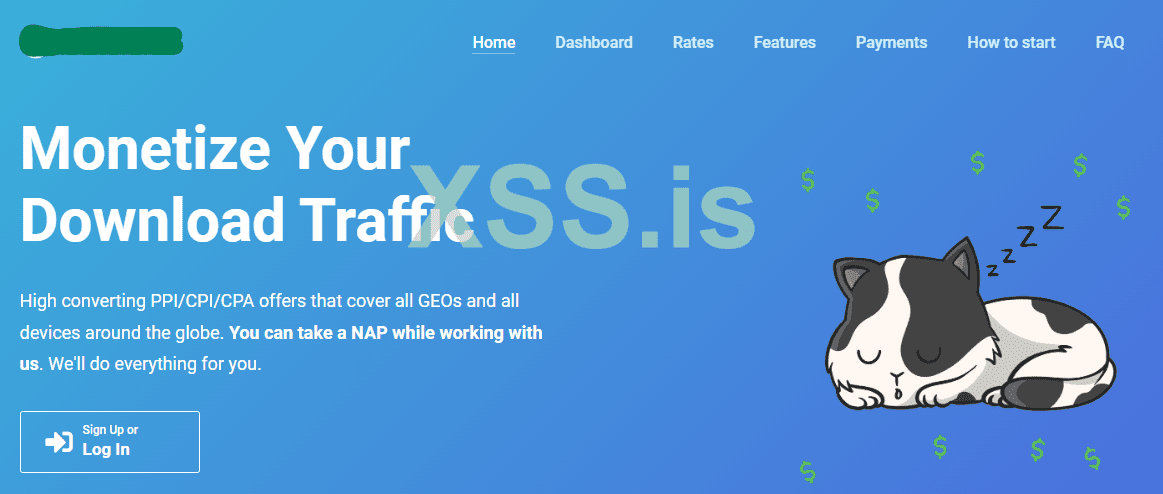
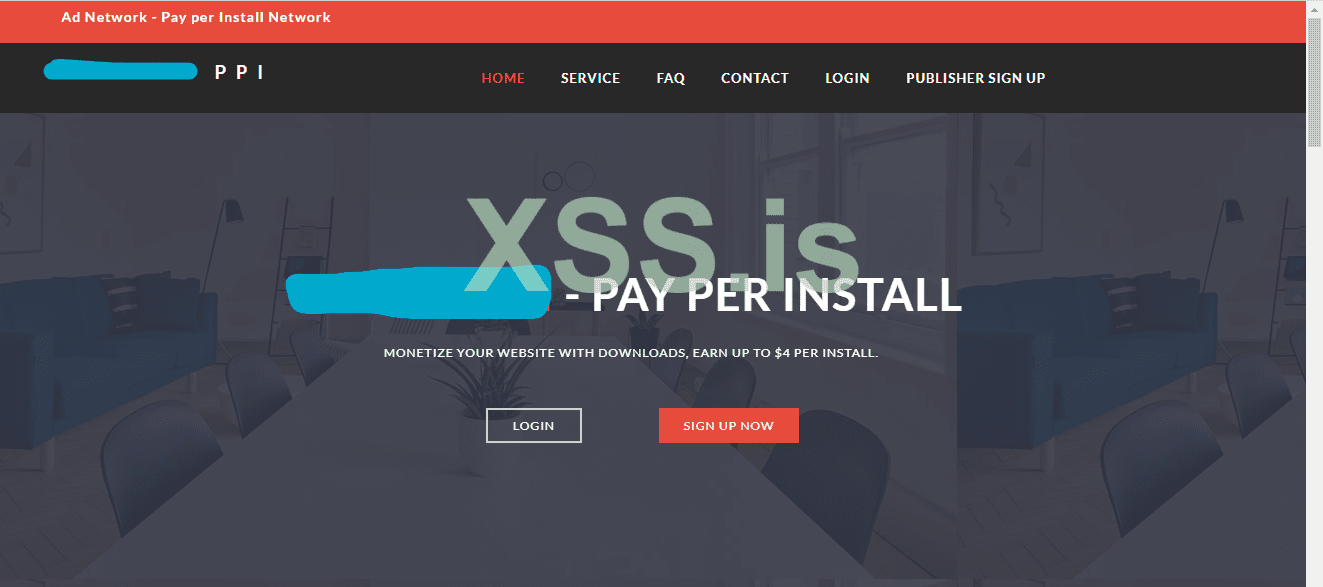
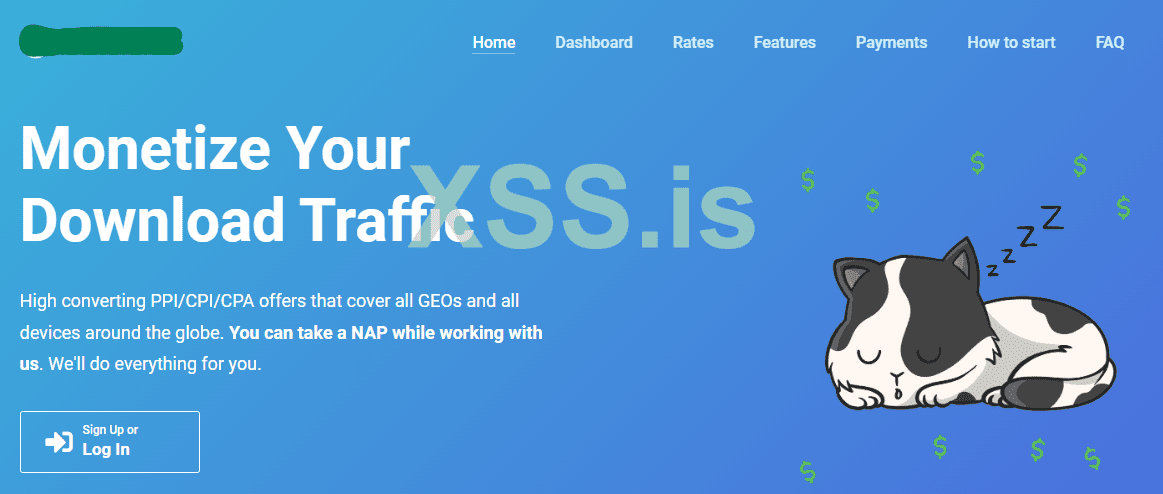
2. Pay per install network
A few years back some Israeli companies come together to provide a service of monetization downloads. simply converting download/software sites.
the idea itself makes their cluster "download velly". also, very less people know about it. the pay per install companies is still offering money to their download bloggers to obtain some fresh conversation which is exclusively called installs.
the PPI also has sub-parts where you could look for buying android traffic from CPI networks. as well as mac installs as they claimed.
The working principle of the PPI ad network is very straight like a gay! and I don't care what homos do. also, the technique behind PPI can be used to create an own network of installs by involving video/software/music/torrent websites.
simply the campaign setup is like an offer fillup form:
Greetings! thanks.
---------start---------------
-> for desktop software — Exe installer running in silent mode,
-> which company do you represent?
-> a brief description of the product in 1-2 sentences;
-> logo;
-> license agreement;
-> privacy policy;
-> how much are you willing to pay to install your software? Provide information in the context of the GEO you are interested in (in the format GEO = price);
-> what is your budget for distribution purposes and is this a one-time promotion, are you ready to work permanently?
-> do you have a system for collecting statistics (sending back, perhaps you are ready to provide us with statistics by mail) or will we need to collect them ourselves?
-> specify which type of distribution you are interested in:
- embedding in software/game installers
- banner (example of a banner used to advertise one of the suppliers - https://www.dropbox.com/s/sr2qz7fhevxws83/img-2019-08-21-12-03-23.png?dl=0 )
-> can you provide a suggestion screen and text for promotional materials?
-> do you only accept traffic from desktop computers or also from mobile devices? Which OS?
-> what method of monetization of your software do you use?
We will also be glad to cooperate!d.
-----------end--------------------
The third way to gain installs in bulk and mainly mass spreading is all about sending emails to valid lists.
3. Spreading via exploits
the vulnerability of the machine is simply attacked, an exploiter can do various tasks unlike sending a file extension directly we can parse its code to another extension that will carry the malicious file, and it's something like a trojan horse.
I think most of us are aware of exploits. doc, pdf, link, xll, etc. so let's talk about how we can use an exploit for mass spreading.
a) via mailers to reach inbox files.
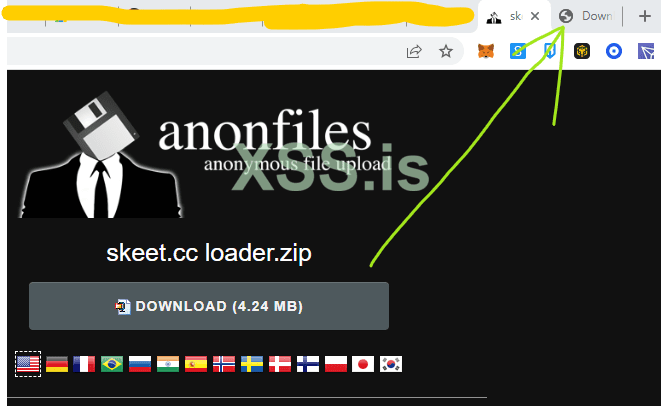
b) via fake websites offering to download unique material.
using mailers is for starting an email campaign and spreading files to email inboxes. another part of setting email campaigns is :
a.a) simple mail transfer protocol
a.b) a mailer, of course.
a.c) email list - valid
a.d) a good letter
on the other hand, setting up fake websites needs a lot of time. but you can make the process faster with driving traffic.
Bonus method,
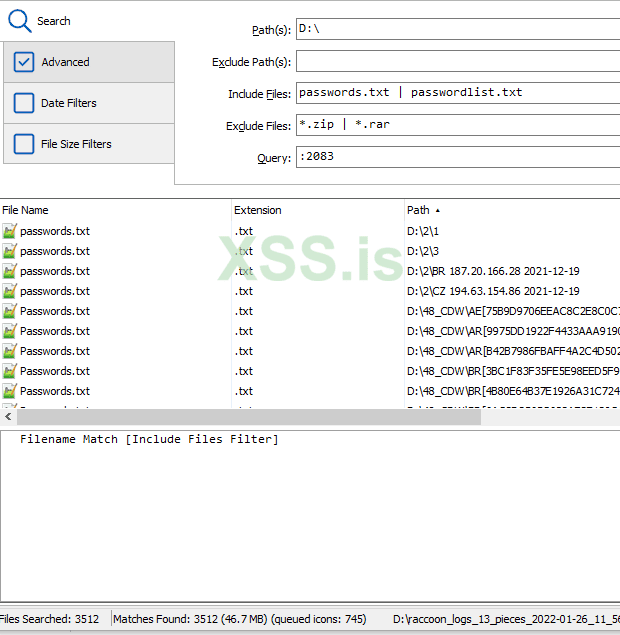
The fourth method I wish to write is spreading via old logs.
yes, it's a good part of a when it comes to stealer data, especially where no one looks, the work is to search through logs and collect hosting accounts for websites with a satisfactory amount of traffic. you can collect 20-30 websites with a good amount of traffic, furthermore, hijack the domain for using it to send traffic to a fake website or add your download ads to them.
the monthly traffic charts can be obtained online. the internet is very huge. we can simply look for sites that tell other website traffic.
other than these 4 methods others are known like:
a) botshops - A telegram shops that drive loader-based traffic
b) youtube/Facebook - very costly but good decent results in the end.
c) forum, telegram, reply sections on blogs.
In final words, the usage of these methods for discovering new methods is possible. it takes less time to do than think.
 lets's just simply dive into info.
lets's just simply dive into info. 
First of all, spreading work is very boring work.. and without proper guidance, it's almost a disaster. so, I include these three methods to make things easier.
1. spreading via traffic
2. spreading via PPI networks, also.
3. spreading via vulnerability
so let's start with the first method, on live traffic.
1. spreading via traffic
when you use an ad network to perform installs you first need a CPA-based ad network. CPA stands for cost per action or performance-based marketing as redefined part.
a CPA network is a part of the advertising industry that mainly focuses on actions or is called a complete task. let's assume we have opened the browser. the first thing the browser will do is give us an identity for eg: Unknown.
when we first open a search engine and search some text we are identified as a user
when we reach a certain website according to our search we become traffic
when we choose some from websites like a product or something and checkout. we become a customer.
the main focus of CPA network is making customers.
not only CPA ad networks but also landing pages are needed. the full list is:
a) CPA ads network or performance-based ad network
b) landing pages
c) tracking
d) approval
continuing about landing pages, you need to design your landing pages so it will not be downloading files by forcing but tricking. it isn't bad using a download button. also, it's the basic approval phenomenon you should be aware of. other than this, it'll be healthy if you use redirect between multiple landing pages.
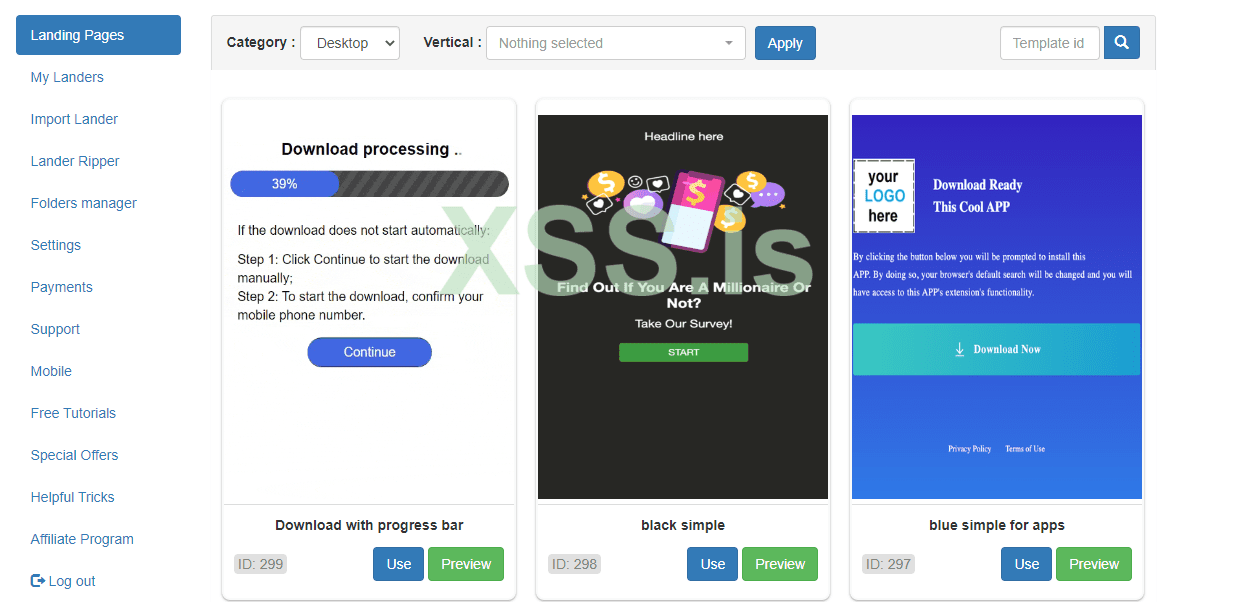
Redirect will help you to the direction of the traffic on the second landing page which is saying download file. you do redirect because putting a redirect download page on the ads network isn't allowed.. more you can learn with their blog section.
According to google search, when you have a redirect landing page, nothing is shown to the user when the landing page is being redirected to the final URL
you should avoid it in websites, only use it for setting up a redirect for landing to redirect page to offer page to avoid campaign disapproval policies

tracking is useful for making a campaign URL as well as the place where you'll set up your landing pages and offer URL. an offer is simply a task that will get performed. and tracking will let know exactly what task was performed or not it's different than ads network impression stats.
on approval, I already wrote in the landing pages section. also, the campaign design guidelines can be found in ads network setup campaign guides.
The next part is pay per install.
2. Pay per install network
A few years back some Israeli companies come together to provide a service of monetization downloads. simply converting download/software sites.
the idea itself makes their cluster "download velly". also, very less people know about it. the pay per install companies is still offering money to their download bloggers to obtain some fresh conversation which is exclusively called installs.
the PPI also has sub-parts where you could look for buying android traffic from CPI networks. as well as mac installs as they claimed.
