Hello
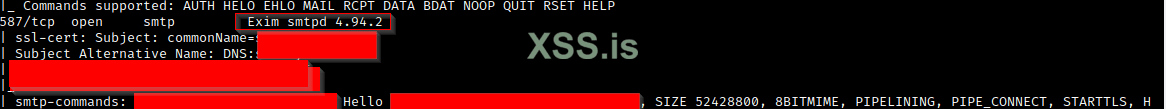
I found a server that may be exploitable by the above CVE but I have no fucking idea when it comes to using C.
When I try to run a proof of concept found on github I'm met with permissions error.
I'm unsure if I need to compile the file exploit.c first. When I try to compile it with gcc I get a error messages saying 'usr/bin/ld: exploit.c.text+0x114): undefined reference to `OPENSSL_init_ssl'. Thats just one example. Most of the errors seem to be related to SSL.
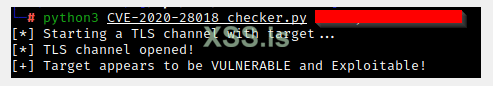
python script included in poc says site is vulnerable to CVE

 github.com
github.com
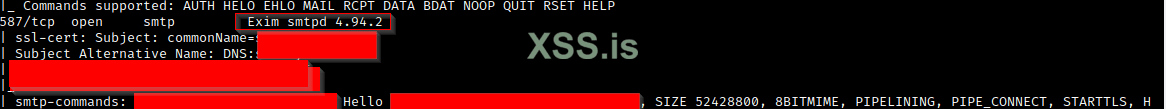
I found a server that may be exploitable by the above CVE but I have no fucking idea when it comes to using C.
When I try to run a proof of concept found on github I'm met with permissions error.
I'm unsure if I need to compile the file exploit.c first. When I try to compile it with gcc I get a error messages saying 'usr/bin/ld: exploit.c.text+0x114): undefined reference to `OPENSSL_init_ssl'. Thats just one example. Most of the errors seem to be related to SSL.
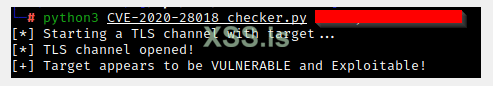
python script included in poc says site is vulnerable to CVE

GitHub - dorkerdevil/CVE-2020-28018: exim use after free exploit and detection
exim use after free exploit and detection. Contribute to dorkerdevil/CVE-2020-28018 development by creating an account on GitHub.