[Cracking Windows Kernel with HEVD]
Cracking HackSys Extreme Vulnerable Driver: where do I start?
What is this?
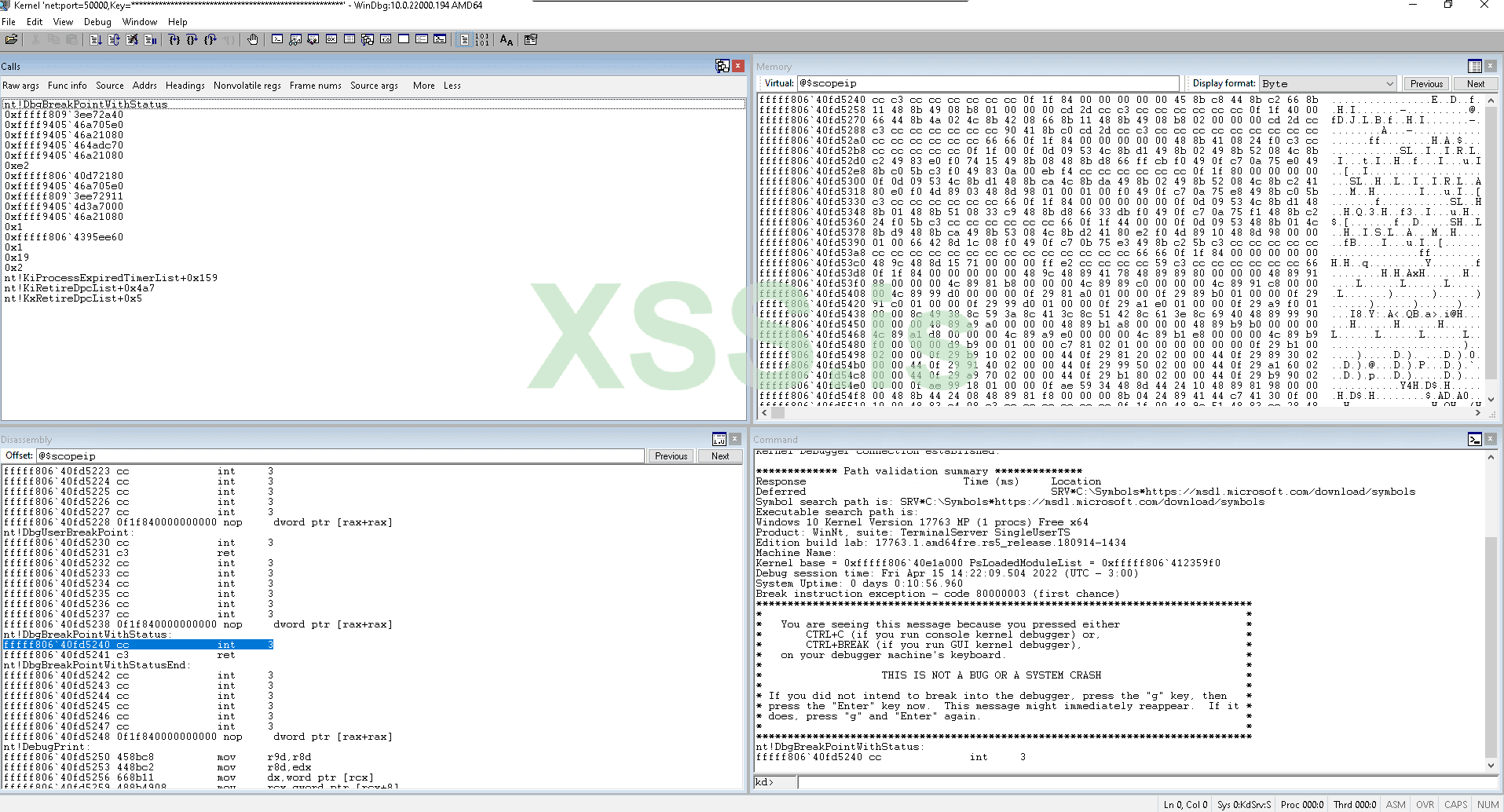
Hello! Previously we exploited vulnerable linux driver by invictus-0x90. If you missed, not to worry: this series is totally unrelated, since we’ll be exploiting the vulnerable Windows driver HEVD. However, if you are a curious one, make sure to check the other post!Today we’ll be attacking HEVD: HackSys Extreme Vulnerable Driver. This Windows driver is intentionally vulnerable to many memory corruption vulnerabilities (stack overflow, int overflow, use after free, type confusion, to name a few). We will exploit stack overflow to gain elevation of privileges in this post.
This exercise is a “must do” if you are starting on Windows kernel exploitation. I would like to thank Payatu and HackSys for developing this extremely useful learning tool.
Many people over the Internet have already solved it and posted writeups (probably way better than mine). However, most writeups I have read lack details on bypassing SMEP and KPTI. This part will be explained in depth here. Another rare, if not unique, feature of this post will be our sysret approach with KPTI.
I warn you this post will be long and slow-paced, good for people who has experience with memory corruption vulnerabilities but are getting started in kernel hacking. It will also go in depth on advanced topics, such as kernel security mitigation bypasses, KPTI bypass and sysret. I have divided in 5 chapters to be released every other week:
Enjoy !