Всем привет интересная штука появилась.
Ищу кого то кто хочет помочь написать чекер
оплата за скорость будит приемлемая, договоримся)
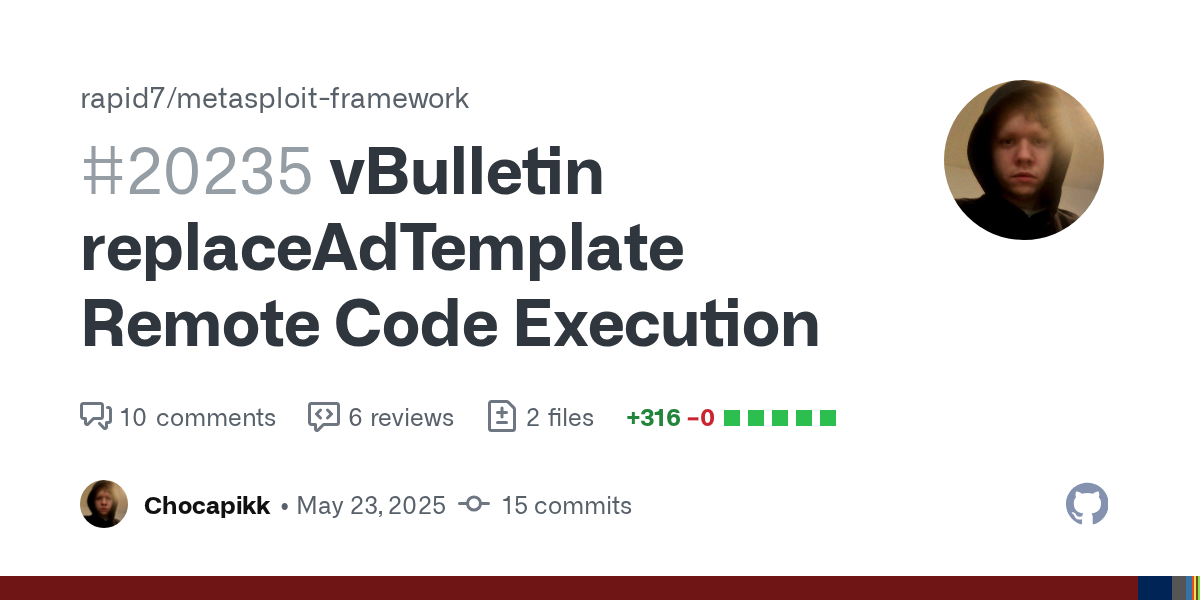
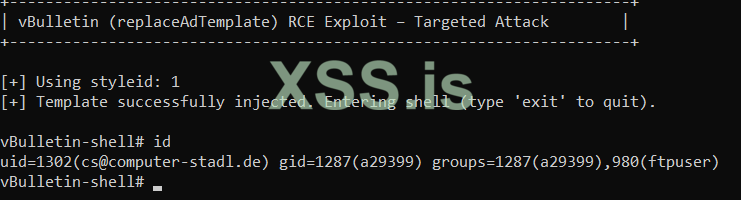
CVE-2025-48828
CVE-2025-48828
WriteUp
Ищу кого то кто хочет помочь написать чекер
оплата за скорость будит приемлемая, договоримся)
CVE-2025-48828
CVE-2025-48828
WriteUp