Пожалуйста, обратите внимание, что пользователь заблокирован
- Цена
- -
- Контакты
- -
hello everyone, i'm programming a c2 in golang, it works very well, and it's multiplatform, windows, linux, freebsd, plan9, macos,
i haven't tested it on macos yet because i don't have a pc with mac,
if anyone wants to help me do tests on macos, welcome, the functions cover all the basics, like system info, download and upload files,
2 methods to execute commands, one using system shells like cmd.exe on windows, and another simply without a shell, also md5sum, change directory, cat command to see the contents of a file and several more commands.
the thing is that i'm thinking of adding modules to it, and i want advice from malware developers with more experience than me, how could i implement modules in memory, the idea was ps, py, dll, exe scripts formats, i will also add a web panel in dark mode, but for now there is no such thing, any advice is welcome
Payload formats:
i haven't tested it on macos yet because i don't have a pc with mac,
if anyone wants to help me do tests on macos, welcome, the functions cover all the basics, like system info, download and upload files,
2 methods to execute commands, one using system shells like cmd.exe on windows, and another simply without a shell, also md5sum, change directory, cat command to see the contents of a file and several more commands.
the thing is that i'm thinking of adding modules to it, and i want advice from malware developers with more experience than me, how could i implement modules in memory, the idea was ps, py, dll, exe scripts formats, i will also add a web panel in dark mode, but for now there is no such thing, any advice is welcome
Payload formats:
Код:
+------------+-----------------+-------------------------------------+--------------+--------+
| Payload Id | Payload Name | Supported Formats | Platform | Arch |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable, 2=shellcode, 4=python | windows | x86 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable, 2=shellcode, 4=python | windows | x64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable, 4=python | windows | arm |
+------------+-----------------+-------------------------------------+--------------+--------+
| 2 | RedLotus_loader | 1=executable | windows | x86 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 2 | RedLotus_loader | 1=executable | windows | x64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable, 4=python | linux | x86 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable, 4=python | linux | x64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | linux | arm64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | linux | arm |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | linux | mips |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | linux | mipsle |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | linux | arm64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | freebsd | x64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | freebsd | arm64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | plan9 | x86 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | plan9 | x64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | macos/darwin | x64 |
+------------+-----------------+-------------------------------------+--------------+--------+
| 1 | RedLotus_client | 1=executable | macos/darwin | arm64 |
+------------+-----------------+-------------------------------------+--------------+--------+
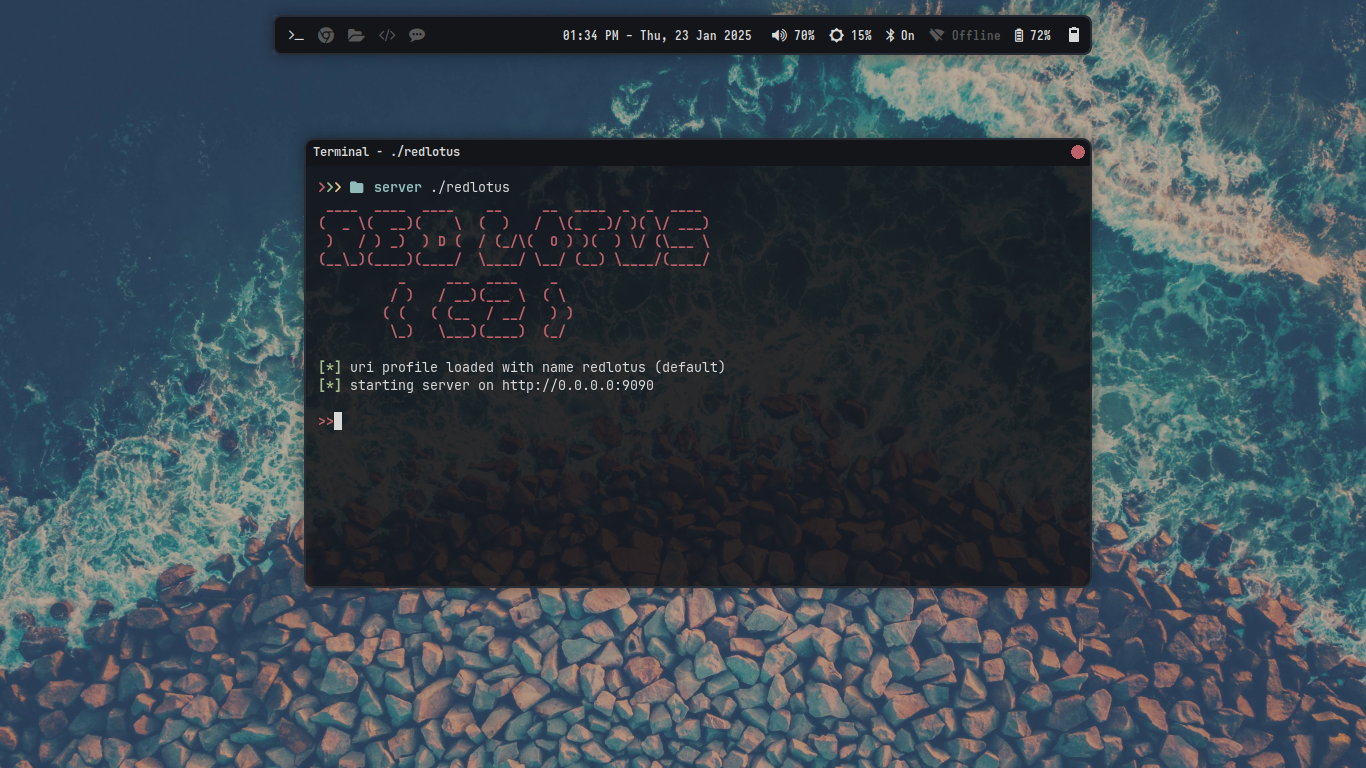
Server cli:
Код:
____ ____ ____ __ __ ____ _ _ ____
( _ \( __)( \ ( ) / \(_ _)/ )( \/ ___)
) / ) _) ) D ( / (_/\( O ) )( ) \/ (\___ \
(__\_)(____)(____/ \____/ \__/ (__) \____/(____/
_ ___ ____ _
/ ) / __)(___ \ ( \
( ( ( (__ / __/ ) )
\_) \___)(____) (_/
Usage of ./redlotus:
-arch string
target arch (x86,x64,arm,arm64,etc) (default "x86")
-build
start the cli in builder mode
-bypass
bypass vm,sandbox,virtual machines, sandbox, etc
-campaignName string
name of the malware spread or attack campaign for spear or apts (default "red lotus")
-format int
payload format (1=executable, 2=shellcode, 3=powershell, 4=python, 5=dll) (default 1)
-gcc-compiler string
gcc (C) compiler command for make dll and other C based payloads (default "gcc")
-icon int
custom icon for the windows payload output 1=excel, 2=word, 3=powepoint, 4=pdf, 5=chrome, 6=edge, 7=firefox
-lang int
funtions obfusction chars language 1=chinese,2=russian,3=english (default 3)
-list-payloads
list payload formats and platforms combinations
-listen string
port for start the http listener (default "9090")
-output string
name of the payload for save output dont extencion need (default "random_name")
-password string
password for the payload (.\backdoor.exe -password 123)
-payload int
payload id for build 1=RedLotus_Client, 2=RedLotus_Loader (default 1)
-persistence
enable persistence for start the agent or payload on startup
-platform string
target platform os (windows/linux/etc) (default "windows")
-port int
builder client (backdoor) port for connect to c2 server (default 9090)
-profile string
uri profile json config dont need .json default (default "redlotus")
-profiles
list available uri profiles
-server string
server ip or domain (127.0.0.1 or www.example.com) (default "127.0.0.1")
-shellcode string
name of the shellcode raw .bin file for encrypt and make loader (default "shellcode.bin")
-ssl-crt string
ssl certificate filename for tls listener (default "redlotus.crt")
-ssl-key string
ssl key pem filename for tls listener (default "redlotus.key")
-transport int
communication transport http=1, https=2 (default 1)