- Цена
- 500
- Контакты
- DM first
Hi,
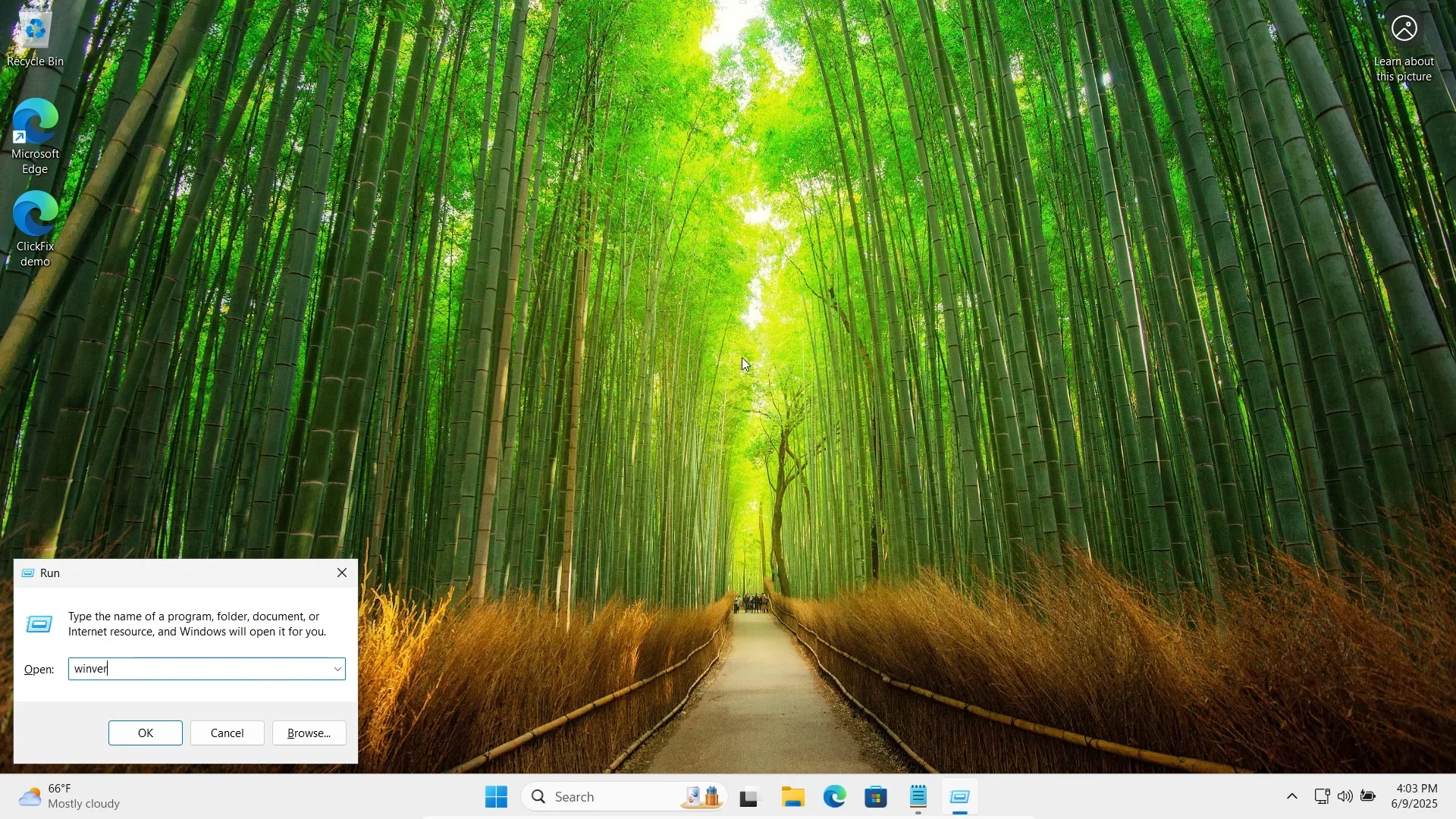
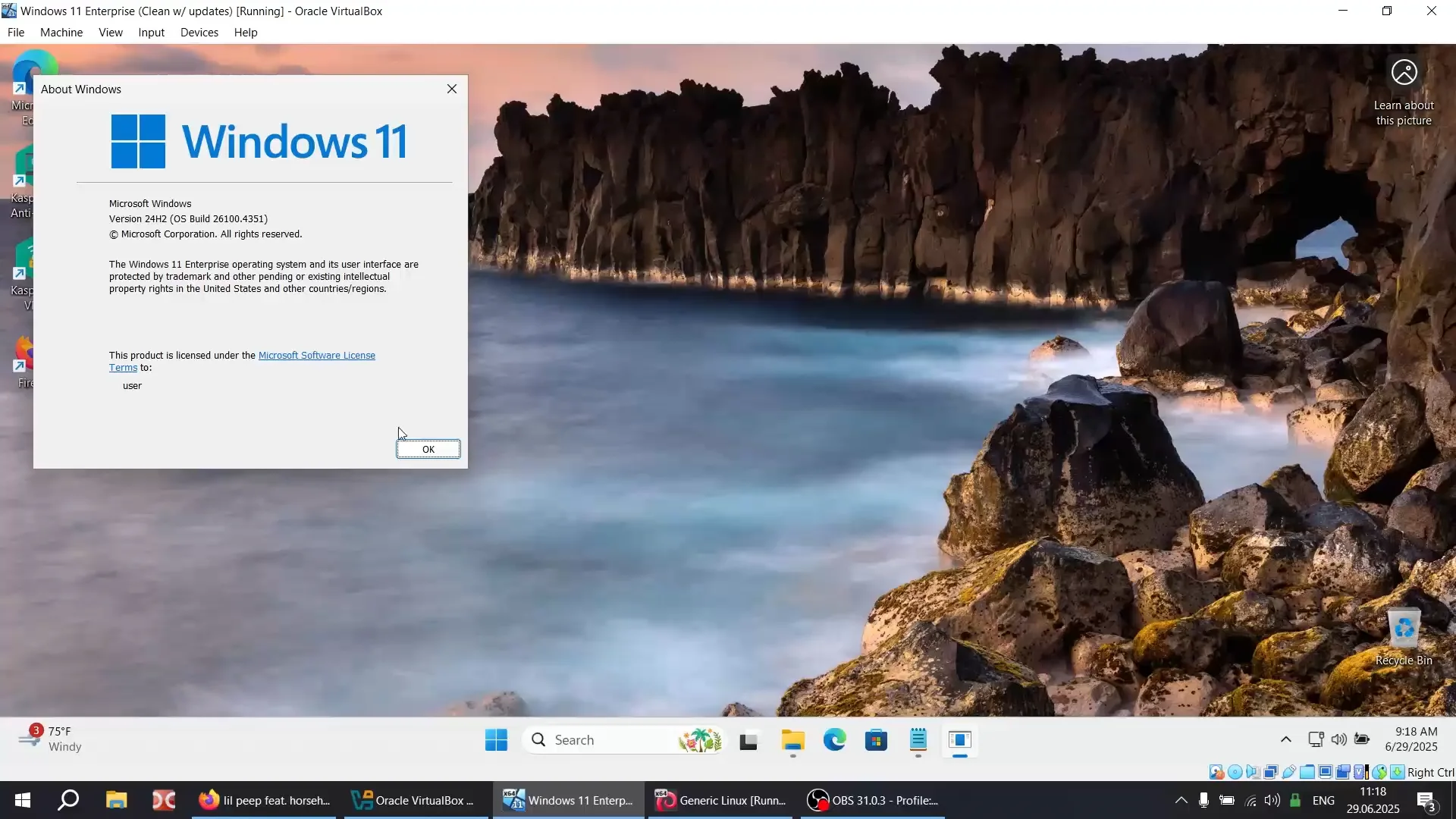
By now you're all probably familiar with ClickFix (Win+R) payload delivery method.
You also might have noticed that all regular delivery commands (powershell, cmd curl, mshta, etc..) are now immediately detected by Windows Defender & co.
I am selling a new method I found for delivery, using a command that is fully undetected.
What you will get:
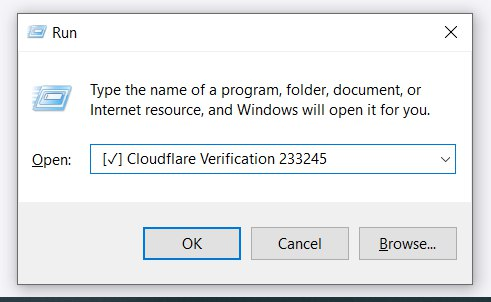
1. new command (Windows native) + correct usage format <== this is the part which victims will use Ctrl + V in "Run" dialog
2. the method, source and tools to create the container archive <== this is downloaded and unpacked by the command
This method allows you to pack either direct .exe payload, or signed .exe with DLL (for DLL Sideload, which is what I personally use and recommend you do too).
Output is 1 file, ready to be hosted on your server and awaiting deployment.
Benefits:
What this is NOT:
- this does not encrypt your payload. Crypting is on your side. This only ensures delivery and execution in 1 command.
Base price (no modifications): $500
If you want mods: let's discuss.
If interested, please DM me first. I will share Tox only through DM (I do not have Telegram).
Will only sell to 2 buyers. Guarantee welcome.
By now you're all probably familiar with ClickFix (Win+R) payload delivery method.
You also might have noticed that all regular delivery commands (powershell, cmd curl, mshta, etc..) are now immediately detected by Windows Defender & co.
I am selling a new method I found for delivery, using a command that is fully undetected.
What you will get:
1. new command (Windows native) + correct usage format <== this is the part which victims will use Ctrl + V in "Run" dialog
2. the method, source and tools to create the container archive <== this is downloaded and unpacked by the command
This method allows you to pack either direct .exe payload, or signed .exe with DLL (for DLL Sideload, which is what I personally use and recommend you do too).
Output is 1 file, ready to be hosted on your server and awaiting deployment.
Benefits:
- full stealth, no suspicious processes invoked, no UAC, etc
- no MotW
- on delivery, payload is executed automatically
- on delivery, command is automatically deleted from user "Run" history
- (optional) this method allows to achieve start-up persistence independently (evade behavioral analysis)
- (optional) custom decoy steps can be added (auto-open URL or PDF file for user on payload execution, etc)
What this is NOT:
- this does not encrypt your payload. Crypting is on your side. This only ensures delivery and execution in 1 command.
Base price (no modifications): $500
If you want mods: let's discuss.
If interested, please DM me first. I will share Tox only through DM (I do not have Telegram).
Will only sell to 2 buyers. Guarantee welcome.
Последнее редактирование: