Как и обещал, продаюсь за лайки как последняя камвхора.
Забудьте про это:
Там не полная база. Но чтобы такого не было, я немного усложняю задачу. Думаю будет меньше желания раскидываться.
Это прошлая. Расскажи про эту базу
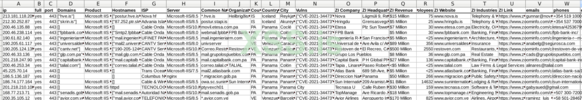
А эта, компоновалась по следующей логике. Была сделана сверка с прошлой базой из Shodan и обнаружена разница в 300к+ хостов, которые тут и выкладываю. Так понятней преимущество Fofa. Наглядно.
Но ты же показывал там почти лям был
Для пытливых умов - дорк /owa содержит мусор, попадается даже Wordpress, поэтому пришлось чистить
С тяп-ляп подходом - базу можно гонять по много раз и каждый раз находить что-то новое. Но надо включать ручки иначе никак. А потом ножки. Ха-Ха
Ну и что, не хитрое дело
Ну, парсить шодан уже некоторые и сами могут, не хитро, в самом деле, поэтому и продаю ключи, не надо от меня и моего парса зависить, я за любые коллаборации. Но это база с Фофы и ее особенность я пояснил. И это не все. Как я чекаю IP2Revenue? Полу-ручной парсинг. В каждую строчку вложен труд и усилия, просмотреть ИП, Хуис, Домены в разных местах, не перепутать с ISP, хостером, партнером, сверить сайт и название, регион и т.п.
http://xssforum7mmh3n56inuf2h73hvhnzobi7h2ytb3gvklrfqm7ut3xdnyd.onion/attachments/26990/http://xssforum7mmh3n56inuf2h73hvhnzobi7h2ytb3gvklrfqm7ut3xdnyd.onion/attachments/26991/http://xssforum7mmh3n56inuf2h73hvhnzobi7h2ytb3gvklrfqm7ut3xdnyd.onion/attachments/26992/
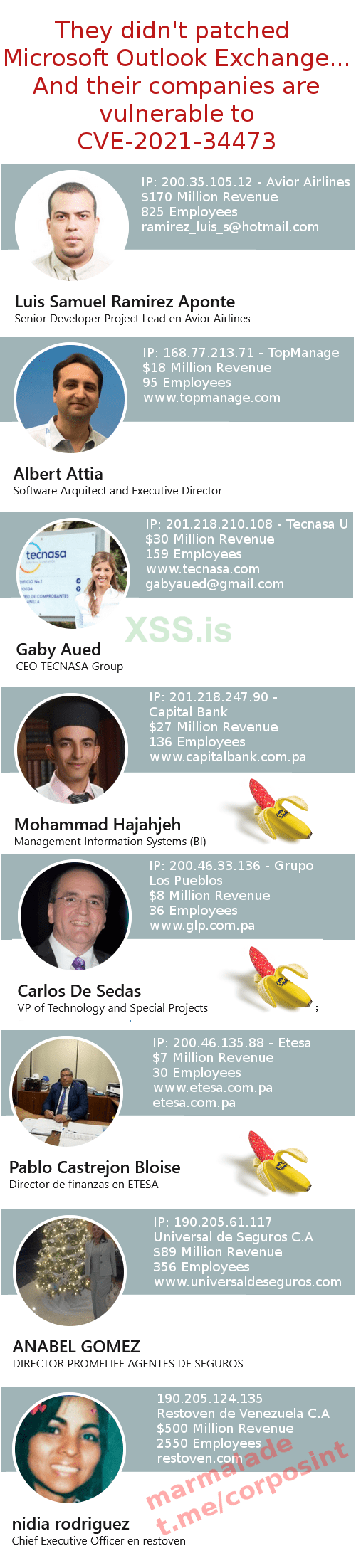
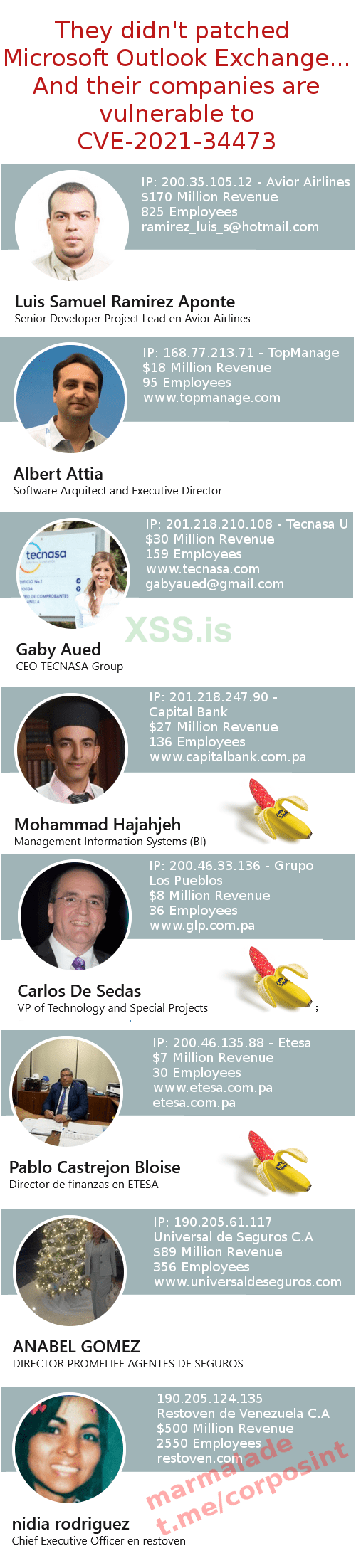
Ну вы только посмотрите...
