Пожалуйста, обратите внимание, что пользователь заблокирован
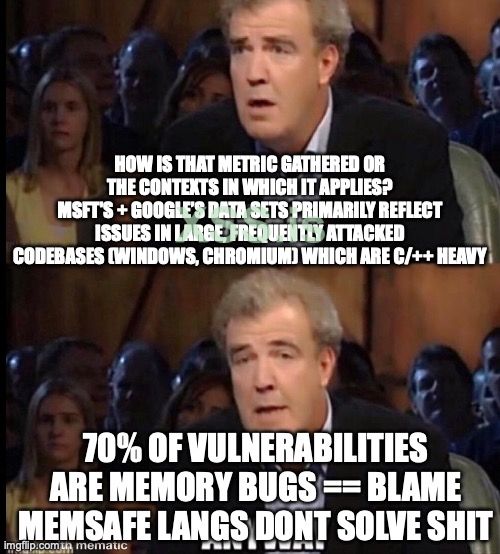
If you listen to all the experts, memory safe languages are the future of cybersecurity. But looking at the modern threat landscape, we see less memory bugs being exploited, even in code written in legacy unsafe languages. Are memory safe languages going to fix all security problems (hint: no)? Are they completely useless (hint: also no)? And what should we expect to see from threat actors going forward?