только без таких тем типо ” как бтутить кашелёк“. Интересует flash loans, reentrance,и тд. Тут кому интересно выкладываю вулнерабилити, но не все:
Код:
Name of weakness
Account Hijacking
API Exposure
Artificial Difficulty Increases
Balance Attack
Bitcoin lightning - Eclipse Attack Time Dilation
Bitcoin lightning - flood and loot
Bitcoin lightning - pinning
Bitcoin lightning - spamming payment micropayments
Block Forger DoS
Block Mining Finney Attack
Block Mining Race Attack
Block Mining Timejack Attack
Block Reordering Attack
Blockchain Ingestion
Blockchain Network Lacks Hash Capacity
Blockchain Network Partitioning Attack
Blockchain Peer flooding Attack
Blockchain Peer flooding Attack Slowloris variant
Blockchain reorganization attack
Blockchain Weak Sources of Randomness
Consensus 34% Attack
Consensus 51% Attack
Consensus Attack
Consensus Attack against PoS
Consensus Attack against PoW
Consensus Delay Attack
Consensus Majority Attack
Credential Stuffing
Cryptomining
Cryptomining Malware
Data corruption
Dictionary Attack
Distributed-Denial-of-Service Attack
DNS Attacks
DoS against Ethereum 2.0 validator to trigger penalty for being offline
Double Spending Attack
Download of Data Without Integrity Check
Dusting attack
Eclipse Attack
EOS RAM Vulnerability
ERC20 token transfer to self token address (and possibly other tokens)
Ethereum Solidity prior to 0.5.0 view promise not enforced
Evil Maid attack
Failure to Update
Fixed Consensus Termination
Flash Loans
Flawed Blockchain Network Design
Fork-after-withhold Attack
Freeloading
Front Running
Front Running displacement
Front Running insertion
Front Running Mempool
Front Running Oracle
Front Running suppression
Frozen ether
Gas Limit DoS on the Blockchain Network via Block Stuffing
Hard fork software update
Hash functions
Homomorphic encryption
Identity and Access Management Overview
Immutable Bugs
Implementation of something they should use a standard library for
Indistinguishable chains
Insecure API Connections
Insider Threat
Leading ether to arbitrary address
Long-Range Attack
Lost ether in the transaction
Majority attack
Malfunctioned MSP
Malicious Mining
Malicious Web Extensions
Membership Service Provider Attacks
Mirroring
Multi-Factor Authentication (MFA)
Multiple signatures
Namespace squatting on internal packages
Network Routing Attacks
Non-existent accounts
Nothing at Stake
On-chain data confidentiality
Orphan Blocks
Parity Multisig Wallet Attack
Permissioned Blockchain MSP DoS
Phishing Attack
Pool Hopping
Private Key Leakage Attack
Public peer selection
Replay Attack
Requirement of keeping real world PII data associated with crypto wallet addresses
Ring signatures
RPC Call vulnerability
Selfish Mining Attack (Block Withholding Attack)
SIM Swap
Single Perspective Validation
Smart Contract Use of Outdated Compiler Version
Smart Contract Access Control - Smart Contract Initialization
Smart Contract Arbitrary Jump with Function Type Variable
Smart Contract Assert Violation
Smart Contract Authorization through tx.origin
Smart Contract Block values as a proxy for time
Smart Contract Call Depth Attack
Smart Contract Call to Unknown function via fallback()
Smart Contract Code With No Effects
Smart Contract Cross-Function Race Condition
Smart Contract default fallback address attack
Smart Contract Delegate call injection
Smart Contract Delegate call to Untrusted Callee
Smart Contract Disordered Exceptions
Smart Contract DoS
Smart Contract DoS With Block Gas Limit
Smart Contract DoS with Failed Call
Smart Contract DoS with unbounded operations
Smart Contract DoS with unexpected revert
Smart Contract Erroneous constructor name
Smart Contract Erroneous visibility
Smart Contract Ether Lost in Transfer
Smart Contract Ether lost to orphan address
Smart Contract Ethereum Gasless Send
Smart Contract Floating Pragma
Smart Contract Forcibly Sending Ether to a Contract
Smart Contract has undocumented "onlyOwner" termination function or other capability
Smart Contract Hash Collisions With Multiple Variable Length Arguments
Smart Contract Immutable Bugs
Smart Contract Incorrect Constructor Name
Smart Contract Incorrect ERC20 implementation
Smart Contract Incorrect function state mutability
Smart Contract Incorrect Inheritance Order
Smart Contract Insufficient Gas Griefing
Smart Contract Integer Overflow and Underflow
Smart Contract Keeping Secrets
Smart Contract Lack of Address Key Binding
Smart Contract Lack of Proper Signature Verification
Smart Contract Manipulated balance
Smart Contract Message call with hardcoded gas amount
Smart Contract Mishandled Exceptions
Smart Contract Missing Protection against Signature Replay Attacks
Smart Contract Presence of unused variables
Smart Contract Race Conditions
Smart Contract Reentrancy Race Condition
Smart Contract Requirement Violation
Smart Contract Right-To-Left-Override control character (U+202E)
Smart Contract Shadowing State Variables
Smart Contract Short Address Attack
Smart Contract Signature Malleability
Smart Contract Source Code Unavailable for review
Smart Contract Stack Size Limit
Smart Contract State Variable Default Visibility
Smart contract time related issues
Smart Contract Timestamp Dependency
Smart Contract Transaction Order Dependence
Smart Contract Transaction Ordering Dependency (TOD)
Smart Contract Typecasts
Smart Contract Typographical Error
Smart Contract Unchecked Call Return Value
Smart Contract Unchecked Return Values
Smart Contract Underpriced opcodes
Smart Contract Unencrypted Private Data On-Chain
Smart Contract unexpected call return value
Smart Contract Unexpected Ether balance
Smart Contract Uninitialized Storage Pointer
Smart Contract Unpredictable State
Smart Contract Unprotected Ether Withdrawal
Smart Contract Unprotected SELFDESTRUCT Instruction
Smart Contract Unprotected suicide
Smart Contract upgradeable contract
Smart Contract Usage of "continue" in "do-while"
Smart Contract Use of Deprecated Solidity Functions
Smart Contract Weak Field Modifier
Smart Contract Weak Sources of Randomness from Chain Attributes
Smart Contract Write to Arbitrary Storage Location
Smat Contrct Function Default Visibility
Soft Forks
Sole Block Synchronization
Stealth addresses
Sybil Attacks
Time Manipulation
Timebomb
Timejacking
Transaction Flooding
Transaction malleability
Two-Factor Authentication (2FA)
Two-Factor Authentication (2FA) via Biometrics
Two-Factor Authentication (2FA) via Email
Two-Factor Authentication (2FA) via SMS
Typo squatting on spellcheck names
Uncle block rewards
Uncle Forks
Unlimited incoming connections
Vector76
Voice Assistant Attack
Vote Token trapping
Vulnerabilities in virtual machines(EVM,JVM)
Vulnerability to Malware
Vulnerable Signatures
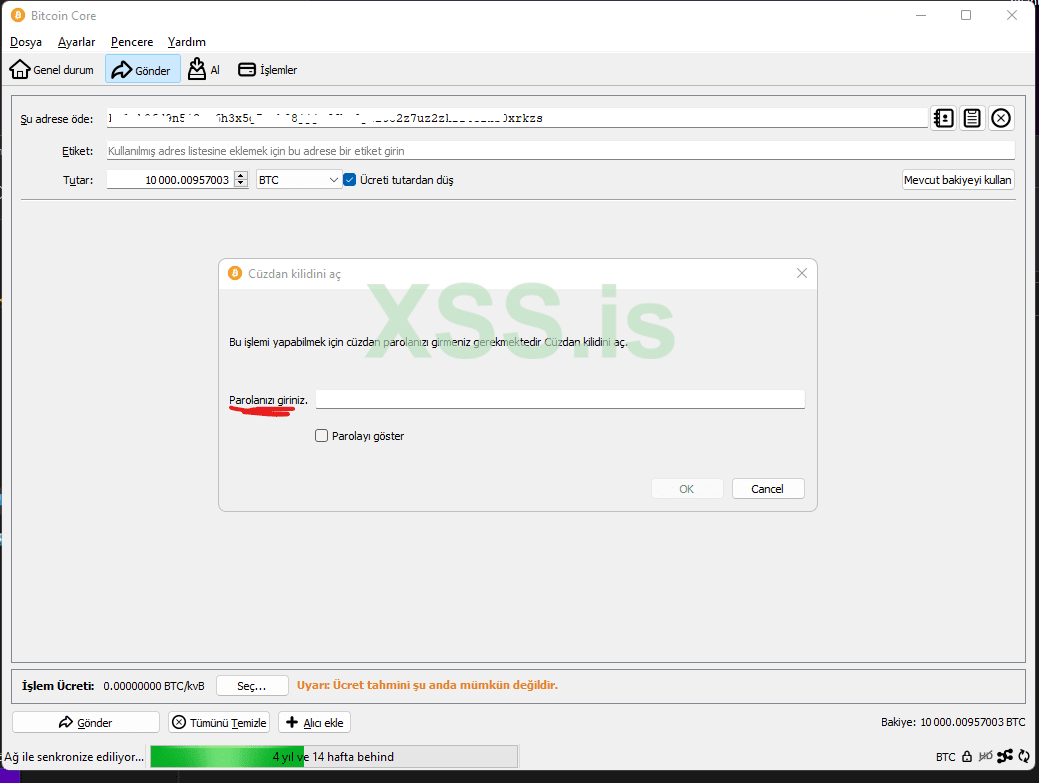
Wallet theft
Wallet Weak seed creation
Zero Balance Accounts
Failure to remove developer or test credentials or addresses from a SmartContract
XSS in wallets and smart contract interfaces via company names/et