Overview of a Relatively New C2
1. Introduction
BruteRatelC4 (BRC4) is a relatively new command-and-control toolkit for red teams that has quickly gained a reputation for stealth.1. Introduction
BruteRatel allows operators to compromise target systems and remotely execute payloads – but it was built from the ground up to be hard for defenders for to detect, in fact, its author (an ex-Mandiant/CrowdStrike red teamer) reverse-engineered top endpoint Detection and Response (EDR) products to tailor Brute Ratel's evasion techniques.
Despite its recent emergence, Initial release in late 2020, BruteRatelC4 offers all the core capabilities one expects from a post-exploitation framework. Operators deploy lightweight agents called “Badgers” (analogous to Cobalt Strike’s beacons) on target machines, What sets BRC4 is how it enables these operations to stay under the radar This article explores how to use BruteRatelC4 in real-world offensive workflows.
2. Operational Workflow with Badgers
In a BruteRatel engagement, the operator typically begins by setting up a C2 team server (the Brute Ratel “Commander” console) (Simple example is:
Код:
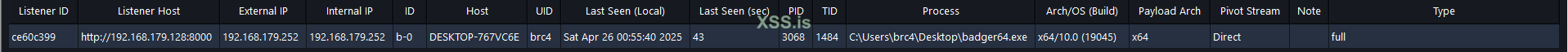
sudo ./brute-ratel-linx64 -ratel -a knight -p test -h 192.168.179.128:5050 -sc cert.pem -sk key.pem -fand configuring one or more listener profiles. picture below shows an overview of a listener configuration for HTTP
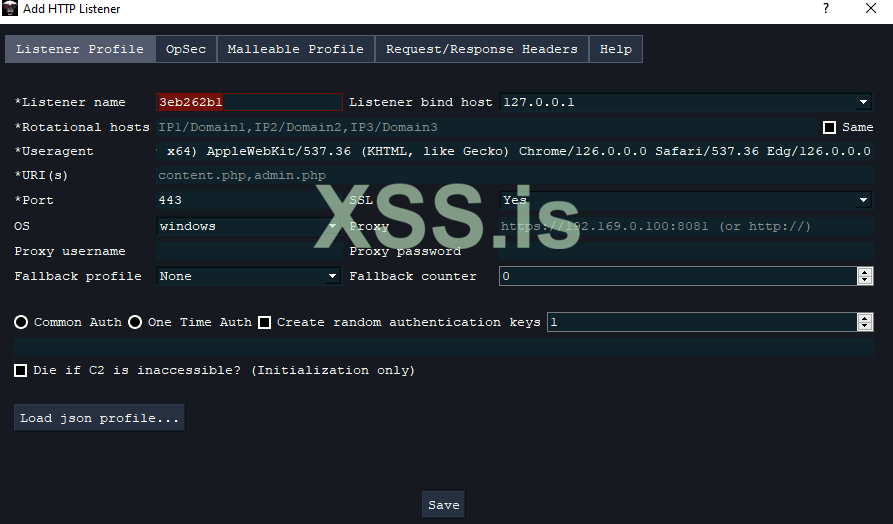
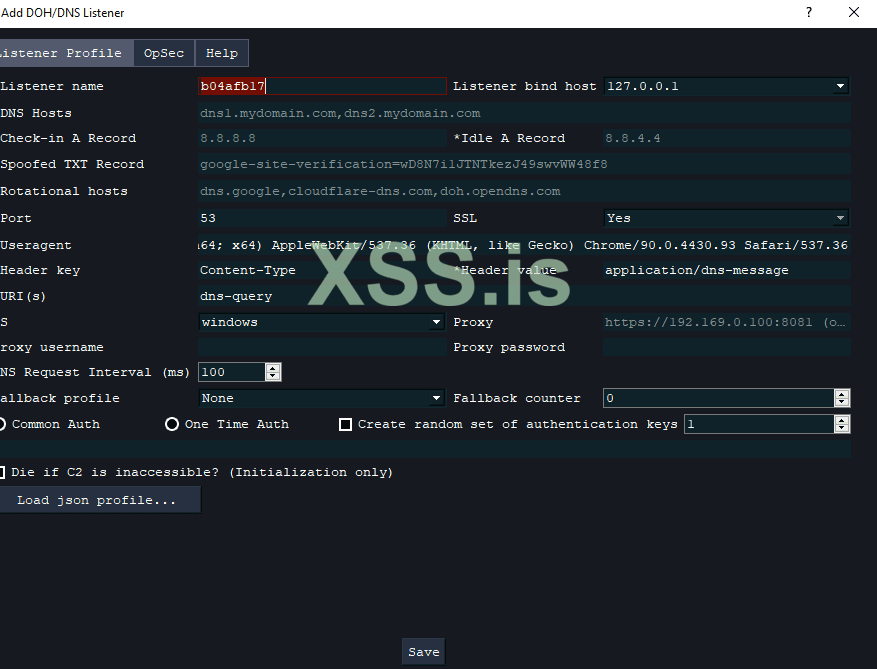
These profiles define how Badger implants will communicate will be communicated simply over HTTP(S), but BRC4 supports also DNS-based channels and more, picture below show DoH configuration
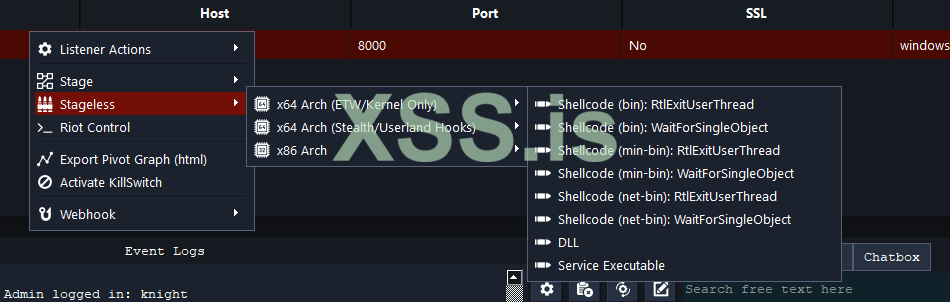
The operator then generates a Badger payload suited to the scenario, there are few payloads, Will be listed below:
- x64 ETW Kernel Only (Shellcode, Service, DLL)
- x64 Stealth/Userland Hooks (Service Executable, Variety of Shellcodes)
- x86 (Service Executable, DLL, Shellcode)
This is how it shows in the commander software:
The Badger payload comes packaged with an embedded configuration that includes the C2 server address, a communication URI and user-agent string, as well as an authentication password and encryption key for the C2 channel, This means each Badger is pre-configured to talk to your server in a particular, covert way – for example, imitating a common web browser or update client in its network traffic. This is called Malleable profile.
2.1 Initial Access With BRC4
How you deliver and launch the Badger is up to you, but BruteRatel is designed to facilitate stealthy deployment.
Story: one real-world attack by APT29
It was documented using a DLL search-order hijacking trick: the attackers distributed an ISO file containing a legitimate OneDriveUpdater.exe along with a malicious version.dll in the same folder. When the user launched the updater, it unknowingly loaded the version.dll – which in fact started a Brute Ratel Badger inside the legitimate process (RuntimeBroker.exe)
This technique allowed the Badger to run under the guise of a trusted Microsoft process, blending into the system.
2.2 Post Exploitation Operations With The C2
Badger receives communication: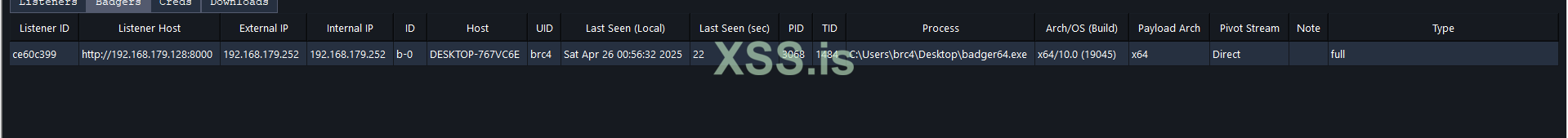
BruteRatel provides a comprehensive menu of built-in commands (the Badger supports on the order of 60+ different actions natively, using a Badger feels similar to using a Cobalt Strike beacon: you can run shell commands, upload/download files, enumerate the system, dump credentials, and pivot to other machines – all from within the BRC4 console. However, there are also some quality-of-life improvements. For example, Brute Ratel’s UI shows a MITRE ATT&CK technique map for every built-in command, This means as you run actions (like credential dumping or lateral movement techniques), BRC4 automatically maps them to ATT&CK techniques, helping you keep track of which tactics have been executed.
2.3 Arsenal
BRC4 includes an LDAP Sentinel module – a point-and-click GUI to query LDAP information from the domain, This saves time over writing custom LDAP queries or running external tools, and it keeps the activity contained within the Badger (no external executables that might get flagged). Similarly, BRC4 allows automation of repetitive tasks or complex chains of actions through its Click Scripts feature, which lets you build custom sequences of commands (even integrating things like C# or PowerShell scripts) and execute them with one clickAn overview of LDAP Sentinel

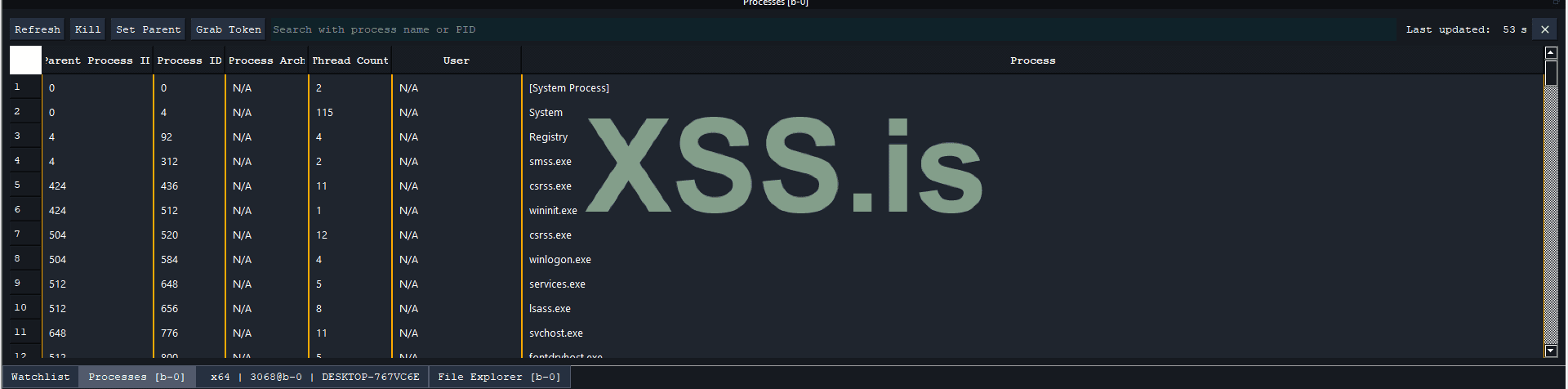
A process explorer and file explorer is also included, a simple overview:
3. Stealth and Evasion in BRC4
Where Brute Ratel truly shines is in its built-in stealth capabilities. Modern EDR and antivirus solutions don’t just look for known malware signatures – they monitor behaviors, API calls, memory anomalies, and more. BRC4 was explicitly designed to fly under these radars, Out of the box, its Badger implant employs numerous tricks to avoid leaving the kinds of traces that defense tools key on.
In-Memory Footprint: Like many post-exploitation agents, Badgers operate mostly in memory to avoid the filesystem. But BRC4 goes further by making its in-memory presence as innocuous as possible. For one, it implements API hashing and indirect execution techniques so that common Windows API functions are not obviously referenced – this confuses static analysis and prevents simplistic hooking of function names
Figure shows API hashing technique
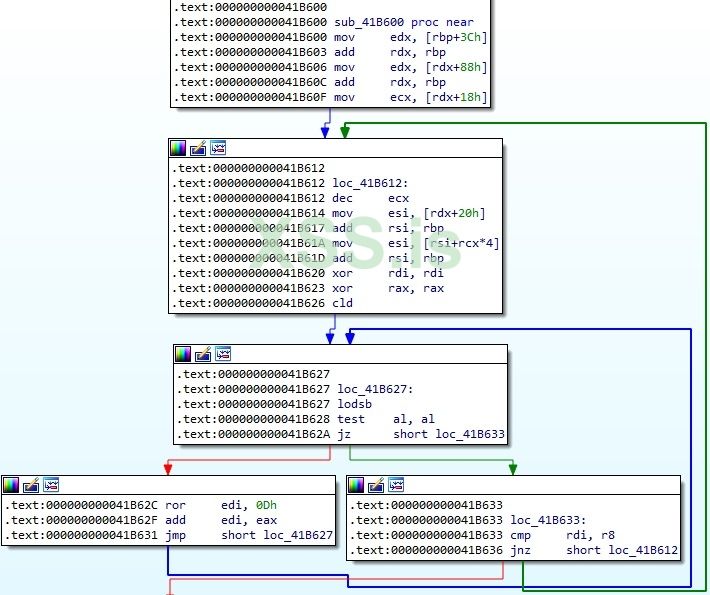
More importantly, Brute Ratel can dynamically switch how it makes system calls.
Using direct system calls means the Badger can bypass user-mode API hooks that EDR products place in DLLs like ntdll.dll.
Cobalt Strike’s beacon, by contrast, would normally use the Windows API and could be detected by those hooks unless one manually integrates a bypass
This level of automated anti-hooking is something operators previously had to handle themselves (e.g. by running an “unhooking” BOF or script in Cobalt Strike); in BRC4 it’s part of the platform’s DNA.
In-Memory Evasion: The Badger can also temporarily encrypt or “sleep” its code sections in memory when idle, using multiple sleep mask techniques on 64-bit systems. This makes it harder for memory scanners to find the agent’s footprints during its downtime.
Encrypted BRC4 Badger:
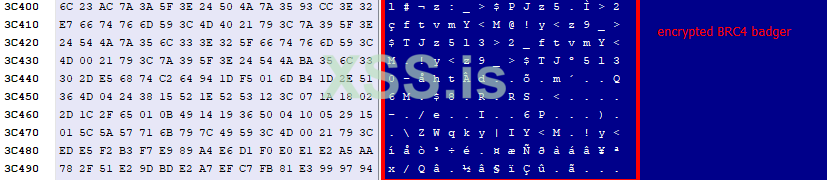
Additionally, BRC4 automatically unhooks APIs and even disables certain Windows telemetry: for instance, it can unhook kernel notifications for DLL loading and use a LoadLibrary proxy to bypass Event Tracing for Windows (ETW) sensors. It even leverages hardware breakpoints to intercept and neuter security APIs like AMSI (Anti-Malware Scan Interface) and ETW at runtime
To put it simply, BruteRatel was built with an assume breach mindset toward EDR: the developer analyzed how top EDR/AV products detect malicious activity, and then designed Badger’s behavior to avoid those detection points
This is why early samples of BRc4 could run through 50+ antivirus engines on VirusTotal with zero detections
4. Lateral Movement and Pivoting
A compromised system running a Badger can act as a pivot point to reach other machines using protocols like SMB, WMI, or WinRM. Command such as pivot_winrm pivot_smb
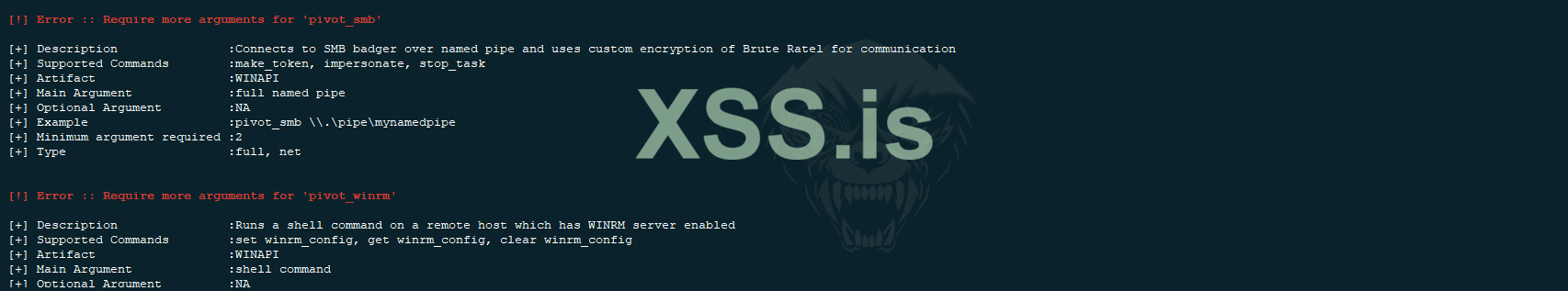
help you do that.
There are many subjects to talk about lateral movement with BRC4, it will take a while to list all, so i only list a few.
BRC4 vs. Cobalt Strike: Key Differences in Practice
It’s natural to compare Brute Ratel C4 with Cobalt Strike, since both are popular adversary simulation frameworks used for post-exploitation. In terms of core functionality, they are quite comparable: both have team servers and operator consoles, both use memory-resident agents (beacons/badgers) to control compromised hosts, both support multiple C2 transports, and both allow extensibility through user scripts or payloads. A skilled operator with Cobalt Strike can achieve most of the same end goals as one using Brute Ratel. Where BRC4 stands out is in the details of stealth, flexibility, and user experience.
Evasion by Design: The most obvious difference is that Brute Ratel embraces EDR evasion as a first-class feature. Many techniques that a Cobalt Strike user might bolt on manually (or via community addons) are integrated into BRC4’s core. For example, BRC4 agents will automatically attempt to unhook security DLLs and use direct syscalls for critical functions
In summary, if you approach Brute Ratel C4 expecting “just another Cobalt Strike,” you’ll quickly notice the emphasis on staying hidden and some polished features that reduce the need for external tooling.
I hope you liked the article, I have been writing it for few hours for now, version 2.1.2 is the latest of BRC4, Thank you for your attention.
Вложения
Последнее редактирование: