Пожалуйста, обратите внимание, что пользователь заблокирован
hello, hope ur good everyone,
im selling all in one c2 framework:
first, its coded in c # (the GUI & modules too), and its loader in (c / cpp / assembly).
-------------------------------------------------- --------------------------------------------------------------------------------------------------
the server can output 3 files:
- loader [native exe "undetected"]
- client [net exe, "detected" - and that's why u have a loader, u will know why i kept this output later]
- a shellcode [.bin file]
-----------------------------------------------------------------------------------------------------------------------------------------------------
here is some of its features:
- ur ip address && port numbers that the client needs to connect back to u, can be obtained by pastebin raw url.
this will prevent analyst from getting ur ip, and what they will find is a encrypted string [which is the url]
- the modules [ill get back to them] are injected in memory, and none of them is uploaded to the disk of the victim
- the type of connection is tcp reverse
- have the ability to detect virtual environments [if u chose to]
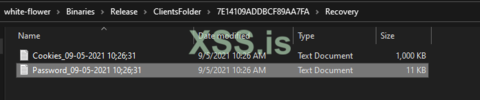
- all credentials that are stolen (passwords / cookies) are saved to a folder carrying the session's id
and recorded audios / screenshots / snaps of camera and the desktop are saved if u want to.
- The number of clients that can connect depends on the amount of RAM and CPU power of the server. For a 2GB RAM and single core CPU, it can easily handle 30 connects.
- Both the client and the server use min Dotnet 4.5, Dotnet 4.5 comes bundled on all Windows 10 and higher computers.
- The RAT has been made modular and plugin based. Each plugin works in its own thread. This ensures non blocking and asynchronous operation.
- the output files, has the ability to sleep [before spawning the session] / detect VMs / evade task mangers [even process hacker]
-------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
the modules [dll files injected in memory]:
- Cmd shell
- Remote Desktop [able to take over the mouse and the keyboards && ability to record]
- Remote Registry Editor
- Remote camera [plus the ability to record snaps of it]
- Remote file manager [allows u to download, upload, execute, rename, copy, paste, compress folder using 7zip,
with the ability to download 7zip if not found, along more shortcuts]
- Process manager [allows u to kill processes]
------------------------------------------------------------------------------------------------------------------
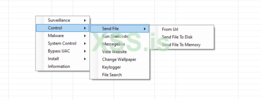
- send file and execute, with the following options:
1- to memory ["Reflectively" to load a dotnet exe && "RunPE" to load a native exe]
2- to disk
3- from url
- execute a shellcode in memory [a bin file]
- some fun modules [message box / changing wallpaper / visiting websites]
- Keylogger
- file searcher [the output will be saved to the logs folder under the client's id]
-----------------------------------------------------------------------------------------------------------------
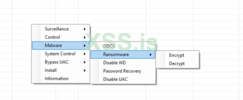
- the hot part:
- Ransomware [ability to encrypt and decrypt]
- ability to disable windows defender and disable uac, [when u are admin, and being an admin is not a problem here ...]
- ddos module that can be set to a website u hate; p
- ability to spread through usb (s)
----------------------------------------------------------------------------------------------------------------
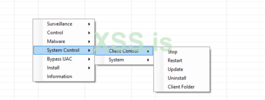
- client control [stop, restart, update, uninstall]
- system control [shutdown, reboot, log out]
---------------------------------------------------------------------------------------------------------------
- bypassing uac, not one module, but 4 different modules [including 3 as bypassing uac and 1 as simply asking cz we are polite ppl]
-----------------------------------------------------------------------------------------------------------------
- installing / uninstalling: 2 kinds:
1- The "schtasks install" copies the client into c: \ windows \ sysnative folder and then adds a scheduled task
by the name GoogleUpdateTaskMachine. This needs admin privs and uses Task Scheduler COM object to perform the task. No binary is executed.
2- The "normal install", the agent checks if it is admin or not.
If not, then it does a normal Registry based startup. If it is admin then it uses the schtasks binary to install persistence.
------------------------------------------------------------------------------------------------------------------
- dumping information [which is a simple module that can dump 148kb of data of useful cmd outputs and save it into logs folder]
-----------------------------------------------------------------------------------------------------------------
-----------------------------------------------------------------------------------------------------------------
Now the loader:
the loader is a native exe, can do the following:
1- use syscalls obtained at run time, through hashses.
2- detect environment and sandboxes before downloading the payload file to temp file [the payload is encrypted bin generated from our server]
3- inject the shellcode to runtimebroker.exe using a new way of process injection [litrally new way ...]
4- all the tasks are automated.
-------------------------------------------------------------------------------------------------------------------
--------------------------------------------------------------------------------------------------------------------
I wanna talk about the detected client now, i know ppl may be saying it is useless or so, but im working on a loader for cobalt strike,
that can inject the net assemblies [even if they are detected] into memory. so it is still useful. and for the ppl who will buy this c2.
the cobalt strike loader will be sold to them 50% less.
-------------------------------------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------------------------------------
How i will sell it (i accept both with guarantor or not):
i will sell it to 10 peoples [for life time]:
5 ppls for 1000 $ [btc / eth]
2 ppls [selling source code] for 2000 $ [btc / eth]
a note for ppl who are thinking in buying the source code. as i said, the modules are dll that are injected into memory.
so if u can code c # u can code ur modules without even changing anything in the rat but some gui.
-------------------------------------------------- -------------------------------------------------- ---------------
-------------------------------------------------- -------------------------------------------------- ---------------
this c2 will have no features update [although i might do it privately], but it will have bug fixes if the users had problems.
for any other questions, feel free to ask me anything.
i will post other things about it later ...
im selling all in one c2 framework:
first, its coded in c # (the GUI & modules too), and its loader in (c / cpp / assembly).
-------------------------------------------------- --------------------------------------------------------------------------------------------------
the server can output 3 files:
- loader [native exe "undetected"]
- client [net exe, "detected" - and that's why u have a loader, u will know why i kept this output later]
- a shellcode [.bin file]
-----------------------------------------------------------------------------------------------------------------------------------------------------
here is some of its features:
- ur ip address && port numbers that the client needs to connect back to u, can be obtained by pastebin raw url.
this will prevent analyst from getting ur ip, and what they will find is a encrypted string [which is the url]
- the modules [ill get back to them] are injected in memory, and none of them is uploaded to the disk of the victim
- the type of connection is tcp reverse
- have the ability to detect virtual environments [if u chose to]
- all credentials that are stolen (passwords / cookies) are saved to a folder carrying the session's id
and recorded audios / screenshots / snaps of camera and the desktop are saved if u want to.
- The number of clients that can connect depends on the amount of RAM and CPU power of the server. For a 2GB RAM and single core CPU, it can easily handle 30 connects.
- Both the client and the server use min Dotnet 4.5, Dotnet 4.5 comes bundled on all Windows 10 and higher computers.
- The RAT has been made modular and plugin based. Each plugin works in its own thread. This ensures non blocking and asynchronous operation.
- the output files, has the ability to sleep [before spawning the session] / detect VMs / evade task mangers [even process hacker]
-------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
the modules [dll files injected in memory]:
- Cmd shell
- Remote Desktop [able to take over the mouse and the keyboards && ability to record]
- Remote Registry Editor
- Remote camera [plus the ability to record snaps of it]
- Remote file manager [allows u to download, upload, execute, rename, copy, paste, compress folder using 7zip,
with the ability to download 7zip if not found, along more shortcuts]
- Process manager [allows u to kill processes]
------------------------------------------------------------------------------------------------------------------
- send file and execute, with the following options:
1- to memory ["Reflectively" to load a dotnet exe && "RunPE" to load a native exe]
2- to disk
3- from url
- execute a shellcode in memory [a bin file]
- some fun modules [message box / changing wallpaper / visiting websites]
- Keylogger
- file searcher [the output will be saved to the logs folder under the client's id]
-----------------------------------------------------------------------------------------------------------------
- the hot part:
- Ransomware [ability to encrypt and decrypt]
- ability to disable windows defender and disable uac, [when u are admin, and being an admin is not a problem here ...]
- ddos module that can be set to a website u hate; p
- ability to spread through usb (s)
----------------------------------------------------------------------------------------------------------------
- client control [stop, restart, update, uninstall]
- system control [shutdown, reboot, log out]
---------------------------------------------------------------------------------------------------------------
- bypassing uac, not one module, but 4 different modules [including 3 as bypassing uac and 1 as simply asking cz we are polite ppl]
-----------------------------------------------------------------------------------------------------------------
- installing / uninstalling: 2 kinds:
1- The "schtasks install" copies the client into c: \ windows \ sysnative folder and then adds a scheduled task
by the name GoogleUpdateTaskMachine. This needs admin privs and uses Task Scheduler COM object to perform the task. No binary is executed.
2- The "normal install", the agent checks if it is admin or not.
If not, then it does a normal Registry based startup. If it is admin then it uses the schtasks binary to install persistence.
------------------------------------------------------------------------------------------------------------------
- dumping information [which is a simple module that can dump 148kb of data of useful cmd outputs and save it into logs folder]
-----------------------------------------------------------------------------------------------------------------
-----------------------------------------------------------------------------------------------------------------
Now the loader:
the loader is a native exe, can do the following:
1- use syscalls obtained at run time, through hashses.
2- detect environment and sandboxes before downloading the payload file to temp file [the payload is encrypted bin generated from our server]
3- inject the shellcode to runtimebroker.exe using a new way of process injection [litrally new way ...]
4- all the tasks are automated.
-------------------------------------------------------------------------------------------------------------------
--------------------------------------------------------------------------------------------------------------------
I wanna talk about the detected client now, i know ppl may be saying it is useless or so, but im working on a loader for cobalt strike,
that can inject the net assemblies [even if they are detected] into memory. so it is still useful. and for the ppl who will buy this c2.
the cobalt strike loader will be sold to them 50% less.
-------------------------------------------------------------------------------------------------------------------
-------------------------------------------------------------------------------------------------------------------
How i will sell it (i accept both with guarantor or not):
i will sell it to 10 peoples [for life time]:
5 ppls for 1000 $ [btc / eth]
2 ppls [selling source code] for 2000 $ [btc / eth]
a note for ppl who are thinking in buying the source code. as i said, the modules are dll that are injected into memory.
so if u can code c # u can code ur modules without even changing anything in the rat but some gui.
-------------------------------------------------- -------------------------------------------------- ---------------
-------------------------------------------------- -------------------------------------------------- ---------------
this c2 will have no features update [although i might do it privately], but it will have bug fixes if the users had problems.
for any other questions, feel free to ask me anything.
i will post other things about it later ...