Hello, have you heard about this report ?
 positive.security
positive.security
There is no CVE attached to it but it was released a few days ago. I think the log4j hype has caused people to look elsewhere.
There are some RCE tricks and a cool phishing technique, I'll let you read the paper.
tried to replicate some of the tricks, some things are already fixed, some are not. I'm also interested in what you think.
Sorry for the non-Russian post. I waited for someone to post to read the threads on the topic but nothing came out so I'm posting.
Also I was wondering if this is the good section, or if I better post it into exploitation section so, I apologize if I got it wrong.
have a nice day guys, cheer
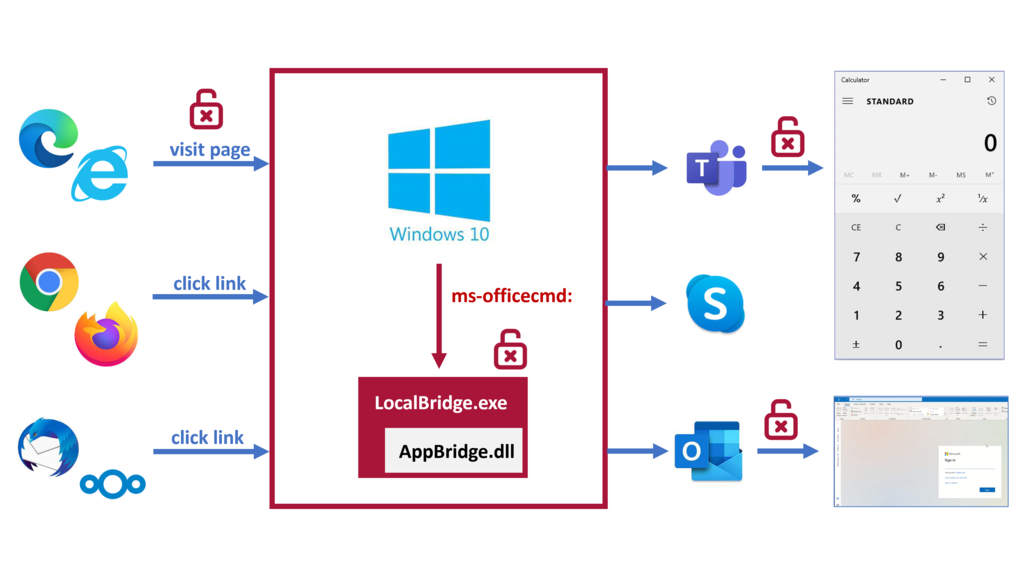
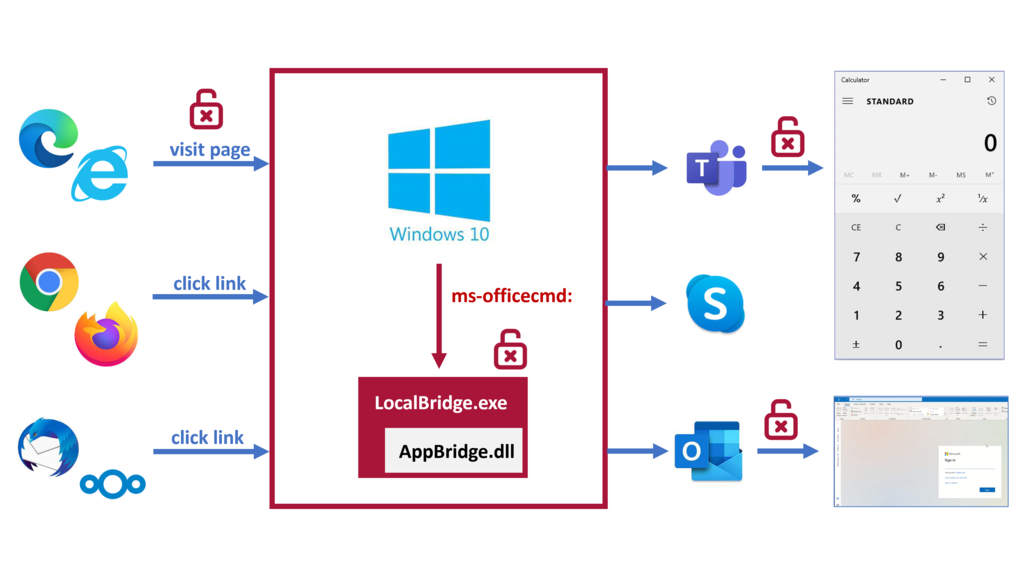
Windows 10 RCE: The exploit is in the link | Positive Security
Chaining a misconfiguration in IE11/Edge Legacy with an argument injection in a Windows 10/11 default URI handler and a bypass for a previous Electron patch, we developed a drive-by RCE exploit for Windows 10. The main vulnerability in the ms-officecmd URI handler has not been patched yet and...
 positive.security
positive.security
There is no CVE attached to it but it was released a few days ago. I think the log4j hype has caused people to look elsewhere.
There are some RCE tricks and a cool phishing technique, I'll let you read the paper.
tried to replicate some of the tricks, some things are already fixed, some are not. I'm also interested in what you think.
Sorry for the non-Russian post. I waited for someone to post to read the threads on the topic but nothing came out so I'm posting.
Also I was wondering if this is the good section, or if I better post it into exploitation section so, I apologize if I got it wrong.
have a nice day guys, cheer