- Автор темы
- Добавить закладку
- #101
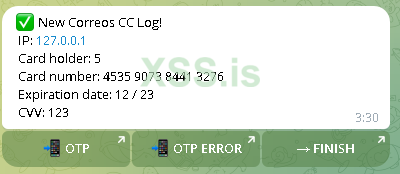
(+) EnZona Cuban Site Scampage Live Panel: https://streama...
I was just sharing my experience.
In your photos it is possible to notice how the source has been protected through the use of a `gzinflate` function which then proceeds to execute the base64 "protected" content.
When I bought the kit, I took care to check all the files inside it (as you should normally do when buying something from someone) and I haven't noticed any kind of function/mechanism like this being used.
I find it hard to believe that the developer uses these features only on some kits, in my experience generally you copy blocks of code from one part to another to speed up the development of new pages.
If you are convinced of what you say, and you have real evidence, I invite you to open a complaint against MoPharma through the forum administrator.
Sharing a screenshot without showing further evidence has no value, why you didn't publish any correspondence between you guys? That phishing kit could be made by anyone.
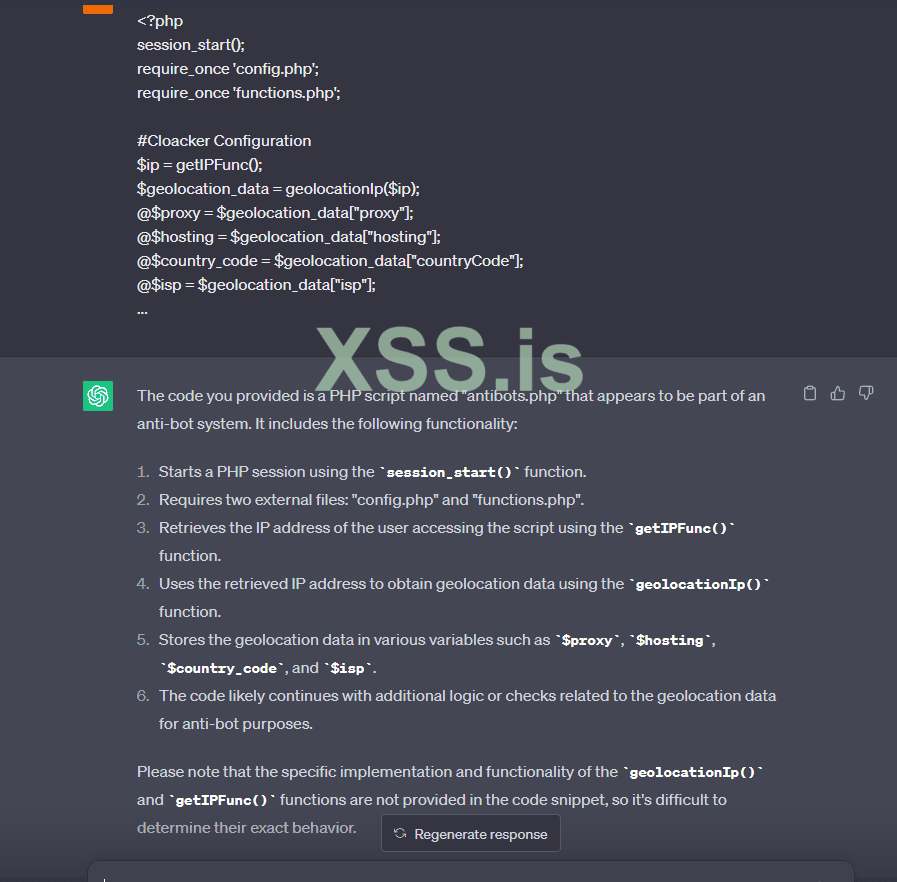
Furthermore, as you're stating that the `antibots.php` file was backdoored, here's the one present in the phishing page I bought.
As you can see everything is clear as water and it doesn't contain any kind of strange function which could potentially execute malicious code/exfil your data.
Bash:~/*****/*****/*****/*****/*****/*****/anti ❯ cat antibots.php <?php session_start(); require_once 'config.php'; require_once 'functions.php'; #Cloacker Configuration $ip = getIPFunc(); $geolocation_data = geolocationIp($ip); @$proxy = $geolocation_data["proxy"]; @$hosting = $geolocation_data["hosting"]; @$country_code = $geolocation_data["countryCode"]; @$isp = $geolocation_data["isp"]; ...