Пожалуйста, обратите внимание, что пользователь заблокирован
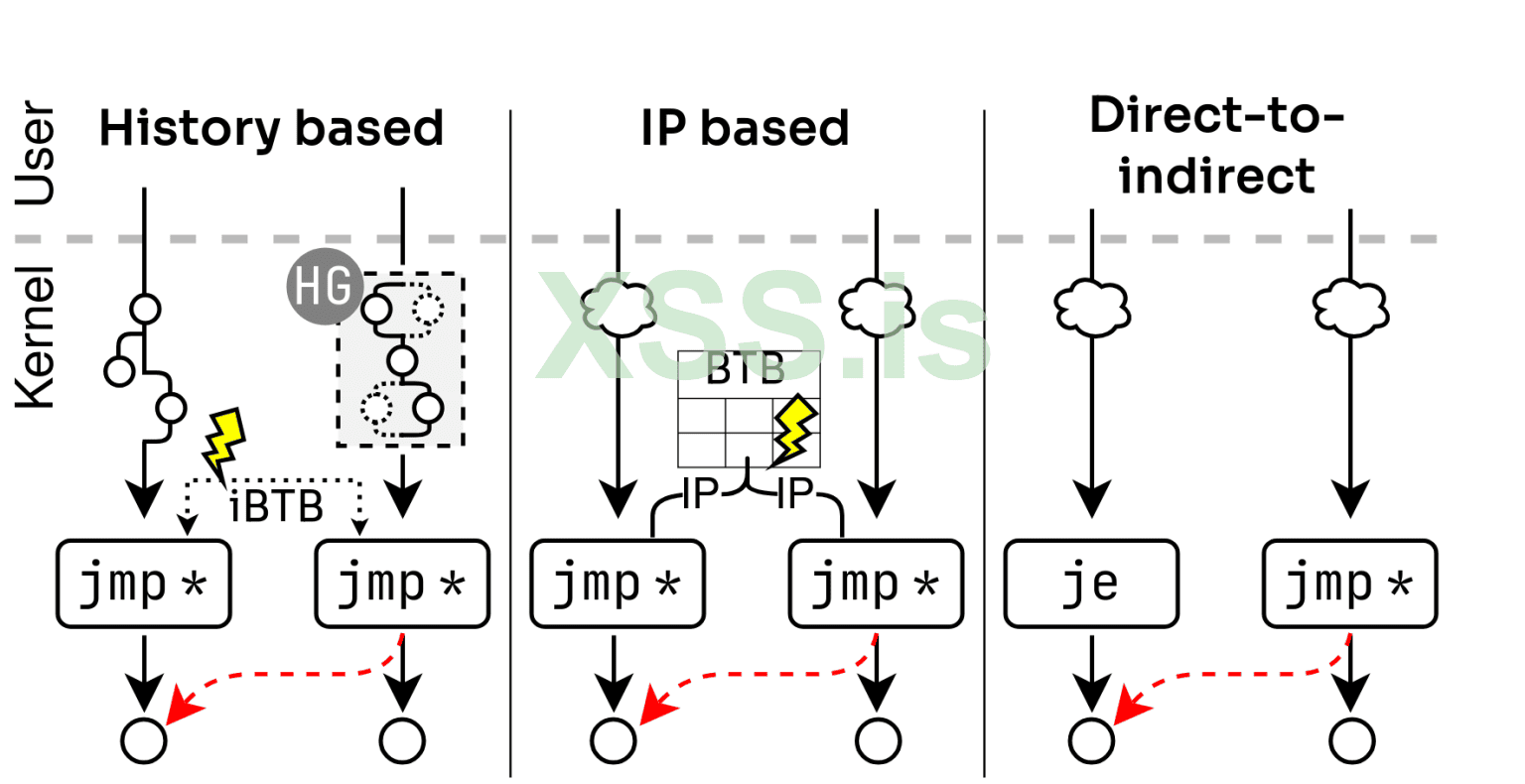
Three self-training attack classes
History-based attacks: Bypass domain isolation by crafting in-kernel branch histories using history-crafting gadgets. We show how attackers can train the kernel via SECCOMP (cBPF, enabled by default for all users, unlike eBPF) to redirect the speculation of an indirect branch to a so-called ‘disclosure gadget’ and leak memory. We created an end-to-end exploit leaking arbitrary memory with 1.7KB/s, tested on Tiger Lake and (Intel’s latest generation) Lion Cove CPUs.
IP-based attacks: Exploit predictable IP collisions in the branch predictor when history-based prediction is disabled. We show how attackers can force the predictor to fallback to a prediction solely based on the branch address (rather than branch history). As a consequence, two indirect branches can train each other if their address aliases (collide) in the BTB. By means of gadget analysis, we provide evidence that such attacks can be feasible in a large-scale attack scenario.
Direct-to-indirect attacks: We discovered that on certain CPUs, direct branches can train indirect branch prediction. This behavior is caused by two hardware issues: Indirect Target Selection (ITS) (CVE-2024-28956) and a hardware issue on Lion Cove (CVE-2025-24495.). For ITS, this drastically increases the self-training attack surface. We demonstrate an end-to-end exploit leaking arbitrary kernel memory at 17 KB/sec.
Подробности тут https://www.vusec.net/projects/training-solo/
Документ https://download.vusec.net/papers/trainingsolo_sp25.pdf
PoCs https://github.com/vusec/training-solo