Пожалуйста, обратите внимание, что пользователь заблокирован
Now I personally don't know about many here but I come across this issue with a lot of fake Tor Hidden Service pages often selling fake stuff like "Low Balance Credit cards" or PayPal/Western Union transfers but it's rather funny to see this, I Know Funshine might see this shout out to him.
Now What's better then good old extortion? Not much.... See here's the problem I have with Tor Hidden Service operators: Most people who are inexperienced shouldn't run them and shouldn't be operating one.
I Come across these scam site (They're noted on many DNM Websites for indexing scams, URLs and what have you). So, when I can find your Hosting provider and DNS you seriously got issues you need to fix.
Now going forward this isn't a Tor based issue either this can happen on the clear net by using "Dangling Domains" in a similar manner, This relies on laziness or inexperienced webmasters/IT Teams.
But either way to simply exploit this to expose a Hidden service is quite easily, I Have heard Either Alphabay or Empire suffered from this issue early on but I'm not 100% sure about it.
first let's grab a domain that's vulnerable: http://puyr3jb76flvqemhkllg5bttt2dmiaexs3ggmfpyewc44vt5265uuaad.onion
Noting the fact this website is a scam please don't get upset about it being posted.
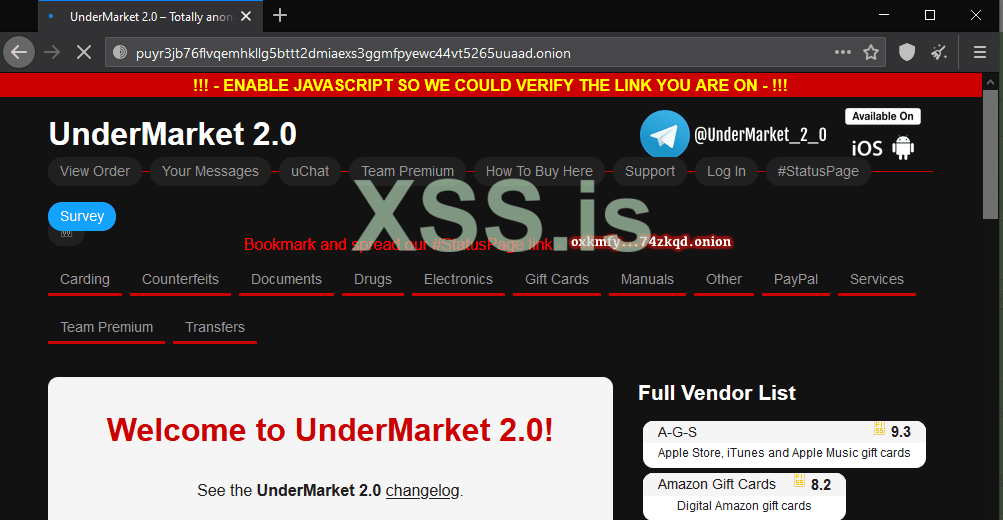
No focus on the domain itself, We'll be adding a few things here
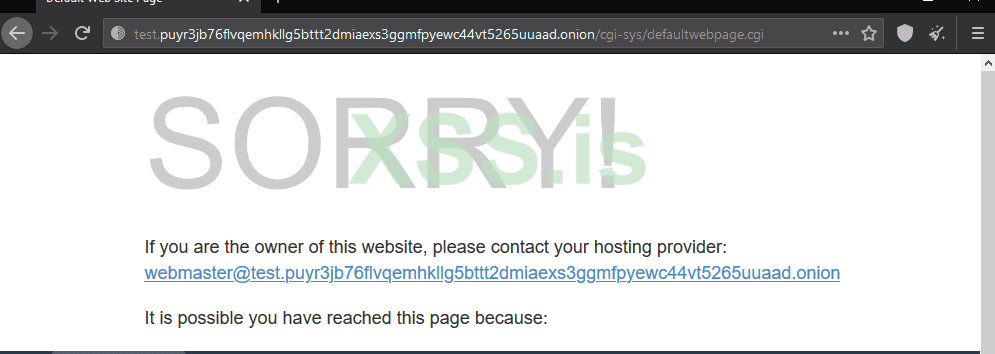
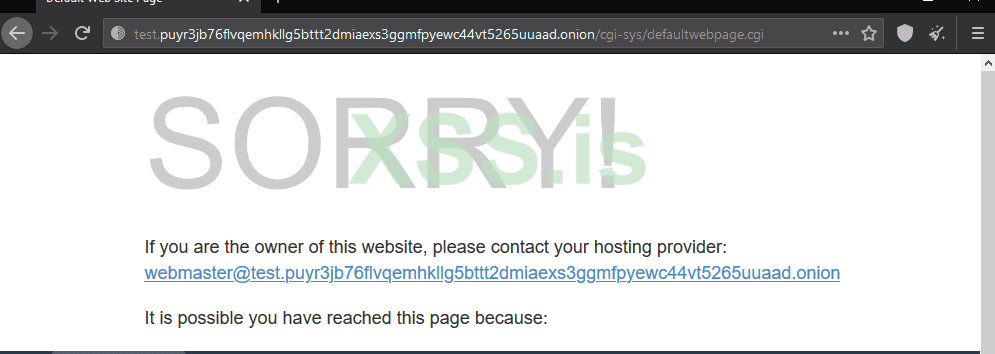
The domain is Modified from http://puyr3jb76flvqemhkllg5bttt2dmiaexs3ggmfpyewc44vt5265uuaad.onion to http://test.puyr3jb76flvqemhkllg5bttt2dmiaexs3ggmfpyewc44vt5265uuaad.onion TEST. is the changing factor that will cause the website to break in of 2 ways.
After the test. insert you'll be greeted with a Cpanel page
Now add delete the long string of useless garbage after the .onion/ and replace with /cpanel as shown below
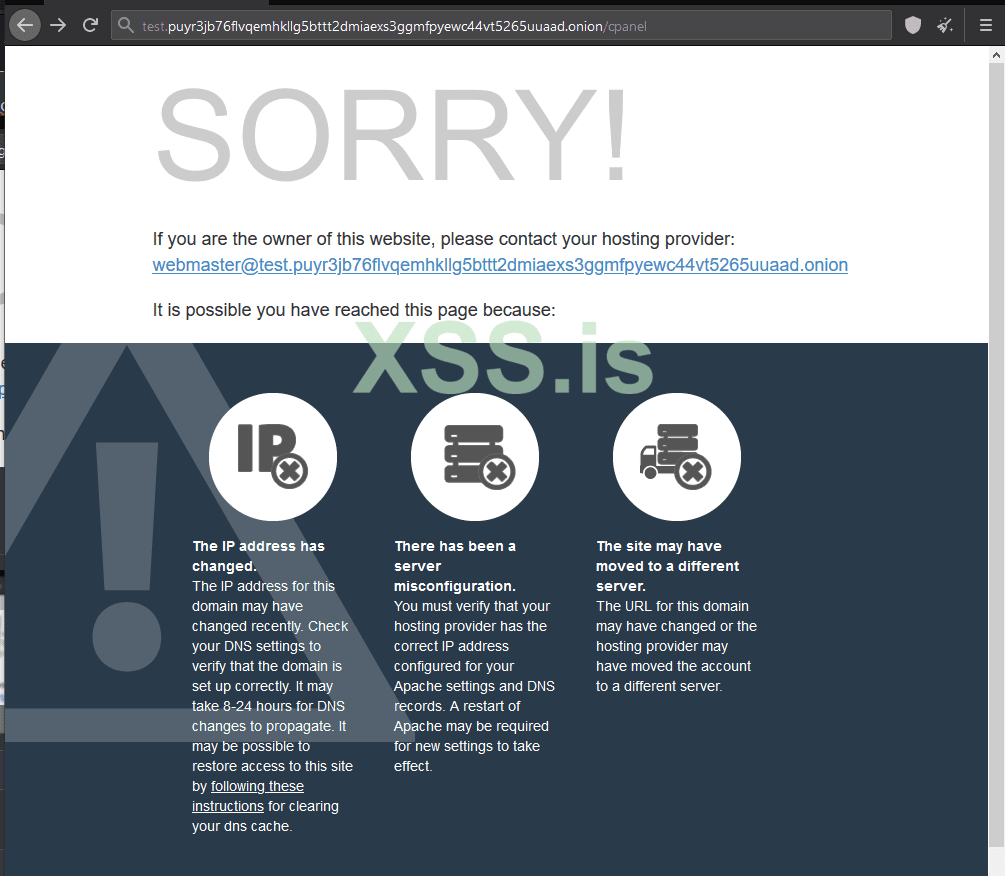
Now Upon hitting enter you can get this lovely Gem:
Now this is one of 2 methods....
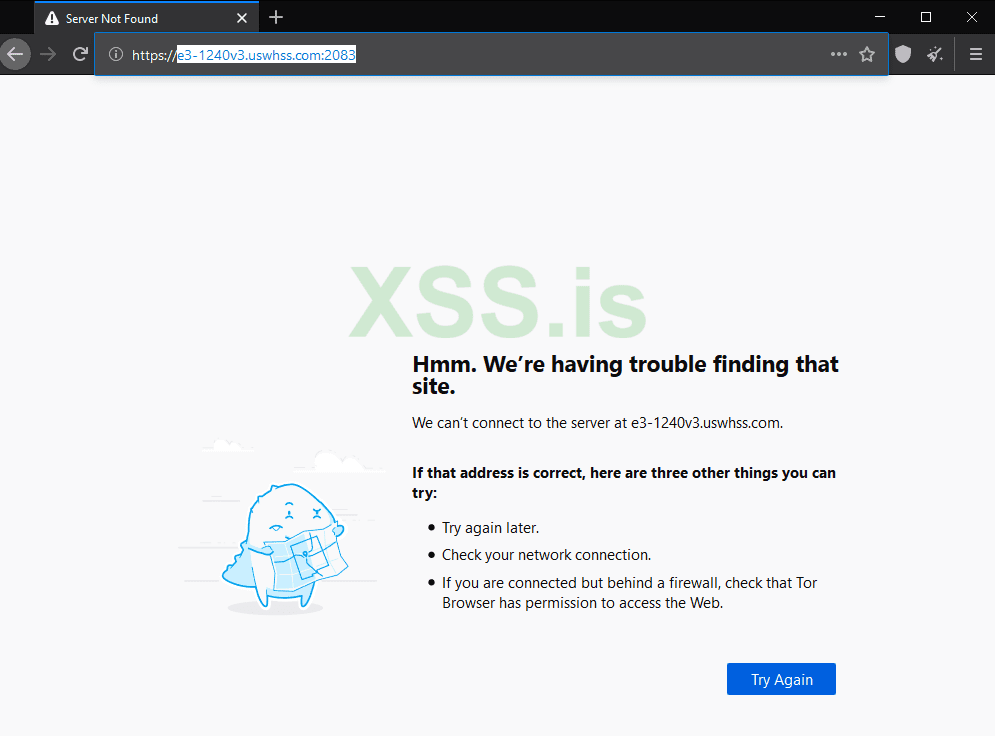
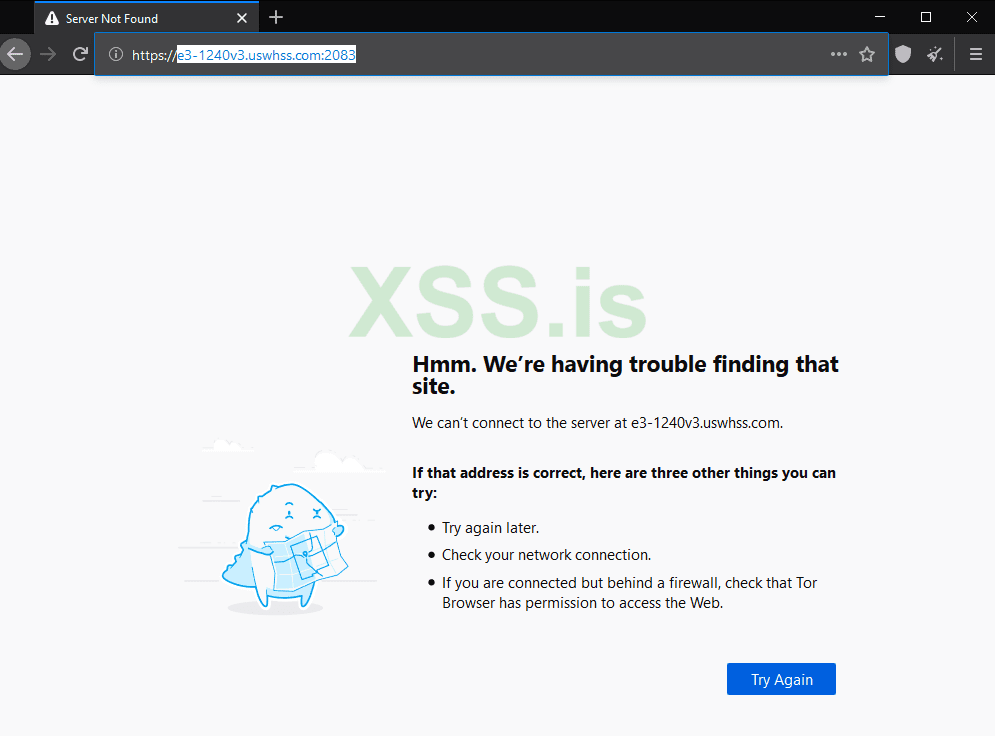
another one will give you a 404 page or something of the like saying that test.xbbaidk3edsertgyhrtyhujuhygtrtyhujhgth.onion/test cannot be found or something.
Now the only difference is if a Cpanel page wasn't there you might get 1 of 2 Errors, You can only due PHP/Apache2/OpenSSL and not PERL/Apache2/OpenSSL Pages.
If no error/redirect occurs at step 1, Add /test to the domain and hit enter should give you an error of some sort.
if the /test gives you the error mentioned above then delete /test and replace with /server status and you should have a bunch of open directories some may contain DBs and other juicy information you can use for extortion or whatever if you steal any Crypto Assets remember I showed you this and a donation would be fairly nice but it's not needed and it should be passed off as humor.
To Conclude this: SECURE YOUR HIDDEN SERVICES. if it's so easy a 5 Year old could commit Grand theft like this, You have issues for not securing your hidden services.
Now What's better then good old extortion? Not much.... See here's the problem I have with Tor Hidden Service operators: Most people who are inexperienced shouldn't run them and shouldn't be operating one.
I Come across these scam site (They're noted on many DNM Websites for indexing scams, URLs and what have you). So, when I can find your Hosting provider and DNS you seriously got issues you need to fix.
Now going forward this isn't a Tor based issue either this can happen on the clear net by using "Dangling Domains" in a similar manner, This relies on laziness or inexperienced webmasters/IT Teams.
But either way to simply exploit this to expose a Hidden service is quite easily, I Have heard Either Alphabay or Empire suffered from this issue early on but I'm not 100% sure about it.
first let's grab a domain that's vulnerable: http://puyr3jb76flvqemhkllg5bttt2dmiaexs3ggmfpyewc44vt5265uuaad.onion
Noting the fact this website is a scam please don't get upset about it being posted.
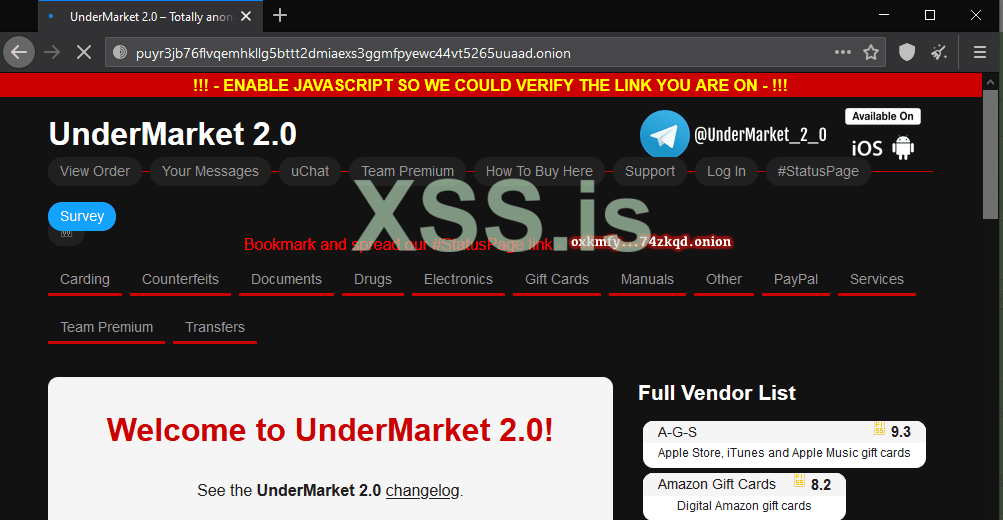
No focus on the domain itself, We'll be adding a few things here
The domain is Modified from http://puyr3jb76flvqemhkllg5bttt2dmiaexs3ggmfpyewc44vt5265uuaad.onion to http://test.puyr3jb76flvqemhkllg5bttt2dmiaexs3ggmfpyewc44vt5265uuaad.onion TEST. is the changing factor that will cause the website to break in of 2 ways.
After the test. insert you'll be greeted with a Cpanel page
Now add delete the long string of useless garbage after the .onion/ and replace with /cpanel as shown below
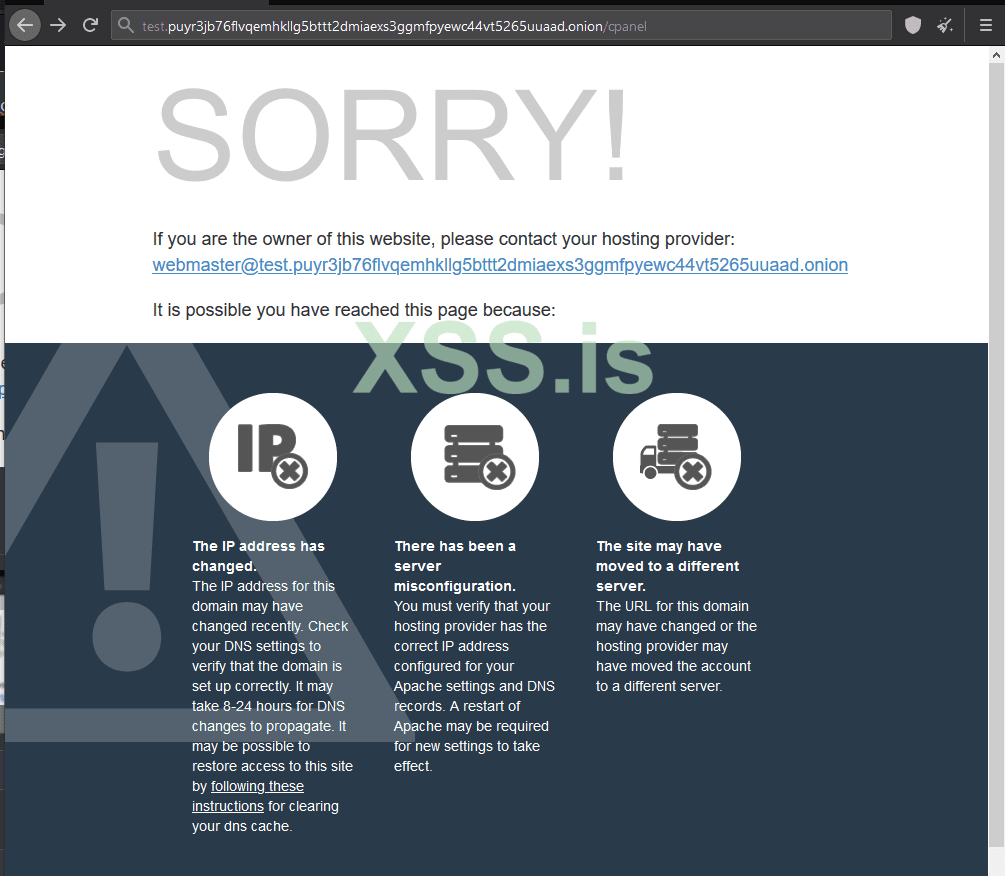
Now Upon hitting enter you can get this lovely Gem:
Now this is one of 2 methods....
another one will give you a 404 page or something of the like saying that test.xbbaidk3edsertgyhrtyhujuhygtrtyhujhgth.onion/test cannot be found or something.
Now the only difference is if a Cpanel page wasn't there you might get 1 of 2 Errors, You can only due PHP/Apache2/OpenSSL and not PERL/Apache2/OpenSSL Pages.
If no error/redirect occurs at step 1, Add /test to the domain and hit enter should give you an error of some sort.
if the /test gives you the error mentioned above then delete /test and replace with /server status and you should have a bunch of open directories some may contain DBs and other juicy information you can use for extortion or whatever if you steal any Crypto Assets remember I showed you this and a donation would be fairly nice but it's not needed and it should be passed off as humor.
To Conclude this: SECURE YOUR HIDDEN SERVICES. if it's so easy a 5 Year old could commit Grand theft like this, You have issues for not securing your hidden services.