hello, hope u are doing fine,
Mirari is a Reflective Dll Loader Coded in c / cpp, and it will be sold with its complete source code
How Does Mirari Work:
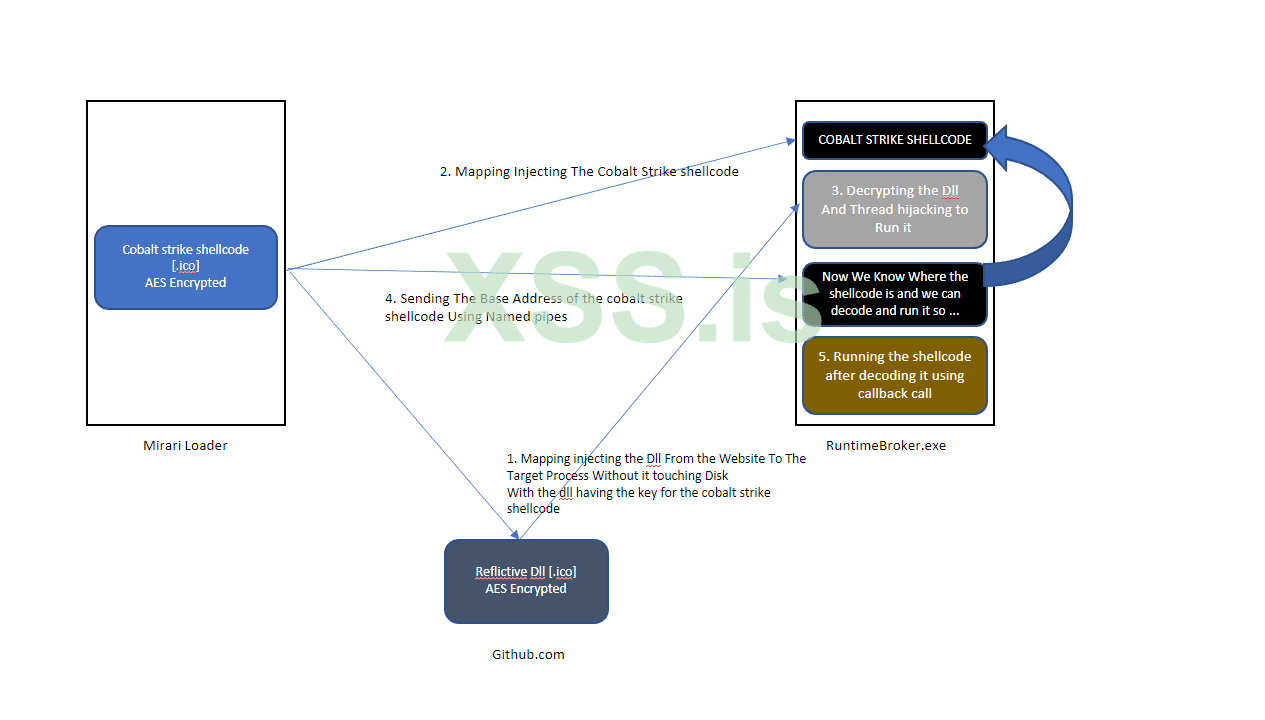
1 - Mirari loader will have 2 payloads to inject, the reflective dll and your shellcode [lets say cobalt strike]
2 - first based on what u entered in the builder, Mirari can detect sandboxes and emulators as well as it has the ability to delete itself while execution [directly when being executed]
3 - when the optional features are executed, Mirari will read the dll [AES encrypted] from the web [Ex: github] without touching the disk and inject it to RuntimeBroker.exe
4 - it uses Mapping injections [using syscalls] to do so, it then map cobalt strike shellcode [which is also AES encrypted] to the same Process
5 - when it does so, it decrypts and runs the dll, the dll will get the base address [our encrypted shellcode in memory] passed from our loader, and decode it with a key that is built in the dll
6 - note here that the dll is encrypted with another key than cobalt strike shellcode encryption key, and the loader doesnt have both keys, which means that cobalt strike is decoded only when the dll is executed.
7 - the reflective dll is executed using thread hijacking [with no suspend / resume thread apis]
8 - the shellcode is executed from the dll using a callback api with a delay. so the loader can be deleted and done executing and still the real payload is not yet executed.
to understand it better, here is a very basic pic on how it work:
More Details:
- In addition Mirari Loader get the api calls without exporting them to the IAT, using a custom function [that act like getprocaddress and getmodulehandle]
- It doesn't have all the functions that are found in a normal loader, [Allocating, Writing, and Running] instead, these functions are divided with the dll, so even if the it is monitored,
not everything is exported from the same point of view.
- if you chose to delete the loader while execution, no samples can be captured for analysis.
- payloads are stored as ".icon" files
it is for sale for 300 $ with the source code. [and its builder]
for any additional details please feel free to ask anything; Dorzues@protonmail.com
and for ppl interested in other things, we can build custom loaders as ur order.
Mirari is a Reflective Dll Loader Coded in c / cpp, and it will be sold with its complete source code
How Does Mirari Work:
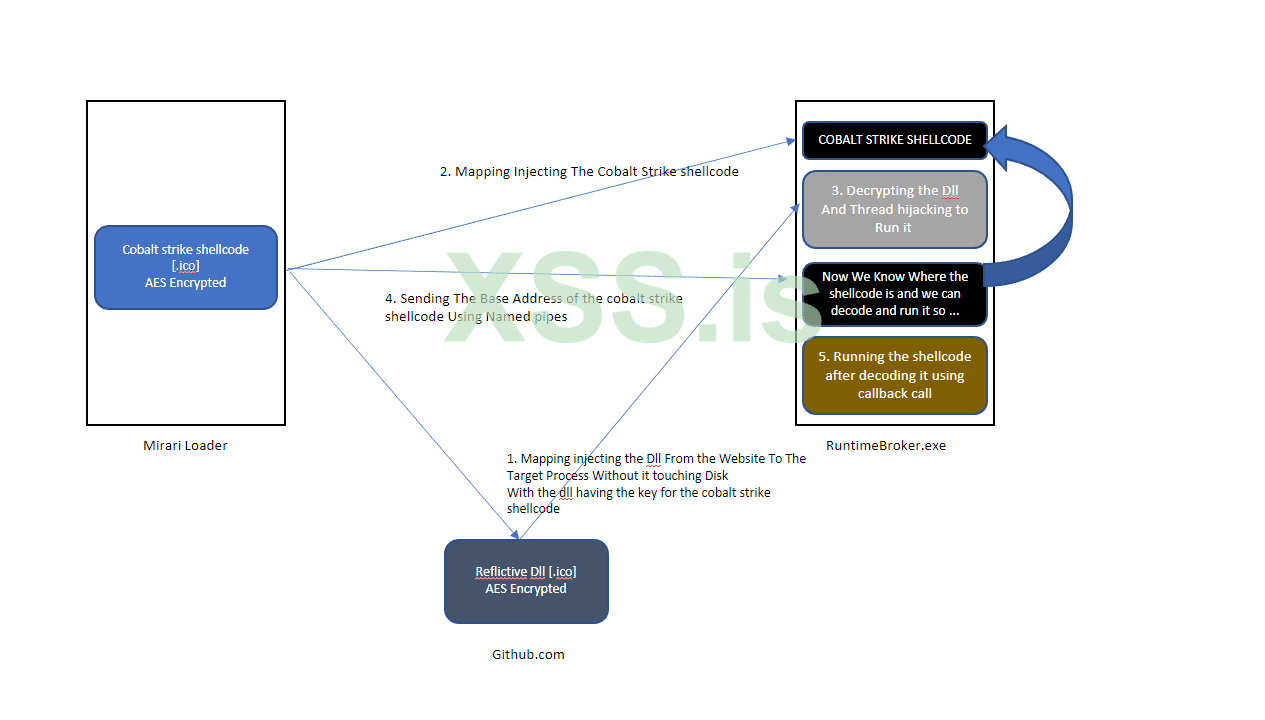
1 - Mirari loader will have 2 payloads to inject, the reflective dll and your shellcode [lets say cobalt strike]
2 - first based on what u entered in the builder, Mirari can detect sandboxes and emulators as well as it has the ability to delete itself while execution [directly when being executed]
3 - when the optional features are executed, Mirari will read the dll [AES encrypted] from the web [Ex: github] without touching the disk and inject it to RuntimeBroker.exe
4 - it uses Mapping injections [using syscalls] to do so, it then map cobalt strike shellcode [which is also AES encrypted] to the same Process
5 - when it does so, it decrypts and runs the dll, the dll will get the base address [our encrypted shellcode in memory] passed from our loader, and decode it with a key that is built in the dll
6 - note here that the dll is encrypted with another key than cobalt strike shellcode encryption key, and the loader doesnt have both keys, which means that cobalt strike is decoded only when the dll is executed.
7 - the reflective dll is executed using thread hijacking [with no suspend / resume thread apis]
8 - the shellcode is executed from the dll using a callback api with a delay. so the loader can be deleted and done executing and still the real payload is not yet executed.
to understand it better, here is a very basic pic on how it work:
More Details:
- In addition Mirari Loader get the api calls without exporting them to the IAT, using a custom function [that act like getprocaddress and getmodulehandle]
- It doesn't have all the functions that are found in a normal loader, [Allocating, Writing, and Running] instead, these functions are divided with the dll, so even if the it is monitored,
not everything is exported from the same point of view.
- if you chose to delete the loader while execution, no samples can be captured for analysis.
- payloads are stored as ".icon" files
it is for sale for 300 $ with the source code. [and its builder]
for any additional details please feel free to ask anything; Dorzues@protonmail.com
and for ppl interested in other things, we can build custom loaders as ur order.