- Цена
- 55
Official Tor Mirror
wdkillerdm2rmoh5fdqkdm4wle7lf2cgmkxdl7yh52c6hxt7khjw3wid.onion
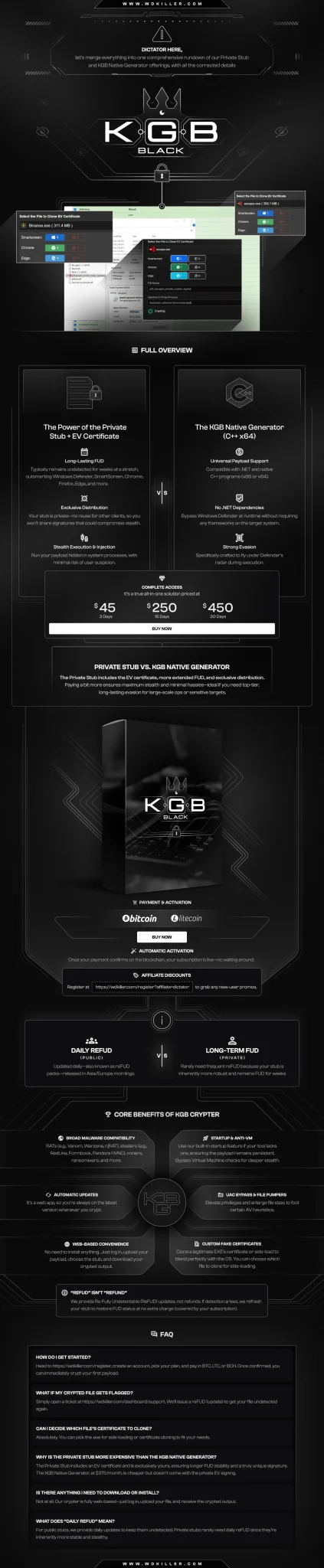
Price: $55 for 3 days.
We are only on TOR now.
Are you tired of your payload getting detected too quickly?
Imagine having your payload stay undetectable for months, bypassing all security warnings, including SmartScreen.
My Promise: BYPASS
 It will bypass Chrome warning, Edge, and Firefox & any other browser warnings.
It will bypass Chrome warning, Edge, and Firefox & any other browser warnings.
 It will bypass Windows SmartScreen warnings.
It will bypass Windows SmartScreen warnings.
With my service, your payload will remain undetectable (FUD) for long time. This premium crypting service ensures your file remains fully undetectable, keeping your operations running smoothly without interruption.
Detection Avoidance:
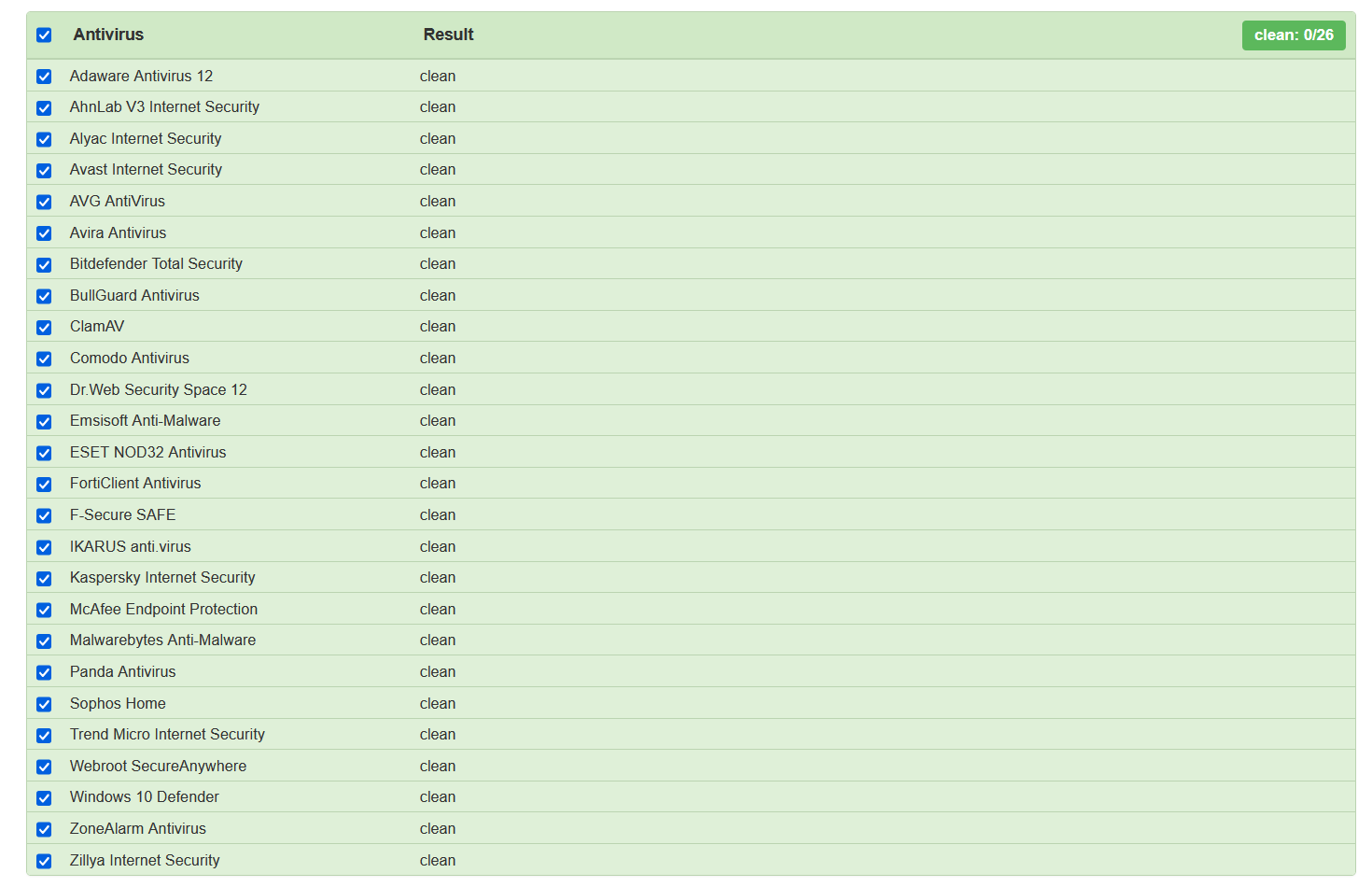
100% No Threats Detected:
Our solution ensures that your payload stays FUD for over 20 days. Typical crypters get detected in 4 hours.
Long-Term FUD Guarantee:
Your file will stay undetectable for an extended period.
Bypassing All Security Measures:
Including SmartScreen, thanks to the EV certificate.
Custom Stub:
Specifically for your payload, ensuring maximum effectiveness.
No Extra Dependencies:
Native output for seamless operation.
I use an EV certificate, which usually costs $5,000 on the black market to sign your .exe, but you won't pay even half of that!
Now, for just $450 per month, enjoy unlimited crypts with our private crypter inside wdkiller.com. No more handmade crypting. Our service now bypasses Windows Defender, SmartScreen, Chrome, Edge, Firefox, and remains fully undetectable (FUD) for many days against Windows Defender.
Contact us on Telegram:
 @WE DON'T HAVE TELEGRAM, ANYONE WHO SAYS TO BE ME ====== SCAMMER
@WE DON'T HAVE TELEGRAM, ANYONE WHO SAYS TO BE ME ====== SCAMMER
Need custom functions?
We tailor the stub to your requirements—add startup if needed, or configure it for stealers without requiring startup.
Our services are compatible with .NET and C++ outputs for both x86 and x64 architectures. Examples of supported tools include RedLine, Origin, Async, Quasar, Venom, XLoader, XWorm, DcRAT, Raccoon, and others.
[size=xx-large]Terms of Use[/size]
Please ensure that all files submitted do not contain any "install," "copy to startup," or "copy to registry" features. These functionalities must be completely clean in the tools provided. If you require startup capabilities to be added, please request this service explicitly.
WARNING:
This program was developed solely for educational purposes and authorized legal penetration testing for companies. It is also intended for individuals seeking to understand how hackers operate in order to better protect themselves. Any use of this tool for illegal activities is strictly prohibited and strongly discouraged.
wdkillerdm2rmoh5fdqkdm4wle7lf2cgmkxdl7yh52c6hxt7khjw3wid.onion
Price: $55 for 3 days.
We are only on TOR now.
Are you tired of your payload getting detected too quickly?
Imagine having your payload stay undetectable for months, bypassing all security warnings, including SmartScreen.
My Promise: BYPASS
 It will bypass Chrome warning, Edge, and Firefox & any other browser warnings.
It will bypass Chrome warning, Edge, and Firefox & any other browser warnings. It will bypass Windows SmartScreen warnings.
It will bypass Windows SmartScreen warnings.With my service, your payload will remain undetectable (FUD) for long time. This premium crypting service ensures your file remains fully undetectable, keeping your operations running smoothly without interruption.
Detection Avoidance:
100% No Threats Detected:
Our solution ensures that your payload stays FUD for over 20 days. Typical crypters get detected in 4 hours.
Long-Term FUD Guarantee:
Your file will stay undetectable for an extended period.
Bypassing All Security Measures:
Including SmartScreen, thanks to the EV certificate.
Custom Stub:
Specifically for your payload, ensuring maximum effectiveness.
No Extra Dependencies:
Native output for seamless operation.
I use an EV certificate, which usually costs $5,000 on the black market to sign your .exe, but you won't pay even half of that!
Now, for just $450 per month, enjoy unlimited crypts with our private crypter inside wdkiller.com. No more handmade crypting. Our service now bypasses Windows Defender, SmartScreen, Chrome, Edge, Firefox, and remains fully undetectable (FUD) for many days against Windows Defender.
Contact us on Telegram:
 @WE DON'T HAVE TELEGRAM, ANYONE WHO SAYS TO BE ME ====== SCAMMER
@WE DON'T HAVE TELEGRAM, ANYONE WHO SAYS TO BE ME ====== SCAMMER Need custom functions?
We tailor the stub to your requirements—add startup if needed, or configure it for stealers without requiring startup.
Our services are compatible with .NET and C++ outputs for both x86 and x64 architectures. Examples of supported tools include RedLine, Origin, Async, Quasar, Venom, XLoader, XWorm, DcRAT, Raccoon, and others.
[size=xx-large]Terms of Use[/size]
- Application and Acceptance: By accessing this site, you agree to these Terms and all applicable laws and regulations.
- Use License: You may temporarily download one copy for personal, non-commercial viewing only; copying, modifying, public display, decompiling, or reverse engineering is prohibited.
- This software is provided solely for educational purposes and authorized corporate Red Team operations.
- Any unauthorized, illegal, or malicious use—including hacking, unauthorized access, data theft, or distribution of malware—is strictly prohibited.
- Users must obtain explicit permission from the target organization before use.
- Subscriptions and Refunds: Refunds are not permitted without escrow; users may acquire a trial to test the service or purchase a full plan via escrow on our website (user pays all escrow fees). Prices, features, and durations may change at any time; misuse or sharing of a subscription will result in immediate ban; subscriptions may be terminated at any time without liability.
- Disclaimer of Warranties: All materials are provided “as is”; no express or implied warranties regarding accuracy or fitness.
- Limitation of Liability: We assume no liability for misuse or damages resulting from unauthorized use and are not liable for any direct or indirect damages, data loss, or loss of profits arising from use or inability to use the site.
- Revisions and Updates: Terms and site content may change at any time without notice.
- We reserve the right to ban any user found to be misusing this software.
- Violations may result in immediate termination of access, ban, and legal prosecution.
Please ensure that all files submitted do not contain any "install," "copy to startup," or "copy to registry" features. These functionalities must be completely clean in the tools provided. If you require startup capabilities to be added, please request this service explicitly.
WARNING:
This program was developed solely for educational purposes and authorized legal penetration testing for companies. It is also intended for individuals seeking to understand how hackers operate in order to better protect themselves. Any use of this tool for illegal activities is strictly prohibited and strongly discouraged.
Последнее редактирование: