Dear Friends,
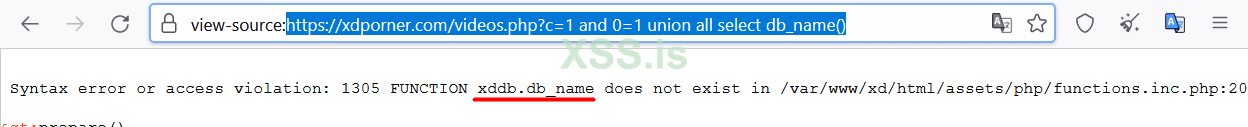
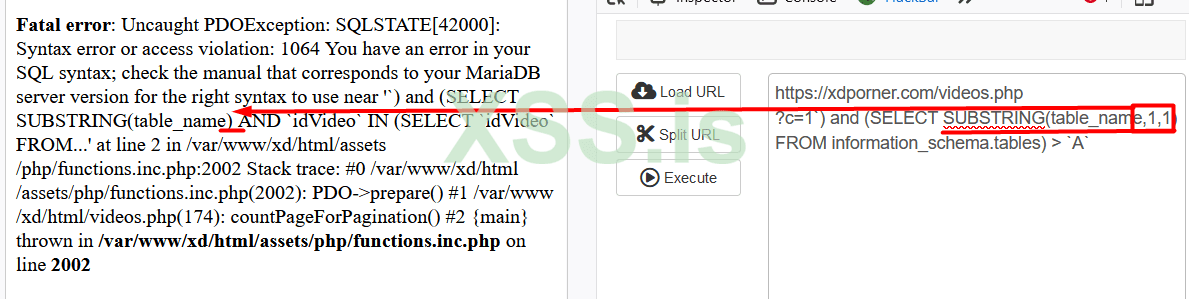
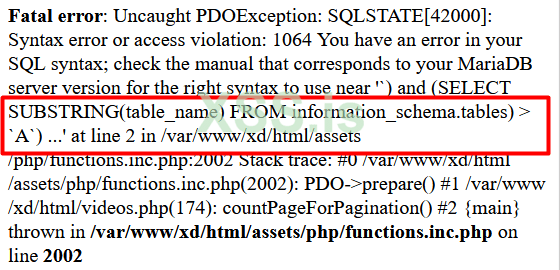
I found SQL injection in one website but I can't fetch the database via sqlmap and manually also.
Here is the detail:
Link: https://xdporner.com/videos.php?c=1\
Please help me with this. if you reach to database please all step in txt file.
Sorry for poor English
Thanks in advance.
I found SQL injection in one website but I can't fetch the database via sqlmap and manually also.
Here is the detail:
Link: https://xdporner.com/videos.php?c=1\
Please help me with this. if you reach to database please all step in txt file.
Sorry for poor English
Thanks in advance.