The working principle of the PPI ad network is very straight like a gay! and I don't care what homos do. also, the technique behind PPI can be used to create an own network of installs by involving video/software/music/torrent websites.
simply the campaign setup is like an offer fillup form:
Greetings! thanks.
---------start---------------
-> for desktop software — Exe installer running in silent mode,
-> which company do you represent?
-> a brief description of the product in 1-2 sentences;
-> logo;
-> license agreement;
-> privacy policy;
-> how much are you willing to pay to install your software? Provide information in the context of the GEO you are interested in (in the format GEO = price);
-> what is your budget for distribution purposes and is this a one-time promotion, are you ready to work permanently?
-> do you have a system for collecting statistics (sending back, perhaps you are ready to provide us with statistics by mail) or will we need to collect them ourselves?
-> specify which type of distribution you are interested in:
- embedding in software/game installers
- banner (example of a banner used to advertise one of the suppliers - https://www.dropbox.com/s/sr2qz7fhevxws83/img-2019-08-21-12-03-23.png?dl=0 )
-> can you provide a suggestion screen and text for promotional materials?
-> do you only accept traffic from desktop computers or also from mobile devices? Which OS?
-> what method of monetization of your software do you use?
We will also be glad to cooperate!d.
-----------end--------------------
The third way to gain installs in bulk and mainly mass spreading is all about sending emails to valid lists.
3. Spreading via exploits
the vulnerability of the machine is simply attacked, an exploiter can do various tasks unlike sending a file extension directly we can parse its code to another extension that will carry the malicious file, and it's something like a trojan horse.
I think most of us are aware of exploits. doc, pdf, link, xll, etc. so let's talk about how we can use an exploit for mass spreading.
a) via mailers to reach inbox files.
b) via fake websites offering to download unique material.
using mailers is for starting an email campaign and spreading files to email inboxes. another part of setting email campaigns is :
a.a) simple mail transfer protocol
a.b) a mailer, of course.
a.c) email list - valid
a.d) a good letter
on the other hand, setting up fake websites needs a lot of time. but you can make the process faster with driving traffic.
Bonus method,
The fourth method I wish to write is spreading via old logs.
yes, it's a good part of a when it comes to stealer data, especially where no one looks, the work is to search through logs and collect hosting accounts for websites with a satisfactory amount of traffic. you can collect 20-30 websites with a good amount of traffic, furthermore, hijack the domain for using it to send traffic to a fake website or add your download ads to them.
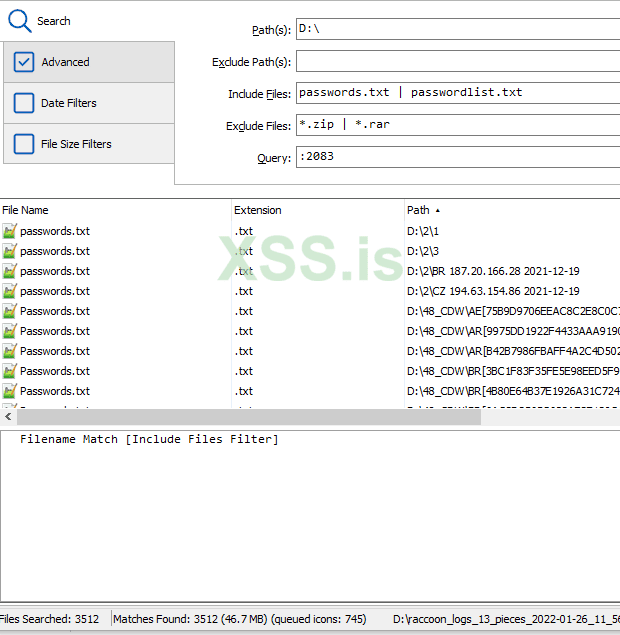
the monthly traffic charts can be obtained online. the internet is very huge. we can simply look for sites that tell other website traffic.
other than these 4 methods others are known like:
a) botshops - A telegram shops that drive loader-based traffic
b) youtube/Facebook - very costly but good decent results in the end.
c) forum, telegram, reply sections on blogs.
In final words, the usage of these methods for discovering new methods is possible. it takes less time to do than think.