Akamai waf blocks any a-Z characters after <
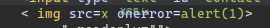
example: /contact?q=value"><a-Z is blocked by waf but if we add space before a-Z its allowed (value">< a-Z)
But xss doesnt alert when there is a space, i tried special-chars instead of regular characters (a-Z)
Blocked characters ? ! /
Allowed characters: ~ @ # $ % ^ & * ( ) - _ + = { } ] [ | \ ` , . ; : ' " < >
+ numbers
Is there a way to abuse these special chars or numbers to pop the xss?
example: /contact?q=value"><a-Z is blocked by waf but if we add space before a-Z its allowed (value">< a-Z)
But xss doesnt alert when there is a space, i tried special-chars instead of regular characters (a-Z)
Blocked characters ? ! /
Allowed characters: ~ @ # $ % ^ & * ( ) - _ + = { } ] [ | \ ` , . ; : ' " < >
+ numbers
Is there a way to abuse these special chars or numbers to pop the xss?