Windows SandboxEscape POC exploit
Windows Zero-Day Bug Allows Overwriting Files with Arbitrary Data
A security researcher has disclosed exploit code for a fourth zero-day vulnerability in Windows operating system in just as many months. The bug enables overwriting a target file with arbitrary data.
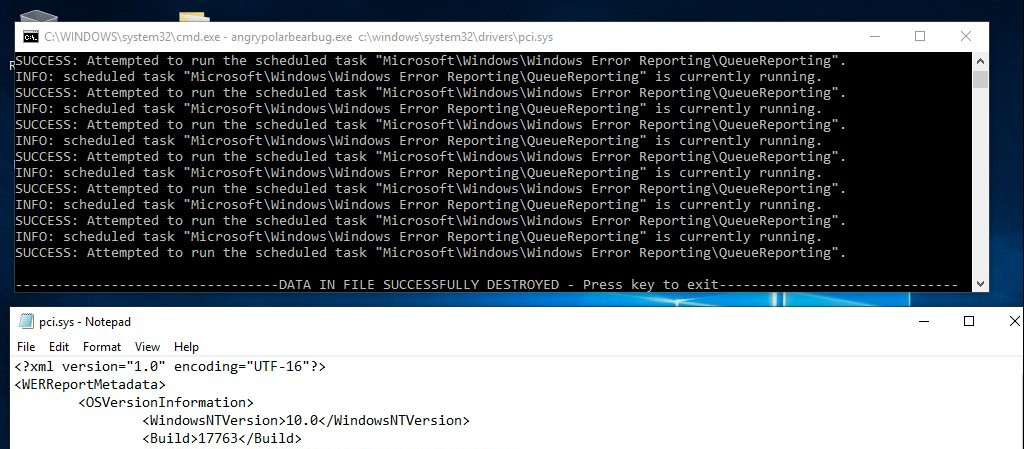
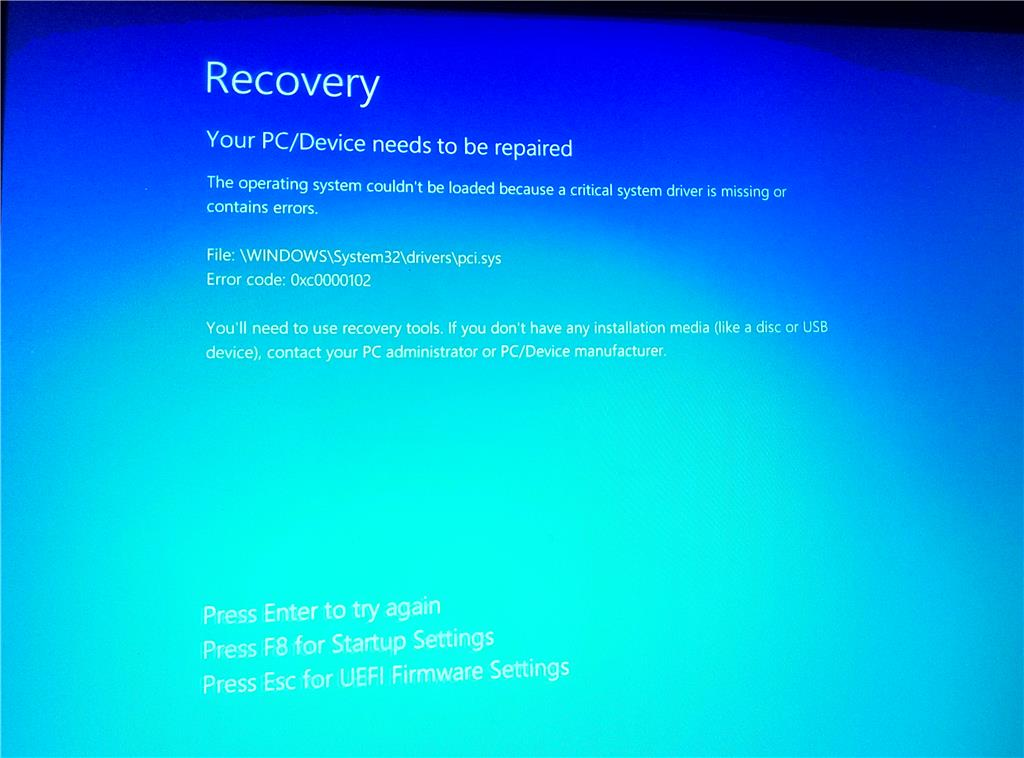
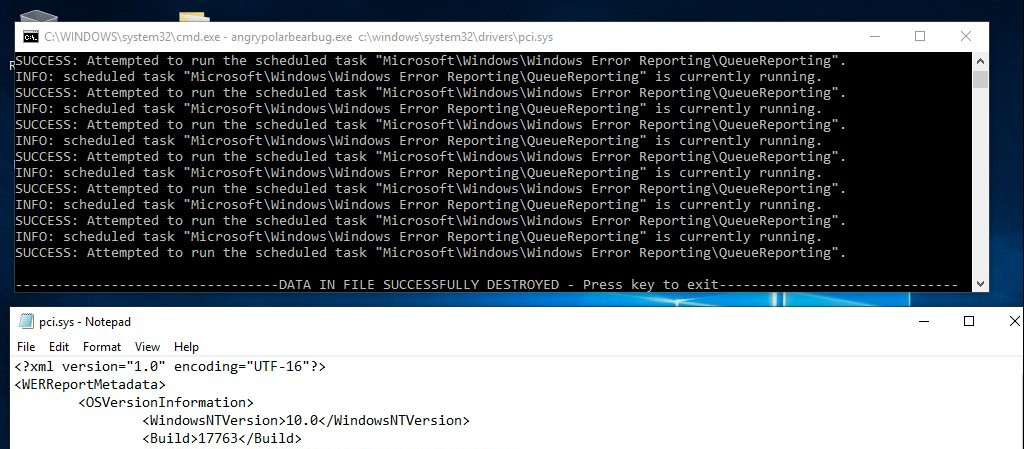
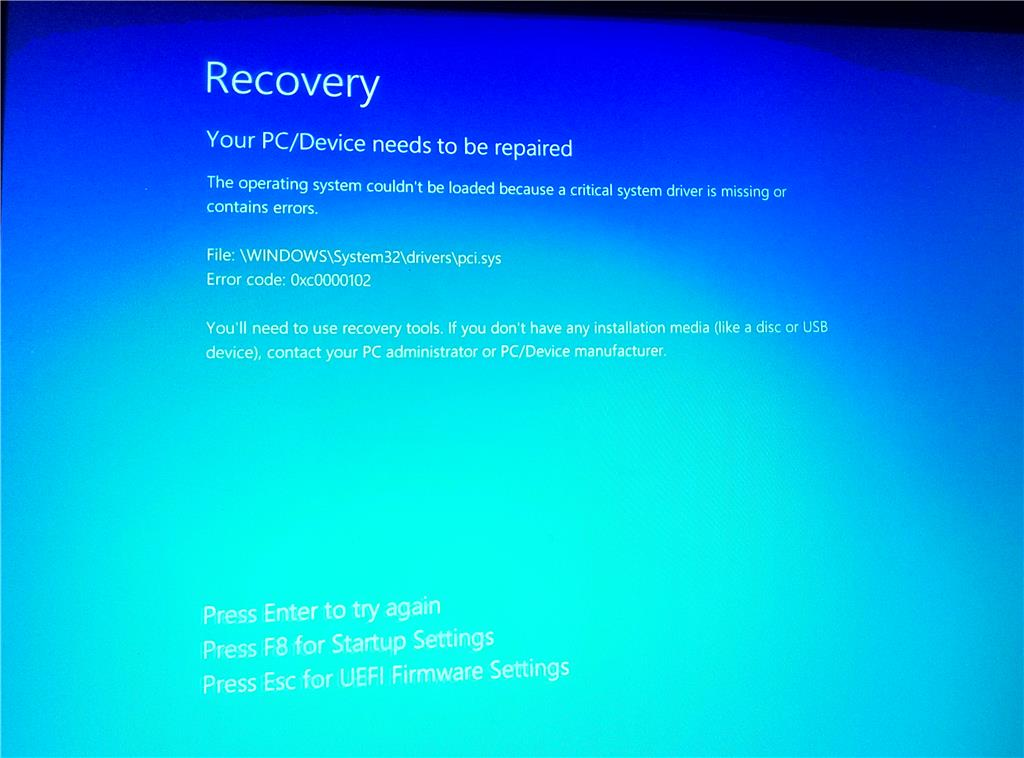
Running the proof-of-concept (PoC) code provided by the researcher that uses the online alias SandboxEscaper results in overwriting 'pci.sys' with information about software and hardware problems, collected through the Windows Error Reporting (WER) event-based feedback infrastructure.
The bug could also take a while to produce an effect, says SandboxEscaper, on account that it relies on a race condition and other operations may break the outcome.
A vulnerability analyst at CERT/CC, who was able to reproduce the bug Windows 10 Home, build 17134.
POC exploit
https://github.com/SandboxEscaper/randomrepo
https://github.com/SandboxEscaper/randomrepo/blob/master/angrypolarbearbug.rar
Windows Zero-Day Bug Allows Overwriting Files with Arbitrary Data
A security researcher has disclosed exploit code for a fourth zero-day vulnerability in Windows operating system in just as many months. The bug enables overwriting a target file with arbitrary data.
Running the proof-of-concept (PoC) code provided by the researcher that uses the online alias SandboxEscaper results in overwriting 'pci.sys' with information about software and hardware problems, collected through the Windows Error Reporting (WER) event-based feedback infrastructure.
The bug could also take a while to produce an effect, says SandboxEscaper, on account that it relies on a race condition and other operations may break the outcome.
A vulnerability analyst at CERT/CC, who was able to reproduce the bug Windows 10 Home, build 17134.
POC exploit
https://github.com/SandboxEscaper/randomrepo
https://github.com/SandboxEscaper/randomrepo/blob/master/angrypolarbearbug.rar