- Цена
- 20000
- Контакты
- Pm Me
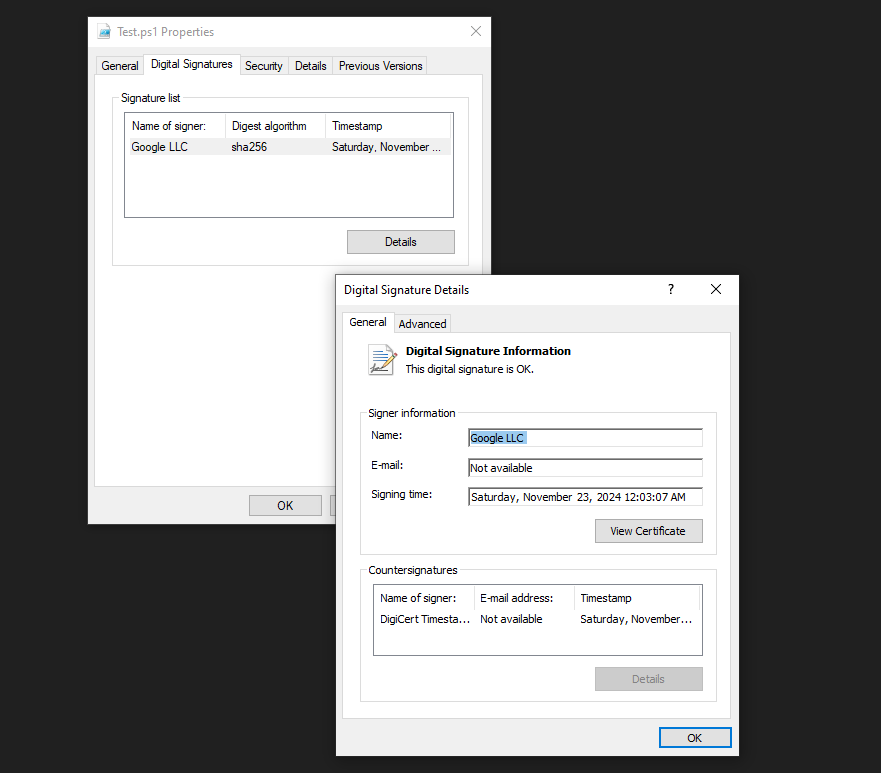
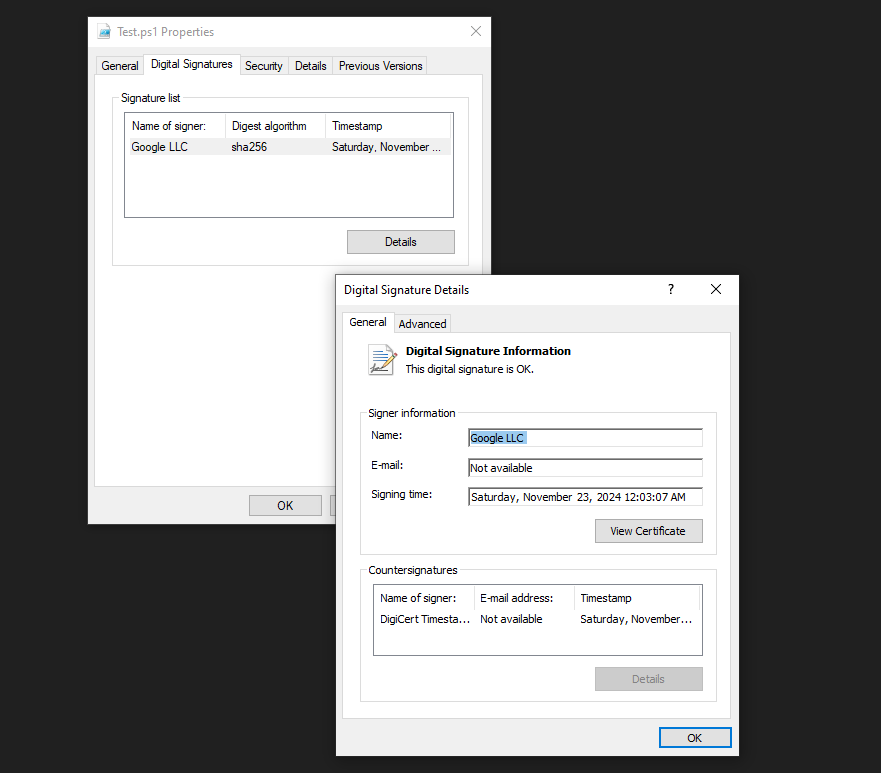
Okay, so I’ve been quietly working on something I think has some serious potential, and I wanted to get some outside perspectives. It’s a PowerShell script that leverages a relatively recent Windows feature – the Exclusion Signed functionality – in a way that’s… well, let’s just say it allows for a degree of process monitoring and potentially even limited manipulation that’s not immediately obvious.
This exploit leverages a signed PowerShell script that is excluded from Windows Defender scans. By tweaking this script, we can execute malicious payloads without triggering any alarms. The beauty of this method lies in its simplicity and effectiveness.
While this exploit is powerful.
Bypasses Security Measures: Because the script is signed and excluded, it slips past most security software.
Easy to Implement: No complex coding required. Just a bit of scripting knowledge will do.
Versatile: You can use this method to deploy various types of malware.
Bypassing Basic Antivirus: Many AVs rely on process name and signature recognition. If the process is excluded, it can slip through.
Technical Details (Brief): It’s written in PowerShell 7. It utilizes the ExclusionSigned API. It’s reasonably well-documented internally, but I’d provide more detailed documentation to a buyer. It’s designed to be relatively easy to deploy – just a few lines of PowerShell to add the process to the exclusion list.
Note: This message is intended only for individuals with a relevant use case.
If this does not apply to you, please do not Flood. Thank you for your understanding.
[/ISPOILER]
This exploit leverages a signed PowerShell script that is excluded from Windows Defender scans. By tweaking this script, we can execute malicious payloads without triggering any alarms. The beauty of this method lies in its simplicity and effectiveness.
While this exploit is powerful.
Bypasses Security Measures: Because the script is signed and excluded, it slips past most security software.
Easy to Implement: No complex coding required. Just a bit of scripting knowledge will do.
Versatile: You can use this method to deploy various types of malware.
Bypassing Basic Antivirus: Many AVs rely on process name and signature recognition. If the process is excluded, it can slip through.
Technical Details (Brief): It’s written in PowerShell 7. It utilizes the ExclusionSigned API. It’s reasonably well-documented internally, but I’d provide more detailed documentation to a buyer. It’s designed to be relatively easy to deploy – just a few lines of PowerShell to add the process to the exclusion list.
Note: This message is intended only for individuals with a relevant use case.
If this does not apply to you, please do not Flood. Thank you for your understanding.
[/ISPOILER]
Последнее редактирование модератором: