Egregious community,
as title, I'm selling an "Automated RDP Exploiter". It exploit a "Private-Unknown-CVE".
It's fast, and efficient. Stable and fully working.
I found it as private leak, in a closed community, few years ago; that said, being not available publicly, I decided to sell it. (Please note): [If someone is able to find the latter in the Web; please make the link to it public by means of this thread. I will stop the sale instantly]. It is not, with absoluteness, my will to speculate in this sense.
[Features]:
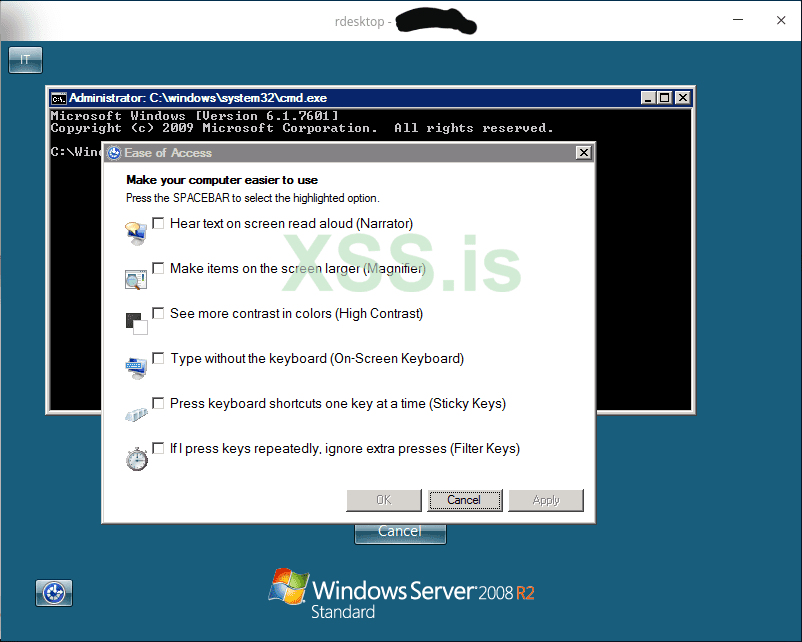
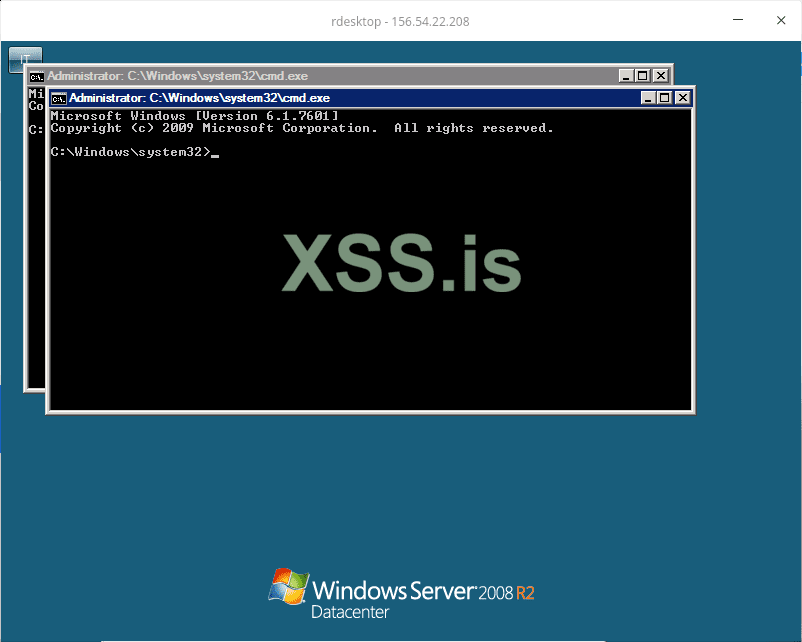
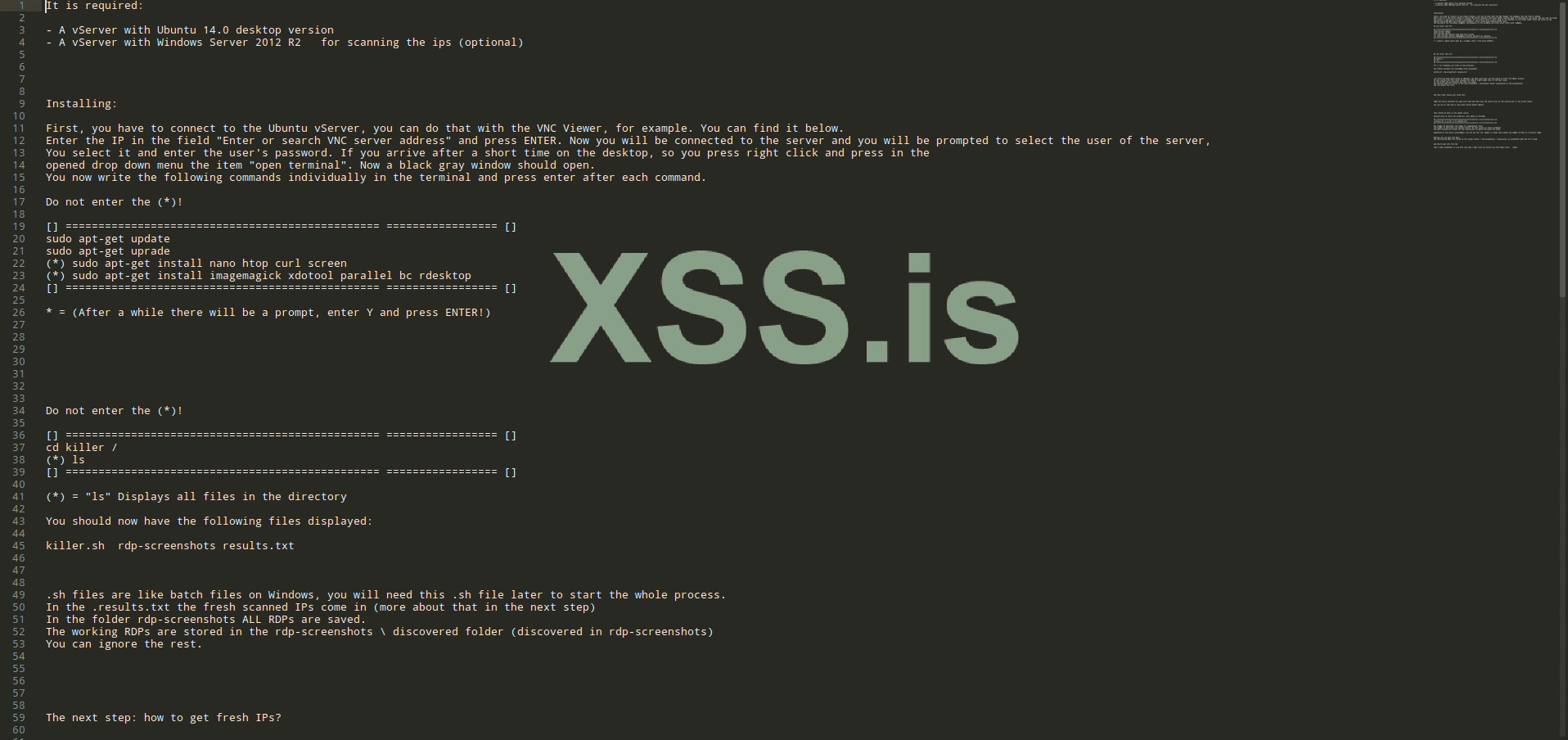
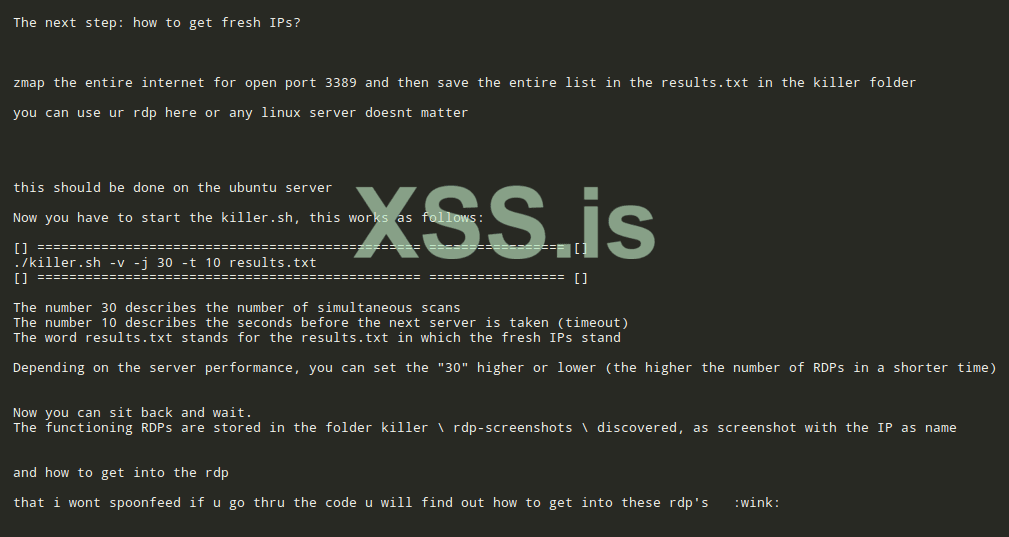
A simple bash script, that use the tool called "rdesktop", as connection method.
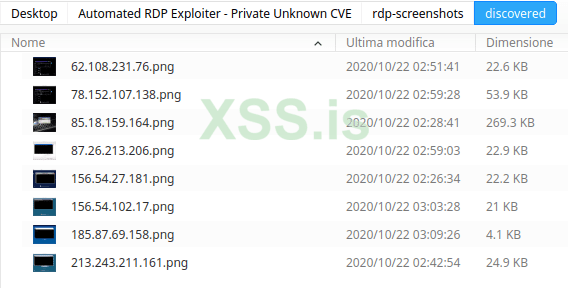
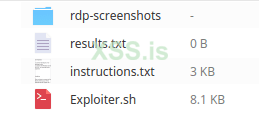
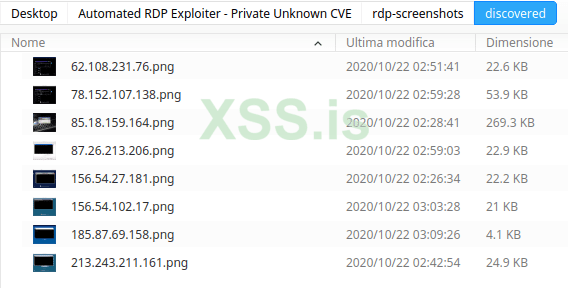
It just require a list of RDP's to test, and will be done everything automatically. The results will be written in a "Text-file", and in a related folder, saved the screenshots of each RDP tested.
I attach the instructions, to give you a better, proper, idea.


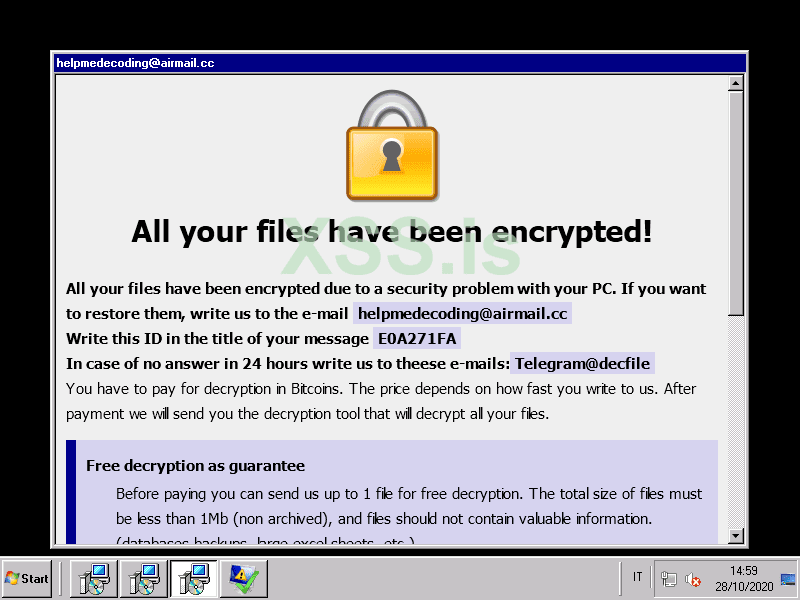
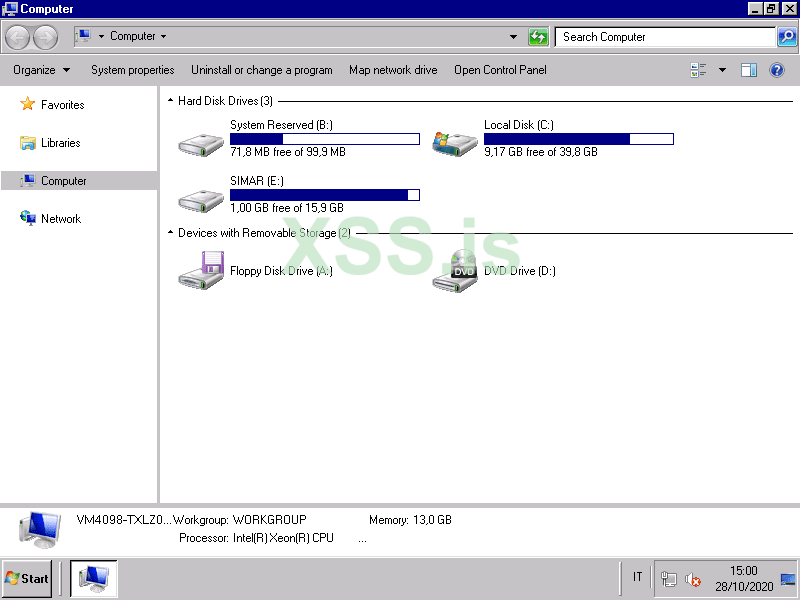
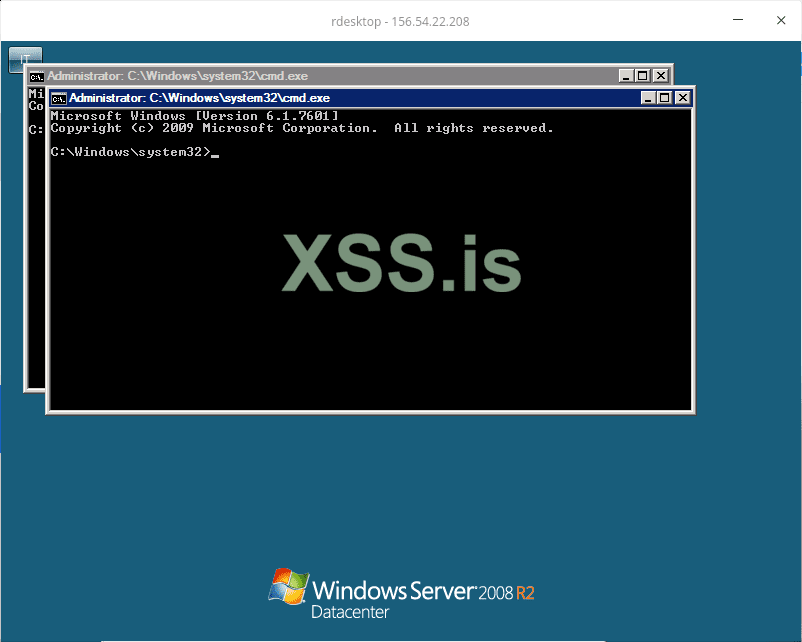
#Mass-Automated RDP Exploiter, in action:
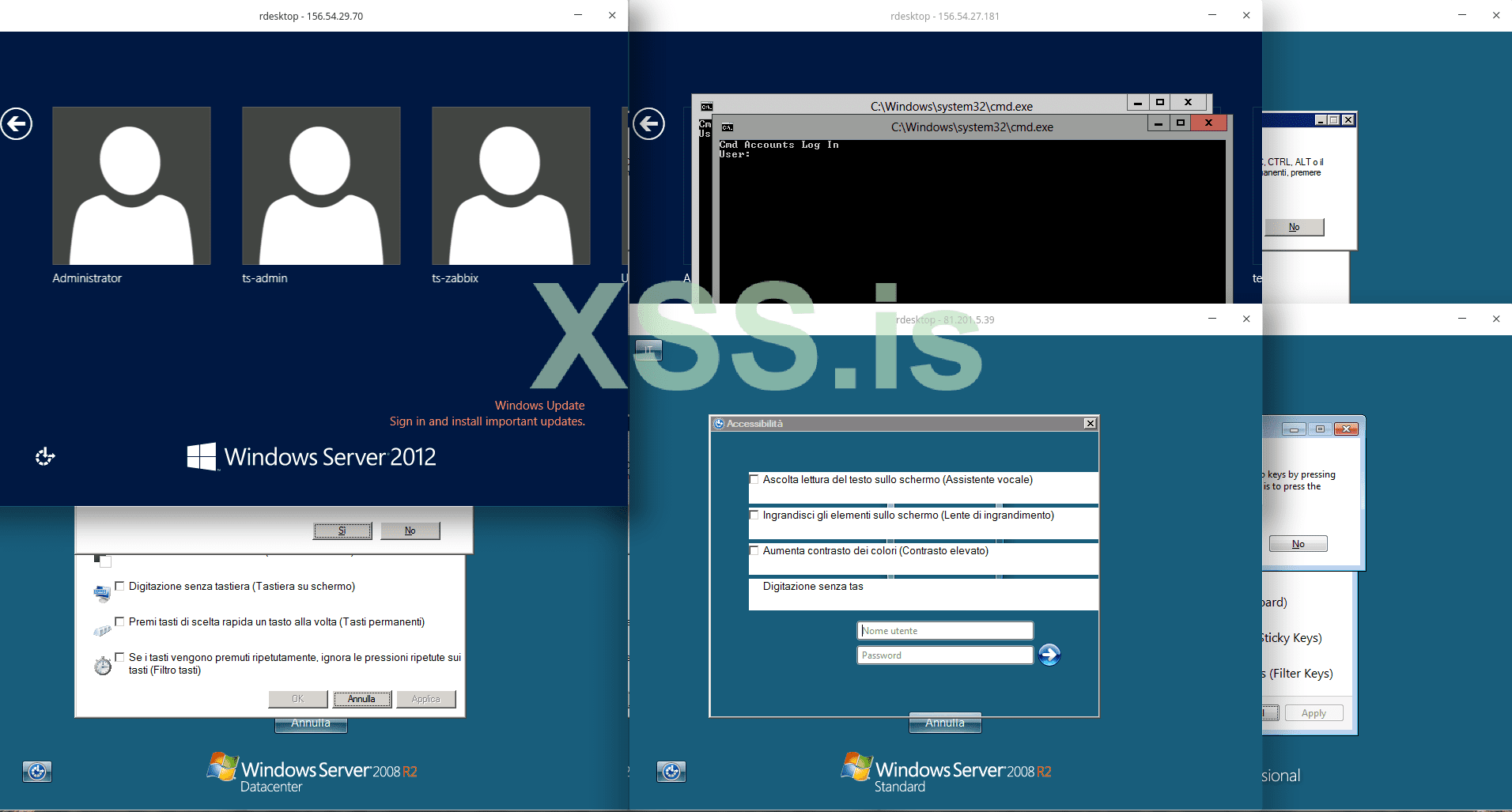
[GIF animated image, in action: "https://postimg.cc/d7czPD1G"].
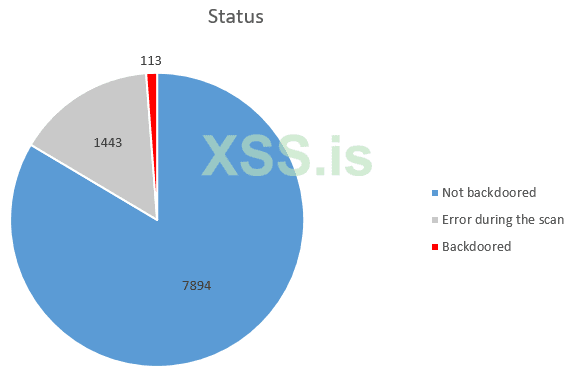
[Tested on few, random, Italian RDP's: RESULTS: -after around 45 minutes of automated elaboration: -> 8 RDP's successfully exploited!].
Price : "200 $" in Bitcoin .
(Included in the price: a wide/large RDP's list, related to several, highly developed/high GDP/rich countries. [Updated, approximately: to the end of May 2019]. The latter has been downloaded from "Shodan" Web service).
If you are interested to buy, or need more information / clear doubts, I'm fully available. [From: 10:00 AM to 11 PM - GMT: +03: 00. (Moscow-timezone)].
Contacts: using Private-Message function of the Forum, or external; 1) XMPP: "arsenic@thesecure.at". (OTR); 2) Telegram: "VoidZero_0".
Thanks in advance!
Best regards,
VoidZero.
as title, I'm selling an "Automated RDP Exploiter". It exploit a "Private-Unknown-CVE".
It's fast, and efficient. Stable and fully working.
I found it as private leak, in a closed community, few years ago; that said, being not available publicly, I decided to sell it. (Please note): [If someone is able to find the latter in the Web; please make the link to it public by means of this thread. I will stop the sale instantly]. It is not, with absoluteness, my will to speculate in this sense.
[Features]:
A simple bash script, that use the tool called "rdesktop", as connection method.
It just require a list of RDP's to test, and will be done everything automatically. The results will be written in a "Text-file", and in a related folder, saved the screenshots of each RDP tested.
I attach the instructions, to give you a better, proper, idea.
#Mass-Automated RDP Exploiter, in action:
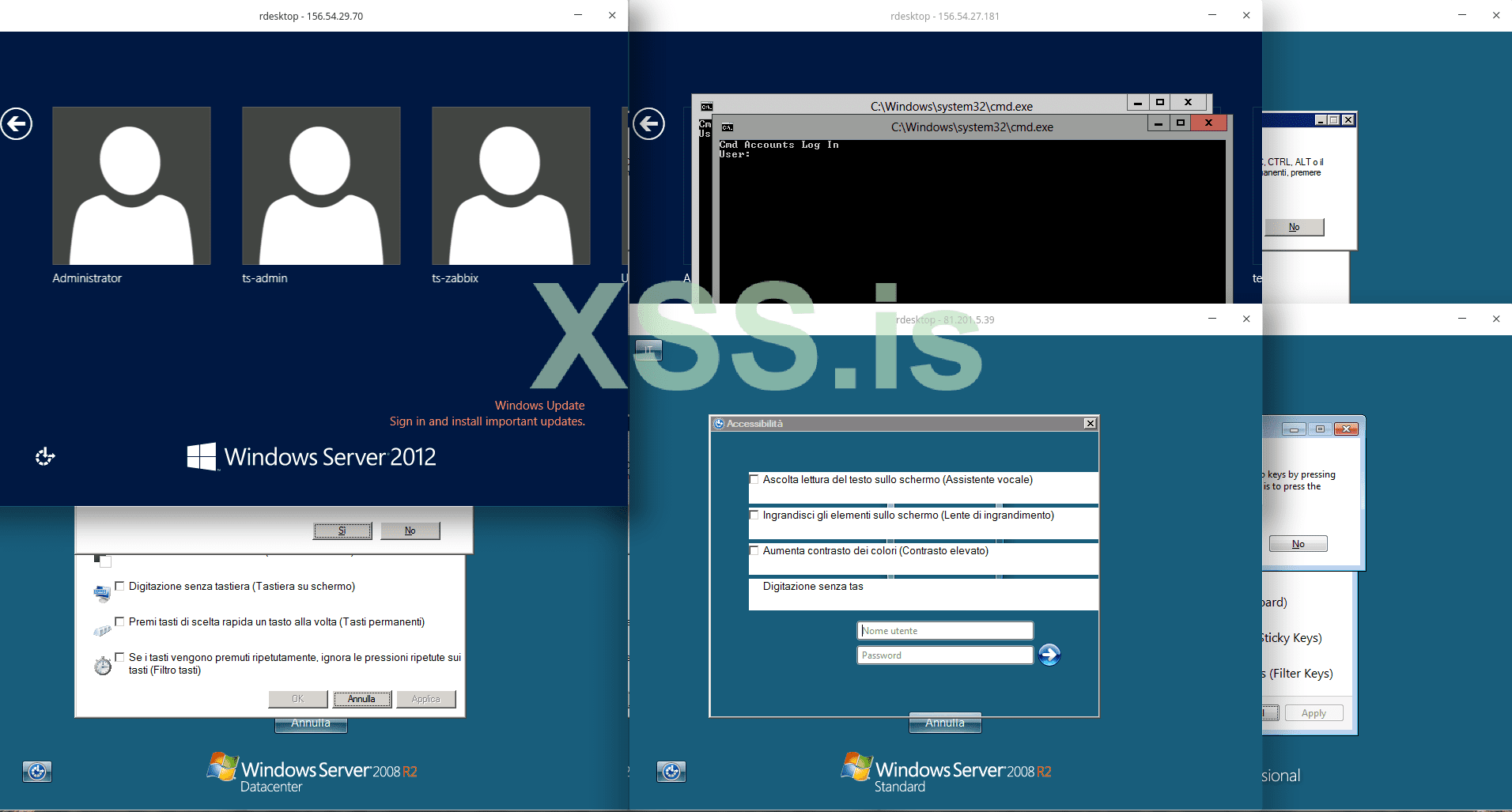
[GIF animated image, in action: "https://postimg.cc/d7czPD1G"].
[Tested on few, random, Italian RDP's: RESULTS: -after around 45 minutes of automated elaboration: -> 8 RDP's successfully exploited!].
Price : "200 $" in Bitcoin .
(Included in the price: a wide/large RDP's list, related to several, highly developed/high GDP/rich countries. [Updated, approximately: to the end of May 2019]. The latter has been downloaded from "Shodan" Web service).
If you are interested to buy, or need more information / clear doubts, I'm fully available. [From: 10:00 AM to 11 PM - GMT: +03: 00. (Moscow-timezone)].
Contacts: using Private-Message function of the Forum, or external; 1) XMPP: "arsenic@thesecure.at". (OTR); 2) Telegram: "VoidZero_0".
Thanks in advance!
Best regards,
VoidZero.
Последнее редактирование модератором: