ОгнищеДобавил генерацию простенького репорта для обнов.
Пока 4 таблички.
1. Топ-10 CWE
2. Топ-8 высокорисковых уязвимостей (c приоритетом для эксплуатируемых in the wild и с публик эксплойтами)
3. Таблица компонент-бинарь-cve
4. Кол-во патченных функций для бинарей
Посмотреть вложение 106764
Посмотреть вложение 106763
Посмотреть вложение 106762
-
XSS.stack #1 – первый литературный журнал от юзеров форума
Патчдифф для Windows в 2025 году
- Автор темы varwar
- Дата начала
- Автор темы
- Добавить закладку
- #22
Пожалуйста, обратите внимание, что пользователь заблокирован
Patch Report for 2025-05-13
Top 10 CWE's
High-Risk Vulnerabilities
Known Associated CVE's*
Patched Functions per Binary
* Some data might be lost because of mapping incompletion
Top 10 CWE's
| CWE | Count |
|---|---|
| CWE-122 - Heap-based Buffer Overflow | 7 |
| CWE-125 - Out-of-bounds Read | 6 |
| CWE-908 - Use of Uninitialized Resource | 4 |
| CWE-416 - Use After Free | 4 |
| CWE-400 - Uncontrolled Resource Consumption | 2 |
| CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition | 2 |
| CWE-843 - Access of Resource Using Incompatible Type ('Type Confusion') | 1 |
| CWE-59 - Improper Link Resolution Before File Access ('Link Following') | 1 |
| CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') CWE-416 - Use After Free | 1 |
| CWE-349 - Acceptance of Extraneous Untrusted Data With Trusted Data | 1 |
High-Risk Vulnerabilities
| CVE | CWE | Severity | Public | Exploited | Component |
|---|---|---|---|---|---|
| CVE-2025-30397 | CWE-843 - Access of Resource Using Incompatible Type ('Type Confusion') | Important | No | Yes | Microsoft Scripting Engine |
| CVE-2025-30400 | CWE-416 - Use After Free | Important | No | Yes | Windows DWM |
| CVE-2025-32701 | CWE-416 - Use After Free | Important | No | Yes | Windows Common Log File System Driver |
| CVE-2025-32706 | CWE-20 - Improper Input Validation | Important | No | Yes | Windows Common Log File System Driver |
| CVE-2025-32709 | CWE-416 - Use After Free | Important | No | Yes | Windows Ancillary Function Driver for WinSock |
| CVE-2025-29833 | CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition | Critical | No | No | Windows Virtual Machine Bus |
| CVE-2025-29966 | CWE-122 - Heap-based Buffer Overflow | Critical | No | No | Windows Remote Desktop |
| CVE-2025-29967 | CWE-122 - Heap-based Buffer Overflow | Critical | No | No | Remote Desktop Gateway Service |
Known Associated CVE's*
| Component | Binary | CVEs |
|---|---|---|
| Windows Ancillary Function Driver for WinSock | afd.sys | CVE-2025-32709 |
| Windows Common Log File System Driver | clfs.sys | CVE-2025-32701, CVE-2025-32706, CVE-2025-30385 |
| Windows Kernel | ntoskrnl.exe | CVE-2025-29974, CVE-2025-24063 |
Patched Functions per Binary
| Binary | Function Count |
|---|---|
| win32kbase.sys | 430 |
| win32kfull.sys | 188 |
| ntfs.sys | 112 |
| clipsp.sys | 107 |
| refs.sys | 37 |
| ntoskrnl.exe | 26 |
| clfs.sys | 26 |
| vhdmp.sys | 24 |
| afd.sys | 16 |
| ndis.sys | 12 |
| ks.sys | 10 |
| http.sys | 10 |
| wtd.sys | 9 |
| tcpip.sys | 9 |
| mrxsmb.sys | 9 |
| ksecpkg.sys | 9 |
| fvevol.sys | 9 |
| classpnp.sys | 9 |
| ksthunk.sys | 8 |
| bthport.sys | 6 |
| vmswitch.sys | 5 |
| usbvideo.sys | 5 |
| usbxhci.sys | 4 |
| xboxgip.sys | 3 |
| usbhub3.sys | 3 |
| srv2.sys | 3 |
| processr.sys | 3 |
| pci.sys | 3 |
| p9rdr.sys | 3 |
| netvsc.sys | 3 |
| msgpioclx.sys | 3 |
| monitor.sys | 3 |
| mbbcx.sys | 3 |
| dam.sys | 3 |
| bthusb.sys | 3 |
| bindflt.sys | 3 |
| wmiacpi.sys | 2 |
| winnat.sys | 2 |
| usbprint.sys | 2 |
| usbccgp.sys | 2 |
| tpm.sys | 2 |
| tcpipreg.sys | 2 |
| storport.sys | 2 |
| srvnet.sys | 2 |
| rmcast.sys | 2 |
| refsv1.sys | 2 |
| netio.sys | 2 |
| luafv.sys | 2 |
| fltmgr.sys | 2 |
| fastfat.sys | 2 |
| exfat.sys | 2 |
| dxgmms2.sys | 2 |
| dumpfve.sys | 2 |
| cldflt.sys | 2 |
| bthenum.sys | 2 |
| appid.sys | 2 |
| ahcache.sys | 2 |
| acpi.sys | 2 |
| tbs.sys | 1 |
| prjflt.sys | 1 |
| ksecdd.sys | 1 |
| dxgkrnl.sys | 1 |
| crashdmp.sys | 1 |
* Some data might be lost because of mapping incompletion
Последнее редактирование:
- Автор темы
- Добавить закладку
- #23
Пожалуйста, обратите внимание, что пользователь заблокирован
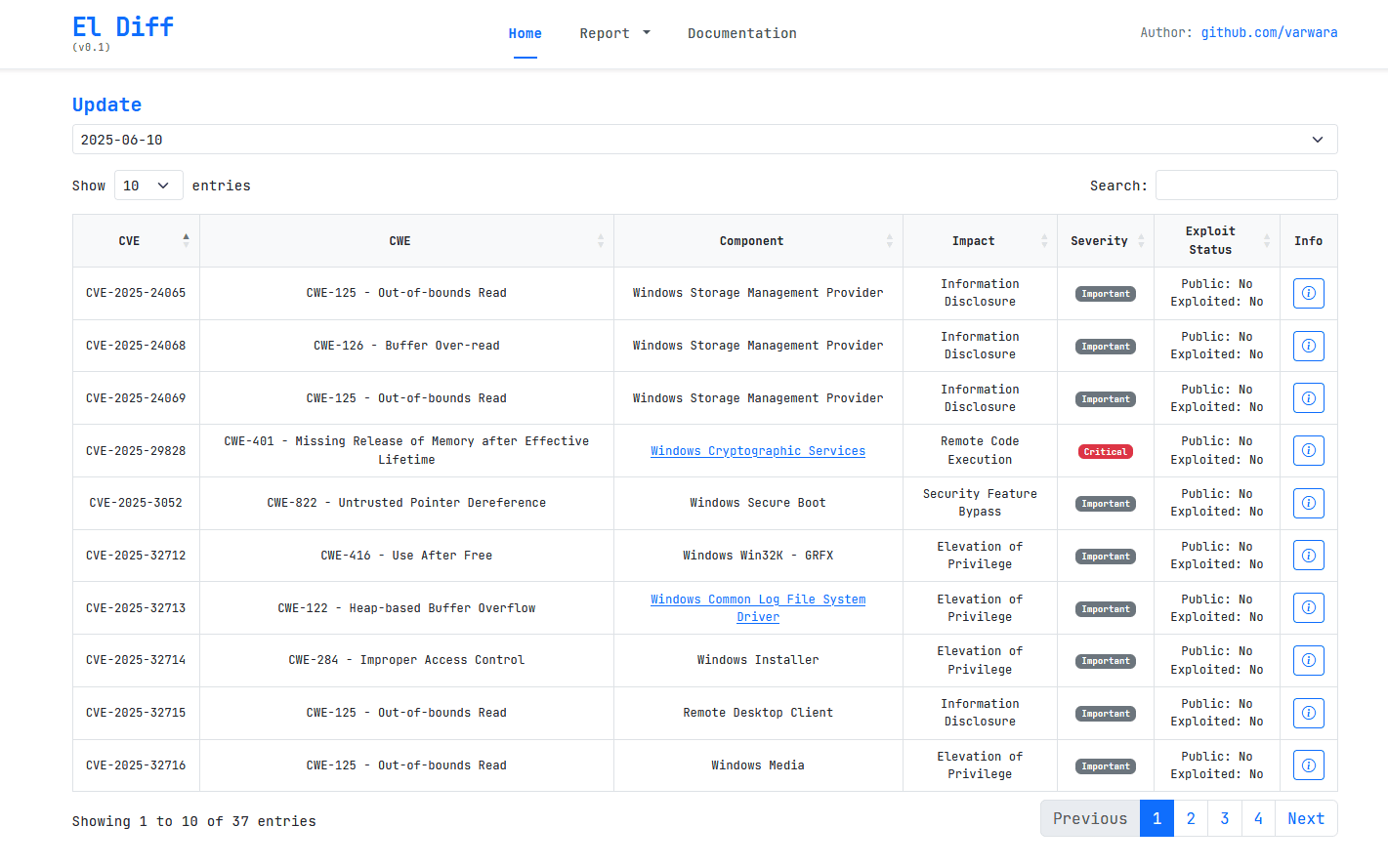
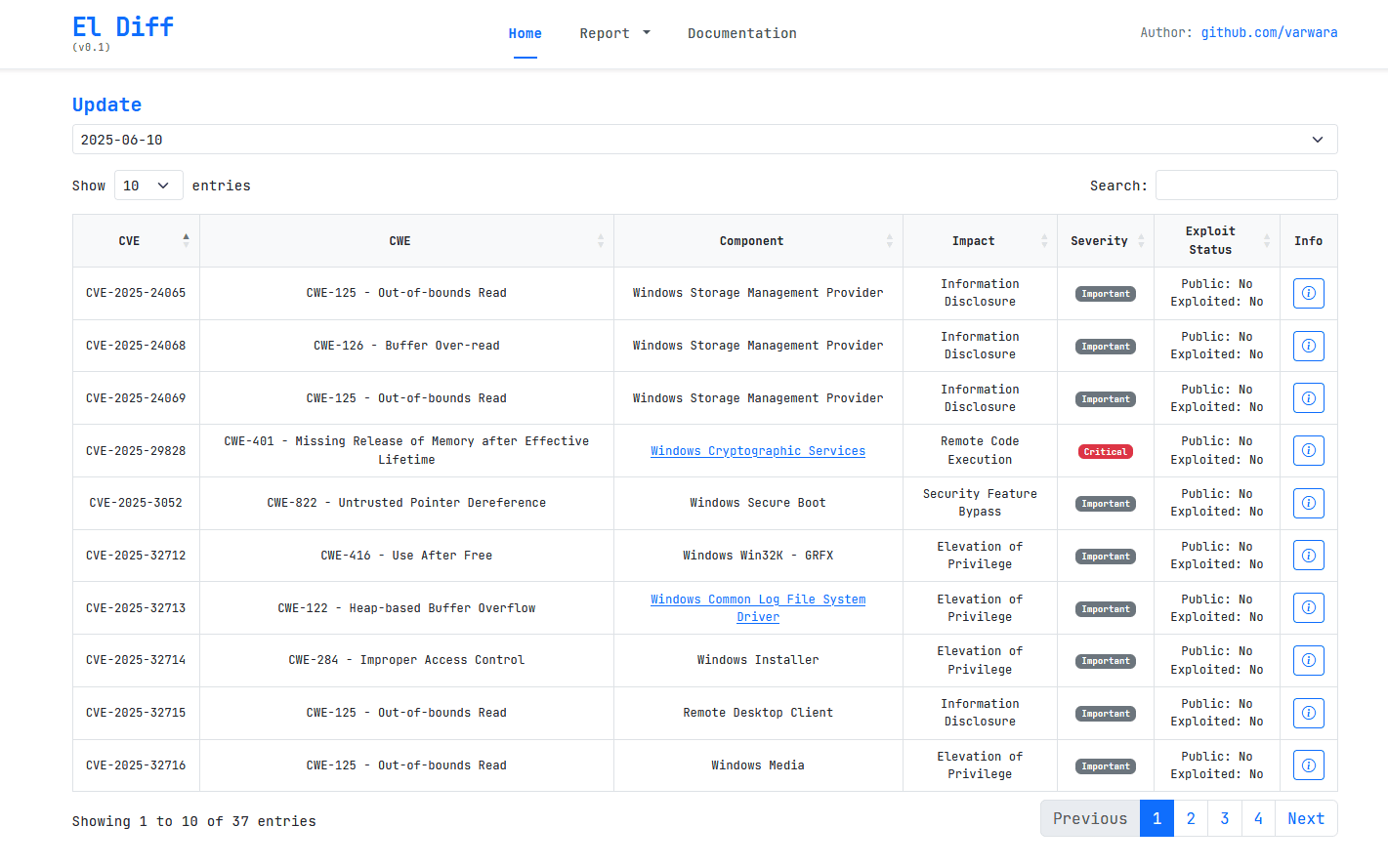
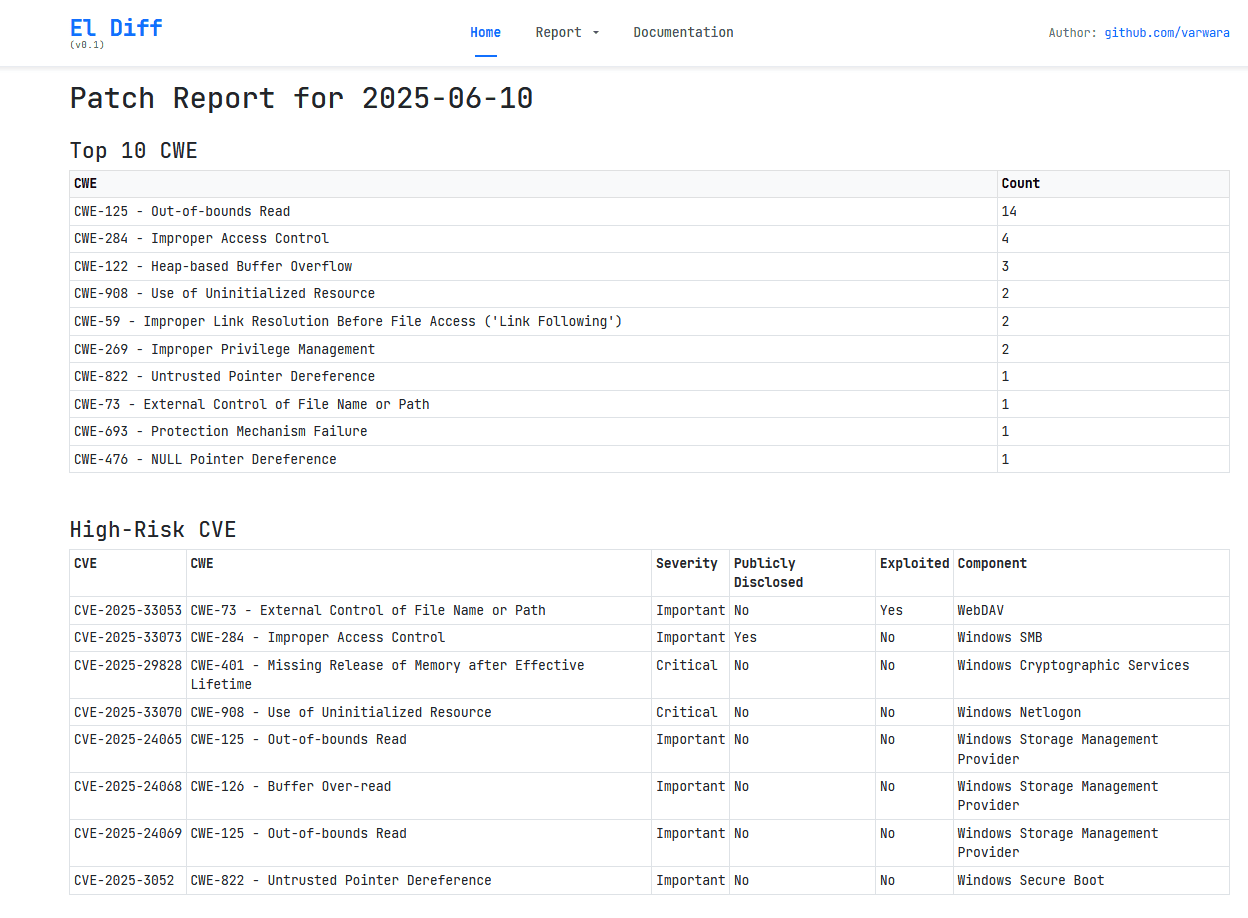
Новости из будущего. В июньском бюллетене будет 37 уязвимостей для Windows 11 23H2.
Уязвимость CVE-2025-33053 (CWE-73 - External Control of File Name or Path) в WebDAV была обнаружена в "дикой природе", а уязвимость CVE-2025-33073 (CWE-284 - Improper Access Control) в SMB имеет публичный PoC.
Подробности в таблице ниже. На текущий момент информации на mitre, nist по перечисленным уязвимостям нет.
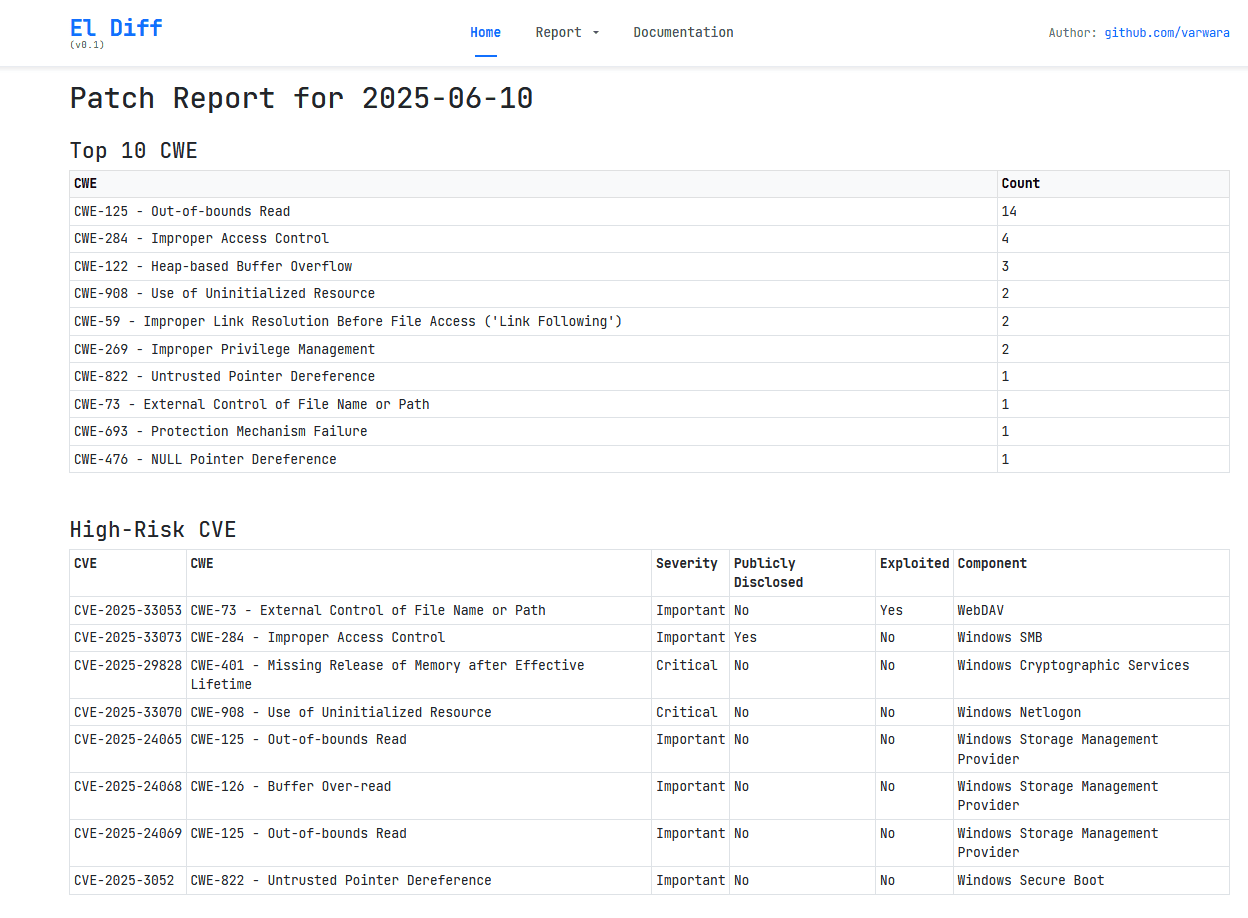
Patch Report for 2025-06-10
Top 10 CWE's
High-Risk Vulnerabilities
All CVE Details
* Some data might be lost because of mapping incompletion
Уязвимость CVE-2025-33053 (CWE-73 - External Control of File Name or Path) в WebDAV была обнаружена в "дикой природе", а уязвимость CVE-2025-33073 (CWE-284 - Improper Access Control) в SMB имеет публичный PoC.
Подробности в таблице ниже. На текущий момент информации на mitre, nist по перечисленным уязвимостям нет.
Patch Report for 2025-06-10
Top 10 CWE's
| CWE | Count |
|---|---|
| CWE-125 - Out-of-bounds Read | 14 |
| CWE-284 - Improper Access Control | 4 |
| CWE-122 - Heap-based Buffer Overflow | 3 |
| CWE-908 - Use of Uninitialized Resource | 2 |
| CWE-59 - Improper Link Resolution Before File Access ('Link Following') | 2 |
| CWE-269 - Improper Privilege Management | 2 |
| CWE-822 - Untrusted Pointer Dereference | 1 |
| CWE-73 - External Control of File Name or Path | 1 |
| CWE-693 - Protection Mechanism Failure | 1 |
| CWE-476 - NULL Pointer Dereference | 1 |
High-Risk Vulnerabilities
| CVE | CWE | Severity | Public | Exploited | Component |
|---|---|---|---|---|---|
| CVE-2025-33053 | CWE-73 - External Control of File Name or Path | Important | No | Yes | WebDAV |
| CVE-2025-33073 | CWE-284 - Improper Access Control | Important | Yes | No | Windows SMB |
| CVE-2025-29828 | CWE-401 - Missing Release of Memory after Effective Lifetime | Critical | No | No | Windows Cryptographic Services |
| CVE-2025-33070 | CWE-908 - Use of Uninitialized Resource | Critical | No | No | Windows Netlogon |
| CVE-2025-24065 | CWE-125 - Out-of-bounds Read | Important | No | No | Windows Storage Management Provider |
| CVE-2025-24068 | CWE-126 - Buffer Over-read | Important | No | No | Windows Storage Management Provider |
| CVE-2025-24069 | CWE-125 - Out-of-bounds Read | Important | No | No | Windows Storage Management Provider |
| CVE-2025-3052 | CWE-822 - Untrusted Pointer Dereference | Important | No | No | Windows Secure Boot |
All CVE Details
| CVE | CWE | Component | Details |
|---|---|---|---|
| CVE-2025-24065 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is an out of bounds read in the caller's address space memory. |
| CVE-2025-24068 | CWE-126 - Buffer Over-read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-24069 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-29828 | CWE-401 - Missing Release of Memory after Effective Lifetime | Windows Cryptographic Services | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to send a large number of messages. How could an attacker exploit the vulnerability? An attacker can exploit this vulnerability through the malicious use of fragmented ClientHello messages to a target server that accepts Transport Layer Security (TLS) connections |
| CVE-2025-3052 | CWE-822 - Untrusted Pointer Dereference | Windows Secure Boot | What kind of security feature could be bypassed by successfully exploiting this vulnerability? An attacker who successfully exploited this vulnerability could bypass Secure Boot. |
| CVE-2025-32712 | CWE-416 - Use After Free | Windows Win32K - GRFX | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-32713 | CWE-122 - Heap-based Buffer Overflow | Windows Common Log File System Driver | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-32714 | CWE-284 - Improper Access Control | Windows Installer | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-32715 | CWE-125 - Out-of-bounds Read | Remote Desktop Client | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. According to the CVSS metric, user interaction is required (UI:R) and privileges required are none (PR:N). What does that mean for this vulnerability? An unauthorized attacker must wait for a user to initiate a connection. |
| CVE-2025-32716 | CWE-125 - Out-of-bounds Read | Windows Media | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-32718 | CWE-190 - Integer Overflow or Wraparound CWE-122 - Heap-based Buffer Overflow | Windows SMB | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-32719 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-32720 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-32721 | CWE-59 - Improper Link Resolution Before File Access ('Link Following') | Windows Recovery Driver | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain administrator privileges. According to the CVSS metric, user interaction is required (UI:R) and privileges required is low (PR:L). What does that mean for this vulnerability? An authorized attacker must send the user a malicious link and convince the user to open it. |
| CVE-2025-32722 | CWE-284 - Improper Access Control | Windows Storage Port Driver | What type of information could be disclosed by this vulnerability? Exploiting this vulnerability could allow the disclosure of certain memory address within kernel space. Knowing the exact location of kernel memory could be potentially leveraged by an attacker for other malicious activities. |
| CVE-2025-32724 | CWE-400 - Uncontrolled Resource Consumption | Windows Local Security Authority Subsystem Service (LSASS) | |
| CVE-2025-33052 | CWE-908 - Use of Uninitialized Resource | Windows DWM Core Library | What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is uninitialized stack memory. |
| CVE-2025-33053 | CWE-73 - External Control of File Name or Path | WebDAV | The Security Updates table indicates that this vulnerability affects all supported versions of Microsoft Windows. Why are IE Cumulative updates listed for Windows Server 2008, Windows Server 2008 R2, Windows Server 2012, and Windows Server 2012 R2? While Microsoft has announced retirement of the Internet Explorer 11 application on certain platforms and the Microsoft Edge Legacy application is deprecated, the underlying MSHTML, EdgeHTML, and scripting platforms are still supported. The MSHTML platform is used by Internet Explorer mode in Microsoft Edge as well as other applications through WebBrowser control. The EdgeHTML platform is used by WebView and some UWP applications. The scripting platforms are used by MSHTML and EdgeHTML but can also be used by other legacy applications. Updates to address vulnerabilities in the MSHTML platform and scripting engine are included in the IE Cumulative Updates; EdgeHTML and Chakra changes are not applicable to those platforms. To stay fully protected, we recommend that customers who install Security Only updates install the IE Cumulative updates for this vulnerability. According to the CVSS metric, the attack vector is network (AV:N) and user interaction is required (UI:R). What is the target context of the remote code execution? This attack requires a user to open a specially crafted file from the attacker to initiate remote code execution. According to the CVSS metric, user interaction is required (UI:R). What interaction would the user have to do? The user would have to click on a specially crafted URL to be compromised by the attacker. |
| CVE-2025-33055 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33056 | CWE-284 - Improper Access Control | Microsoft Local Security Authority Server (lsasrv) | |
| CVE-2025-33057 | CWE-476 - NULL Pointer Dereference | Windows Local Security Authority (LSA) | |
| CVE-2025-33058 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33059 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33060 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33061 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33062 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33063 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33064 | CWE-122 - Heap-based Buffer Overflow | Windows Routing and Remote Access Service (RRAS) | How could an attacker exploit this vulnerability? An authenticated attacker could send a specially crafted protocol message to a Routing and Remote Access Service (RRAS) server, which could lead to remote code execution (RCE) on the RAS server machine. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. |
| CVE-2025-33065 | CWE-125 - Out-of-bounds Read | Windows Storage Management Provider | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-33066 | CWE-122 - Heap-based Buffer Overflow | Windows Routing and Remote Access Service (RRAS) | According to the CVSS metric, the attack vector is network (AV:N) and the user interaction is required (UI:R). What is the target context of the remote code execution? This attack requires a client to connect to a malicious server, and that could allow the attacker to gain code execution on the client. How could an attacker exploit this vulnerability? An unauthenticated attacker could send a specially crafted protocol message to a Routing and Remote Access Service (RRAS) server, which could lead to remote code execution (RCE) on the RAS server machine. |
| CVE-2025-33067 | CWE-269 - Improper Privilege Management | Windows Kernel | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. How could an attacker exploit this vulnerability? An attacker could exploit this vulnerability by capitalizing on the permissions handling flaw in the task scheduler that allows them, without privileges, to interact with certain scheduled tasks under specific conditions. |
| CVE-2025-33070 | CWE-908 - Use of Uninitialized Resource | Windows Netlogon | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to take additional actions prior to exploitation to prepare the target environment. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain domain administrator privileges. How an attacker exploit this vulnerability? The attacker could exploit the vulnerability by leveraging an authentication bypass in the Windows Netlogon service, which would allow an unauthenticated remote code execution without user interaction. |
| CVE-2025-33073 | CWE-284 - Improper Access Control | Windows SMB | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. How could an attacker exploit this vulnerability? When multiple attack vectors can be used, we assign a score based on the scenario with the higher risk. In one such scenario for this vulnerability, the attacker could convince a victim to connect to an attacker controlled malicious application (for example, SMB) server. Upon connecting, the malicious server could compromise the protocol. How could an attacker exploit the vulnerability? To exploit this vulnerability, an attacker could execute a specially crafted malicious script to coerce the victim machine to connect back to the attack system using SMB and authenticate. This could result in elevation of privilege. |
| CVE-2025-33075 | CWE-59 - Improper Link Resolution Before File Access ('Link Following') | Windows Installer | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47160 | CWE-693 - Protection Mechanism Failure | Windows Shell | According to the CVSS metrics, successful exploitation of this vulnerability could lead to no loss of confidentiality (C:N), with minor loss of integrity (I:L) and availability (A:L). What does that mean for this vulnerability? While we cannot rule out the impact to Confidentiality, Integrity, and Availability, the ability to exploit this vulnerability by itself is limited. An attacker would need to combine this with other vulnerabilities to perform an attack. How could an attacker exploit the vulnerability? In an email or instant message attack scenario, the attacker could send the targeted user a specially crafted file that is designed to exploit the vulnerability. In any case an attacker would have no way to force a user to view attacker-controlled content. Instead, an attacker would have to convince a user to take action. For example, an attacker could entice a user to either click a link that directs the user to the attacker's site or send a malicious attachment. According to the CVSS metric, successful exploitation of this vulnerability could lead to some loss of integrity (I:L) and some loss of availability (A:L). What does that mean for this vulnerability? An attacker can craft a malicious file that would evade Mark of the Web (MOTW) defenses, resulting in a limited loss of integrity and availability of security features such as SmartScreen Application Reputation security check and/or the legacy Windows Attachment Services security prompt. How could an attacker exploit the vulnerability? To exploit this vulnerability, an attacker could host a file on an attacker-controlled server, then convince a targeted user to download and open the file. This could allow the attacker to interfere with the Mark of the Web functionality. Please see Additional information about Mark of the Web (https://learn.microsoft.com/en-us/d...#additional-information-about-mark-of-the-web) for further clarification |
| CVE-2025-47955 | CWE-269 - Improper Privilege Management | Windows Remote Access Connection Manager | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47969 | CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor | Windows Hello | What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is secrets or privileged information belonging to the user of the affected application. |
* Some data might be lost because of mapping incompletion
Последнее редактирование:
Пожалуйста, обратите внимание, что пользователь заблокирован
Как думаешь будет ли мощнейший дроп - зероклик эксплойта в октябре под Windows 10, когда поддержка прекратится м? Чтобы убить её окончательно, чтобы все пользователи перешли на Windows 11.Новости из будущего.
- Автор темы
- Добавить закладку
- #25
Пожалуйста, обратите внимание, что пользователь заблокирован
Звучит как план, но мне кажется этот день тогда можно будет объявить международным днем шифрования. На этом концерте будет много АРТистов.Как думаешь будет ли мощнейший дроп - зероклик эксплойта в октябре под Windows 10, когда поддержка прекратится м? Чтобы убить её окончательно, чтобы все пользователи перешли на Windows 11.
Последнее редактирование:
- Автор темы
- Добавить закладку
- #26
Пожалуйста, обратите внимание, что пользователь заблокирован
El Diff — Краткое введение и руководство по использованию
El Diff — это простой веб-интерфейс, позволяющий быстро анализировать обновления Patch Tuesday от Microsoft на уровне бинарников и псевдокода функций.
В базе представлены данные для Windows 11 22/23H2. Информация по уязвимостям актуальна за весь период существования данной версии, а информация по бинарникам доступна частично с декабря 2024 по июнь 2025 года. Базу планирую поддерживать в актуальном состоянии.
Возможности
Инструкция по установке
Воркфлоу
1. Таблица CVE
2. Отображение KB
- Показывает большинство бинарников, затронутыx в обновлении
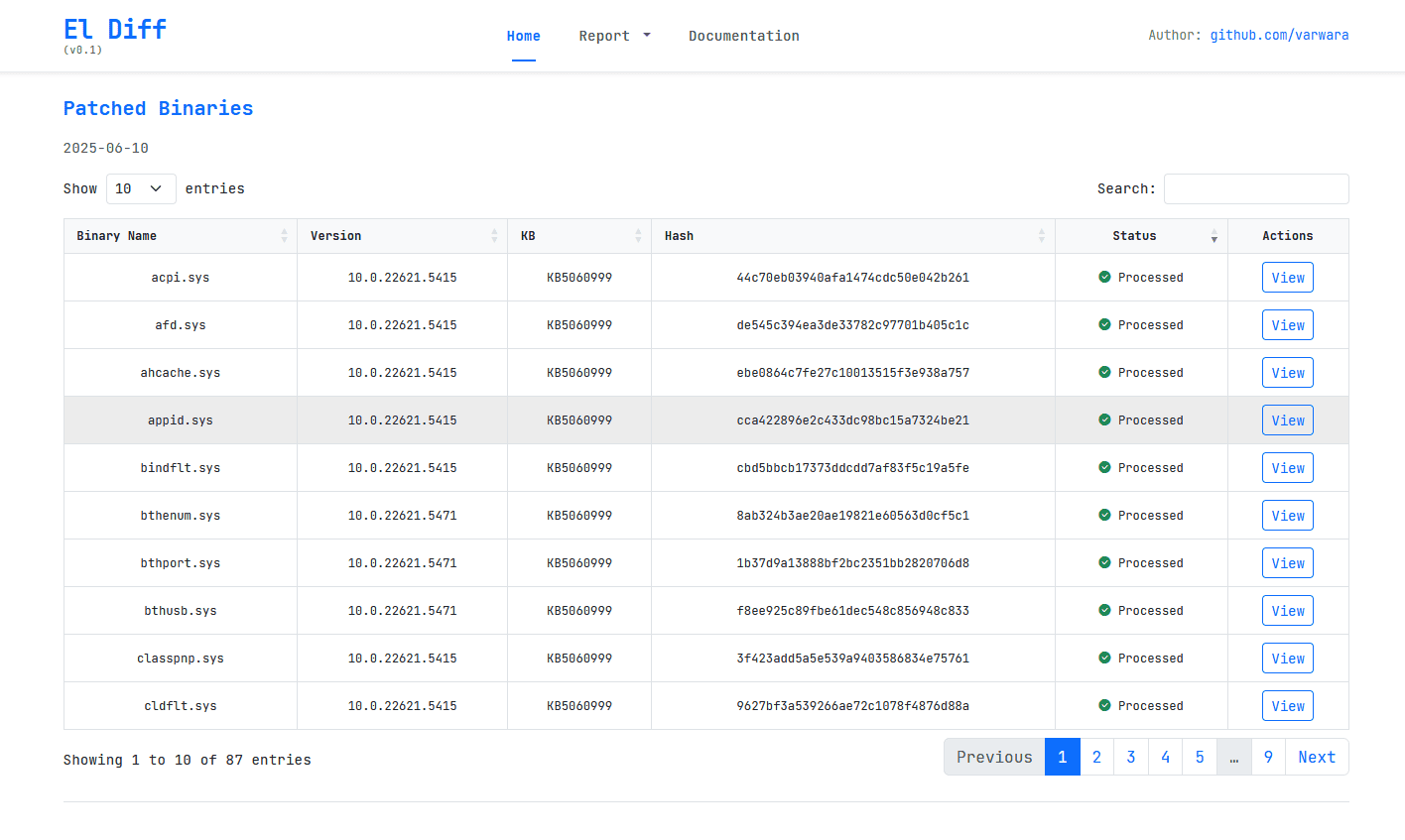
Открытие окна с бинарниками осуществляется по двойному клику в таблице CVE.
3. Отображение изменений
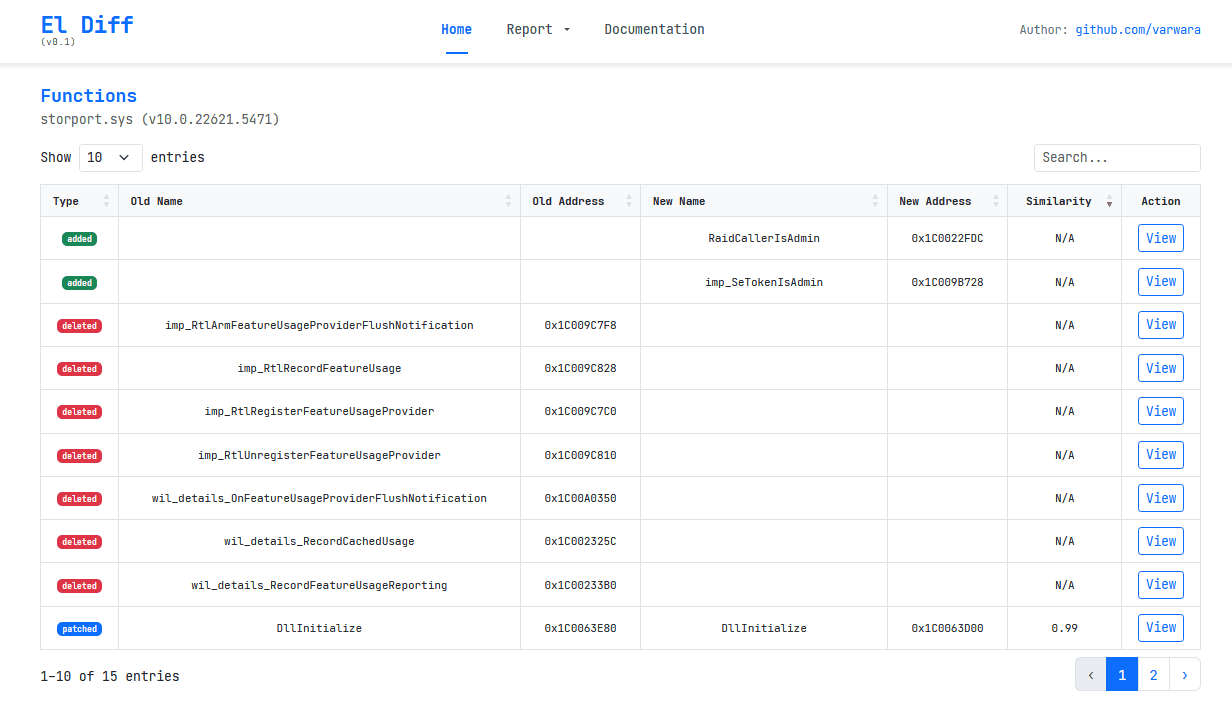
- Таблица всех функций:
- Изменённые
- Добавленные/удалённые и импортированные
Чтобы открыть вкладку с функциями нужно нажать на кнопку View. Вы можете открывать бесконечное число вкладок для удобства.
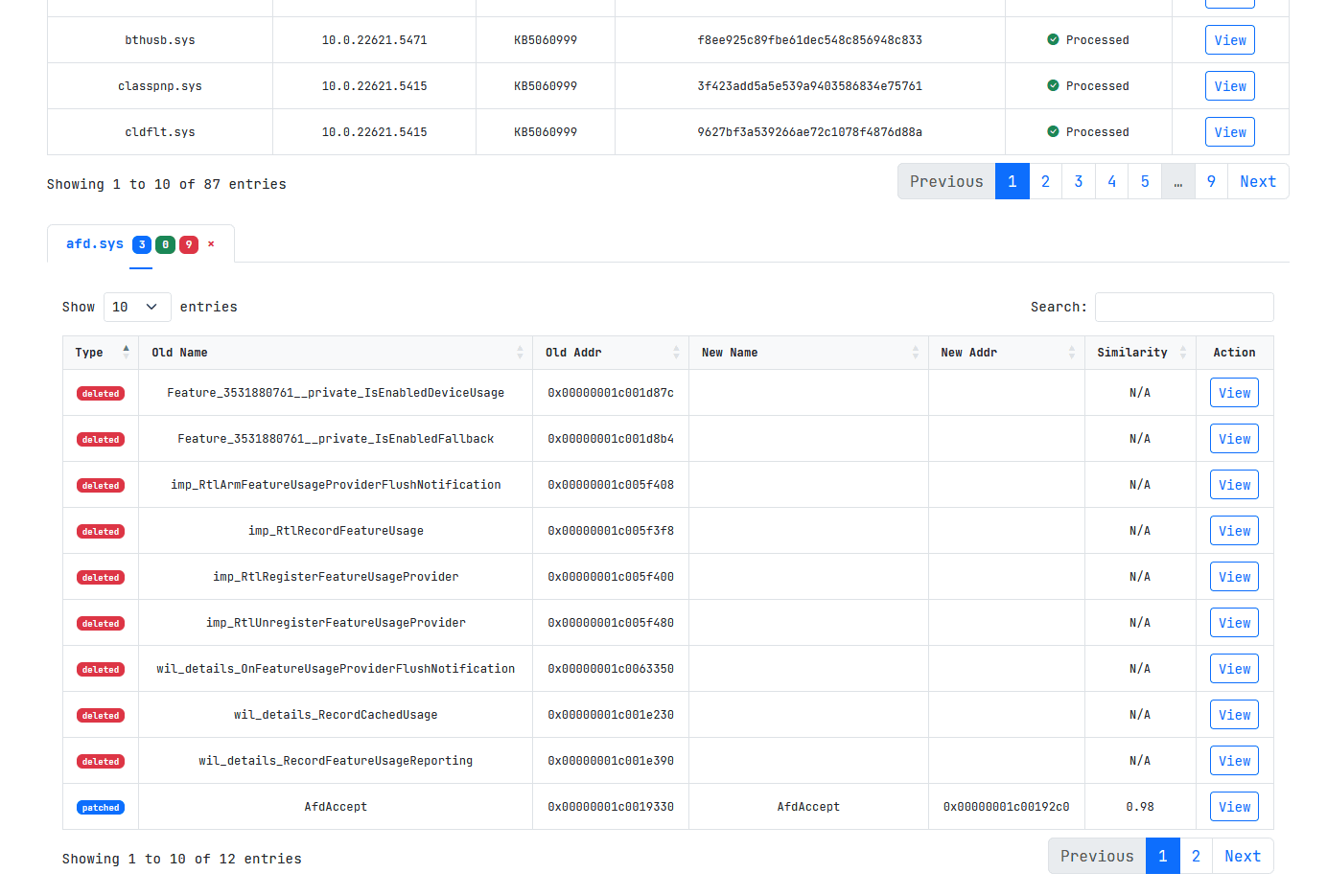
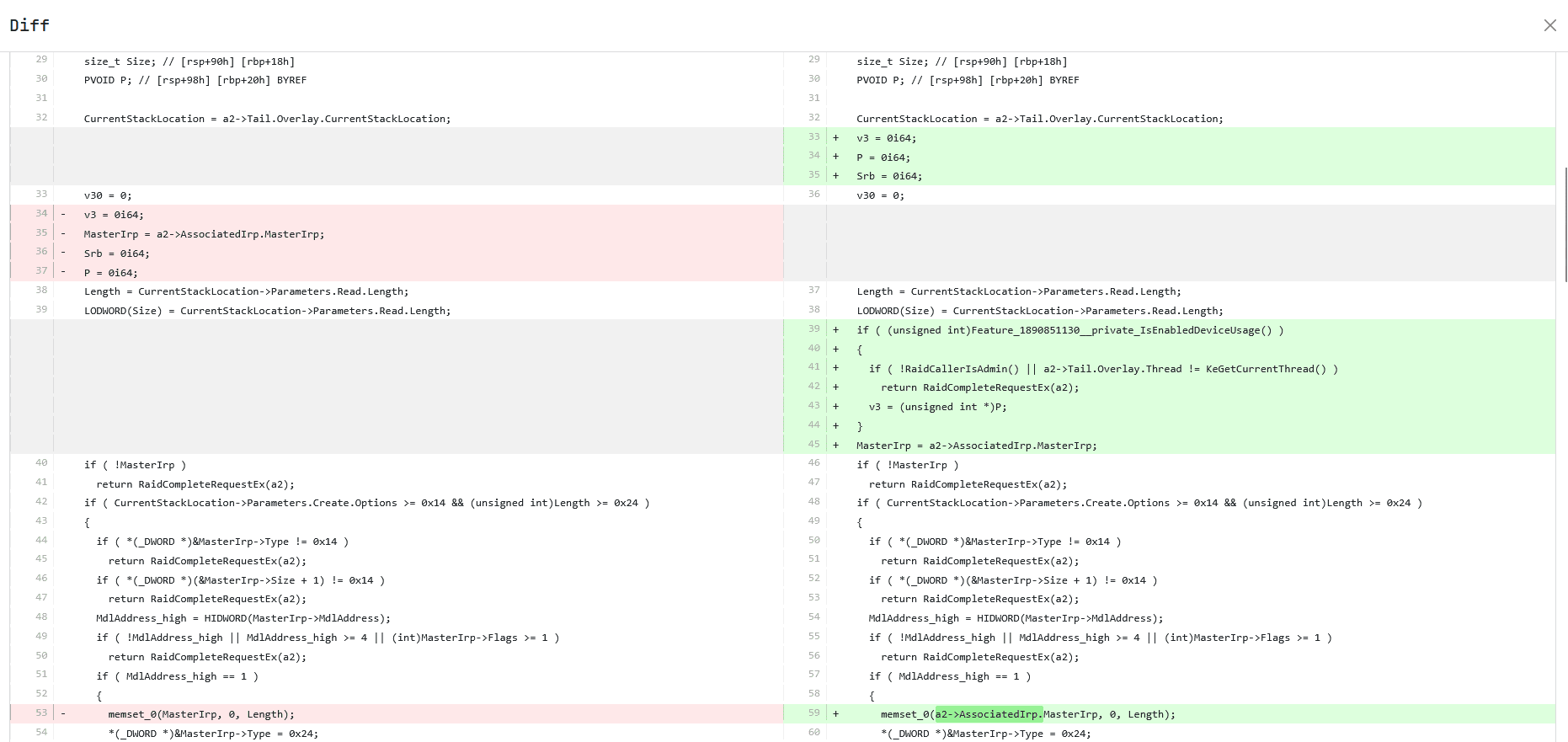
4. Просмотр декомпилированного диффа
- Показывает унифицированный diff для выбранной функции
Чтобы открыть окно с diff нажмите на кнопку View.
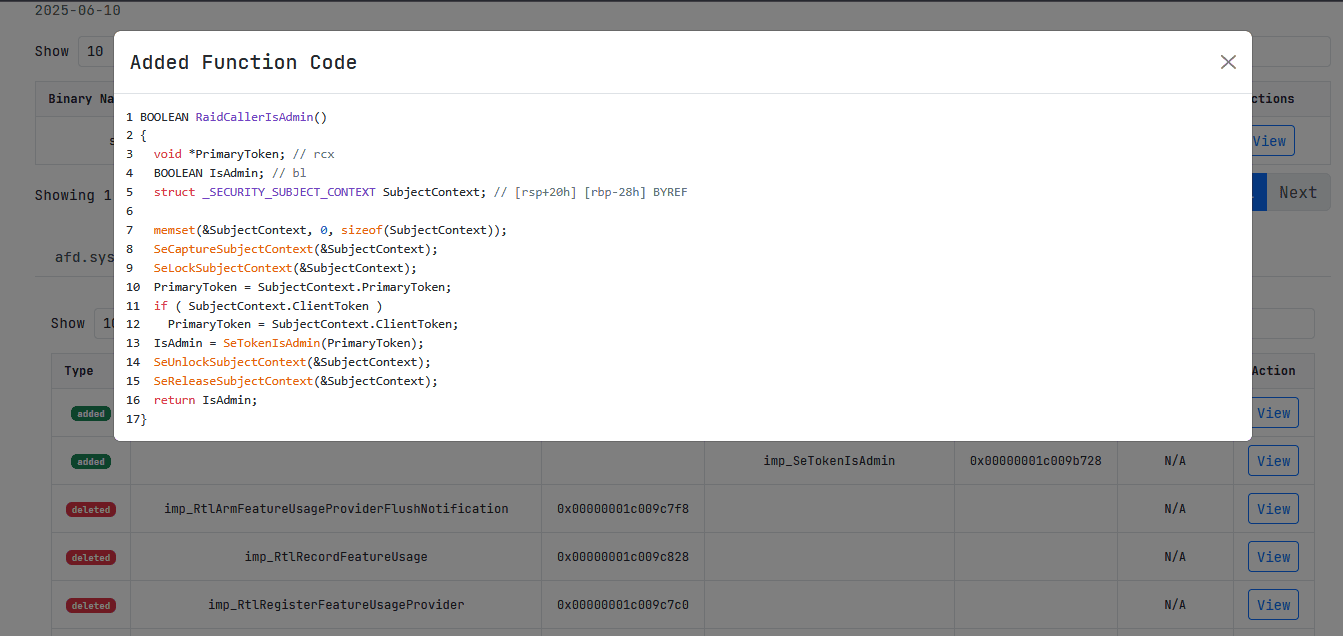
5. Просмотр удаленных и добавленных функций
- Для этих листингов доступна подсветка синтаксиса
6. Маппинг
- Реализован частичный маппинг для уязвимостей и бинарников, позволяющий быстрой перейти по ссылке от списка уязвимостей к уязвимому бинарнику и его функциям. Может быть дополнен самостоятельно посредством прямой записи в базу в таблицу component_mapping.
Простые отчёты
- Отчёт по обновлению включают 4 таблицы со статистикой
- TOP-10 CWE
- High-Risk CVE
- Known Component → Binary → CVE
- Binary Functions
Может быть расширен/модифицирован.
Отчеты доступны по вкладке Report.
Специально для любимого форума.
Поддержать чеканной монетой: bc1q8zznvwzxlf5dmfhw3p940lxtuupdq2v5chmm2t (BTC)
Ссылка на проект: https://github.com/varwara/eldiff
Креды guest:xss.pro
El Diff — это простой веб-интерфейс, позволяющий быстро анализировать обновления Patch Tuesday от Microsoft на уровне бинарников и псевдокода функций.
В базе представлены данные для Windows 11 22/23H2. Информация по уязвимостям актуальна за весь период существования данной версии, а информация по бинарникам доступна частично с декабря 2024 по июнь 2025 года. Базу планирую поддерживать в актуальном состоянии.
Возможности
- Просмотр всех CVE из выбранного обновления Microsoft
- Анализ бинарников с отображением изменений функций
- Просмотр добавленных, удалённых и изменённых функций
- Декомпилированные диффы
- Частичный маппинг для бинарников и уязвимостей
Инструкция по установке
Код:
git clone https://github.com/varwara/eldiff.git
cd eldiff
python3 -m venv venv
source venv/bin/activate
pip install -r requirements.txt
export FLASK_APP=eldiff_minimal.py
flask run --debugВоркфлоу
1. Таблица CVE
- Показывает CVE из последнего обновления
- Выпадающее меню позволяет выбрать другое обновление (например,
2024-Jun) - По кнопке Info открывается окно с деталями для текущей CVE
2. Отображение KB
- Показывает большинство бинарников, затронутыx в обновлении
Открытие окна с бинарниками осуществляется по двойному клику в таблице CVE.
3. Отображение изменений
- Таблица всех функций:
- Изменённые
- Добавленные/удалённые и импортированные
Чтобы открыть вкладку с функциями нужно нажать на кнопку View. Вы можете открывать бесконечное число вкладок для удобства.
4. Просмотр декомпилированного диффа
- Показывает унифицированный diff для выбранной функции
Чтобы открыть окно с diff нажмите на кнопку View.
5. Просмотр удаленных и добавленных функций
- Для этих листингов доступна подсветка синтаксиса
6. Маппинг
- Реализован частичный маппинг для уязвимостей и бинарников, позволяющий быстрой перейти по ссылке от списка уязвимостей к уязвимому бинарнику и его функциям. Может быть дополнен самостоятельно посредством прямой записи в базу в таблицу component_mapping.
Простые отчёты
- Отчёт по обновлению включают 4 таблицы со статистикой
- TOP-10 CWE
- High-Risk CVE
- Known Component → Binary → CVE
- Binary Functions
Может быть расширен/модифицирован.
Отчеты доступны по вкладке Report.
Специально для любимого форума.
Поддержать чеканной монетой: bc1q8zznvwzxlf5dmfhw3p940lxtuupdq2v5chmm2t (BTC)
Ссылка на проект: https://github.com/varwara/eldiff
Креды guest:xss.pro
огоньEl Diff — Краткое введение и руководство по использованию
El Diff — это простой веб-интерфейс, позволяющий быстро анализировать обновления Patch Tuesday от Microsoft на уровне бинарников и псевдокода функций.
В базе представлены данные для Windows 11 22/23H2. Информация по уязвимостям актуальна за весь период существования данной версии, а информация по бинарникам доступна частично с декабря 2024 по июнь 2025 года. Базу планирую поддерживать в актуальном состоянии.
Возможности
- Просмотр всех CVE из выбранного обновления Microsoft
- Анализ бинарников с отображением изменений функций
- Просмотр добавленных, удалённых и изменённых функций
- Декомпилированные диффы
- Частичный маппинг для бинарников и уязвимостей
Инструкция по установке
Код:git clone https://github.com/varwara/eldiff.git cd eldiff python3 -m venv venv source venv/bin/activate pip install -r requirements.txt export FLASK_APP=eldiff_minimal.py flask run --debug
Воркфлоу
1. Таблица CVE
- Показывает CVE из последнего обновления
- Выпадающее меню позволяет выбрать другое обновление (например,
2024-Jun)- По кнопке Info открывается окно с деталями для текущей CVE
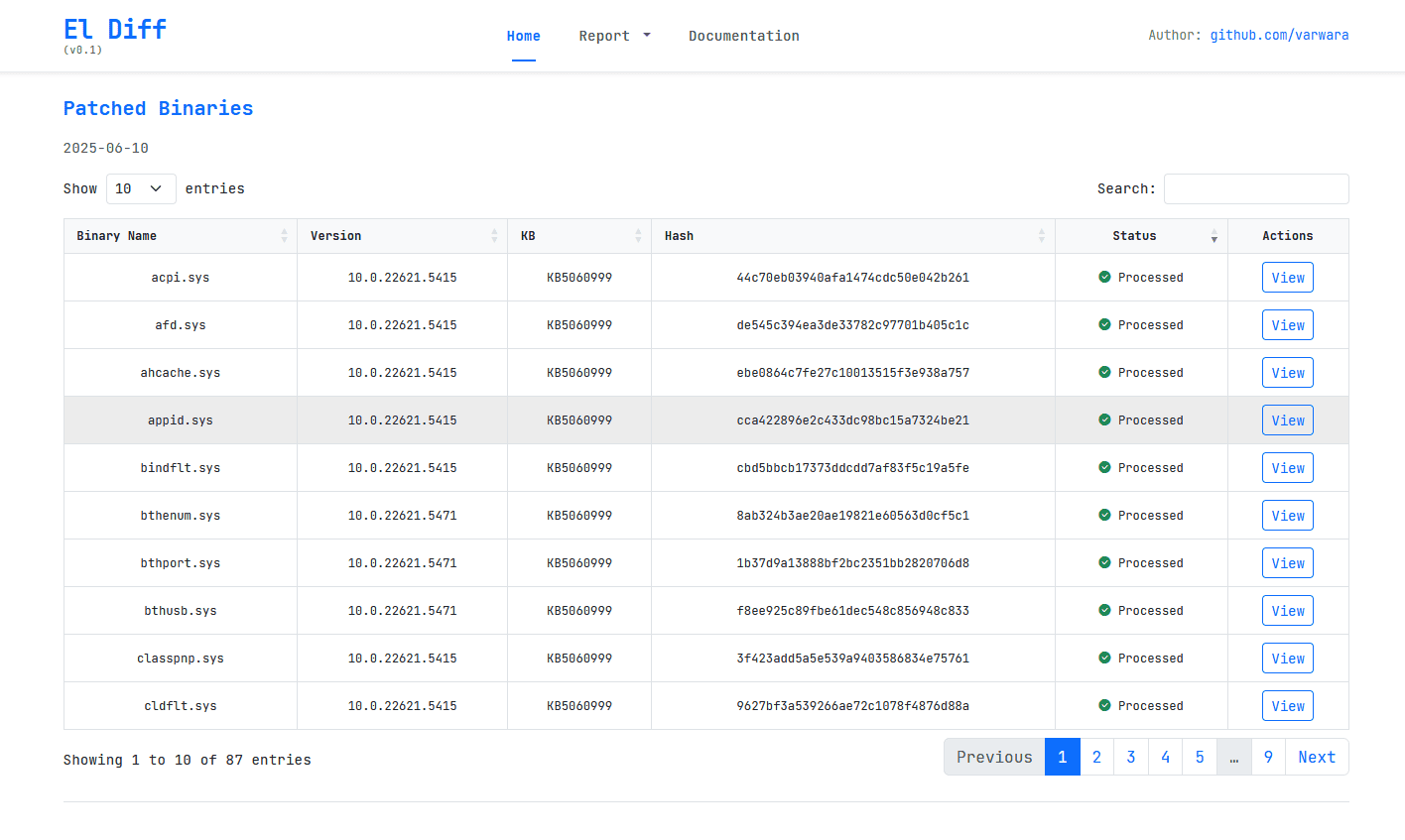
Посмотреть вложение 108684
2. Отображение KB
- Показывает большинство бинарников, затронутыx в обновлении
Посмотреть вложение 108683
Открытие окна с бинарниками осуществляется по двойному клику в таблице CVE.
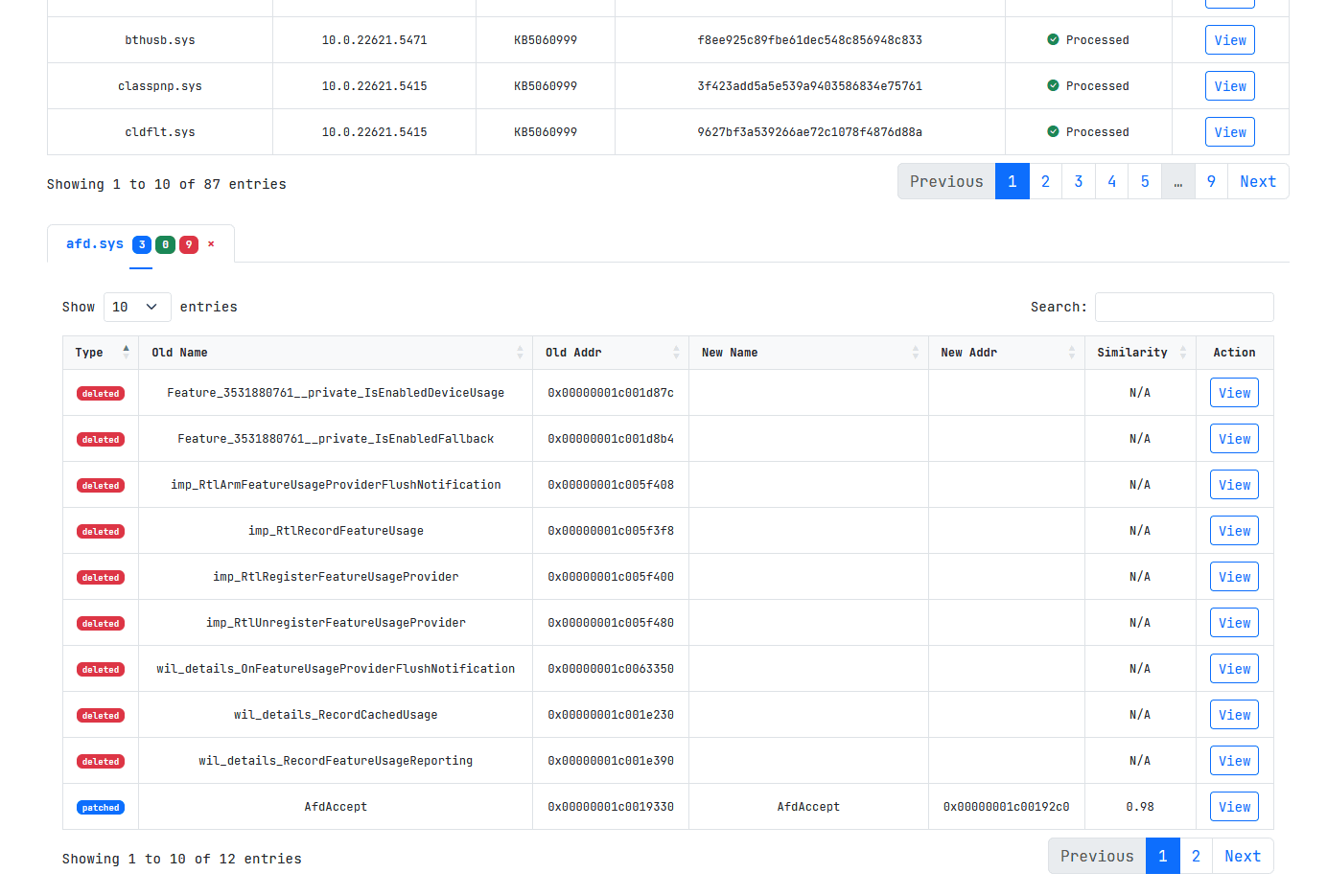
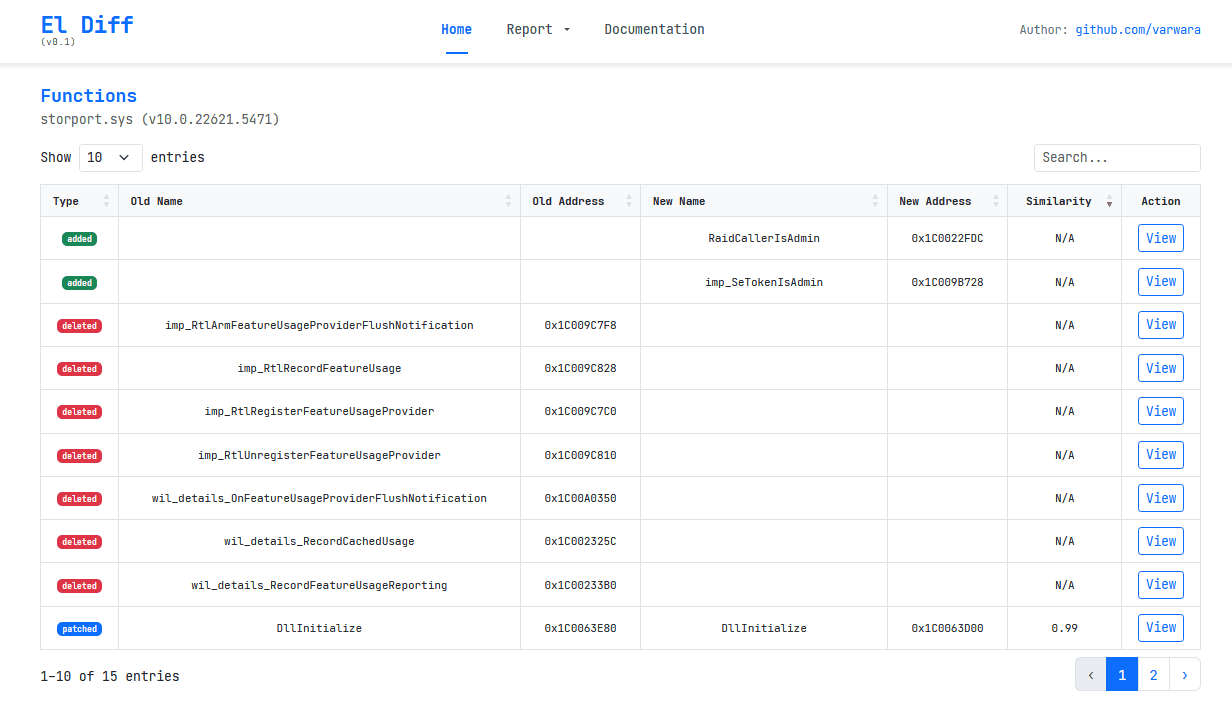
3. Отображение изменений
- Таблица всех функций:
- Изменённые
- Добавленные/удалённые и импортированные
Чтобы открыть вкладку с функциями нужно нажать на кнопку View. Вы можете открывать бесконечное число вкладок для удобства.
Посмотреть вложение 108682
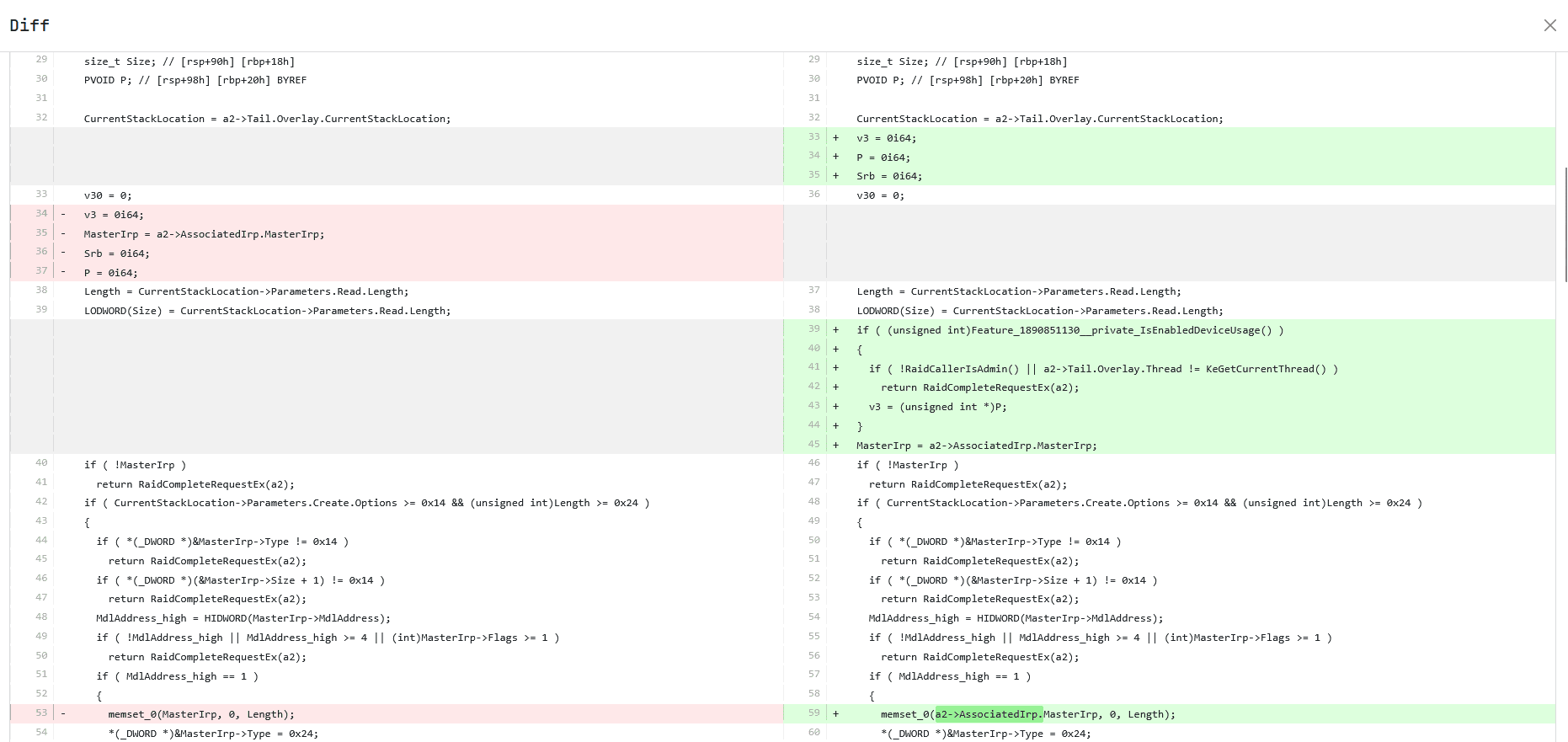
4. Просмотр декомпилированного диффа
- Показывает унифицированный diff для выбранной функции
Чтобы открыть окно с diff нажмите на кнопку View.
Посмотреть вложение 108681
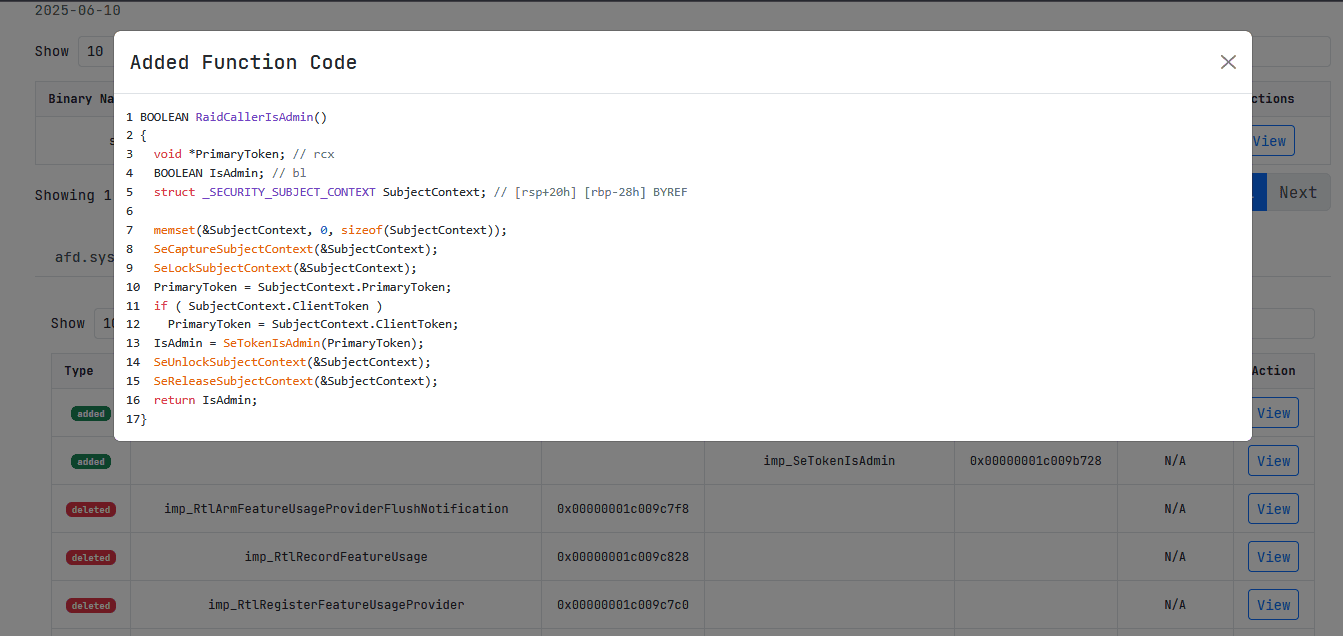
5. Просмотр удаленных и добавленных функций
- Для этих листингов доступна подсветка синтаксиса
Посмотреть вложение 108680
6. Маппинг
- Реализован частичный маппинг для уязвимостей и бинарников, позволяющий быстрой перейти по ссылке от списка уязвимостей к уязвимому бинарнику и его функциям. Может быть дополнен самостоятельно посредством прямой записи в базу в таблицу component_mapping.
Посмотреть вложение 108678
Простые отчёты
- Отчёт по обновлению включают 4 таблицы со статистикой
- TOP-10 CWE
- High-Risk CVE
- Known Component → Binary → CVE
- Binary Functions
Может быть расширен/модифицирован.
Отчеты доступны по вкладке Report.
Посмотреть вложение 108679
Специально для любимого форума.
Поддержать чеканной монетой: bc1q8zznvwzxlf5dmfhw3p940lxtuupdq2v5chmm2t (BTC)
Ссылка на проект: https://github.com/varwara/eldiff
Креды guest:xss.pro
посмотрел блин воообще класс, дизайн очень кайфовый глаз радуется все понятно и предельно просто. Красавчик.El Diff — Краткое введение и руководство по использованию
El Diff — это простой веб-интерфейс, позволяющий быстро анализировать обновления Patch Tuesday от Microsoft на уровне бинарников и псевдокода функций.
В базе представлены данные для Windows 11 22/23H2. Информация по уязвимостям актуальна за весь период существования данной версии, а информация по бинарникам доступна частично с декабря 2024 по июнь 2025 года. Базу планирую поддерживать в актуальном состоянии.
Возможности
- Просмотр всех CVE из выбранного обновления Microsoft
- Анализ бинарников с отображением изменений функций
- Просмотр добавленных, удалённых и изменённых функций
- Декомпилированные диффы
- Частичный маппинг для бинарников и уязвимостей
Инструкция по установке
Код:git clone https://github.com/varwara/eldiff.git cd eldiff python3 -m venv venv source venv/bin/activate pip install -r requirements.txt export FLASK_APP=eldiff_minimal.py flask run --debug
Воркфлоу
1. Таблица CVE
- Показывает CVE из последнего обновления
- Выпадающее меню позволяет выбрать другое обновление (например,
2024-Jun)- По кнопке Info открывается окно с деталями для текущей CVE
Посмотреть вложение 108684
2. Отображение KB
- Показывает большинство бинарников, затронутыx в обновлении
Посмотреть вложение 108683
Открытие окна с бинарниками осуществляется по двойному клику в таблице CVE.
3. Отображение изменений
- Таблица всех функций:
- Изменённые
- Добавленные/удалённые и импортированные
Чтобы открыть вкладку с функциями нужно нажать на кнопку View. Вы можете открывать бесконечное число вкладок для удобства.
Посмотреть вложение 108682
4. Просмотр декомпилированного диффа
- Показывает унифицированный diff для выбранной функции
Чтобы открыть окно с diff нажмите на кнопку View.
Посмотреть вложение 108681
5. Просмотр удаленных и добавленных функций
- Для этих листингов доступна подсветка синтаксиса
Посмотреть вложение 108680
6. Маппинг
- Реализован частичный маппинг для уязвимостей и бинарников, позволяющий быстрой перейти по ссылке от списка уязвимостей к уязвимому бинарнику и его функциям. Может быть дополнен самостоятельно посредством прямой записи в базу в таблицу component_mapping.
Посмотреть вложение 108678
Простые отчёты
- Отчёт по обновлению включают 4 таблицы со статистикой
- TOP-10 CWE
- High-Risk CVE
- Known Component → Binary → CVE
- Binary Functions
Может быть расширен/модифицирован.
Отчеты доступны по вкладке Report.
Посмотреть вложение 108679
Специально для любимого форума.
Поддержать чеканной монетой: bc1q8zznvwzxlf5dmfhw3p940lxtuupdq2v5chmm2t (BTC)
Ссылка на проект: https://github.com/varwara/eldiff
Креды guest:xss.pro
- Автор темы
- Добавить закладку
- #28
Пожалуйста, обратите внимание, что пользователь заблокирован
Спасибо. Я конечно далеко не дизайнер, но пока так вижу.посмотрел блин воообще класс, дизайн очень кайфовый глаз радуется все понятно и предельно просто. Красавчик.
- Автор темы
- Добавить закладку
- #29
Пожалуйста, обратите внимание, что пользователь заблокирован
Подъехали обновы за июль. Обновленная база - http://**************************************************************/d/4bepAxetDoEhVJTnoAzni2
Заменить в папке /data.
Patch Report for 2025-07-08
Top 10 CWEs
High-Risk Vulnerabilities
Known Associated CVEs
Function Changes by Binary
All CVE Details
* Some data might be lost because of mapping incompletion
Заменить в папке /data.
Patch Report for 2025-07-08
Top 10 CWEs
| CWE | Count |
|---|---|
| CWE-416 - Use After Free | 13 |
| CWE-122 - Heap-based Buffer Overflow | 6 |
| CWE-693 - Protection Mechanism Failure | 5 |
| CWE-126 - Buffer Over-read | 4 |
| CWE-59 - Improper Link Resolution Before File Access ('Link Following') | 3 |
| CWE-415 - Double Free | 3 |
| CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor | 3 |
| CWE-125 - Out-of-bounds Read | 3 |
| 3 | |
| CWE-822 - Untrusted Pointer Dereference | 2 |
High-Risk Vulnerabilities
| CVE | CWE | Severity | Public | Exploited | Component |
|---|---|---|---|---|---|
| CVE-2025-36350 | Critical | No | No | AMD Store Queue | |
| CVE-2025-36357 | Critical | No | No | AMD L1 Data Queue | |
| CVE-2025-47980 | CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor | Critical | No | No | Windows Imaging Component |
| CVE-2025-47981 | CWE-122 - Heap-based Buffer Overflow | Critical | No | No | Windows SPNEGO Extended Negotiation |
| CVE-2025-48822 | CWE-125 - Out-of-bounds Read | Critical | No | No | Role: Windows Hyper-V |
| CVE-2025-33054 | CWE-357 - Insufficient UI Warning of Dangerous Operations | Important | No | No | Remote Desktop Client |
| CVE-2025-47159 | CWE-693 - Protection Mechanism Failure | Important | No | No | Windows Virtualization-Based Security (VBS) Enclave |
| CVE-2025-47971 | CWE-126 - Buffer Over-read | Important | No | No | Virtual Hard Disk (VHDX) |
Known Associated CVEs
| Component | Binary | CVEs |
|---|---|---|
| Kernel Streaming WOW Thunk Service Driver | ksthunk.sys | CVE-2025-49675 |
| Windows Ancillary Function Driver for WinSock | afd.sys | CVE-2025-49661 |
| Windows BitLocker | fvevol.sys | CVE-2025-48001, CVE-2025-48003, CVE-2025-48800, CVE-2025-48818, CVE-2025-48804 |
| Windows Fast FAT Driver | fastfat.sys | CVE-2025-49721 |
| Windows Kernel | ntoskrnl.exe | CVE-2025-48808 |
| Windows Storage VSP Driver | storvsp.sys | CVE-2025-47982 |
| Windows TCP/IP | tcpip.sys | CVE-2025-49686 |
Function Changes by Binary
| Binary | Patched | Added | Deleted |
|---|---|---|---|
| afd.sys (10.0.22621.5624) | 1 | 2 | 0 |
| ahcache.sys (10.0.22621.5547) | 0 | 0 | 0 |
| appid.sys (10.0.22621.5547) | 0 | 0 | 0 |
| applockerfltr.sys (10.0.22621.5547) | 0 | 0 | 0 |
| bootmgfw.efi (10.0.22621.5624) | 1 | 0 | 0 |
| bthenum.sys (10.0.22621.5624) | 0 | 0 | 0 |
| bthmini.sys (10.0.22621.5624) | 0 | 0 | 0 |
| bthport.sys (10.0.22621.5624) | 0 | 0 | 0 |
| bthusb.sys (10.0.22621.5624) | 0 | 0 | 0 |
| clfs.sys (10.0.22621.5547) | 2 | 0 | 2 |
| clipsp.sys (10.0.22621.5547) | 105 | 13 | 14 |
| dumpfve.sys (10.0.22621.5624) | 0 | 0 | 0 |
| dxgkrnl.sys (10.0.22621.5547) | 3 | 0 | 7 |
| dxgmms1.sys (10.0.22621.5547) | 0 | 0 | 0 |
| dxgmms2.sys (10.0.22621.5547) | 0 | 0 | 0 |
| exfat.sys (10.0.22621.5624) | 4 | 0 | 0 |
| fastfat.sys (10.0.22621.5624) | 12 | 2 | 0 |
| fvevol.sys (10.0.22621.5624) | 0 | 0 | 0 |
| fwpkclnt.sys (10.0.22621.5624) | 0 | 0 | 0 |
| hdaudio.sys (10.0.22621.5624) | 0 | 0 | 0 |
| hvax64.exe (10.0.22621.5624) | 60 | 0 | 0 |
| hvix64.exe (10.0.22621.5624) | 27 | 0 | 0 |
| hvloader.dll (10.0.22621.5624) | 0 | 0 | 0 |
| kdhvcom.dll (10.0.22621.5624) | 0 | 0 | 0 |
| ks.sys (10.0.22621.5547) | 3 | 0 | 8 |
| ksecpkg.sys (10.0.22621.5547) | 0 | 0 | 0 |
| ksthunk.sys (10.0.22621.5624) | 8 | 0 | 4 |
| mrxsmb.sys (10.0.22621.5624) | 4 | 5 | 0 |
| mskssrv.sys (10.0.22621.5547) | 0 | 0 | 0 |
| netio.sys (10.0.22621.5624) | 0 | 0 | 0 |
| ntfs.sys (10.0.22621.5624) | 13 | 0 | 6 |
| ntoskrnl.exe (10.0.22621.5624) | 218 | 25 | 0 |
| pci.sys (10.0.22621.5547) | 0 | 0 | 0 |
| processr.sys (10.0.22621.5624) | 4 | 1 | 0 |
| rdpvideominiport.sys (10.0.22621.5624) | 0 | 0 | 0 |
| refs.sys (10.0.22621.5547) | 13 | 0 | 2 |
| srv.sys (10.0.22621.5624) | 0 | 0 | 0 |
| srv2.sys (10.0.22621.5624) | 0 | 0 | 0 |
| srvnet.sys (10.0.22621.5624) | 10 | 3 | 0 |
| storport.sys (10.0.22621.5624) | 2 | 2 | 0 |
| storvsp.sys (10.0.22621.5624) | 0 | 0 | 0 |
| tcpip.sys (10.0.22621.5624) | 0 | 0 | 0 |
| tcpipreg.sys (10.0.22621.5624) | 0 | 0 | 0 |
| usbvideo.sys (10.0.22621.5547) | 24 | 0 | 7 |
| vkrnlintvsp.sys (10.0.22621.5547) | 0 | 0 | 0 |
| vmsproxy.sys (10.0.22621.5624) | 0 | 0 | 0 |
| vmsproxyhnic.sys (10.0.22621.5624) | 0 | 0 | 0 |
| vmswitch.sys (10.0.22621.5624) | 0 | 0 | 0 |
| win32k.sys (10.0.22621.5624) | 0 | 0 | 0 |
| win32kbase.sys (10.0.22621.5624) | 24 | 3 | 0 |
| win32kfull.sys (10.0.22621.5624) | 42 | 10 | 0 |
| winload.exe (10.0.22621.5624) | 2 | 0 | 0 |
| xboxgip.sys (10.0.22621.5547) | 0 | 0 | 0 |
All CVE Details
| CVE | CWE | Tag | Details |
|---|---|---|---|
| CVE-2025-33054 | CWE-357 - Insufficient UI Warning of Dangerous Operations | Remote Desktop Client | According to the CVSS metric, user interaction is required (UI:R). What does that mean for this vulnerability? An attacker must trick the user into interacting with a spoofed WebAuthn prompt and entering their credentials. According to the CVSS metric, user interaction is required (UI:R) and privileges required are none (PR:N). What does that mean for this vulnerability? An unauthorized attacker must wait for a user to initiate a connection. |
| CVE-2025-36350 | AMD Store Queue | Why is this AMD CVE included in the Security Update Guide? The vulnerability assigned to this CVE is in certain processor models offered by AMD. The mitigation for this vulnerability requires a Windows update. This CVE is being documented in the Security Update Guide to announce that the latest builds of Windows enable the mitigation and provide protection against the vulnerability. Please see the following for more information: AMD-SB-7029 (https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7029.html) | |
| CVE-2025-36357 | AMD L1 Data Queue | Why is this AMD CVE included in the Security Update Guide? The vulnerability assigned to this CVE is in certain processor models offered by AMD. The mitigation for this vulnerability requires a Windows update. This CVE is being documented in the Security Update Guide to announce that the latest builds of Windows enable the mitigation and provide protection against the vulnerability. Please see the following for more information: AMD-SB-7029 (https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7029.html) | |
| CVE-2025-47159 | CWE-693 - Protection Mechanism Failure | Windows Virtualization-Based Security (VBS) Enclave | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47971 | CWE-126 - Buffer Over-read | Virtual Hard Disk (VHDX) | According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47972 | CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') | Microsoft Input Method Editor (IME) | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. According to the CVSS metric, user interaction is required (UI:R) and privileges required is low (PR:L). What does that mean for this vulnerability? An authorized attacker must send the user a malicious file and convince the user to open it. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited the vulnerability could elevate from a low integrity level up to a medium integrity level. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? In this case, successful exploitation of this vulnerability could allow an attacker to perform remote code execution resulting in a Sandbox escape in the imebroker COM (Component Object Model) object. |
| CVE-2025-47973 | CWE-126 - Buffer Over-read | Virtual Hard Disk (VHDX) | According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47975 | CWE-415 - Double Free | Windows SSDP Service | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain administrator privileges. |
| CVE-2025-47976 | CWE-416 - Use After Free | Windows SSDP Service | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47980 | CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor | Windows Imaging Component | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. |
| CVE-2025-47981 | CWE-122 - Heap-based Buffer Overflow | Windows SPNEGO Extended Negotiation | How could an attacker exploit the vulnerability? An attacker could exploit this vulnerability by sending a malicious message to the server, potentially leading to remote code execution. What is SPNEGO Extended Negotiation? The SPNEGO Extended Negotiation Security Mechanism (NEGOEX) extends Simple and Protected GSS-API Negotiation Mechanism (SPNEGO) described in [RFC4178]. Please see SPNEGO Overview (https://docs.microsoft.com/en-us/op...s-negoex/77c795cf-e522-4678-b0f1-2063c5c0561c) for more information. |
| CVE-2025-47982 | CWE-20 - Improper Input Validation CWE-822 - Untrusted Pointer Dereference | Windows Storage VSP Driver | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47984 | CWE-693 - Protection Mechanism Failure | Windows GDI | What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is sensitive information. |
| CVE-2025-47985 | CWE-822 - Untrusted Pointer Dereference | Windows Event Tracing | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47986 | CWE-416 - Use After Free | Universal Print Management Service | According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? This vulnerability could lead to a contained execution environment escape. Please refer to AppContainer Isolation (https://learn.microsoft.com/en-us/windows/win32/secauthz/appcontainer-isolation) for more information. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. How could an attacker exploit this vulnerability? An authenticated attacker could send a specially crafted file to a shared printer. This could result in arbitrary code execution on the system that is sharing the printer. |
| CVE-2025-47987 | CWE-122 - Heap-based Buffer Overflow CWE-190 - Integer Overflow or Wraparound | Windows Cred SSProvider Protocol | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47991 | CWE-416 - Use After Free | Microsoft Input Method Editor (IME) | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited the vulnerability could elevate from a low integrity level up to a medium integrity level. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? In this case, successful exploitation of this vulnerability could allow an attacker to perform remote code execution resulting in a Sandbox escape in the imebroker COM (Component Object Model) object. |
| CVE-2025-47996 | CWE-191 - Integer Underflow (Wrap or Wraparound) CWE-125 - Out-of-bounds Read | Windows MBT Transport driver | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-47999 | CWE-820 - Missing Synchronization | Role: Windows Hyper-V | According to the CVSS metric, the attack vector is adjacent (AV:A). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires that an attacker will need to first gain access to the restricted network before running an attack. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? Successful exploitation of this vulnerability could allow a Hyper-V guest to affect the functionality of the Hyper-V host. |
| CVE-2025-48000 | CWE-416 - Use After Free CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') | Windows Connected Devices Platform Service | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker could use this vulnerability to elevate privileges from Medium Integrity Level to Local Service. |
| CVE-2025-48001 | CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition | Windows BitLocker | What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. |
| CVE-2025-48003 | CWE-693 - Protection Mechanism Failure | Windows BitLocker | What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. |
| CVE-2025-48799 | CWE-59 - Improper Link Resolution Before File Access ('Link Following') | Windows Update Service | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could create, modify, or delete files in the security context of the "NT AUTHORITY\SYSTEM" account. |
| CVE-2025-48800 | CWE-693 - Protection Mechanism Failure | Windows BitLocker | What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. |
| CVE-2025-48802 | CWE-295 - Improper Certificate Validation | Windows SMB | |
| CVE-2025-48803 | CWE-353 - Missing Support for Integrity Check | Windows Virtualization-Based Security (VBS) Enclave | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain Virtual Trust Level 1 (VTL1) privileges. |
| CVE-2025-48804 | CWE-349 - Acceptance of Extraneous Untrusted Data With Trusted Data | Windows BitLocker | What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. How could an attacker exploit this vulnerability? An attacker could exploit this vulnerability by loading a WinRE.wim file while the OS volume is unlocked, granting access to BitLocker encrypted data. **Are there any further actions I need to take to be protected from this boot manager rollback vulnerability?" Boot manager Secure Version Number/SVN has been incremented and optional Bootmgr SVN revision DBXUpdate has been included in updates released on or after July 9, 2024 security update. Refer to [How to manage the Windows Boot Manager revocations for Secure Boot changes associated with CVE-2023-24932[(https://support.microsoft.com/en-us...23-24932-41a975df-beb2-40c1-99a3-b3ff139f832d) for guidance on how to apply these revocations to get full protection from boot manager rollback vulnerabilities. |
| CVE-2025-48805 | CWE-122 - Heap-based Buffer Overflow | Microsoft MPEG-2 Video Extension | According to the CVSS metric, the attack vector is local (AV:L). Why does the CVE title indicate that this is a remote code execution? The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally. This means an attacker or victim needs to execute code from the local machine to exploit the vulnerability. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. |
| CVE-2025-48806 | CWE-416 - Use After Free | Microsoft MPEG-2 Video Extension | According to the CVSS metric, the attack vector is local (AV:L). Why does the CVE title indicate that this is a remote code execution? The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally. This means an attacker or victim needs to execute code from the local machine to exploit the vulnerability. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. |
| CVE-2025-48808 | CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor | Windows Kernel | What type of information could be disclosed by this vulnerability? Exploiting this vulnerability could allow the disclosure of certain memory address within kernel space. Knowing the exact location of kernel memory could be potentially leveraged by an attacker for other malicious activities. |
| CVE-2025-48811 | CWE-353 - Missing Support for Integrity Check | Windows Virtualization-Based Security (VBS) Enclave | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain Virtual Trust Level 1 (VTL1) privileges. |
| CVE-2025-48814 | CWE-306 - Missing Authentication for Critical Function | Windows Remote Desktop Licensing Service | What security feature is being bypassed? An attacker with a machine-in-the-middle (MitM) position who successfully exploited this vulnerability could bypass the certificate validation performed when a targeted user connects to a trusted server. |
| CVE-2025-48815 | CWE-843 - Access of Resource Using Incompatible Type ('Type Confusion') | Windows SSDP Service | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. |
| CVE-2025-48816 | CWE-190 - Integer Overflow or Wraparound CWE-125 - Out-of-bounds Read | HID class driver | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain specific limited SYSTEM privileges. |
| CVE-2025-48817 | CWE-23 - Relative Path Traversal CWE-284 - Improper Access Control | Remote Desktop Client | According to the CVSS metric, the attack vector is network (AV:N) and the user interaction is required (UI:R). What is the target context of the remote code execution? This attack requires an admin user on the client to connect to a malicious server, and that could allow the attacker to gain code execution on the client. How could an attacker exploit this vulnerability? In the case of a Remote Desktop connection, an attacker with control of a Remote Desktop Server could trigger a remote code execution (RCE) on the RDP client machine when a victim connects to the attacker's server with the vulnerable Remote Desktop Client. |
| CVE-2025-48818 | CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition | Windows BitLocker | What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. |
| CVE-2025-48819 | CWE-591 - Sensitive Data Storage in Improperly Locked Memory | Windows Universal Plug and Play (UPnP) Device Host | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, the attack vector is adjacent (AV:A). What does that mean for this vulnerability? An authenticated attacker could exploit this vulnerability with LAN access. |
| CVE-2025-48820 | CWE-59 - Improper Link Resolution Before File Access ('Link Following') | Windows AppX Deployment Service | What privileges could be gained by an attacker who successfully exploited this vulnerability? An authenticated attacker would be able to delete targeted files on a system which could result in them gaining SYSTEM privileges. |
| CVE-2025-48821 | CWE-416 - Use After Free | Windows Universal Plug and Play (UPnP) Device Host | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, the attack vector is adjacent (AV:A). What does that mean for this vulnerability? An authenticated attacker could exploit this vulnerability with LAN access. |
| CVE-2025-48822 | CWE-125 - Out-of-bounds Read | Role: Windows Hyper-V | According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? An exploited vulnerability can affect resources beyond the security scope managed by the security authority of the vulnerable component. In this case, the vulnerable component and the impacted component are different and managed by different security authorities. According to the CVSS metric, user interaction is required (UI:R). What interaction would the user have to do? A user needs to be tricked into importing an INF file. |
| CVE-2025-48823 | Windows Cryptographic Services | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability To exploit this vulnerability, an attacker would need to target an application by persisting encrypted secrets that are using specific old cryptography and Windows APIs. What type of information could be disclosed by this vulnerability If the attacker has both the ability to modify the encrypted secret where it is stored and to observe the precise timing for the secret being decrypted by the application, the attacker could infer the original secret across many decryption attempts. | |
| CVE-2025-49658 | CWE-125 - Out-of-bounds Read | Windows TDX.sys | What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of stack memory. |
| CVE-2025-49659 | CWE-126 - Buffer Over-read | Windows TDX.sys | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49660 | CWE-416 - Use After Free | Windows Event Tracing | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49661 | CWE-822 - Untrusted Pointer Dereference | Windows Ancillary Function Driver for WinSock | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49664 | CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor | Windows User-Mode Driver Framework Host | What type of information could be disclosed by this vulnerability? Exploiting this vulnerability could allow the disclosure of certain memory address within kernel space. Knowing the exact location of kernel memory could be potentially leveraged by an attacker for other malicious activities. |
| CVE-2025-49665 | CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') CWE-416 - Use After Free | Workspace Broker | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. |
| CVE-2025-49667 | CWE-415 - Double Free | Windows Win32K - ICOMP | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49675 | CWE-416 - Use After Free | Kernel Streaming WOW Thunk Service Driver | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49678 | CWE-476 - NULL Pointer Dereference CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') | Windows NTFS | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49679 | CWE-197 - Numeric Truncation Error | Windows Shell | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49680 | CWE-59 - Improper Link Resolution Before File Access ('Link Following') | Windows Performance Recorder | According to the CVSS metric, user interaction is required (UI:R) and privileges required is Low (PR:L). What does that mean for this vulnerability? Exploitation of this attack requires a local attacker to create arbitrary directories. User interaction is necessary as the attacker relies on an Administrator to run wprui.exe for the first time. |
| CVE-2025-49682 | CWE-416 - Use After Free | Windows Media | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, user interaction is required (UI:R) and privileges required is Low (PR:L). What does that mean for this vulnerability An authorized attacker with privileges could send controlled inputs to exploit this vulnerability. User interaction is required because the vulnerable function is typically triggered through a diagnostic workflow, such as launching a video troubleshooting tool or initiating a certificate validation process. These actions often involve user-initiated steps like opening a UI or selecting a monitor. |
| CVE-2025-49683 | CWE-190 - Integer Overflow or Wraparound CWE-122 - Heap-based Buffer Overflow | Virtual Hard Disk (VHDX) | According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. Why could an attacker achieve remote code execution on affected versions of Window Server 2008, but only cause denial of service on systems running Window Server 2008 R2 or newer versions of Windows? In Windows 7 and newer, an existing mechanism prevents an attacker from achieving remote code execution. They could only use this vulnerability to cause denial of service. |
| CVE-2025-49684 | CWE-126 - Buffer Over-read | Storage Port Driver | What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is a small amount of kernel memory which could be leaked back to the attacker. |
| CVE-2025-49685 | CWE-416 - Use After Free | Microsoft Windows Search Component | How could an attacker exploit this vulnerability? To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system. According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? For an attacker to exploit this vulnerability, they would need to have knowledge of a specific operation that triggers a memory allocation failure, specifically a use after free. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49686 | CWE-476 - NULL Pointer Dereference | Windows TCP/IP | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49687 | CWE-125 - Out-of-bounds Read | Microsoft Input Method Editor (IME) | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker could use this vulnerability to elevate privileges from a Low Integrity Level in a contained ("sandboxed") execution environment to a Medium Integrity Level or a High Integrity Level. Please refer to AppContainer isolation (https://learn.microsoft.com/en-us/windows/win32/secauthz/appcontainer-isolation) and Mandatory Integrity Control (https://learn.microsoft.com/en-us/windows/win32/secauthz/mandatory-integrity-control) for more information. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? This vulnerability could lead to a contained execution environment escape. Please refer to AppContainer Isolation (https://learn.microsoft.com/en-us/windows/win32/secauthz/appcontainer-isolation) for more information. How could an attacker exploit this vulnerability? To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system. |
| CVE-2025-49689 | CWE-190 - Integer Overflow or Wraparound CWE-125 - Out-of-bounds Read CWE-822 - Untrusted Pointer Dereference | Virtual Hard Disk (VHDX) | According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49690 | CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') CWE-415 - Double Free | Capability Access Management Service (camsvc) | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49691 | CWE-122 - Heap-based Buffer Overflow | Windows Media | How could an attacker exploit this vulnerability? An unauthenticated attacker could project to a vulnerable system on the same wireless network that was configured to allow "Projecting to this PC" and marked as "Available Everywhere". This is not a default configuration. According to the CVSS metric, user interaction is required (UI:R) and privileges required are none (PR:N). What does that mean for this vulnerability? An unauthorized attacker must wait for a user to initiate a connection. |
| CVE-2025-49693 | CWE-415 - Double Free | Microsoft Brokering File System | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49721 | CWE-122 - Heap-based Buffer Overflow | Windows Fast FAT Driver | According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49722 | CWE-400 - Uncontrolled Resource Consumption | Windows Print Spooler Components | According to the CVSS score, the attack vector is adjacent (AV:A). What does this mean for this vulnerability? This attack is limited to systems connected to the same network segment as the attacker. The attack cannot be performed across multiple networks (for example, a WAN) and would be limited to systems on the same network switch or virtual network. |
| CVE-2025-49723 | CWE-862 - Missing Authorization | Windows StateRepository API | According to the CVSS metric, successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? In this case, a successful attack could be performed from a low privilege AppContainer (https://docs.microsoft.com/windows/win32/secauthz/appcontainer-isolation) . The attacker could elevate their privileges and execute code or access resources at a higher integrity level than that of the AppContainer execution environment. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker would only be able to delete targeted files on a system. They would not gain privileges to view or modify file contents. How could an attacker exploit this vulnerability? An attacker could exploit this vulnerability by leveraging a function that lacks proper privilege checks to delete items in a specific table. This allows the attacker to escape the sandbox and delete entries belonging to other users. |
| CVE-2025-49724 | CWE-416 - Use After Free | Windows Connected Devices Platform Service | How could an attacker exploit the vulnerability? To exploit this vulnerability, an remote unauthenticated attacker would need to send specially crafted traffic to a system with the "Nearby Sharing" feature enabled and convince a user to take specifc actions. |
| CVE-2025-49725 | CWE-416 - Use After Free | Windows Notification | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. |
| CVE-2025-49726 | CWE-416 - Use After Free | Windows Notification | What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. |
| CVE-2025-49727 | CWE-122 - Heap-based Buffer Overflow | Windows Win32K - GRFX | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49730 | CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition CWE-122 - Heap-based Buffer Overflow | Microsoft Windows QoS scheduler | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. |
| CVE-2025-49732 | CWE-122 - Heap-based Buffer Overflow | Microsoft Graphics Component | What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, the attack vector is local (AV:L). What does this mean for this vulnerability? The attacker would have to be an authenticated user logged on to the vulnerable system to be able to exploit this vulnerability. |
| CVE-2025-49733 | CWE-416 - Use After Free | Windows Win32K - ICOMP | What privileges could be gained by an attacker who successfully exploited the vulnerability? A local, authenticated attacker could gain elevated local system or administrator privileges through a vulnerability in the Win32k.sys driver. |
| CVE-2025-49740 | CWE-693 - Protection Mechanism Failure | Windows SmartScreen | What kind of security feature could be bypassed by successfully exploiting this vulnerability? An attacker who successfully exploited the vulnerability could evade Mark of the Web (MOTW) defenses. How could an attacker exploit this vulnerability? To exploit this security feature bypass vulnerability, an attacker would need to convince a user to launch malicious files using a launcher application that requests that no UI be shown. According to the CVSS metric, user interaction is required (UI:R). What interaction would the user have to do? A user needs to be tricked into running malicious files. |
| CVE-2025-49742 | CWE-190 - Integer Overflow or Wraparound CWE-122 - Heap-based Buffer Overflow | Microsoft Graphics Component | According to the CVSS metric, the attack vector is local (AV:L). Why does the CVE title indicate that this is a remote code execution? The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally. This means an attacker or victim needs to execute code from the local machine to exploit the vulnerability. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. |
| CVE-2025-49744 | CWE-122 - Heap-based Buffer Overflow CWE-191 - Integer Underflow (Wrap or Wraparound) CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') | Microsoft Graphics Component | According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? To successfully exploit this vulnerability, an attacker would need to gain elevated privileges enabling them to perform file operations in directories they would not normally be able to access or perform. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain specific limited SYSTEM privileges. |
| CVE-2025-49760 | CWE-73 - External Control of File Name or Path | Windows Storage | According to the CVSS metric, user interaction is required (UI:R) and privileges required is Low (PR:L). What does that mean for this vulnerability? An authorized attacker with low privileges creates a scheduled task that is set to run when a user logs on and spoofs interfaces that belong to many services so the victim can connect to the attacker's server instead of the original. According to the CVSS metrics, successful exploitation of this vulnerability could lead to some loss of confidentiality (C:L) but have no effect on integrity (I:N) or on availability (A:N). What does that mean for this vulnerability? An attacker who successfully exploited the vulnerability could view some sensitive information (Confidentiality) but not all resources within the impacted component may be divulged to the attacker. The attacker cannot make changes to disclosed information (Integrity) or limit access to the resource (Availability). |
* Some data might be lost because of mapping incompletion
Последнее редактирование:
Bitlocker, Bitlocker, Bitlocker, Bitlocker...Подъехали обновы за июль. Обновленная база - http://**************************************************************/d/4bepAxetDoEhVJTnoAzni2
Заменить в папке /data.
Patch Report for 2025-07-08
Top 10 CWEs
CWE Count CWE-416 - Use After Free 13 CWE-122 - Heap-based Buffer Overflow 6 CWE-693 - Protection Mechanism Failure 5 CWE-126 - Buffer Over-read 4 CWE-59 - Improper Link Resolution Before File Access ('Link Following') 3 CWE-415 - Double Free 3 CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor 3 CWE-125 - Out-of-bounds Read 3 3 CWE-822 - Untrusted Pointer Dereference 2
High-Risk Vulnerabilities
CVE CWE Severity Public Exploited Component CVE-2025-36350 Critical No No AMD Store Queue CVE-2025-36357 Critical No No AMD L1 Data Queue CVE-2025-47980 CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor Critical No No Windows Imaging Component CVE-2025-47981 CWE-122 - Heap-based Buffer Overflow Critical No No Windows SPNEGO Extended Negotiation CVE-2025-48822 CWE-125 - Out-of-bounds Read Critical No No Role: Windows Hyper-V CVE-2025-33054 CWE-357 - Insufficient UI Warning of Dangerous Operations Important No No Remote Desktop Client CVE-2025-47159 CWE-693 - Protection Mechanism Failure Important No No Windows Virtualization-Based Security (VBS) Enclave CVE-2025-47971 CWE-126 - Buffer Over-read Important No No Virtual Hard Disk (VHDX)
Known Associated CVEs
Component Binary CVEs Kernel Streaming WOW Thunk Service Driver ksthunk.sys CVE-2025-49675 Windows Ancillary Function Driver for WinSock afd.sys CVE-2025-49661 Windows BitLocker fvevol.sys CVE-2025-48001, CVE-2025-48003, CVE-2025-48800, CVE-2025-48818, CVE-2025-48804 Windows Fast FAT Driver fastfat.sys CVE-2025-49721 Windows Kernel ntoskrnl.exe CVE-2025-48808 Windows Storage VSP Driver storvsp.sys CVE-2025-47982 Windows TCP/IP tcpip.sys CVE-2025-49686
Function Changes by Binary
Binary Patched Added Deleted afd.sys (10.0.22621.5624) 1 2 0 ahcache.sys (10.0.22621.5547) 0 0 0 appid.sys (10.0.22621.5547) 0 0 0 applockerfltr.sys (10.0.22621.5547) 0 0 0 bootmgfw.efi (10.0.22621.5624) 1 0 0 bthenum.sys (10.0.22621.5624) 0 0 0 bthmini.sys (10.0.22621.5624) 0 0 0 bthport.sys (10.0.22621.5624) 0 0 0 bthusb.sys (10.0.22621.5624) 0 0 0 clfs.sys (10.0.22621.5547) 2 0 2 clipsp.sys (10.0.22621.5547) 105 13 14 dumpfve.sys (10.0.22621.5624) 0 0 0 dxgkrnl.sys (10.0.22621.5547) 3 0 7 dxgmms1.sys (10.0.22621.5547) 0 0 0 dxgmms2.sys (10.0.22621.5547) 0 0 0 exfat.sys (10.0.22621.5624) 4 0 0 fastfat.sys (10.0.22621.5624) 12 2 0 fvevol.sys (10.0.22621.5624) 0 0 0 fwpkclnt.sys (10.0.22621.5624) 0 0 0 hdaudio.sys (10.0.22621.5624) 0 0 0 hvax64.exe (10.0.22621.5624) 60 0 0 hvix64.exe (10.0.22621.5624) 27 0 0 hvloader.dll (10.0.22621.5624) 0 0 0 kdhvcom.dll (10.0.22621.5624) 0 0 0 ks.sys (10.0.22621.5547) 3 0 8 ksecpkg.sys (10.0.22621.5547) 0 0 0 ksthunk.sys (10.0.22621.5624) 8 0 4 mrxsmb.sys (10.0.22621.5624) 4 5 0 mskssrv.sys (10.0.22621.5547) 0 0 0 netio.sys (10.0.22621.5624) 0 0 0 ntfs.sys (10.0.22621.5624) 13 0 6 ntoskrnl.exe (10.0.22621.5624) 218 25 0 pci.sys (10.0.22621.5547) 0 0 0 processr.sys (10.0.22621.5624) 4 1 0 rdpvideominiport.sys (10.0.22621.5624) 0 0 0 refs.sys (10.0.22621.5547) 13 0 2 srv.sys (10.0.22621.5624) 0 0 0 srv2.sys (10.0.22621.5624) 0 0 0 srvnet.sys (10.0.22621.5624) 10 3 0 storport.sys (10.0.22621.5624) 2 2 0 storvsp.sys (10.0.22621.5624) 0 0 0 tcpip.sys (10.0.22621.5624) 0 0 0 tcpipreg.sys (10.0.22621.5624) 0 0 0 usbvideo.sys (10.0.22621.5547) 24 0 7 vkrnlintvsp.sys (10.0.22621.5547) 0 0 0 vmsproxy.sys (10.0.22621.5624) 0 0 0 vmsproxyhnic.sys (10.0.22621.5624) 0 0 0 vmswitch.sys (10.0.22621.5624) 0 0 0 win32k.sys (10.0.22621.5624) 0 0 0 win32kbase.sys (10.0.22621.5624) 24 3 0 win32kfull.sys (10.0.22621.5624) 42 10 0 winload.exe (10.0.22621.5624) 2 0 0 xboxgip.sys (10.0.22621.5547) 0 0 0
All CVE Details
CVE CWE Tag Details CVE-2025-33054 CWE-357 - Insufficient UI Warning of Dangerous Operations Remote Desktop Client According to the CVSS metric, user interaction is required (UI:R). What does that mean for this vulnerability? An attacker must trick the user into interacting with a spoofed WebAuthn prompt and entering their credentials. According to the CVSS metric, user interaction is required (UI:R) and privileges required are none (PR:N). What does that mean for this vulnerability? An unauthorized attacker must wait for a user to initiate a connection. CVE-2025-36350 AMD Store Queue Why is this AMD CVE included in the Security Update Guide? The vulnerability assigned to this CVE is in certain processor models offered by AMD. The mitigation for this vulnerability requires a Windows update. This CVE is being documented in the Security Update Guide to announce that the latest builds of Windows enable the mitigation and provide protection against the vulnerability. Please see the following for more information: AMD-SB-7029 (https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7029.html) CVE-2025-36357 AMD L1 Data Queue Why is this AMD CVE included in the Security Update Guide? The vulnerability assigned to this CVE is in certain processor models offered by AMD. The mitigation for this vulnerability requires a Windows update. This CVE is being documented in the Security Update Guide to announce that the latest builds of Windows enable the mitigation and provide protection against the vulnerability. Please see the following for more information: AMD-SB-7029 (https://www.amd.com/en/resources/product-security/bulletin/amd-sb-7029.html) CVE-2025-47159 CWE-693 - Protection Mechanism Failure Windows Virtualization-Based Security (VBS) Enclave What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47971 CWE-126 - Buffer Over-read Virtual Hard Disk (VHDX) According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47972 CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') Microsoft Input Method Editor (IME) According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. According to the CVSS metric, user interaction is required (UI:R) and privileges required is low (PR:L). What does that mean for this vulnerability? An authorized attacker must send the user a malicious file and convince the user to open it. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited the vulnerability could elevate from a low integrity level up to a medium integrity level. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? In this case, successful exploitation of this vulnerability could allow an attacker to perform remote code execution resulting in a Sandbox escape in the imebroker COM (Component Object Model) object. CVE-2025-47973 CWE-126 - Buffer Over-read Virtual Hard Disk (VHDX) According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47975 CWE-415 - Double Free Windows SSDP Service According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain administrator privileges. CVE-2025-47976 CWE-416 - Use After Free Windows SSDP Service What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47980 CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor Windows Imaging Component What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of heap memory. CVE-2025-47981 CWE-122 - Heap-based Buffer Overflow Windows SPNEGO Extended Negotiation How could an attacker exploit the vulnerability? An attacker could exploit this vulnerability by sending a malicious message to the server, potentially leading to remote code execution. What is SPNEGO Extended Negotiation? The SPNEGO Extended Negotiation Security Mechanism (NEGOEX) extends Simple and Protected GSS-API Negotiation Mechanism (SPNEGO) described in [RFC4178]. Please see SPNEGO Overview (https://docs.microsoft.com/en-us/op...s-negoex/77c795cf-e522-4678-b0f1-2063c5c0561c) for more information. CVE-2025-47982 CWE-20 - Improper Input Validation CWE-822 - Untrusted Pointer Dereference Windows Storage VSP Driver What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47984 CWE-693 - Protection Mechanism Failure Windows GDI What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is sensitive information. CVE-2025-47985 CWE-822 - Untrusted Pointer Dereference Windows Event Tracing What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47986 CWE-416 - Use After Free Universal Print Management Service According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? This vulnerability could lead to a contained execution environment escape. Please refer to AppContainer Isolation (https://learn.microsoft.com/en-us/windows/win32/secauthz/appcontainer-isolation) for more information. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. How could an attacker exploit this vulnerability? An authenticated attacker could send a specially crafted file to a shared printer. This could result in arbitrary code execution on the system that is sharing the printer. CVE-2025-47987 CWE-122 - Heap-based Buffer Overflow CWE-190 - Integer Overflow or Wraparound Windows Cred SSProvider Protocol What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47991 CWE-416 - Use After Free Microsoft Input Method Editor (IME) According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited the vulnerability could elevate from a low integrity level up to a medium integrity level. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? In this case, successful exploitation of this vulnerability could allow an attacker to perform remote code execution resulting in a Sandbox escape in the imebroker COM (Component Object Model) object. CVE-2025-47996 CWE-191 - Integer Underflow (Wrap or Wraparound) CWE-125 - Out-of-bounds Read Windows MBT Transport driver What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-47999 CWE-820 - Missing Synchronization Role: Windows Hyper-V According to the CVSS metric, the attack vector is adjacent (AV:A). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires that an attacker will need to first gain access to the restricted network before running an attack. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? Successful exploitation of this vulnerability could allow a Hyper-V guest to affect the functionality of the Hyper-V host. CVE-2025-48000 CWE-416 - Use After Free CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') Windows Connected Devices Platform Service What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker could use this vulnerability to elevate privileges from Medium Integrity Level to Local Service. CVE-2025-48001 CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition Windows BitLocker What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. CVE-2025-48003 CWE-693 - Protection Mechanism Failure Windows BitLocker What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. CVE-2025-48799 CWE-59 - Improper Link Resolution Before File Access ('Link Following') Windows Update Service What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could create, modify, or delete files in the security context of the "NT AUTHORITY\SYSTEM" account. CVE-2025-48800 CWE-693 - Protection Mechanism Failure Windows BitLocker What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. CVE-2025-48802 CWE-295 - Improper Certificate Validation Windows SMB CVE-2025-48803 CWE-353 - Missing Support for Integrity Check Windows Virtualization-Based Security (VBS) Enclave What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain Virtual Trust Level 1 (VTL1) privileges. CVE-2025-48804 CWE-349 - Acceptance of Extraneous Untrusted Data With Trusted Data Windows BitLocker What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. How could an attacker exploit this vulnerability? An attacker could exploit this vulnerability by loading a WinRE.wim file while the OS volume is unlocked, granting access to BitLocker encrypted data. **Are there any further actions I need to take to be protected from this boot manager rollback vulnerability?" Boot manager Secure Version Number/SVN has been incremented and optional Bootmgr SVN revision DBXUpdate has been included in updates released on or after July 9, 2024 security update. Refer to [How to manage the Windows Boot Manager revocations for Secure Boot changes associated with CVE-2023-24932[(https://support.microsoft.com/en-us...23-24932-41a975df-beb2-40c1-99a3-b3ff139f832d) for guidance on how to apply these revocations to get full protection from boot manager rollback vulnerabilities. CVE-2025-48805 CWE-122 - Heap-based Buffer Overflow Microsoft MPEG-2 Video Extension According to the CVSS metric, the attack vector is local (AV:L). Why does the CVE title indicate that this is a remote code execution? The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally. This means an attacker or victim needs to execute code from the local machine to exploit the vulnerability. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. CVE-2025-48806 CWE-416 - Use After Free Microsoft MPEG-2 Video Extension According to the CVSS metric, the attack vector is local (AV:L). Why does the CVE title indicate that this is a remote code execution? The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally. This means an attacker or victim needs to execute code from the local machine to exploit the vulnerability. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. CVE-2025-48808 CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor Windows Kernel What type of information could be disclosed by this vulnerability? Exploiting this vulnerability could allow the disclosure of certain memory address within kernel space. Knowing the exact location of kernel memory could be potentially leveraged by an attacker for other malicious activities. CVE-2025-48811 CWE-353 - Missing Support for Integrity Check Windows Virtualization-Based Security (VBS) Enclave What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain Virtual Trust Level 1 (VTL1) privileges. CVE-2025-48814 CWE-306 - Missing Authentication for Critical Function Windows Remote Desktop Licensing Service What security feature is being bypassed? An attacker with a machine-in-the-middle (MitM) position who successfully exploited this vulnerability could bypass the certificate validation performed when a targeted user connects to a trusted server. CVE-2025-48815 CWE-843 - Access of Resource Using Incompatible Type ('Type Confusion') Windows SSDP Service What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. CVE-2025-48816 CWE-190 - Integer Overflow or Wraparound CWE-125 - Out-of-bounds Read HID class driver What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain specific limited SYSTEM privileges. CVE-2025-48817 CWE-23 - Relative Path Traversal CWE-284 - Improper Access Control Remote Desktop Client According to the CVSS metric, the attack vector is network (AV:N) and the user interaction is required (UI:R). What is the target context of the remote code execution? This attack requires an admin user on the client to connect to a malicious server, and that could allow the attacker to gain code execution on the client. How could an attacker exploit this vulnerability? In the case of a Remote Desktop connection, an attacker with control of a Remote Desktop Server could trigger a remote code execution (RCE) on the RDP client machine when a victim connects to the attacker's server with the vulnerable Remote Desktop Client. CVE-2025-48818 CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition Windows BitLocker What kind of security feature could be bypassed by successfully exploiting this vulnerability? A successful attacker could bypass the BitLocker Device Encryption feature on the system storage device. An attacker with physical access to the target could exploit this vulnerability to gain access to encrypted data. CVE-2025-48819 CWE-591 - Sensitive Data Storage in Improperly Locked Memory Windows Universal Plug and Play (UPnP) Device Host According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, the attack vector is adjacent (AV:A). What does that mean for this vulnerability? An authenticated attacker could exploit this vulnerability with LAN access. CVE-2025-48820 CWE-59 - Improper Link Resolution Before File Access ('Link Following') Windows AppX Deployment Service What privileges could be gained by an attacker who successfully exploited this vulnerability? An authenticated attacker would be able to delete targeted files on a system which could result in them gaining SYSTEM privileges. CVE-2025-48821 CWE-416 - Use After Free Windows Universal Plug and Play (UPnP) Device Host According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, the attack vector is adjacent (AV:A). What does that mean for this vulnerability? An authenticated attacker could exploit this vulnerability with LAN access. CVE-2025-48822 CWE-125 - Out-of-bounds Read Role: Windows Hyper-V According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? An exploited vulnerability can affect resources beyond the security scope managed by the security authority of the vulnerable component. In this case, the vulnerable component and the impacted component are different and managed by different security authorities. According to the CVSS metric, user interaction is required (UI:R). What interaction would the user have to do? A user needs to be tricked into importing an INF file. CVE-2025-48823 Windows Cryptographic Services According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability To exploit this vulnerability, an attacker would need to target an application by persisting encrypted secrets that are using specific old cryptography and Windows APIs. What type of information could be disclosed by this vulnerability If the attacker has both the ability to modify the encrypted secret where it is stored and to observe the precise timing for the secret being decrypted by the application, the attacker could infer the original secret across many decryption attempts. CVE-2025-49658 CWE-125 - Out-of-bounds Read Windows TDX.sys What type of information could be disclosed by this vulnerability? An attacker who successfully exploited this vulnerability could potentially read small portions of stack memory. CVE-2025-49659 CWE-126 - Buffer Over-read Windows TDX.sys What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49660 CWE-416 - Use After Free Windows Event Tracing What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49661 CWE-822 - Untrusted Pointer Dereference Windows Ancillary Function Driver for WinSock What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49664 CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor Windows User-Mode Driver Framework Host What type of information could be disclosed by this vulnerability? Exploiting this vulnerability could allow the disclosure of certain memory address within kernel space. Knowing the exact location of kernel memory could be potentially leveraged by an attacker for other malicious activities. CVE-2025-49665 CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') CWE-416 - Use After Free Workspace Broker What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. CVE-2025-49667 CWE-415 - Double Free Windows Win32K - ICOMP What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49675 CWE-416 - Use After Free Kernel Streaming WOW Thunk Service Driver What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49678 CWE-476 - NULL Pointer Dereference CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') Windows NTFS According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49679 CWE-197 - Numeric Truncation Error Windows Shell What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49680 CWE-59 - Improper Link Resolution Before File Access ('Link Following') Windows Performance Recorder According to the CVSS metric, user interaction is required (UI:R) and privileges required is Low (PR:L). What does that mean for this vulnerability? Exploitation of this attack requires a local attacker to create arbitrary directories. User interaction is necessary as the attacker relies on an Administrator to run wprui.exe for the first time. CVE-2025-49682 CWE-416 - Use After Free Windows Media What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, user interaction is required (UI:R) and privileges required is Low (PR:L). What does that mean for this vulnerability An authorized attacker with privileges could send controlled inputs to exploit this vulnerability. User interaction is required because the vulnerable function is typically triggered through a diagnostic workflow, such as launching a video troubleshooting tool or initiating a certificate validation process. These actions often involve user-initiated steps like opening a UI or selecting a monitor. CVE-2025-49683 CWE-190 - Integer Overflow or Wraparound CWE-122 - Heap-based Buffer Overflow Virtual Hard Disk (VHDX) According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. Why could an attacker achieve remote code execution on affected versions of Window Server 2008, but only cause denial of service on systems running Window Server 2008 R2 or newer versions of Windows? In Windows 7 and newer, an existing mechanism prevents an attacker from achieving remote code execution. They could only use this vulnerability to cause denial of service. CVE-2025-49684 CWE-126 - Buffer Over-read Storage Port Driver What type of information could be disclosed by this vulnerability? The type of information that could be disclosed if an attacker successfully exploited this vulnerability is a small amount of kernel memory which could be leaked back to the attacker. CVE-2025-49685 CWE-416 - Use After Free Microsoft Windows Search Component How could an attacker exploit this vulnerability? To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system. According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? For an attacker to exploit this vulnerability, they would need to have knowledge of a specific operation that triggers a memory allocation failure, specifically a use after free. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49686 CWE-476 - NULL Pointer Dereference Windows TCP/IP What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49687 CWE-125 - Out-of-bounds Read Microsoft Input Method Editor (IME) What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker could use this vulnerability to elevate privileges from a Low Integrity Level in a contained ("sandboxed") execution environment to a Medium Integrity Level or a High Integrity Level. Please refer to AppContainer isolation (https://learn.microsoft.com/en-us/windows/win32/secauthz/appcontainer-isolation) and Mandatory Integrity Control (https://learn.microsoft.com/en-us/windows/win32/secauthz/mandatory-integrity-control) for more information. According to the CVSS metric, a successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? This vulnerability could lead to a contained execution environment escape. Please refer to AppContainer Isolation (https://learn.microsoft.com/en-us/windows/win32/secauthz/appcontainer-isolation) for more information. How could an attacker exploit this vulnerability? To exploit this vulnerability, an attacker would first have to log on to the system. An attacker could then run a specially crafted application that could exploit the vulnerability and take control of an affected system. CVE-2025-49689 CWE-190 - Integer Overflow or Wraparound CWE-125 - Out-of-bounds Read CWE-822 - Untrusted Pointer Dereference Virtual Hard Disk (VHDX) According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49690 CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') CWE-415 - Double Free Capability Access Management Service (camsvc) According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? Successful exploitation of this vulnerability requires an attacker to win a race condition. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49691 CWE-122 - Heap-based Buffer Overflow Windows Media How could an attacker exploit this vulnerability? An unauthenticated attacker could project to a vulnerable system on the same wireless network that was configured to allow "Projecting to this PC" and marked as "Available Everywhere". This is not a default configuration. According to the CVSS metric, user interaction is required (UI:R) and privileges required are none (PR:N). What does that mean for this vulnerability? An unauthorized attacker must wait for a user to initiate a connection. CVE-2025-49693 CWE-415 - Double Free Microsoft Brokering File System What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49721 CWE-122 - Heap-based Buffer Overflow Windows Fast FAT Driver According to the CVSS metric, the attack vector is local (AV:L) while user interaction is required (UI:R). What does that mean for this vulnerability? An attacker can trick a local user on a vulnerable system into mounting a specially crafted VHD that would then trigger the vulnerability. What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49722 CWE-400 - Uncontrolled Resource Consumption Windows Print Spooler Components According to the CVSS score, the attack vector is adjacent (AV:A). What does this mean for this vulnerability? This attack is limited to systems connected to the same network segment as the attacker. The attack cannot be performed across multiple networks (for example, a WAN) and would be limited to systems on the same network switch or virtual network. CVE-2025-49723 CWE-862 - Missing Authorization Windows StateRepository API According to the CVSS metric, successful exploitation could lead to a scope change (S:C). What does this mean for this vulnerability? In this case, a successful attack could be performed from a low privilege AppContainer (https://docs.microsoft.com/windows/win32/secauthz/appcontainer-isolation) . The attacker could elevate their privileges and execute code or access resources at a higher integrity level than that of the AppContainer execution environment. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker would only be able to delete targeted files on a system. They would not gain privileges to view or modify file contents. How could an attacker exploit this vulnerability? An attacker could exploit this vulnerability by leveraging a function that lacks proper privilege checks to delete items in a specific table. This allows the attacker to escape the sandbox and delete entries belonging to other users. CVE-2025-49724 CWE-416 - Use After Free Windows Connected Devices Platform Service How could an attacker exploit the vulnerability? To exploit this vulnerability, an remote unauthenticated attacker would need to send specially crafted traffic to a system with the "Nearby Sharing" feature enabled and convince a user to take specifc actions. CVE-2025-49725 CWE-416 - Use After Free Windows Notification What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. CVE-2025-49726 CWE-416 - Use After Free Windows Notification What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could potentially gain the ability to crash the system by exploiting the use-after-free vulnerability, even as a standard user. CVE-2025-49727 CWE-122 - Heap-based Buffer Overflow Windows Win32K - GRFX What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49730 CWE-367 - Time-of-check Time-of-use (TOCTOU) Race Condition CWE-122 - Heap-based Buffer Overflow Microsoft Windows QoS scheduler What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. CVE-2025-49732 CWE-122 - Heap-based Buffer Overflow Microsoft Graphics Component What privileges could be gained by an attacker who successfully exploited this vulnerability? An attacker who successfully exploited this vulnerability could gain SYSTEM privileges. According to the CVSS metric, the attack vector is local (AV:L). What does this mean for this vulnerability? The attacker would have to be an authenticated user logged on to the vulnerable system to be able to exploit this vulnerability. CVE-2025-49733 CWE-416 - Use After Free Windows Win32K - ICOMP What privileges could be gained by an attacker who successfully exploited the vulnerability? A local, authenticated attacker could gain elevated local system or administrator privileges through a vulnerability in the Win32k.sys driver. CVE-2025-49740 CWE-693 - Protection Mechanism Failure Windows SmartScreen What kind of security feature could be bypassed by successfully exploiting this vulnerability? An attacker who successfully exploited the vulnerability could evade Mark of the Web (MOTW) defenses. How could an attacker exploit this vulnerability? To exploit this security feature bypass vulnerability, an attacker would need to convince a user to launch malicious files using a launcher application that requests that no UI be shown. According to the CVSS metric, user interaction is required (UI:R). What interaction would the user have to do? A user needs to be tricked into running malicious files. CVE-2025-49742 CWE-190 - Integer Overflow or Wraparound CWE-122 - Heap-based Buffer Overflow Microsoft Graphics Component According to the CVSS metric, the attack vector is local (AV:L). Why does the CVE title indicate that this is a remote code execution? The word Remote in the title refers to the location of the attacker. This type of exploit is sometimes referred to as Arbitrary Code Execution (ACE). The attack itself is carried out locally. This means an attacker or victim needs to execute code from the local machine to exploit the vulnerability. According to the CVSS metric, privileges required is low (PR:L). What does that mean for this vulnerability? Any authenticated attacker could trigger this vulnerability. It does not require admin or other elevated privileges. CVE-2025-49744 CWE-122 - Heap-based Buffer Overflow CWE-191 - Integer Underflow (Wrap or Wraparound) CWE-362 - Concurrent Execution using Shared Resource with Improper Synchronization ('Race Condition') Microsoft Graphics Component According to the CVSS metric, the attack complexity is high (AC:H). What does that mean for this vulnerability? To successfully exploit this vulnerability, an attacker would need to gain elevated privileges enabling them to perform file operations in directories they would not normally be able to access or perform. What privileges could be gained by an attacker who successfully exploited the vulnerability? An attacker who successfully exploited this vulnerability could gain specific limited SYSTEM privileges. CVE-2025-49760 CWE-73 - External Control of File Name or Path Windows Storage According to the CVSS metric, user interaction is required (UI:R) and privileges required is Low (PR:L). What does that mean for this vulnerability? An authorized attacker with low privileges creates a scheduled task that is set to run when a user logs on and spoofs interfaces that belong to many services so the victim can connect to the attacker's server instead of the original. According to the CVSS metrics, successful exploitation of this vulnerability could lead to some loss of confidentiality (C:L) but have no effect on integrity (I:N) or on availability (A:N). What does that mean for this vulnerability? An attacker who successfully exploited the vulnerability could view some sensitive information (Confidentiality) but not all resources within the impacted component may be divulged to the attacker. The attacker cannot make changes to disclosed information (Integrity) or limit access to the resource (Availability).
* Some data might be lost because of mapping incompletion
- Автор темы
- Добавить закладку
- #31
Пожалуйста, обратите внимание, что пользователь заблокирован
Продолжаем несмотря ни на что. Здесь описал алгоритм тулзы.

 github.com
github.com
Позже опубликую исходники.

eldiff/eldiff_en.md at main · varwara/eldiff
Simple web-application to view Windows OS patches. Contribute to varwara/eldiff development by creating an account on GitHub.
Позже опубликую исходники.