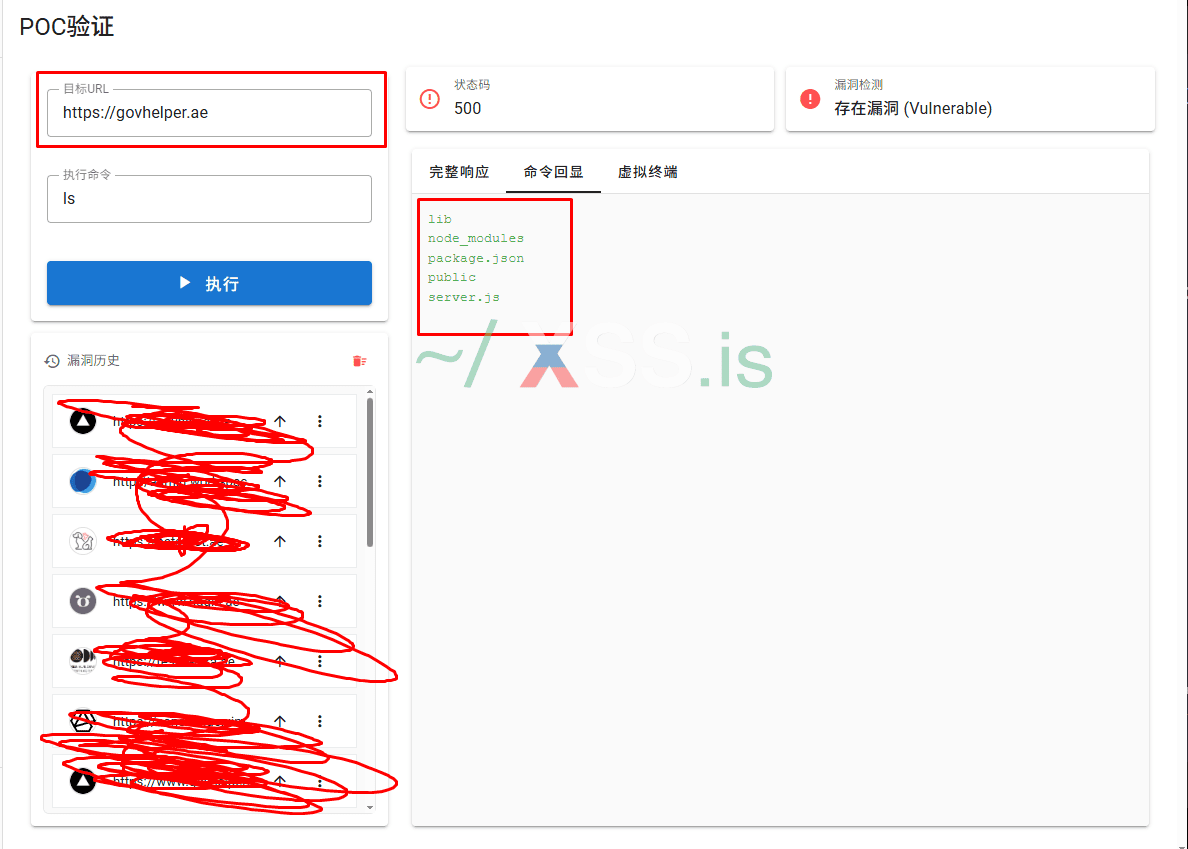
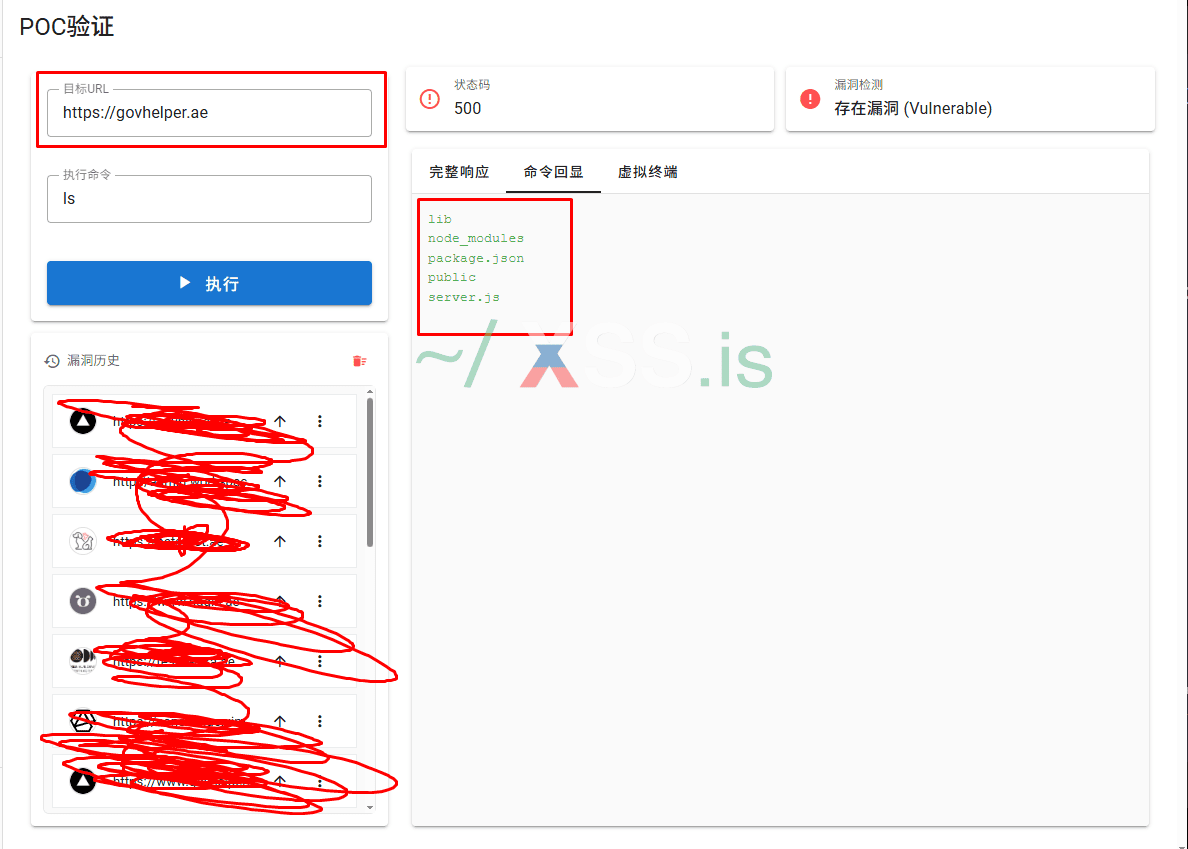
I used a graphical batch vulnerability scanner and found many websites with this vulnerability (CVE-2025-55182), but they all seem to be static websites or containerized websites (Docker, Kubernetes). What should I do next? Or how can I escape the container and gain root privileges? Would that be too complicated?