Банки в Панаме. С дыркой в аутлуке. С местными (чингачгуки) админами. Офшорный финанс. Обновляют софт по календарю майя. Вот здесь и нужны глазки, какой еще многопоточный чекер? Это не то.
Классно, давай по офшорам!
Но это сервера в Панаме. Айпи. Не всегда именно контора. Нужны конторы в Мавритании, Гибралтаре, ГК, BVI. Глазками перепроверяем и находим.
Или по категории, айтишки и софтвар? Аналогично но дополнительным парсером прогоняем.
База для ознакомления! Нужно нанимать целый штат чтобы было красиво. На данный момент так, но уже видно к чему можно стремиться. Открыт к любым предложениям.
А пока,есть два стула, два варианта:
Для умных:
Для деловых:
Благодарю National Hazard Agency за идею
Пошумим?
Ну что, может выложить базу Zoominfo? Вы знаете что делать.
Давайте сделаем 100 и я точно что-то интересное выложу.
UPD: пост будет обновлятся еще в течении дня
Забудьте про это:
Там не полная база. Но чтобы такого не было, я немного усложняю задачу. Думаю будет меньше желания раскидываться.
Это прошлая. Расскажи про эту базу
А эта, компоновалась по следующей логике. Была сделана сверка с прошлой базой из Shodan и обнаружена разница в 300к+ хостов, которые тут и выкладываю. Так понятней преимущество Fofa. Наглядно.
Но ты же показывал там почти лям был
Для пытливых умов - дорк /owa содержит мусор, попадается даже Wordpress, поэтому пришлось чистить
С тяп-ляп подходом - базу можно гонять по много раз и каждый раз находить что-то новое. Но надо включать ручки иначе никак. А потом ножки. Ха-Ха
Ну и что, не хитрое дело
Ну, парсить шодан уже некоторые и сами могут, не хитро, в самом деле, поэтому и продаю ключи, не надо от меня и моего парса зависить, я за любые коллаборации. Но это база с Фофы и ее особенность я пояснил. И это не все. Как я чекаю IP2Revenue? Полу-ручной парсинг. В каждую строчку вложен труд и усилия, просмотреть ИП, Хуис, Домены в разных местах, не перепутать с ISP, хостером, партнером, сверить сайт и название, регион и т.п.
http://xssforum7mmh3n56inuf2h73hvhnzobi7h2ytb3gvklrfqm7ut3xdnyd.onion/attachments/26990/http://xssforum7mmh3n56inuf2h73hvhnzobi7h2ytb3gvklrfqm7ut3xdnyd.onion/attachments/26991/http://xssforum7mmh3n56inuf2h73hvhnzobi7h2ytb3gvklrfqm7ut3xdnyd.onion/attachments/26992/
Ну вы только посмотрите...
Банки в Панаме. С дыркой в аутлуке. С местными (чингачгуки) админами. Офшорный финанс. Обновляют софт по календарю майя. Вот здесь и нужны глазки, какой еще многопоточный чекер? Это не то.
Классно, давай по офшорам!
Но это сервера в Панаме. Айпи. Не всегда именно контора. Нужны конторы в Мавритании, Гибралтаре, ГК, BVI. Глазками перепроверяем и находим.
Или по категории, айтишки и софтвар? Аналогично но дополнительным парсером прогоняем.
База для ознакомления! Нужно нанимать целый штат чтобы было красиво. На данный момент так, но уже видно к чему можно стремиться. Открыт к любым предложениям.
А пока,
Для умных:
У вас должно быть более 50 реакций для просмотра скрытого контента.
Для деловых:
Платный контент.
GIMMEBASE - пароль в ПМ Эта штука оплаты вообще рабочая?
Благодарю National Hazard Agency за идею
Пошумим?
Ну что, может выложить базу Zoominfo? Вы знаете что делать.
Давайте сделаем 100 и я точно что-то интересное выложу.
UPD: пост будет обновлятся еще в течении дня
Вложения
Последнее редактирование: