Пожалуйста, обратите внимание, что пользователь заблокирован
Напоминание для тех кто делает переводы.
Заливайте картинки не посредственно на сам форум, не надо картинки по ссылке вставлять. Если линк мрет то и картинка мрет и не отображается больше на форуме. Поэтому лейте на форум. Если количество картинок больше, чем можно прикрепить. Отпишите тут. Увеличим.
Вот еще темы для переводов.

 sploitfun.wordpress.com
sploitfun.wordpress.com
level 1

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com
 sploitfun.wordpress.com
sploitfun.wordpress.com
level 2

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com
level3

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com

 sploitfun.wordpress.com
sploitfun.wordpress.com

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz

 rootkits.xyz
rootkits.xyz
p.s. переводы туториалов лучше постить в одну тему, т. е. не создавать кучу новых тем для отдельной статьи. Один туториал и в него все статьи из цикла в последующих сообщениях.
Заливайте картинки не посредственно на сам форум, не надо картинки по ссылке вставлять. Если линк мрет то и картинка мрет и не отображается больше на форуме. Поэтому лейте на форум. Если количество картинок больше, чем можно прикрепить. Отпишите тут. Увеличим.
Вот еще темы для переводов.

Linux (x86) Exploit Development Series
First of all I would like to thank phrack articles, its author and other security researchers for teaching me about different exploit techniques, without whom none of the posts would have been poss…
level 1

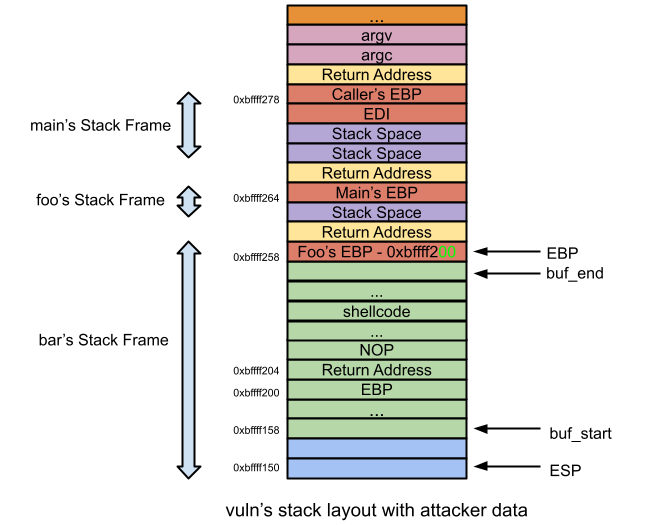
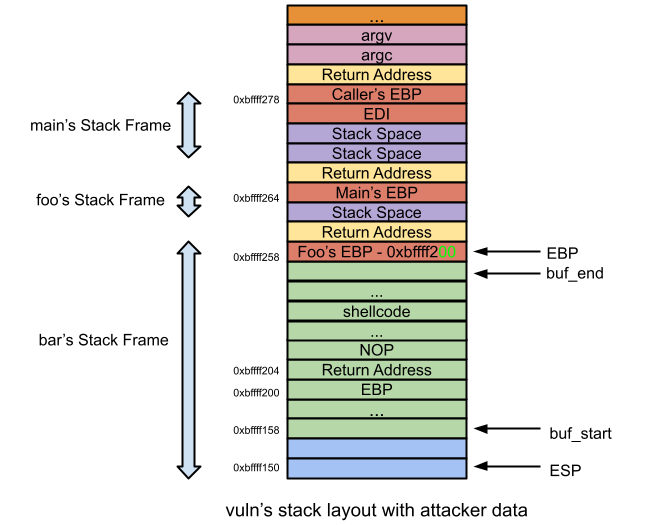
Classic Stack Based Buffer Overflow
VM Setup: Ubuntu 12.04 (x86) This post is the most simplest of the exploit development tutorial series and in the internet you can already find many articles about it. Despite its abundance and fam…

Integer Overflow
VM Setup: Ubuntu 12.04 (x86) What is Integer Overflow? Storing a value greater than maximum supported value is called integer overflow. Integer overflow on its own doesnt lead to arbitrary code exe…
Off-By-One Vulnerability (Stack Based)
Prerequisite: Classic Stack Based Buffer Overflow VM Setup: Ubuntu 12.04 (x86) What is off-by-one bug? Copying source string into destination buffer could result in off-by-one when Source string l…
level 2

Bypassing NX bit using return-to-libc
Prerequisite: Classic Stack Based Buffer Overflow VM Setup: Ubuntu 12.04 (x86) In previous posts, we saw that attacker copies shellcode to stack and jumps to it!! in order to successfully exploit v…

Bypassing NX bit using chained return-to-libc
Prerequisite: Classic Stack Based Buffer Overflow Bypassing NX bit using return-to-libc VM Setup: Ubuntu 12.04 (x86) Chained returned-to-libc? As seen in previous post, need arises for an attacker …

Bypassing ASLR – Part I
Prerequisite: Classic Stack Based Buffer Overflow VM Setup: Ubuntu 12.04 (x86) In previous posts, we saw that attacker needs to know stack address (to jump to shellcode) libc base address (to succe…

Bypassing ASLR – Part II
Prerequisite: Classic Stack Based Buffer Overflow VM Setup: Ubuntu 12.04 (x86) In this post lets see how to bypass shared library address randomization using brute force technique. What is brute-fo…

Bypassing ASLR – Part III
Prerequisite: Classic Stack Based Buffer Overflow Bypassing ASLR – Part I VM Setup: Ubuntu 12.04 (x86) In this post lets see how to bypass shared library address randomization using GOT overw…
level3

Heap overflow using unlink
Prerequisite: Understanding glibc malloc In this post lets learn how heap overflow can be successfully exploited using unlink technique. But before looking into unlink, first lets look into a vulne…

Heap overflow using Malloc Maleficarum
Prerequisite: Understanding glibc malloc During late 2004, ‘glibc malloc’ got hardened. After which techniques such as unlink got obsolete, leaving the attackers clueless. But only for …

Off-By-One Vulnerability (Heap Based)
Prerequisite: Off-By-One Vulnerability (Stack Based) Understanding glibc malloc VM Setup: Fedora 20 (x86) What is off-by-one bug? As said in this post, copying source string into destination buffe…

Use-After-Free
Prerequisite: Off-By-One Vulnerability (Heap Based) Understanding glibc malloc VM Setup: Fedora 20 (x86) What is use-after-free (UaF)? Continuing to use a heap memory pointer which is already been…

Windows Kernel Exploitation Tutorial Part 1: Setting up the Environment - rootkit
Intro Recently, I had the pleasure to attend the training on Windows Kernel Exploitation at nullcon by the HackSysTeam. The training was well executed, and I got the intro into the world of kernel. But, as you know, nobody could teach you internals about Kernel Exploitation in a couple of days...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 2: Stack Overflow - rootkit
Overview In the part 1, we looked into how to manually setup the environment for Kernel Debugging. If something straightforward is what you want, you can look into this great writeup by hexblog about setting up the VirtualKd for much faster debugging. In this post, we’d dive deep into the kernel...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 3: Arbitrary Memory Overwrite (Write-What-Where) - rootkit
Overview In the previous part, we looked into exploiting a basic kernel stack overflow vulnerability. This part will focus on another vulnerability, Arbitrary Memory Overwrite, also known as Write-What-Where vulnerability. Basic exploitation concept for this would be to overwrite a pointer in a...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 4: Pool Feng-Shui -> Pool Overflow - rootkit
Overview We discussed about Write-What-Where vulnerability in the previous part. This part will deal with another vulnerability, Pool Overflow, which in simpler terms, is just an Out-of-Bounds write on the pool buffer. This part could be intimidating and goes really in-depth on how to groom the...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 5: NULL Pointer Dereference - rootkit
Overview First of all, a happy new year. 🙂 After the exhaustive last part in this series, to start off this new year, this post will be about a lighter, more easy to understand vulnerability. A null pointer dereference vulnerability exists when the value of the pointer is NULL, and is used by...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 6: Uninitialized Stack Variable - rootkit
Overview In the previous part, we looked into a simple NULL Pointer Dereference vulnerability. In this part, we’ll discuss about another vulnerability, Uninitialized Stack Variable. This vulnerability arises when the developer defines a variable in the code, but doesn’t initialize it. So, during...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 7: Uninitialized Heap Variable - rootkit
Overview In the previous part, we looked into an Uninitialized Stack Variable vulnerability. In this part, we’ll discuss about another vulnerability on similar lines, Uninitialized Heap Variable. We’d be grooming Paged Pool in this one, so as to direct our execution flow to the shellcode. Again...
 rootkits.xyz
rootkits.xyz

Windows Kernel Exploitation Tutorial Part 8: Use After Free - rootkit
Overview In our previous post, we discussed about Uninitialized Heap Variable. This post will focus on another vulnerability, Use After Free. As the name might suggest, we’d be exploiting a stale pointer, that should’ve been freed, but due to a flaw, the pointer is called through a Callback...
 rootkits.xyz
rootkits.xyz
p.s. переводы туториалов лучше постить в одну тему, т. е. не создавать кучу новых тем для отдельной статьи. Один туториал и в него все статьи из цикла в последующих сообщениях.
Последнее редактирование:









